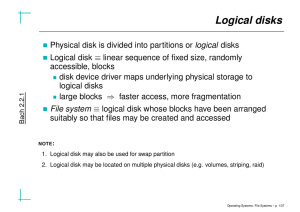
File Systems
... of device being unmounted; release inode of special file. 3. Get mount table entry, based on major/minor #. 4. Check whether files on the f.s. are still in use: 4.1 search inode table for all files whose dev. # matches the f.s. to be unmounted; 4.2 if any such file has ref. count > 0 (current direct ...
... of device being unmounted; release inode of special file. 3. Get mount table entry, based on major/minor #. 4. Check whether files on the f.s. are still in use: 4.1 search inode table for all files whose dev. # matches the f.s. to be unmounted; 4.2 if any such file has ref. count > 0 (current direct ...
Operating System Concepts
... processors. Scheduler activations attempt to address these limitations to userlevel threads. A scheduler activation is a kernel thread that can notify a userlevel threading library of events (e.g., a thread has blocked or a processor is available). This type of kernel thread is called a "scheduler a ...
... processors. Scheduler activations attempt to address these limitations to userlevel threads. A scheduler activation is a kernel thread that can notify a userlevel threading library of events (e.g., a thread has blocked or a processor is available). This type of kernel thread is called a "scheduler a ...
Lecture 13
... • What if multiple processes have a given file open? • Should they share one control structure or have one each? • In-memory structures typically contain a cursor pointer – Indicating how far into the file data has been read/written ...
... • What if multiple processes have a given file open? • Should they share one control structure or have one each? • In-memory structures typically contain a cursor pointer – Indicating how far into the file data has been read/written ...
Chapter 4: Threads
... To discuss the APIs for the Pthreads, Windows, and Java thread libraries To explore several strategies that provide implicit threading To examine issues related to multithreaded programming To cover operating system support for threads in Windows and Linux Operating System Concepts – 9th Edi ...
... To discuss the APIs for the Pthreads, Windows, and Java thread libraries To explore several strategies that provide implicit threading To examine issues related to multithreaded programming To cover operating system support for threads in Windows and Linux Operating System Concepts – 9th Edi ...
ppt
... A piece of code (library) is “thread-safe” if it defines critical sections and uses synchronization to control access to them All entry points must be re-entrant Results not returned in shared global variables nor global statically allocated storage All calls should be synchronous ...
... A piece of code (library) is “thread-safe” if it defines critical sections and uses synchronization to control access to them All entry points must be re-entrant Results not returned in shared global variables nor global statically allocated storage All calls should be synchronous ...
ppt
... A piece of code (library) is “thread-safe” if it defines critical sections and uses synchronization to control access to them All entry points must be re-entrant Results not returned in shared global variables nor global statically allocated storage All calls should be synchronous ...
... A piece of code (library) is “thread-safe” if it defines critical sections and uses synchronization to control access to them All entry points must be re-entrant Results not returned in shared global variables nor global statically allocated storage All calls should be synchronous ...
Ch4-Threads - Columbus State University
... Each user-level thread kernel thread Creating a user-level thread creates a kernel thread More concurrency than many-to-one # threads per process sometimes restricted due to overhead Examples ...
... Each user-level thread kernel thread Creating a user-level thread creates a kernel thread More concurrency than many-to-one # threads per process sometimes restricted due to overhead Examples ...
Comparison of Erlang Runtime System and Java Virtual Machine
... Figure 2 shows the general architecture of the Erlang Runtime System when looked upon as memory areas[8]. The major difference here is that instead of having a single shared heap, each process in Erlang has it’s own. The same memory area is also used for the stack of the process, where the two are g ...
... Figure 2 shows the general architecture of the Erlang Runtime System when looked upon as memory areas[8]. The major difference here is that instead of having a single shared heap, each process in Erlang has it’s own. The same memory area is also used for the stack of the process, where the two are g ...
ppt
... To explore several strategies that provide implicit threading To examine issues related to multithreaded programming To cover operating system support for threads in Windows and ...
... To explore several strategies that provide implicit threading To examine issues related to multithreaded programming To cover operating system support for threads in Windows and ...
OPERATING- SYSTEM CONCEPTS with Java
... Additional work that might be considered is learning about the particular systems that the students will have access to at your institution. This is still just a general overview, as specific interfaces are considered in Chapter 3. ...
... Additional work that might be considered is learning about the particular systems that the students will have access to at your institution. This is still just a general overview, as specific interfaces are considered in Chapter 3. ...
Lecture Notes- Operating Systems
... 4 Security of the system from outsiders requires user authentication, extends to defending external I/O devices from invalid access attempts 4 If a system is to be protected and secure, precautions must be instituted throughout it. A chain is only as strong as its weakest link. ...
... 4 Security of the system from outsiders requires user authentication, extends to defending external I/O devices from invalid access attempts 4 If a system is to be protected and secure, precautions must be instituted throughout it. A chain is only as strong as its weakest link. ...
Chapter 13 Exception Handling
... Mistakes happen No matter how well designed a program is, there is always the chance that some kind of error will arise during its execution. ...
... Mistakes happen No matter how well designed a program is, there is always the chance that some kind of error will arise during its execution. ...
Chap04
... The primary data structures of a thread include: ETHREAD (executive thread block) – includes pointer to process to which thread belongs and to KTHREAD, in kernel space KTHREAD (kernel thread block) – scheduling and synchronization info, kernelmode stack, pointer to TEB, in kernel space TEB ...
... The primary data structures of a thread include: ETHREAD (executive thread block) – includes pointer to process to which thread belongs and to KTHREAD, in kernel space KTHREAD (kernel thread block) – scheduling and synchronization info, kernelmode stack, pointer to TEB, in kernel space TEB ...
COP2800 * Computer Programming Using JAVA
... • It is simple to make it work • Applets are supported by most Web browsers • Execution can be fast • Computational work can be moved from server to client • Increased scalability with number of users and clients Some Disadvantages of Applets: • Requires Java plug-in • Some browsers, notably mobile ...
... • It is simple to make it work • Applets are supported by most Web browsers • Execution can be fast • Computational work can be moved from server to client • Increased scalability with number of users and clients Some Disadvantages of Applets: • Requires Java plug-in • Some browsers, notably mobile ...
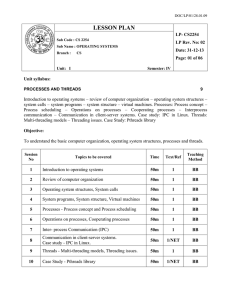
CS2254 os
... Introduction to operating systems – review of computer organization – operating system structures – system calls – system programs – system structure – virtual machines. Processes: Process concept – Process scheduling – Operations on processes – Cooperating processes – Interprocess communication – C ...
... Introduction to operating systems – review of computer organization – operating system structures – system calls – system programs – system structure – virtual machines. Processes: Process concept – Process scheduling – Operations on processes – Cooperating processes – Interprocess communication – C ...
Chapter 4: Threads
... To explore several strategies that provide implicit threading To examine issues related to multithreaded programming To cover operating system support for threads in Windows and ...
... To explore several strategies that provide implicit threading To examine issues related to multithreaded programming To cover operating system support for threads in Windows and ...
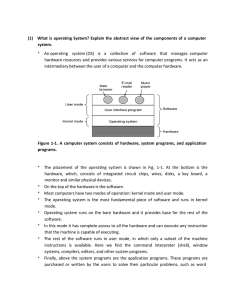
(1) What is operating System? Explain the abstract view of the
... Error detection and response Various types of errors can occur while a computer system is running, which includes internal and external hardware errors. For example, memory error, device failure error and software errors as arithmetic overflow. In case, operating system must provide a response that ...
... Error detection and response Various types of errors can occur while a computer system is running, which includes internal and external hardware errors. For example, memory error, device failure error and software errors as arithmetic overflow. In case, operating system must provide a response that ...
the internal operating system
... user interface. Chapter 17 moved inward to the next layer and presented the features and organization of the file management system. The file manager converts the logical representation of files as seen by the user or the user’s programs to the physical representation stored and manipulated within t ...
... user interface. Chapter 17 moved inward to the next layer and presented the features and organization of the file management system. The file manager converts the logical representation of files as seen by the user or the user’s programs to the physical representation stored and manipulated within t ...
Slides
... Type – needed for systems that support different types Location – pointer to file location on device Size – current file size Protection – controls who can do reading, writing, executing Time, date, and user identification – data for protection, security, and usage monitoring ...
... Type – needed for systems that support different types Location – pointer to file location on device Size – current file size Protection – controls who can do reading, writing, executing Time, date, and user identification – data for protection, security, and usage monitoring ...
M.C.A.(Sem - V) Distributed Computing
... 1. How does the system find an idle workstation? 2. How is a process transferred from one workstation to get it executed on another workstation? 3. What happens to a remote process if a user logs onto a workstation that was idle until now and was being used to execute a process of another workstatio ...
... 1. How does the system find an idle workstation? 2. How is a process transferred from one workstation to get it executed on another workstation? 3. What happens to a remote process if a user logs onto a workstation that was idle until now and was being used to execute a process of another workstatio ...
the linux operating system
... made to any portion of a typical monolithic OS, all the modules and routines must be relinked and reinstalled and the system rebooted before the changes can take effect. As a result, any modification, such as adding a new device driver or file system function, is difficult. This problem is especiall ...
... made to any portion of a typical monolithic OS, all the modules and routines must be relinked and reinstalled and the system rebooted before the changes can take effect. As a result, any modification, such as adding a new device driver or file system function, is difficult. This problem is especiall ...
University of Tehran
... Like kernels, only less number of abstractions exported (threads, address space, communication channel) Try to include only small set of required services in the microkernel Moves even more out of innermost OS part ...
... Like kernels, only less number of abstractions exported (threads, address space, communication channel) Try to include only small set of required services in the microkernel Moves even more out of innermost OS part ...
Threads
... To introduce the notion of a thread—a fundamental unit of CPU utilization that forms the basis of multithreaded computer systems ...
... To introduce the notion of a thread—a fundamental unit of CPU utilization that forms the basis of multithreaded computer systems ...
OSC message
... Numeric and symbolic arguments to messages Pattern matching language to specify multiple targets of a single message High resolution time tags "Bundles" of messages whose effects must occur simultaneously Query system to dynamically find out the capabilities of an OSC server and get documentation ...
... Numeric and symbolic arguments to messages Pattern matching language to specify multiple targets of a single message High resolution time tags "Bundles" of messages whose effects must occur simultaneously Query system to dynamically find out the capabilities of an OSC server and get documentation ...
Implementing Processes, Threads, and Resources
... Windows NT Process Descriptor (2) Kernel process object including: ...
... Windows NT Process Descriptor (2) Kernel process object including: ...
Library (computing)
In computer science, a library is a collection of non-volatile resources used by computer programs, often to develop software. These may include configuration data, documentation, help data, message templates, pre-written code and subroutines, classes, values or type specifications. In IBM's OS/360 and its successors they are referred to as partitioned data sets.In computer science, a library is a collection of implementations of behavior, written in terms of a language, that has a well-defined interface by which the behavior is invoked. This means that as long as a higher level program uses a library to make system calls, it does not need to be re-written to implement those system calls over and over again. In addition, the behavior is provided for reuse by multiple independent programs. A program invokes the library-provided behavior via a mechanism of the language. For example, in a simple imperative language such as C, the behavior in a library is invoked by using C's normal function-call. What distinguishes the call as being to a library, versus being to another function in the same program, is the way that the code is organized in the system. Library code is organized in such a way that it can be used by multiple programs that have no connection to each other, while code that is part of a program is organized to only be used within that one program. This distinction can gain a hierarchical notion when a program grows large, such as a multi-million-line program. In that case, there may be internal libraries that are reused by independent sub-portions of the large program. The distinguishing feature is that a library is organized for the purposes of being reused by independent programs or sub-programs, and the user only needs to know the interface, and not the internal details of the library.The value of a library is the reuse of the behavior. When a program invokes a library, it gains the behavior implemented inside that library without having to implement that behavior itself. Libraries encourage the sharing of code in a modular fashion, and ease the distribution of the code. The behavior implemented by a library can be connected to the invoking program at different program lifecycle phases. If the code of the library is accessed during the build of the invoking program, then the library is called a static library. An alternative is to build the executable of the invoking program and distribute that, independently from the library implementation. The library behavior is connected after the executable has been invoked to be executed, either as part of the process of starting the execution, or in the middle of execution. In this case the library is called a dynamic library. A dynamic library can be loaded and linked as part of preparing a program for execution, by the linker. Alternatively, in the middle of execution, an application may explicitly request that a module be loaded.Most compiled languages have a standard library although programmers can also create their own custom libraries. Most modern software systems provide libraries that implement the majority of system services. Such libraries have commoditized the services which a modern application requires. As such, most code used by modern applications is provided in these system libraries.