File system implementation
... The table has one entry for each disk block, indexed by block number The FAT is used like a linked list. The directory entry contains the block number of the first block of the file The table entry indexed by that block number then contains the block number of the next block in the file, until the l ...
... The table has one entry for each disk block, indexed by block number The FAT is used like a linked list. The directory entry contains the block number of the first block of the file The table entry indexed by that block number then contains the block number of the next block in the file, until the l ...
Chapter 8 - Marshall University Personal Web Pages
... When a person needs some particular information that’s not in her brain at the moment, she finds a book in the library that has the information and, by reading it, transfers the information from the book into her brain. ...
... When a person needs some particular information that’s not in her brain at the moment, she finds a book in the library that has the information and, by reading it, transfers the information from the book into her brain. ...
SQL Server, Storage And You Part 2: SAN, NAS and IP Storage
... Over subscribing single disks “hot spots” Fabric misconfiguration SAN replication over large distance ...
... Over subscribing single disks “hot spots” Fabric misconfiguration SAN replication over large distance ...
BIM - BOUWonderWIJS.net
... General-purpose markup language capable of describing many different kinds of data XML provides a text-based format to describe and apply a tree-based structure to information XML can be used effectively to transfer various data via the Internet aecXML is a new framework for using the XML standard f ...
... General-purpose markup language capable of describing many different kinds of data XML provides a text-based format to describe and apply a tree-based structure to information XML can be used effectively to transfer various data via the Internet aecXML is a new framework for using the XML standard f ...
File
... designer as the principle means of identifying tuples within a relation. The primary key should be chosen such that its values are never, or rarely changed. E.g. :- the column containing department numbers in the S_DEPT table is created as a primary key and therefore every department number is diffe ...
... designer as the principle means of identifying tuples within a relation. The primary key should be chosen such that its values are never, or rarely changed. E.g. :- the column containing department numbers in the S_DEPT table is created as a primary key and therefore every department number is diffe ...
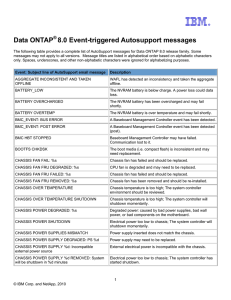
Data ONTAP® 8.0 Event-triggered Autosupport messages
... Data ONTAP® 8.0 Event-triggered Autosupport messages The following table provides a complete list of AutoSupport messages for Data ONTAP 8.0 release family. Some messages may not apply to all versions. Message titles are listed in alphabetical order based on alphabetic characters only. Spaces, under ...
... Data ONTAP® 8.0 Event-triggered Autosupport messages The following table provides a complete list of AutoSupport messages for Data ONTAP 8.0 release family. Some messages may not apply to all versions. Message titles are listed in alphabetical order based on alphabetic characters only. Spaces, under ...
MIS 485 Week 1 - University of Dayton
... to translate the logical description of the data into technical specifications for storing and retrieving data • Goal: create a design that will provide adequate performance and insure database integrity, security, and recoverability • Decisions made in this phase have a major impact on data accessi ...
... to translate the logical description of the data into technical specifications for storing and retrieving data • Goal: create a design that will provide adequate performance and insure database integrity, security, and recoverability • Decisions made in this phase have a major impact on data accessi ...
Files and Directories
... – Inefficient for tiny files (a 1 byte file requires both an inode and a data block) – Inefficient encoding when file is mostly contiguous on disk (no equivalent to superpages) – Need to reserve 10-20% of free space to prevent ...
... – Inefficient for tiny files (a 1 byte file requires both an inode and a data block) – Inefficient encoding when file is mostly contiguous on disk (no equivalent to superpages) – Need to reserve 10-20% of free space to prevent ...
The Complete A+ Guide to PC Repair
... • The term multimedia has different meanings to different people because there are so many different types of multimedia devices. This chapter focuses on the most popular areas and you will find that other devices are similar to install and troubleshoot. • Multimedia devices: – CD and DVD technologi ...
... • The term multimedia has different meanings to different people because there are so many different types of multimedia devices. This chapter focuses on the most popular areas and you will find that other devices are similar to install and troubleshoot. • Multimedia devices: – CD and DVD technologi ...
INFORMATION PROCESSING FOR A STORE - AN OVERVIEW
... known methods of operations research can then be used to compute stock level for initiating reorder and the optimal quantity to be reordered. Operational data collected over a period of time is called data archives and the process of collecting it is called data archiving. With the availability of m ...
... known methods of operations research can then be used to compute stock level for initiating reorder and the optimal quantity to be reordered. Operational data collected over a period of time is called data archives and the process of collecting it is called data archiving. With the availability of m ...
CUSTOMER_CODE SMUDE DIVISION_CODE SMUDE
... Document database servers are used to for electronic mail database and document based repositories. They are similar to the traditional database as they also contain alphanumeric data but differ from it as they contain special text fields that may be indexed within themselves using a hypertext engi ...
... Document database servers are used to for electronic mail database and document based repositories. They are similar to the traditional database as they also contain alphanumeric data but differ from it as they contain special text fields that may be indexed within themselves using a hypertext engi ...
Introduction to Databases - Department of Software and Information
... Organized to improve reliability and increase performance Performance Increased through data striping • Data segmented into equal-size partitions (striping unit) • Transparently distributed across multiple disks ...
... Organized to improve reliability and increase performance Performance Increased through data striping • Data segmented into equal-size partitions (striping unit) • Transparently distributed across multiple disks ...
L15_FS - Web Services Overview
... Break storage space into small fixed-size pieces, or blocks Allocate as many as needed to hold the file Store the disk block addresses for each of the blocks in the metadata record ...
... Break storage space into small fixed-size pieces, or blocks Allocate as many as needed to hold the file Store the disk block addresses for each of the blocks in the metadata record ...
categories of computer hardware
... Cache: it is a temporary storage area in the memory. It is a special highspeed memory that allows a microprocessor to access data more rapidly than from memory located elsewhere on the system board. Instruction set: this is the collection of pre-programmed activities such as addition, subtractio ...
... Cache: it is a temporary storage area in the memory. It is a special highspeed memory that allows a microprocessor to access data more rapidly than from memory located elsewhere on the system board. Instruction set: this is the collection of pre-programmed activities such as addition, subtractio ...
FILE SYSTEMS INTERFACE
... The Operating System "maps" or "connects" the data in the file with a region of memory in a process. b) When the file is closed, memory information is written back to the file. c) This is a great way to implement shared memory - have several processes open a memory-mapped file - they then each see t ...
... The Operating System "maps" or "connects" the data in the file with a region of memory in a process. b) When the file is closed, memory information is written back to the file. c) This is a great way to implement shared memory - have several processes open a memory-mapped file - they then each see t ...
OSPP: File Systems
... – Inefficient for tiny files (a 1 byte file requires both an inode and a data block) – Inefficient encoding when file is mostly contiguous on disk (no equivalent to superpages) – Need to reserve 10-20% of free space to prevent ...
... – Inefficient for tiny files (a 1 byte file requires both an inode and a data block) – Inefficient encoding when file is mostly contiguous on disk (no equivalent to superpages) – Need to reserve 10-20% of free space to prevent ...
Experiences with Content Addressable Storage and Virtual Disks Anthony Liguori
... templates for multiple logical instances which store perinstance modifications. We have previously experimented with both file and block-based copy-on-write technologies [9] for managing the life cycle of servers. While we found such “stackable” technologies to be very effective for initial installa ...
... templates for multiple logical instances which store perinstance modifications. We have previously experimented with both file and block-based copy-on-write technologies [9] for managing the life cycle of servers. While we found such “stackable” technologies to be very effective for initial installa ...
The Data Growth Problem
... The primary differentiator from business to business is the speed at which data progresses through its lifecycle ...
... The primary differentiator from business to business is the speed at which data progresses through its lifecycle ...
iscsi_and_dedupe.pps
... Because it is more granular, other overlaying file systems will align well. This comes at an increased load on the CPU, but because of the deduplication store tables which consume a great amount of memory it should be avoided with iSCSI. ...
... Because it is more granular, other overlaying file systems will align well. This comes at an increased load on the CPU, but because of the deduplication store tables which consume a great amount of memory it should be avoided with iSCSI. ...
File concept
... Text files – sequence of characters organized into lines Source files – sequence of subroutines & lines , further organized into executable statements Object file – sequence of bytes organized into blocks understandable by system linker\ Executable file – series of code sections that the loader can ...
... Text files – sequence of characters organized into lines Source files – sequence of subroutines & lines , further organized into executable statements Object file – sequence of bytes organized into blocks understandable by system linker\ Executable file – series of code sections that the loader can ...
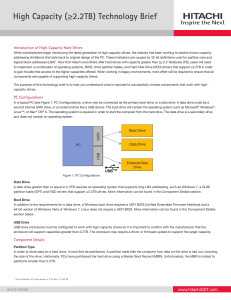
High Capacity (≥2.2TB) Technology Brief
... When powering up the PC, the PC BIOS will search for the boot drive and boot the operating system (OS) contained on that drive. For this process to work, the traditional PC BIOS relies on data stored in the partition table (i.e. the MBR) in order to boot the PC. When GPT was created, a new boot meth ...
... When powering up the PC, the PC BIOS will search for the boot drive and boot the operating system (OS) contained on that drive. For this process to work, the traditional PC BIOS relies on data stored in the partition table (i.e. the MBR) in order to boot the PC. When GPT was created, a new boot meth ...
File Systems - Computer Science Department
... • If the current file does not fill the last block or fragment, and there is enough room to write new data in the existing space no additional space is allocated. • If the last block doesn't contain enough space for the new data, look for one or more contiguous fragments. – If the amount to be writt ...
... • If the current file does not fill the last block or fragment, and there is enough room to write new data in the existing space no additional space is allocated. • If the last block doesn't contain enough space for the new data, look for one or more contiguous fragments. – If the amount to be writt ...
vandy_ibpgrid_05
... Accessing Globally Distributed Data » Collaboration requires shared file system • Nearly impossible over the wide-area network » Other methods include HTTP, FTP, GridFTP, scp • Can be painfully slow to transfer large data • Can be cumbersome to set up/manage accounts » How to manage replication? • ...
... Accessing Globally Distributed Data » Collaboration requires shared file system • Nearly impossible over the wide-area network » Other methods include HTTP, FTP, GridFTP, scp • Can be painfully slow to transfer large data • Can be cumbersome to set up/manage accounts » How to manage replication? • ...
CHAPTER 8 System Resources Optimization
... unsolicited. It can be sent over any media including email, online forums, blogs, etc. The main aim of SPAM is for free advertising. A person who creates a SPAM is called a spammer. When spamming floods the email inbox of a user, he will have to waste time and effort deleting all the unwanted messag ...
... unsolicited. It can be sent over any media including email, online forums, blogs, etc. The main aim of SPAM is for free advertising. A person who creates a SPAM is called a spammer. When spamming floods the email inbox of a user, he will have to waste time and effort deleting all the unwanted messag ...