A Connectivity Based Partition Approach for Node
... – Expected link delay are estimated based on statistical information • Vehicle densities on the roads vary with time • Vehicle density is quite stable during a period of time ...
... – Expected link delay are estimated based on statistical information • Vehicle densities on the roads vary with time • Vehicle density is quite stable during a period of time ...
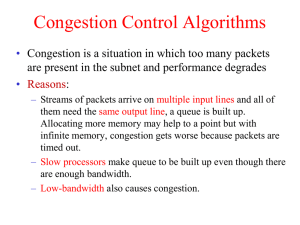
Chapter 5
... Architecture for streaming multimedia. Also called flow-based algorithms It was aimed at both unicast and multicast applications. Unicast Example :single user streaming a video clip from a news site ...
... Architecture for streaming multimedia. Also called flow-based algorithms It was aimed at both unicast and multicast applications. Unicast Example :single user streaming a video clip from a news site ...
Chapter 7 Lecture Presentation
... Call set-up phase establishes a fixed path along network before the data transfer phase All packets for the connection follow the same path Abbreviated header identifies connection on each link Packets queue for transmission Variable bit rates possible, negotiated during call set-up Delays are still ...
... Call set-up phase establishes a fixed path along network before the data transfer phase All packets for the connection follow the same path Abbreviated header identifies connection on each link Packets queue for transmission Variable bit rates possible, negotiated during call set-up Delays are still ...
Cognitive Packet Networks - TERENA Networking Conference 2001
... CPN: packet network architecture in which routing is carried under Packet Control -Cognitive Adaptive Routing: Smart or Cognitive Packets Control the Routing of the Dumb Packets Cognitive Packet Routing is Designed Using Random Neural Network based Reinforcement Learning, ...
... CPN: packet network architecture in which routing is carried under Packet Control -Cognitive Adaptive Routing: Smart or Cognitive Packets Control the Routing of the Dumb Packets Cognitive Packet Routing is Designed Using Random Neural Network based Reinforcement Learning, ...
ppt
... different computers • Must understand application needs/demands • Traffic data rate • Traffic pattern (bursty or constant bit rate) • Traffic target (multipoint or single destination, mobile or fixed) • Delay sensitivity • Loss sensitivity ...
... different computers • Must understand application needs/demands • Traffic data rate • Traffic pattern (bursty or constant bit rate) • Traffic target (multipoint or single destination, mobile or fixed) • Delay sensitivity • Loss sensitivity ...
WB_IP-2
... total length - packet length in bytes. precedence (3 bits) - designed for priority, but no standard procedure for this; little used. TOS - type of service TTL - time to live (die). Standard specified seconds, but in practice - router hops. ...
... total length - packet length in bytes. precedence (3 bits) - designed for priority, but no standard procedure for this; little used. TOS - type of service TTL - time to live (die). Standard specified seconds, but in practice - router hops. ...
Lecture 6: Vector
... Connectionless • Connectionless: every package of information must have an address => packets – Each package is routed to its destination by looking at its address – Analogy, the postal system (sending a letter) – also called “Statistical multiplexing” – Note: “Split phase buses” are sending packets ...
... Connectionless • Connectionless: every package of information must have an address => packets – Each package is routed to its destination by looking at its address – Analogy, the postal system (sending a letter) – also called “Statistical multiplexing” – Note: “Split phase buses” are sending packets ...
A method for IP multicast performance monitoring
... • … count the number of packets of each “block” to measure packet loss • … or take the timestamp of a particular packet within a block (f.i. the first packet of each block) to measure delay / jitter MBONED WG ...
... • … count the number of packets of each “block” to measure packet loss • … or take the timestamp of a particular packet within a block (f.i. the first packet of each block) to measure delay / jitter MBONED WG ...
jen-network - Princeton University
... – Don’t reserve bandwidth and memory – Don’t do error detection and correction – Don’t remember from one packet to next ...
... – Don’t reserve bandwidth and memory – Don’t do error detection and correction – Don’t remember from one packet to next ...
one.world — System Support for Pervasive Applications
... Keep up with Maximum Loss Free Receive Rate (MLFRR) Keep transmitting as you keep receiving ...
... Keep up with Maximum Loss Free Receive Rate (MLFRR) Keep transmitting as you keep receiving ...
The Infrastructure Technologies
... Application layer protocols that directly support application programs protocols such as telnet, FTP, SMTP, DNS, POP, and HTTP Transport layer TCP (Transmission Control Protocol) creates packets and reassembles messages ...
... Application layer protocols that directly support application programs protocols such as telnet, FTP, SMTP, DNS, POP, and HTTP Transport layer TCP (Transmission Control Protocol) creates packets and reassembles messages ...
Home Energy Management
... With the implementation of our Home Energy Management System and the advantage of Real-Time Pricing (RTP) provided by electric utility companies, consumers have the ability to adjust their energy usage in order to reduce their electricity bill. Sponsored by FEEDER – Foundation for Engineering Educ ...
... With the implementation of our Home Energy Management System and the advantage of Real-Time Pricing (RTP) provided by electric utility companies, consumers have the ability to adjust their energy usage in order to reduce their electricity bill. Sponsored by FEEDER – Foundation for Engineering Educ ...
Overview
... Self Learning: Building the Table • When a frame arrives – Inspect the source MAC address – Associate the address with the incoming interface – Store the mapping in the switch table – Use a time-to-live field to eventually forget the mapping ...
... Self Learning: Building the Table • When a frame arrives – Inspect the source MAC address – Associate the address with the incoming interface – Store the mapping in the switch table – Use a time-to-live field to eventually forget the mapping ...