Analysis of Reliable Multicast Protocols
... 6 : The destination network is unknown 7 : The destination host is unknown 8 : The source is isolated 9 : Communication with the destination network is administratively prohibited 10 : Communication with the destination host is administratively prohibited 11 : The network is unreachable for the spec ...
... 6 : The destination network is unknown 7 : The destination host is unknown 8 : The source is isolated 9 : Communication with the destination network is administratively prohibited 10 : Communication with the destination host is administratively prohibited 11 : The network is unreachable for the spec ...
OneWireless R240.1 Release Notes
... Refer to the OneWireless R240 Migration User's Guide for instructions on how to migrate a OneWireless R120.1 system to OneWireless R240.1. ATTENTION: OneWireless Network ID 1 is supported in R120.1 but is not supported in R240.1. Migration from R120.1 with Network ID 1 automatically reset Multinodes ...
... Refer to the OneWireless R240 Migration User's Guide for instructions on how to migrate a OneWireless R120.1 system to OneWireless R240.1. ATTENTION: OneWireless Network ID 1 is supported in R120.1 but is not supported in R240.1. Migration from R120.1 with Network ID 1 automatically reset Multinodes ...
IPV6 Essentials - AFCEA International
... – Distinguish packets from different classes or priorities – Same functionality as type of service field in IPv4 header ...
... – Distinguish packets from different classes or priorities – Same functionality as type of service field in IPv4 header ...
PPT Version
... Info: What the IBTA needs to define • Means for permitting a Host to establish an iSCSI/iSER connection with a peer InfiniBand end-node – Indicating when that end node does not support iSER • So the Host would be able to fall back to iSCSI/TCP over IPoIB ...
... Info: What the IBTA needs to define • Means for permitting a Host to establish an iSCSI/iSER connection with a peer InfiniBand end-node – Indicating when that end node does not support iSER • So the Host would be able to fall back to iSCSI/TCP over IPoIB ...
Datagram
... • Delivery of a packet can be accomplished by using either a connectionoriented or a connectionless network service. In a connection-oriented service, the source first makes a connection with the destination before sending a packet. When the connection is established, a sequence of packets from the ...
... • Delivery of a packet can be accomplished by using either a connectionoriented or a connectionless network service. In a connection-oriented service, the source first makes a connection with the destination before sending a packet. When the connection is established, a sequence of packets from the ...
The CELTIC Office Workplan
... – user access authorization. – IP mobility management for any legacy application. – network security (e.g, from femtocells to security gateways) – enforcement of security policies (filters out unwanted traffic) – load distribution (HIP provides opportunities for smart traffic steering in the HIP pee ...
... – user access authorization. – IP mobility management for any legacy application. – network security (e.g, from femtocells to security gateways) – enforcement of security policies (filters out unwanted traffic) – load distribution (HIP provides opportunities for smart traffic steering in the HIP pee ...
Ubee DDW366 Dual-Band Concurrent Advanced
... 1. 2.4G radio with Wi-Fi MAC address F4:B7:E2:E5:C3:D2 SSID: DDW366.E5C3D2-2.4G 2. 5G radio with Wi-Fi MAC address F4:B7:E2:E5:C3:D2 SSID: DDW366.E5C3D3-5G If the subscriber changes the SSID, the device does not revert to this default SSID when the device is reset, except when a factory reset is p ...
... 1. 2.4G radio with Wi-Fi MAC address F4:B7:E2:E5:C3:D2 SSID: DDW366.E5C3D2-2.4G 2. 5G radio with Wi-Fi MAC address F4:B7:E2:E5:C3:D2 SSID: DDW366.E5C3D3-5G If the subscriber changes the SSID, the device does not revert to this default SSID when the device is reset, except when a factory reset is p ...
Note - FlexWATCH
... 2 What is FlexWATCHTM NDVR server ? FlexWATCHTM 5000 is a stand alone network video recorder server which is designed to record real time JPEG video streams transmitted from any FlexWATCH™ network camera and video server series over the TCP/IP network. It supports rate up to 60fps for recording over ...
... 2 What is FlexWATCHTM NDVR server ? FlexWATCHTM 5000 is a stand alone network video recorder server which is designed to record real time JPEG video streams transmitted from any FlexWATCH™ network camera and video server series over the TCP/IP network. It supports rate up to 60fps for recording over ...
PowerPoint - UBC Department of Computer Science
... Demultiplexing of each incoming message to direct it to the proper receive function. ...
... Demultiplexing of each incoming message to direct it to the proper receive function. ...
5 Home network resource management
... Figure 1. Each layer consists of information sources, for example ISO/PAS 16739 (IFC) ca n act as an information source for physical layer (floor plan). Also the resource management requires defined representation models for the components in each layer and a mapping method to represent the relation ...
... Figure 1. Each layer consists of information sources, for example ISO/PAS 16739 (IFC) ca n act as an information source for physical layer (floor plan). Also the resource management requires defined representation models for the components in each layer and a mapping method to represent the relation ...
TR-0024-3GPP_Rel13_IWK-V2_0_1 - FTP
... © 2016, oneM2M Partners Type 1 (ARIB, ATIS, CCSA, ETSI, TIA, TSDSI, TTA, TTC). ...
... © 2016, oneM2M Partners Type 1 (ARIB, ATIS, CCSA, ETSI, TIA, TSDSI, TTA, TTC). ...
We need to have support for the notion of advertisements
... environments between “consenting” peers over the “edges” of the internet; the “disruptive” [11] impact of which has resulted in a slew of powerful applications built around this model. Resources shared could be anything – from CPU cycles, exemplified by SETI@home (extraterrestrial life) [14] and Fol ...
... environments between “consenting” peers over the “edges” of the internet; the “disruptive” [11] impact of which has resulted in a slew of powerful applications built around this model. Resources shared could be anything – from CPU cycles, exemplified by SETI@home (extraterrestrial life) [14] and Fol ...
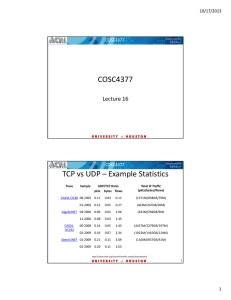
COSC4377 TCP vs UDP – Example Statistics
... routers. Routers advertise prefixes that identify the subnet(s) associated with a link, while hosts generate an "interface identifier" that uniquely identifies an interface on a subnet. An address is formed by combining the two. In the absence of routers, a host can only generate link‐local addre ...
... routers. Routers advertise prefixes that identify the subnet(s) associated with a link, while hosts generate an "interface identifier" that uniquely identifies an interface on a subnet. An address is formed by combining the two. In the absence of routers, a host can only generate link‐local addre ...
address… - ECSE - Rensselaer Polytechnic Institute
... not other UDP apps when reply is broadcast Does not wake up other servers during broadcast reply Shivkumar Kalyanaraman ...
... not other UDP apps when reply is broadcast Does not wake up other servers during broadcast reply Shivkumar Kalyanaraman ...
SAML Whitepaper
... A real world example of this type of scenario would be where a company is using an ASP (Application Service Provider) to provide its expense management functionality. It would be very desirable for the company’s employees to not have to authenticate directly to the ASP’s site each time they want to ...
... A real world example of this type of scenario would be where a company is using an ASP (Application Service Provider) to provide its expense management functionality. It would be very desirable for the company’s employees to not have to authenticate directly to the ASP’s site each time they want to ...
IPv6 Transition Mechanisms and Strategies
... time the host attaches to a different physical network (used for routing) A Mobile Host (MH) is allowed to roam to any IP network while other nodes connect using the original home address The binding of the two addresses are kept at the home agent (e.g. router) Pace University ...
... time the host attaches to a different physical network (used for routing) A Mobile Host (MH) is allowed to roam to any IP network while other nodes connect using the original home address The binding of the two addresses are kept at the home agent (e.g. router) Pace University ...
Analysis of Reliable Multicast Protocols
... 6 : The destination network is unknown 7 : The destination host is unknown 8 : The source is isolated 9 : Communication with the destination network is administratively prohibited 10 : Communication with the destination host is administratively prohibited 11 : The network is unreachable for the spec ...
... 6 : The destination network is unknown 7 : The destination host is unknown 8 : The source is isolated 9 : Communication with the destination network is administratively prohibited 10 : Communication with the destination host is administratively prohibited 11 : The network is unreachable for the spec ...
Cryptography and Network Security
... — MD5-Challenge: Analogous to the PPP CHAP protocol with MD5 as the specified algorithm, RFC 1994. The Request contains a "challenge" message to the peer. — One-Time Password (OTP): Defined in "A One-Time Password System," RFC 1938. The Request contains a displayable message containing an OTP challe ...
... — MD5-Challenge: Analogous to the PPP CHAP protocol with MD5 as the specified algorithm, RFC 1994. The Request contains a "challenge" message to the peer. — One-Time Password (OTP): Defined in "A One-Time Password System," RFC 1938. The Request contains a displayable message containing an OTP challe ...
802.1X Authentication - Training
... Some EAP methods, such as EAP-TLS, use certificate-based authentication to uniquely identify a client and provide the ability for the client to authenticate to the network without user intervention. Both the client and server have an identity, and these identities, along with other certificates, are ...
... Some EAP methods, such as EAP-TLS, use certificate-based authentication to uniquely identify a client and provide the ability for the client to authenticate to the network without user intervention. Both the client and server have an identity, and these identities, along with other certificates, are ...
Ubee DDW365 Advanced Wireless Gateway
... Understanding Safety and Regulatory Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1 Understanding Connections and Applications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3 Requesting Support . . . . . . . ...
... Understanding Safety and Regulatory Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1 Understanding Connections and Applications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3 Requesting Support . . . . . . . ...
Ubee DDW365 Advanced Wireless Gateway
... Understanding Safety and Regulatory Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1 Understanding Connections and Applications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3 Requesting Support . . . . . . . ...
... Understanding Safety and Regulatory Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1 Understanding Connections and Applications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3 Requesting Support . . . . . . . ...
Aalborg Universitet HomePort ZigBee Adapter
... C. Solution 3: Non-transparency A final option is to let HomePort be HomePort in the ZigBee network and avoid any transparency in the solution that would allow ZigBee devices to perform discovery as usually. One method would be to design an interface to the HomePort webservice. In this solution, Zig ...
... C. Solution 3: Non-transparency A final option is to let HomePort be HomePort in the ZigBee network and avoid any transparency in the solution that would allow ZigBee devices to perform discovery as usually. One method would be to design an interface to the HomePort webservice. In this solution, Zig ...
LN_ch07_Networking_Unix_Linux[2]ch14
... Signal is transferred to the ISP’s (Internet Service Provider) POP – Point of Present (located in the tel. switching office) and injected into the ISP’s regional network from this point the system is fully digital and Jozef Goetz, 2012 packet switched ...
... Signal is transferred to the ISP’s (Internet Service Provider) POP – Point of Present (located in the tel. switching office) and injected into the ISP’s regional network from this point the system is fully digital and Jozef Goetz, 2012 packet switched ...
MSG(13)034xxx Pseudo CHANGE REQUEST 124 301 Version 11.8
... CSG ID: A CSG ID is a unique identifier within the scope of one PLMN defined in 3GPP TS 23.003 [2] which identifies a Closed Subscriber Group (CSG) in the PLMN associated with a cell or group of cells to which access is restricted to members of the CSG. CSG selection: A UE supporting CSG selection s ...
... CSG ID: A CSG ID is a unique identifier within the scope of one PLMN defined in 3GPP TS 23.003 [2] which identifies a Closed Subscriber Group (CSG) in the PLMN associated with a cell or group of cells to which access is restricted to members of the CSG. CSG selection: A UE supporting CSG selection s ...
BGP messages - ece.virginia.edu
... selected a less specific route without selecting a more specific one that is included in it. – AGGREGATOR (type code 7): specifies the last AS number that formed the aggregate route followed by the IP address of the BGP router that formed the aggregate route. ...
... selected a less specific route without selecting a more specific one that is included in it. – AGGREGATOR (type code 7): specifies the last AS number that formed the aggregate route followed by the IP address of the BGP router that formed the aggregate route. ...









![LN_ch07_Networking_Unix_Linux[2]ch14](http://s1.studyres.com/store/data/008747649_1-f6bc28385c6088d404edcf68eef533e5-300x300.png)

