Streams and File I/O
... errors can be isolated better if they have different messages so create different catch blocks for each exception type put the more specific one first (the derived one) so it catches specifically file-not-found exceptions then you will know that an I/O error is something other than file-not-found ...
... errors can be isolated better if they have different messages so create different catch blocks for each exception type put the more specific one first (the derived one) so it catches specifically file-not-found exceptions then you will know that an I/O error is something other than file-not-found ...
CEG 210 FALL 2010 Chapter 9 Network Operating Systems
... – The ability to apply permissions for file and directory access and modification – A uniform method of issuing data to or receiving data from hardware devices, files, and running programs – The ability to start a program without interfering with a currently running program ...
... – The ability to apply permissions for file and directory access and modification – A uniform method of issuing data to or receiving data from hardware devices, files, and running programs – The ability to start a program without interfering with a currently running program ...
File I/O, if-then-else
... • A block is a group of lines of code that belong together. if ():
• In the Python interpreter, the ellipse indicates that you are inside a
block.
• Python uses indentation to keep track of blocks.
• You can use any number of spaces to indicate bl ...
... • A block is a group of lines of code that belong together. if (
File I/O, if-then-else
... • A block is a group of lines of code that belong together. if ():
• In the Python interpreter, the ellipse indicates that you are inside a
block.
• Python uses indentation to keep track of blocks.
• You can use any number of spaces to indicate bl ...
... • A block is a group of lines of code that belong together. if (
1 - Shrek
... command to recompile them. The decision is mainly based on “last modified time” of different sources and objects. The make utility uses a file usually named Makefile or makefile to represent dependencies between source files. Makefile consists of command like these: Rule_name:[list of rule dependenc ...
... command to recompile them. The decision is mainly based on “last modified time” of different sources and objects. The make utility uses a file usually named Makefile or makefile to represent dependencies between source files. Makefile consists of command like these: Rule_name:[list of rule dependenc ...
Producing SAS Files from Larger Master Files for a Clinical Research Project
... data for analysts from the m4ster file because the data are eucTypted and because only a subset of the thouSQndB of variables for each subject are deSi~ed for analySiS. AnalyuiB file Bub settiog is initiated by listing the'mnemon1ce and visit number a of desired-1t-ems~ These are linked with an item ...
... data for analysts from the m4ster file because the data are eucTypted and because only a subset of the thouSQndB of variables for each subject are deSi~ed for analySiS. AnalyuiB file Bub settiog is initiated by listing the'mnemon1ce and visit number a of desired-1t-ems~ These are linked with an item ...
Econ 231 / 232 Examples Using MAPLE
... can be used to solve a Keynesian macroeconomic system. While students may grasp the concept of an indifference curve, they often have difficulty envisioning a single indifference curve as part of an indifference map. This first example can be used to familiarize the student with the basic syntax of ...
... can be used to solve a Keynesian macroeconomic system. While students may grasp the concept of an indifference curve, they often have difficulty envisioning a single indifference curve as part of an indifference map. This first example can be used to familiarize the student with the basic syntax of ...
inode - Wikipedia, the free encyclopedia
... removed from the disk and its resources freed for reallocation (the normal process of deleting a file) but if any processes are holding the file open, they may continue to access it, and the file will only be finally deleted when the last reference to it is closed. This includes executable images wh ...
... removed from the disk and its resources freed for reallocation (the normal process of deleting a file) but if any processes are holding the file open, they may continue to access it, and the file will only be finally deleted when the last reference to it is closed. This includes executable images wh ...
Modeling of Synthetic & Biological Macromolecules: A Journey
... Manages the resources (CPU and I/O) present in the computer Unix is a true multi-user operating system The primary user interface with Unix is through a command line interface (terminal console) It has several GUI interfaces available, all built on Xwindows Integrated networking capabilities ...
... Manages the resources (CPU and I/O) present in the computer Unix is a true multi-user operating system The primary user interface with Unix is through a command line interface (terminal console) It has several GUI interfaces available, all built on Xwindows Integrated networking capabilities ...
Sample Title Slide - Fachhochschule Nordwestschweiz
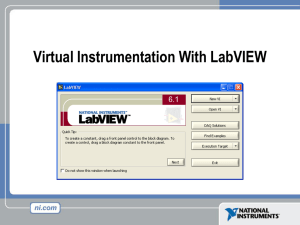
... Dataflow Programming • Block diagram does NOT execute left to right • Node executes when data is available to ALL input terminals • Nodes supply data to all output terminals when done ...
... Dataflow Programming • Block diagram does NOT execute left to right • Node executes when data is available to ALL input terminals • Nodes supply data to all output terminals when done ...
File input/output: Almost identical console input/output
... public static void main ( String [] args ) throws IOException { String line ; BufferedWriter fout = new BufferedWriter ( new FileWriter (" test . dat ")); for ( int i = 1; i <= 5; i ++) { fout . write ( i + " " + i * i + " " + i * i * i ) ; fout . newLine () ; ...
... public static void main ( String [] args ) throws IOException { String line ; BufferedWriter fout = new BufferedWriter ( new FileWriter (" test . dat ")); for ( int i = 1; i <= 5; i ++) { fout . write ( i + " " + i * i + " " + i * i * i ) ; fout . newLine () ; ...
Instructions to authors for the proceedings article
... 5. Don’t use any kind of “see above”-like phrases. However, try to avoid such kind of listings. A more concise version is given as: (i) don’t use vertical lines, (ii) don’t use double lines, (iii) write the units in the heading of each column, not inside the tabulated material, (iv) write always som ...
... 5. Don’t use any kind of “see above”-like phrases. However, try to avoid such kind of listings. A more concise version is given as: (i) don’t use vertical lines, (ii) don’t use double lines, (iii) write the units in the heading of each column, not inside the tabulated material, (iv) write always som ...
Input File
... multiplication, and division of f (x) and g (x ) are defined similar to its corresponding operation of the ordinary polynomials, except that all operations should be computed in Z 2 as defined above. For example, ( x 2 x1 ) ( x1 1) x 3 x 2 x 2 x1 x 3 x1 . A polynomial f (x) is prim ...
... multiplication, and division of f (x) and g (x ) are defined similar to its corresponding operation of the ordinary polynomials, except that all operations should be computed in Z 2 as defined above. For example, ( x 2 x1 ) ( x1 1) x 3 x 2 x 2 x1 x 3 x1 . A polynomial f (x) is prim ...
File Sizes & Types
... A .png does everything a .jpg OR .gif can do PLUS it creates beautiful transparency (which we’ll see in a second). The drawback is that .png tends to be a somewhat larger size than .gif or .jpg, so we don’t use it often, but the one thing it does better than any other file format is “transparency.” ...
... A .png does everything a .jpg OR .gif can do PLUS it creates beautiful transparency (which we’ll see in a second). The drawback is that .png tends to be a somewhat larger size than .gif or .jpg, so we don’t use it often, but the one thing it does better than any other file format is “transparency.” ...
Introduction to Unix
... subroutines to be executed first if they do not exist. Finally the command (or rule) is to be executed if all if the dependencies exist; it takes the dependencies and turns them into the target. There are two important things to remember: The file names must start on the first character of a line. ...
... subroutines to be executed first if they do not exist. Finally the command (or rule) is to be executed if all if the dependencies exist; it takes the dependencies and turns them into the target. There are two important things to remember: The file names must start on the first character of a line. ...
The Little Work Project
... The largest difference between our portable environment and the fixed environment is the lack of distributed file service when the modems are not connected. This requires us to violate our basic rule of dataless client. Currently when we want use a set of files on the portable machine we have two op ...
... The largest difference between our portable environment and the fixed environment is the lack of distributed file service when the modems are not connected. This requires us to violate our basic rule of dataless client. Currently when we want use a set of files on the portable machine we have two op ...
vasserman_foci12_slides
... Check replication level of manifest and file Re-encode the encrypted file (like publisher) ...
... Check replication level of manifest and file Re-encode the encrypted file (like publisher) ...
Problem A. Divide and conquer
... N people came to some bank to get their salary of a1 , a2 , . . . , aN tenge. There are total M banknotes left in the bank with values b1 , b2 , . . . , bM tenge correspondently. You need to determine whether bank is able to give exact salary to all people using given banknotes or not. ...
... N people came to some bank to get their salary of a1 , a2 , . . . , aN tenge. There are total M banknotes left in the bank with values b1 , b2 , . . . , bM tenge correspondently. You need to determine whether bank is able to give exact salary to all people using given banknotes or not. ...
Problem 3a: Hyperbolic PDE
... This problem holds an elastic string of length X=1 at both ends and deflects it at its midpoint by a max of u=.1. The string is then released and allowed to perform undamped oscillations. Since the hyperbolic PDE has 2 second order derivatives with respect to time and 2 second order derivatives with ...
... This problem holds an elastic string of length X=1 at both ends and deflects it at its midpoint by a max of u=.1. The string is then released and allowed to perform undamped oscillations. Since the hyperbolic PDE has 2 second order derivatives with respect to time and 2 second order derivatives with ...
Market Leader Error Message “ An Import is Currently in Progress
... database at the same time. 2.2. The import of a data file by another user may have ended abnormally due to a system lockup or other event. 3. Solution/Workaround: 3.1. Open the Maintenance Utility and repair the database file (usually DML.MDB). 3.2. If the repair does not resolve the error, open (in ...
... database at the same time. 2.2. The import of a data file by another user may have ended abnormally due to a system lockup or other event. 3. Solution/Workaround: 3.1. Open the Maintenance Utility and repair the database file (usually DML.MDB). 3.2. If the repair does not resolve the error, open (in ...
Lecture 1 - Thurs., 1/25/07
... All arguments are passed by value May pass literal values Compiler will check parameter usage: – Match a given call to its prototype – Match a function definition to its prototype – Pitfall: Critical to have only one prototype for each function • Put in a common file (.h) • the .h file is then inclu ...
... All arguments are passed by value May pass literal values Compiler will check parameter usage: – Match a given call to its prototype – Match a function definition to its prototype – Pitfall: Critical to have only one prototype for each function • Put in a common file (.h) • the .h file is then inclu ...
How to Write, Compile, and Run a Simple Java Program
... Change to the correct drive If the disk portion of the path (the drive letter) that is shown in the command prompt window is not the same as the drive where the code file is saved then change the disk by typing the correct letter, a colon, and pressing the ‘Enter’ key. For example, suppose that I sa ...
... Change to the correct drive If the disk portion of the path (the drive letter) that is shown in the command prompt window is not the same as the drive where the code file is saved then change the disk by typing the correct letter, a colon, and pressing the ‘Enter’ key. For example, suppose that I sa ...