All about “Spam”
... their contracts and run a significant risk of disconnection. At present there is no specific anti-spam law in the UK. However, this will soon change because the European Union has recently approved an E-Privacy Directive10 that must be transposed into UK law by 31st October 2003. This will make it u ...
... their contracts and run a significant risk of disconnection. At present there is no specific anti-spam law in the UK. However, this will soon change because the European Union has recently approved an E-Privacy Directive10 that must be transposed into UK law by 31st October 2003. This will make it u ...
LearnEnglish Professionals
... monitors internet trends. Michael, what exactly is 'viral marketing'? M: Hi Tony. The idea of viral marketing is basically that the internet does your advertising for you. A good example is internet email providers like Hotmail or Yahoo. Every time someone sends you an email using a Yahoo address ...
... monitors internet trends. Michael, what exactly is 'viral marketing'? M: Hi Tony. The idea of viral marketing is basically that the internet does your advertising for you. A good example is internet email providers like Hotmail or Yahoo. Every time someone sends you an email using a Yahoo address ...
E-goi and Return Path partner to improve email marketing
... E-goi clients can now build upon email marketing best practices with Return Path’s certification, which audits and closely monitors their sender reputation to help permission-based emails get through subscriber’s inboxes. “As an international email marketing provider, E-goi is a natural fit to partn ...
... E-goi clients can now build upon email marketing best practices with Return Path’s certification, which audits and closely monitors their sender reputation to help permission-based emails get through subscriber’s inboxes. “As an international email marketing provider, E-goi is a natural fit to partn ...
Introduction - Computer Science and Engineering
... • The latest threat on VoIP application is Spamming over Internet telephony (SPIT). “SPIT is a type of spam or solicitation made over VoIP. This means that spitters can now send annoying, repetitious advertisements similar to the spam choking our e-mail inboxes but in pre-recorded voice format. Not ...
... • The latest threat on VoIP application is Spamming over Internet telephony (SPIT). “SPIT is a type of spam or solicitation made over VoIP. This means that spitters can now send annoying, repetitious advertisements similar to the spam choking our e-mail inboxes but in pre-recorded voice format. Not ...
Team project: Stopping Spam
... the Internet. Unlike regular mail where the sender pays the cost of delivering the mail, email does not require the mailer to pay postage. In many cases email is cheap to send, and may be expensive to receive (depending on service provider pricing and connection speed). The process of sending unsoli ...
... the Internet. Unlike regular mail where the sender pays the cost of delivering the mail, email does not require the mailer to pay postage. In many cases email is cheap to send, and may be expensive to receive (depending on service provider pricing and connection speed). The process of sending unsoli ...
Email Marketing
... marketing: 1. Get into the inbox 2. Stay welcome in their inbox Everything we do with our email marketing should be designed to accomplish these two goals. ...
... marketing: 1. Get into the inbox 2. Stay welcome in their inbox Everything we do with our email marketing should be designed to accomplish these two goals. ...
Madleňák Radovan BASIC ASPECTS OF SPAM
... Internet for open relays in foreign countries for their messages not to be traced. Some spammers open free e-mail accounts and abandon them before they’re caught. Spammers also write programs that load in multiple accounts so when one account is terminated, another automatically kicks in. Quite a fe ...
... Internet for open relays in foreign countries for their messages not to be traced. Some spammers open free e-mail accounts and abandon them before they’re caught. Spammers also write programs that load in multiple accounts so when one account is terminated, another automatically kicks in. Quite a fe ...
View Comment
... Legitimate, reputable companies need to communicate with their existing and potential customers and stand to lose business if their marketing communications are intrusive. They generally seek to comply with the law and with codes of conduct and to apply good marketing practice. Laws such as those en ...
... Legitimate, reputable companies need to communicate with their existing and potential customers and stand to lose business if their marketing communications are intrusive. They generally seek to comply with the law and with codes of conduct and to apply good marketing practice. Laws such as those en ...
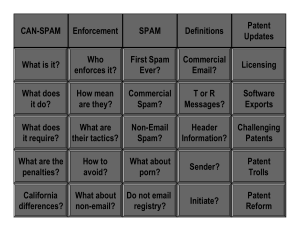
CAN SPAM Presentation
... •The target does not know until it gets served, which is too late. •The FTC will then fight tooth and nail with their endless resources. It's not pleasant. ...
... •The target does not know until it gets served, which is too late. •The FTC will then fight tooth and nail with their endless resources. It's not pleasant. ...
Top Online Marketing Platforms
... Strongview – reviews, ranked highest in research conducted by Forrestor, One of StrongView’s chief selling points, per Forrester, is Message Studio, an innovative email management platform where users can create personalized campaigns to target specific customers based on their profiles and shopping ...
... Strongview – reviews, ranked highest in research conducted by Forrestor, One of StrongView’s chief selling points, per Forrester, is Message Studio, an innovative email management platform where users can create personalized campaigns to target specific customers based on their profiles and shopping ...
Chapter 9: Intellectual Property
... to be confused by the similarity between the marks here; that precludes summary judgment in the case. Even if Beacon could not show that it lost sales, if it could show that there was confusion among selling agents and likely buyers, it has raised the possibility of damage to its goodwill and busine ...
... to be confused by the similarity between the marks here; that precludes summary judgment in the case. Even if Beacon could not show that it lost sales, if it could show that there was confusion among selling agents and likely buyers, it has raised the possibility of damage to its goodwill and busine ...
Fighting Spam - Northern Michigan University
... • 80% of all spam came from bot-nets – We helped • Open relays are mostly gone. • You can hire this done for you (see Google). ...
... • 80% of all spam came from bot-nets – We helped • Open relays are mostly gone. • You can hire this done for you (see Google). ...
international telecommunication union
... communication and transactions. Organizations need to continue to operate when hackers attack and keep infiltrators out. More security incidents were reported in 2002 than in the prior two years combined. And with most systems going wireless, security is paramount. Between palm pilots, mobile phones ...
... communication and transactions. Organizations need to continue to operate when hackers attack and keep infiltrators out. More security incidents were reported in 2002 than in the prior two years combined. And with most systems going wireless, security is paramount. Between palm pilots, mobile phones ...
Email spam

Email spam, also known as junk email or unsolicited bulk email (UBE), is a subset of electronic spam involving nearly identical messages sent to numerous recipients by email. The messages may contain disguised links that appear to be for familiar websites but in fact lead to phishing web sites or sites that are hosting malware. Spam email may also include malware as scripts or other executable file attachments. Definitions of spam usually include the aspects that email is unsolicited and sent in bulk. One subset of UBE is UCE (unsolicited commercial email). The opposite of ""spam"", email which one wants, is sometimes called ""ham"". Like other forms of unwanted bulk messaging, it is named for Spam luncheon meat by way of a Monty Python sketch in which Spam is depicted as ubiquitous and unavoidable.Email spam has steadily grown since the early 1990s. Botnets, networks of virus-infected computers, are used to send about 80% of spam. Since the expense of the spam is borne mostly by the recipient, it is effectively postage due advertising.The legal status of spam varies from one jurisdiction to another. In the United States, spam was declared to be legal by the CAN-SPAM Act of 2003 provided the message adheres to certain specifications. ISPs have attempted to recover the cost of spam through lawsuits against spammers, although they have been mostly unsuccessful in collecting damages despite winning in court.Spammers collect email addresses from chatrooms, websites, customer lists, newsgroups, and viruses which harvest users' address books, and are sold to other spammers. They also use a practice known as ""email appending"" or ""epending"" in which they use known information about their target (such as a postal address) to search for the target's email address. Much of spam is sent to invalid email addresses. According to the Message Anti-Abuse Working Group, the amount of spam email was between 88–92% of email messages sent in the first half of 2010.