An Improved Approach to Generating Configuration Files from a
... • Code sharing with web applications • PL/SQL programs are shorter – Faster to write ...
... • Code sharing with web applications • PL/SQL programs are shorter – Faster to write ...
Schedule File Transformation Tools
... GSU class schedule can be printed or saved as a text file. This file is not very user friendly to analyze the data and take effective decisions. This text file has section details spanned across multiple pages with headers repeating in each page. This text file also has some additional details in be ...
... GSU class schedule can be printed or saved as a text file. This file is not very user friendly to analyze the data and take effective decisions. This text file has section details spanned across multiple pages with headers repeating in each page. This text file also has some additional details in be ...
File Share Dependencies
... It is recommended that the share name be dependent on the virtual server name, the server name be dependent on the Internet Protocol (IP) address, and the IP address dependent on the disk. These dependencies create a vertical dependency tree, which is useful for troubleshooting, and also provide con ...
... It is recommended that the share name be dependent on the virtual server name, the server name be dependent on the Internet Protocol (IP) address, and the IP address dependent on the disk. These dependencies create a vertical dependency tree, which is useful for troubleshooting, and also provide con ...
Operating System - GCG-42
... remember and learn the syntaxes of various commands as is the case in DOS. The user can just point and click on the Icons provided to him on the screen. ...
... remember and learn the syntaxes of various commands as is the case in DOS. The user can just point and click on the Icons provided to him on the screen. ...
Introduction to Operating Systems - Seneca
... the user’s wishes to the operating system We will be using the Korn Shell This is a command-line interface Command line interfaces are programmable, making them useful for many tasks for which GUIs are poorly suited ...
... the user’s wishes to the operating system We will be using the Korn Shell This is a command-line interface Command line interfaces are programmable, making them useful for many tasks for which GUIs are poorly suited ...
24 File Locking 25 Filesystem Reliability
... disks. A ninth disk stores a parity bit for each data byte. Parity bit is the result of an XOR among the eight data bits of the corresponding data byte. As a result, can still recover the data if one of the nine disks fails. Versioning filesystem: filesystem created a new version every time a file i ...
... disks. A ninth disk stores a parity bit for each data byte. Parity bit is the result of an XOR among the eight data bits of the corresponding data byte. As a result, can still recover the data if one of the nine disks fails. Versioning filesystem: filesystem created a new version every time a file i ...
Lecture 22 File-System Interface
... collection of similar records treated as a single entity have unique file names may restrict access ...
... collection of similar records treated as a single entity have unique file names may restrict access ...
Database/Record Structure
... Hypertext was invented by Ted Nelson in the 1960s. In a hypertext database, objects (text, pictures, music, and other media) are linked to each other. ...
... Hypertext was invented by Ted Nelson in the 1960s. In a hypertext database, objects (text, pictures, music, and other media) are linked to each other. ...
File concept
... Text files – sequence of characters organized into lines Source files – sequence of subroutines & lines , further organized into executable statements Object file – sequence of bytes organized into blocks understandable by system linker\ Executable file – series of code sections that the loader can ...
... Text files – sequence of characters organized into lines Source files – sequence of subroutines & lines , further organized into executable statements Object file – sequence of bytes organized into blocks understandable by system linker\ Executable file – series of code sections that the loader can ...
File System - QES Main Website
... storage devices, such as the hard drive • It also allow us to access external storage devices, such as USB sticks • And is even includes network ‘drives’, such as ‘Student Resources’ ...
... storage devices, such as the hard drive • It also allow us to access external storage devices, such as USB sticks • And is even includes network ‘drives’, such as ‘Student Resources’ ...
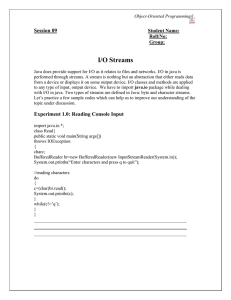
View File - UET Taxila
... Q1) By using the above techniques, copy a text file or java file to another already created file. You have to mention the names of the source and destination files at runtime. Also count number of words in that file. Q2) While compiling the above code, do mention such a name of destination file that ...
... Q1) By using the above techniques, copy a text file or java file to another already created file. You have to mention the names of the source and destination files at runtime. Also count number of words in that file. Q2) While compiling the above code, do mention such a name of destination file that ...
ComputersandFiles
... Computers and Files What you need to know before we start making web pages ...
... Computers and Files What you need to know before we start making web pages ...
installing debian
... UNIX Operating System (process management, memory management, the file system, I/O, etc.) Hardware (cpu, memory, disks, terminals, etc.) ...
... UNIX Operating System (process management, memory management, the file system, I/O, etc.) Hardware (cpu, memory, disks, terminals, etc.) ...
SCALABLE DECENTRALIZED DE
... Removing duplicate copies of files and storing only the pointers to the original copy. Block-level deduplication Allows more granularity and hence offers a greater reduction in storage space. Requires more processing power when compared to filelevel deduplication. ...
... Removing duplicate copies of files and storing only the pointers to the original copy. Block-level deduplication Allows more granularity and hence offers a greater reduction in storage space. Requires more processing power when compared to filelevel deduplication. ...
Implementation of Log Based File Systems on Open Source
... has its own set of advantages and disadvantages. Likewise, computing components, both physical components and software components, have similar sets of advantages and disadvantages One area of research is the tradeoffs associated with particular types of file systems. The file system is a software c ...
... has its own set of advantages and disadvantages. Likewise, computing components, both physical components and software components, have similar sets of advantages and disadvantages One area of research is the tradeoffs associated with particular types of file systems. The file system is a software c ...
File System Facts 5.3.3
... component that a file system uses to organize raw bits of data on the storage device itself. The file name is made up of the directory path plus the file name. An extension can also be added to the filename to identify the file type and the program used to create, view, and modify the file. ...
... component that a file system uses to organize raw bits of data on the storage device itself. The file name is made up of the directory path plus the file name. An extension can also be added to the filename to identify the file type and the program used to create, view, and modify the file. ...
cfintro
... Capturing a Drive Image Drive may be imaged via a USB or FireWire connection, or over the network. The size of the drive being imaged affects the time required to perform the capture. The speed of the connection also affects the time required to image the drive. A 500 GB drive may require 8 ...
... Capturing a Drive Image Drive may be imaged via a USB or FireWire connection, or over the network. The size of the drive being imaged affects the time required to perform the capture. The speed of the connection also affects the time required to image the drive. A 500 GB drive may require 8 ...
OPERATING SYSTEM FUNCTIONS
... To provide a place to keep files, most operating system has the concept of a directory as a way of grouping files together. A student, for example, might have one directory for each course he is taking (for the programs needed for that course), another directory for his electronic mail, and still an ...
... To provide a place to keep files, most operating system has the concept of a directory as a way of grouping files together. A student, for example, might have one directory for each course he is taking (for the programs needed for that course), another directory for his electronic mail, and still an ...
Partition In personal computers, a partition is a logical division of a
... Boot viruses can put the wrong information in the partition sector so that your operating system can't be located. For this reason, you should have a back-up version of your partition sector on a diskette known as a bootable floppy. ...
... Boot viruses can put the wrong information in the partition sector so that your operating system can't be located. For this reason, you should have a back-up version of your partition sector on a diskette known as a bootable floppy. ...
Presentation on File Managers
... a file system so as to waste as little storage as possible, speed up access to the files and to move often used files to the front of the ...
... a file system so as to waste as little storage as possible, speed up access to the files and to move often used files to the front of the ...
PPTX
... – File and device I/O are as similar as possible – File and device names have the same syntax and meaning, can pass as arguments to programs – Same protection mechanism as regular files ...
... – File and device I/O are as similar as possible – File and device names have the same syntax and meaning, can pass as arguments to programs – Same protection mechanism as regular files ...
PPTX
... – File and device I/O are as similar as possible – File and device names have the same syntax and meaning, can pass as arguments to programs – Same protection mechanism as regular files ...
... – File and device I/O are as similar as possible – File and device names have the same syntax and meaning, can pass as arguments to programs – Same protection mechanism as regular files ...
(1) OS: Operating System
... Critical Section Problem, Semaphores, Monitors, Deadlocks: Necessary conditions, resource allocation graph, Methods for handling deadlocks, preventions, avoidance, detection and recovery Protection –Goal domain of protection, access matrix. UNIT –IV:FILE SYSTEM Types of files in Unix - Structure of ...
... Critical Section Problem, Semaphores, Monitors, Deadlocks: Necessary conditions, resource allocation graph, Methods for handling deadlocks, preventions, avoidance, detection and recovery Protection –Goal domain of protection, access matrix. UNIT –IV:FILE SYSTEM Types of files in Unix - Structure of ...
Computer file

A computer file is a resource for storing information, which is available to a computer program and is usually based on some kind of durable storage. A file is ""durable"" in the sense that it remains available for other programs to use after the program that created it has finished executing. Computer files can be considered as the modern counterpart of paper documents which traditionally are kept in office and library files, and this is the source of the term.