Computer Networking : Principles, Protocols and Practice
... [Comer1988], a difficult choice at that time. He later extended his textbook by describing a complete TCP/IP implementation, adding practical considerations to the theoretical descriptions in [Comer1988]. Richard Stevens approached the Internet like an explorer and explained the operation of protoco ...
... [Comer1988], a difficult choice at that time. He later extended his textbook by describing a complete TCP/IP implementation, adding practical considerations to the theoretical descriptions in [Comer1988]. Richard Stevens approached the Internet like an explorer and explained the operation of protoco ...
Reference Manual for the 108 Mbps Wireless Firewall Router WGT624
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiat ...
... This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This equipment generates, uses, and can radiat ...
RangeMax Dual Band Wireless-N Modem Router Setup
... Router Manually (Advanced, Mac, and Linux Users)” on page 13. For example, if you are connecting to a Mac, are using a Linux operating system, or are technically knowledgeable, select this option. If you choose to use this option and install your router manually, for best results, install and set up ...
... Router Manually (Advanced, Mac, and Linux Users)” on page 13. For example, if you are connecting to a Mac, are using a Linux operating system, or are technically knowledgeable, select this option. If you choose to use this option and install your router manually, for best results, install and set up ...
2509, 2510, 2511, 2512 User Guide
... The console terminal is used to provide basic and emergency local system access. The auxiliary port is used to provide basic and emergency remote system access. The access server uses a 68-pin connector and breakout cable, which provides 8 RJ-45 ports on each cable. These ports use RJ-45-to-DB-25 ad ...
... The console terminal is used to provide basic and emergency local system access. The auxiliary port is used to provide basic and emergency remote system access. The access server uses a 68-pin connector and breakout cable, which provides 8 RJ-45 ports on each cable. These ports use RJ-45-to-DB-25 ad ...
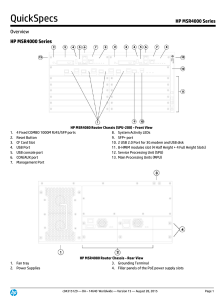
HP MSR4000 Series
... VXLAN (Virtual eXtensible LAN, scalable virtual local area network) is an IP-based network, using the "MAC in UDP" package of Layer VPN technology. VXLAN can be based on an existing ISP or enterprise IP networks for decentralized physical site provides Layer 2 communication, and can provide service ...
... VXLAN (Virtual eXtensible LAN, scalable virtual local area network) is an IP-based network, using the "MAC in UDP" package of Layer VPN technology. VXLAN can be based on an existing ISP or enterprise IP networks for decentralized physical site provides Layer 2 communication, and can provide service ...
Chapter 6: The Transport Layer
... – Increase window size • The maximum size in the header (16-bit) might be too small ...
... – Increase window size • The maximum size in the header (16-bit) might be too small ...
What is Cisco Remote-PHY Solution
... Driven by market evolution towards triple-play services, cable operators in emerging markets are seeking standardized and digital fiber-based solutions for economical and future proof access technologies. Much of the demand is driven by the need to provide higher bandwidth packet transport for Inter ...
... Driven by market evolution towards triple-play services, cable operators in emerging markets are seeking standardized and digital fiber-based solutions for economical and future proof access technologies. Much of the demand is driven by the need to provide higher bandwidth packet transport for Inter ...
Wireless-N 300 Modem Router DGN2200 Setup Manual
... Router” on page 1). Become familiar with the front and back panels of your router—especially the LEDs—and the important information on the router label (see “Hardware Features” on page 2). Then, read the section on “Positioning Your Wireless Router” on page 6 to ensure that you have selected the bes ...
... Router” on page 1). Become familiar with the front and back panels of your router—especially the LEDs—and the important information on the router label (see “Hardware Features” on page 2). Then, read the section on “Positioning Your Wireless Router” on page 6 to ensure that you have selected the bes ...
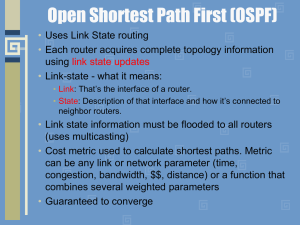
module10b
... • Full state (adjacency) - both routers have the synchronized database and are fully adjacent with each other. ...
... • Full state (adjacency) - both routers have the synchronized database and are fully adjacent with each other. ...
BSG 8ew 1.0 Solution Guide
... network and involve several components. The components involved in the architecture are the Communication Servers (CS2000), Media Gateways, Signaling Gateways, and CPE devices. They are interconnected through the Managed IP network that can be viewed as a core network that is managed by the service ...
... network and involve several components. The components involved in the architecture are the Communication Servers (CS2000), Media Gateways, Signaling Gateways, and CPE devices. They are interconnected through the Managed IP network that can be viewed as a core network that is managed by the service ...
Demystifying Layer 2 and Layer 3 VPNs
... 4.2.16 Less Vulnerable to Internet-Borne Security Threats .......................................................................................................................................................... 35 4.2.17 Multi-Homing for WAN Redundancy.............................................. ...
... 4.2.16 Less Vulnerable to Internet-Borne Security Threats .......................................................................................................................................................... 35 4.2.17 Multi-Homing for WAN Redundancy.............................................. ...
Cisco Inter-network Operating System (IOS) A short guide for the
... If things go fine we should be able to see a “Router>” prompt which is purely informational. The Cisco IOS command-line interface is organized around the idea of modes (Unprivileged/Privileged) which determine what commands you can use. Each mode has a set of commands available in that mode, and som ...
... If things go fine we should be able to see a “Router>” prompt which is purely informational. The Cisco IOS command-line interface is organized around the idea of modes (Unprivileged/Privileged) which determine what commands you can use. Each mode has a set of commands available in that mode, and som ...
Chapter11 (Unicast Routing Protocols)
... We refer to information about each route received from a neighbor as R, which has only two piece of information : R.dest and R.cost. The next hop is not included in the received record because it is the source address of the sender ...
... We refer to information about each route received from a neighbor as R, which has only two piece of information : R.dest and R.cost. The next hop is not included in the received record because it is the source address of the sender ...
69 Kyung Hee University Router Link LSA 70 Kyung Hee University
... We refer to information about each route received from a neighbor as R, which has only two piece of information : R.dest and R.cost. The next hop is not included in the received record because it is the source address of the sender ...
... We refer to information about each route received from a neighbor as R, which has only two piece of information : R.dest and R.cost. The next hop is not included in the received record because it is the source address of the sender ...
Where is the collision domain?
... sizes) can be generated. If an adapter is not working the hub can disconnect it internally and the network will not be affected. ©The McGraw-Hill Companies, Inc., 2004 ...
... sizes) can be generated. If an adapter is not working the hub can disconnect it internally and the network will not be affected. ©The McGraw-Hill Companies, Inc., 2004 ...
ccna3-mod4-SwitchingConcept
... please feel free to email me at [email protected] (I really don’t mind helping.) Also, if you run across any typos or errors in my ...
... please feel free to email me at [email protected] (I really don’t mind helping.) Also, if you run across any typos or errors in my ...
Datagram
... • Delivery of a packet can be accomplished by using either a connectionoriented or a connectionless network service. In a connection-oriented service, the source first makes a connection with the destination before sending a packet. When the connection is established, a sequence of packets from the ...
... • Delivery of a packet can be accomplished by using either a connectionoriented or a connectionless network service. In a connection-oriented service, the source first makes a connection with the destination before sending a packet. When the connection is established, a sequence of packets from the ...
I Know What Your Packet Did Last Hop: Using Packet
... The challenge for any system offering packet histories is to efficiently and scalably process a stream of postcards into archived, queryable packet histories. Surprisingly, a single NetSight server suffices to assemble and store packet histories from packet headers collected at each hop, for every p ...
... The challenge for any system offering packet histories is to efficiently and scalably process a stream of postcards into archived, queryable packet histories. Surprisingly, a single NetSight server suffices to assemble and store packet histories from packet headers collected at each hop, for every p ...
Raven and PinPoint GPRS User Guide
... GSM network. GPRS gives packet-switched access over GSM to external data networks with high peak transfer capacity. The main objective of GPRS is to offer access to standard data networks such as TCP/IP. GPRS is a non-voice service designed specifically for transmitting data. It breaks data messages ...
... GSM network. GPRS gives packet-switched access over GSM to external data networks with high peak transfer capacity. The main objective of GPRS is to offer access to standard data networks such as TCP/IP. GPRS is a non-voice service designed specifically for transmitting data. It breaks data messages ...
ppt
... multicast address = an IP address in the Class D range (224.0.0.0 – 239.255.255.255), used to refer to multiple recipients. A multicast address is also called a multicast group or channel. multicast stream = stream of IP packets with multicast address for IP destination address. All multicast uses U ...
... multicast address = an IP address in the Class D range (224.0.0.0 – 239.255.255.255), used to refer to multiple recipients. A multicast address is also called a multicast group or channel. multicast stream = stream of IP packets with multicast address for IP destination address. All multicast uses U ...
ICMP.pptx
... Historically, ICMP errors returned the offending IP header and the 1st 8 data bytes No longer adequate with more complicated headers like IP in IP New rules say that it should contain as much as original datagram as possible, without the length of ICMP datagram being > 576 bytes (standard Internet m ...
... Historically, ICMP errors returned the offending IP header and the 1st 8 data bytes No longer adequate with more complicated headers like IP in IP New rules say that it should contain as much as original datagram as possible, without the length of ICMP datagram being > 576 bytes (standard Internet m ...
AlliedWare Plus™ OS How To | Introduction
... network connectivity devices – such as switches – and the media endpoint devices connected to them – such as IP phones. A powerful feature of LLDP-MED is its ability to carry configuration instructions from the switch to the media devices that are connected to the switch. This configuration informat ...
... network connectivity devices – such as switches – and the media endpoint devices connected to them – such as IP phones. A powerful feature of LLDP-MED is its ability to carry configuration instructions from the switch to the media devices that are connected to the switch. This configuration informat ...
Chapter 6 - YSU Computer Science & Information Systems
... Each EIGRP router maintains a neighbor table that lists adjacent routers there is a neighbor table for each protocol that EIGRP supports used to support reliable, sequenced delivery of packets • One field in each row of the table is populated with the last sequence number of the packet received f ...
... Each EIGRP router maintains a neighbor table that lists adjacent routers there is a neighbor table for each protocol that EIGRP supports used to support reliable, sequenced delivery of packets • One field in each row of the table is populated with the last sequence number of the packet received f ...
ch08
... Introducing DHCP • DHCP – Service that provides a way for client computer to request IP address assignment – Delivers necessary configuration information to clients – Traces its origins back to an earlier protocol named BOOTP – Servers can manage one or more ranges of IP addresses ...
... Introducing DHCP • DHCP – Service that provides a way for client computer to request IP address assignment – Delivers necessary configuration information to clients – Traces its origins back to an earlier protocol named BOOTP – Servers can manage one or more ranges of IP addresses ...