Here is the Original File
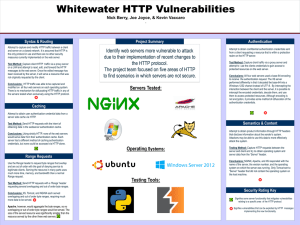
... Use the Range header to request byte ranges that overlap and are out of order with the goal of denying service to legitimate clients. Serving the resource in many parts uses much more time, memory, and bandwidth than a normal Range request. Test Method: Send HTTP requests with a ‘Range’ header reque ...
... Use the Range header to request byte ranges that overlap and are out of order with the goal of denying service to legitimate clients. Serving the resource in many parts uses much more time, memory, and bandwidth than a normal Range request. Test Method: Send HTTP requests with a ‘Range’ header reque ...
He-JPDC09-slide - People at VT Computer Science
... PICMM scheme outperforms all other schemes. PICMM uses a proxy to serve as a GFA to reduce the cost of location handoffs and the benefit is especially pronounced when the mobility rate of the MH is high. ...
... PICMM scheme outperforms all other schemes. PICMM uses a proxy to serve as a GFA to reduce the cost of location handoffs and the benefit is especially pronounced when the mobility rate of the MH is high. ...
Read more
... Intrinsyx delivers state-of-the-art engineering and software solutions for flight, network, database, and enterprise systems; and has unique expertise with process and systems engineering, CMMI, research, technology infusion and IT integration. Since 2000, Intrinsyx has delivered a variety of innovat ...
... Intrinsyx delivers state-of-the-art engineering and software solutions for flight, network, database, and enterprise systems; and has unique expertise with process and systems engineering, CMMI, research, technology infusion and IT integration. Since 2000, Intrinsyx has delivered a variety of innovat ...
suggested
... ie. without giving up the device identity to observers on the network Current TLS prevents passive monitoring. TLS 1.3 expected to protect against active as well. ...
... ie. without giving up the device identity to observers on the network Current TLS prevents passive monitoring. TLS 1.3 expected to protect against active as well. ...
module_70
... destination port addresses, and type of protocol (TCP or UDP). Incoming packets from network 131.34.0.0 are blocked. ‘*’ means any. Incoming packets destined for any internal TELNET server (port 23) are blocked. ...
... destination port addresses, and type of protocol (TCP or UDP). Incoming packets from network 131.34.0.0 are blocked. ‘*’ means any. Incoming packets destined for any internal TELNET server (port 23) are blocked. ...
cs591report
... city, state, zip code, country). We can probably borrow from this system for determining location within the Internet. Using regions for the IP address would introduce a few new problems. The first is the potential of address inefficiency5 where if the country is the topmost level then all countries ...
... city, state, zip code, country). We can probably borrow from this system for determining location within the Internet. Using regions for the IP address would introduce a few new problems. The first is the potential of address inefficiency5 where if the country is the topmost level then all countries ...
07-Servers - dolinski.co.uk | home
... Help you understand different types of servers commonly found on a network including: ...
... Help you understand different types of servers commonly found on a network including: ...
Firewall and Proxy Server
... SOCKS is networking proxy protocol that enables hosts on one side of a SOCKS server to gain full access to hosts on the other side of the SOCKS server without requiring direct IP reachability. SOCKS redirects connection requests from hosts on opposite sides of a SOCKS server. The SOCKS server auth ...
... SOCKS is networking proxy protocol that enables hosts on one side of a SOCKS server to gain full access to hosts on the other side of the SOCKS server without requiring direct IP reachability. SOCKS redirects connection requests from hosts on opposite sides of a SOCKS server. The SOCKS server auth ...
Optimal_Proxy_Cache_Allocation_for_Efficient_Streaming_Media
... The proxy can schedule a transmission of the complete suffix at t2+vi. (SBatch) Another option is to schedule a patch of [vi, t2] of the suffix from the server since segment [t2, Li] has already been scheduled to be transmitted. ...
... The proxy can schedule a transmission of the complete suffix at t2+vi. (SBatch) Another option is to schedule a patch of [vi, t2] of the suffix from the server since segment [t2, Li] has already been scheduled to be transmitted. ...
Mobile IP: Introduction
... • Why Performance enhancing proxies? – Most of existing protocols and AP. are designed for wired networks – Many of them do not work properly or efficiently on wireless networks ...
... • Why Performance enhancing proxies? – Most of existing protocols and AP. are designed for wired networks – Many of them do not work properly or efficiently on wireless networks ...
Reassembling
... all other cases, though, it’s true that a proxy should not have a direct interface on the Internet because if a hacker manages to compromise the proxy in some way it can have devastating results for the organization being protected. 14. Which of the following functions the Session-layer of the OSI m ...
... all other cases, though, it’s true that a proxy should not have a direct interface on the Internet because if a hacker manages to compromise the proxy in some way it can have devastating results for the organization being protected. 14. Which of the following functions the Session-layer of the OSI m ...
Author Guidelines for 8
... have developed a cross-layer architecture which offers always-connected services by exploiting all the networks available to the user, and by dynamically adapting their use on the basis of their performance and costs. Thus, our architecture can provide its users with reliable communications even in ...
... have developed a cross-layer architecture which offers always-connected services by exploiting all the networks available to the user, and by dynamically adapting their use on the basis of their performance and costs. Thus, our architecture can provide its users with reliable communications even in ...
(View complete abstract)
... Introduction: The goals of ubiquitous and pervasive computing [1, 2] are becoming more and more feasible as the number of computing resources 1 in the world increases rapidly. However, there are still significant hurdles to overcome when integrating wearable and embedded resources into a ubiquitous ...
... Introduction: The goals of ubiquitous and pervasive computing [1, 2] are becoming more and more feasible as the number of computing resources 1 in the world increases rapidly. However, there are still significant hurdles to overcome when integrating wearable and embedded resources into a ubiquitous ...
******* 1 - DistributedSys
... involve the partitioning and/or replication (or caching) of data amongst servers? Web: Partitioning :Web page masters are held in a file system at a single server. The information on the web as a whole is therefore partitioned amongst many web servers. Replication is not a part of the web protocols, ...
... involve the partitioning and/or replication (or caching) of data amongst servers? Web: Partitioning :Web page masters are held in a file system at a single server. The information on the web as a whole is therefore partitioned amongst many web servers. Replication is not a part of the web protocols, ...
uPortal 2.6 Brownbag I
... • Or some other resource the portal can get to that I’m not intended to get to? ...
... • Or some other resource the portal can get to that I’m not intended to get to? ...
Application and Circuit Gateways
... Many application clients can be configured to use a specific ALG (proxy) by the end user ...
... Many application clients can be configured to use a specific ALG (proxy) by the end user ...
Youtube Proxy Qawali
... Youtube Proxy Qawali - A virtual private network (VPN) extends a private network across a public network, such as the Internet. It enables a computer or network-enabled device to send and receive data across shared or public networks as if it were directly connected to the private network, while ben ...
... Youtube Proxy Qawali - A virtual private network (VPN) extends a private network across a public network, such as the Internet. It enables a computer or network-enabled device to send and receive data across shared or public networks as if it were directly connected to the private network, while ben ...
Split-TCP: State of the Union Address
... This new simulation model uses a TCP session established between the source and target, and dynamic proxy selection is performed along the path. s ...
... This new simulation model uses a TCP session established between the source and target, and dynamic proxy selection is performed along the path. s ...
document
... – Partition machines into those inside the organization and those outside the organization – Enforce an access control policy about what types of traffic are allowed in and out ...
... – Partition machines into those inside the organization and those outside the organization – Enforce an access control policy about what types of traffic are allowed in and out ...
Firewall Toolkit (FWTK)
... For applications to work with the SOCKS proxy server, they must be "SOCKS-ified." Most of the work involved in doing this has been packaged into the SOCKS software development kit (SDK). SOCKS has evolved over time and gone through several revisions. SOCKS version 4 was the first popular version ...
... For applications to work with the SOCKS proxy server, they must be "SOCKS-ified." Most of the work involved in doing this has been packaged into the SOCKS software development kit (SDK). SOCKS has evolved over time and gone through several revisions. SOCKS version 4 was the first popular version ...
Lecture1onInternet - IntroductionToComputing
... Allocates IP addresses to ISPs who then assign those addresses within their regions. Oversees the registration of domains and domain names. ...
... Allocates IP addresses to ISPs who then assign those addresses within their regions. Oversees the registration of domains and domain names. ...
Windows Media Player Cannot Play
... connect to the hosting server and change the protocol to whichever is supported by the server (e.g. RTSP, HTTP). 1) This problem can often be remedied by opening Windows Media Player and right-clicking on its title bar to invoke the menu. 2) From the menu, go to Tools > Options. 3) Click on the Netw ...
... connect to the hosting server and change the protocol to whichever is supported by the server (e.g. RTSP, HTTP). 1) This problem can often be remedied by opening Windows Media Player and right-clicking on its title bar to invoke the menu. 2) From the menu, go to Tools > Options. 3) Click on the Netw ...
Performance-aware Security for Unicast Communication in Hybrid Satellite Networks
... • TCP Performance Enhancing Proxy (PEP) server used to mitigate the negative impact of satellite link propagation delay on TCP performance. • HTTP Proxy server used to reduce the effect of satellite link delay on HTTP protocol/web browsing. • IPSEC disables the functionality of TCP PEP and HTTP ...
... • TCP Performance Enhancing Proxy (PEP) server used to mitigate the negative impact of satellite link propagation delay on TCP performance. • HTTP Proxy server used to reduce the effect of satellite link delay on HTTP protocol/web browsing. • IPSEC disables the functionality of TCP PEP and HTTP ...
CPSC 6126 Computer Security
... • Sniffer programs read IP packet streams for IP addresses of potential target hosts • With proxy server, sniffers will not learn IP addresses of internal hosts Sniffer Host IP Address ...
... • Sniffer programs read IP packet streams for IP addresses of potential target hosts • With proxy server, sniffers will not learn IP addresses of internal hosts Sniffer Host IP Address ...
Proxy server
In computer networks, a proxy server is a server (a computer system or an application) that acts as an intermediary for requests from clients seeking resources from other servers. A client connects to the proxy server, requesting some service, such as a file, connection, web page, or other resource available from a different server and the proxy server evaluates the request as a way to simplify and control its complexity. Proxies were invented to add structure and encapsulation to distributed systems. Today, most proxies are web proxies, facilitating access to content on the World Wide Web and providing anonymity.