Technical Report: The KNIME Text Processing Feature: An
... DocumentCells and the other containing TermCells. This node will only work (configure) properly with an input data table consisting of a column of DocumentCells. The “BoW creator” node, and all other nodes of the Text Processing feature require input data tables of specific structure and create outp ...
... DocumentCells and the other containing TermCells. This node will only work (configure) properly with an input data table consisting of a column of DocumentCells. The “BoW creator” node, and all other nodes of the Text Processing feature require input data tables of specific structure and create outp ...
Adaptive Save Restore” Exploiting Control references to Save
... dependent on the index settings AND the number of elements that are viewable. (Please experiment for yourself). If, however, the arrays viewable size is set to 1 X 1 (this can be controlled using the “Number of Columns” and “Number of Rows” properties), then the index does control which element get ...
... dependent on the index settings AND the number of elements that are viewable. (Please experiment for yourself). If, however, the arrays viewable size is set to 1 X 1 (this can be controlled using the “Number of Columns” and “Number of Rows” properties), then the index does control which element get ...
Oracle`s Business Strategy: Maximizing Your Sales Leverage
... • Hash tables are one of the most powerful ways for searching data based on a key. The main issue with traditional hash function is the hash value collisions • Here's an example of a hash table that uses separate chaining. To look up a word, we run it through a hash function, H() which returns a num ...
... • Hash tables are one of the most powerful ways for searching data based on a key. The main issue with traditional hash function is the hash value collisions • Here's an example of a hash table that uses separate chaining. To look up a word, we run it through a hash function, H() which returns a num ...
pptx
... • Another refinement is to use the BETWEEN operator. If we want only those orders between 10 and 100 then we could define this as: SELECT Orders.cust_id, Orders.cost FROM Orders WHERE Orders.cost >10 and Orders.cost <100; • Or use the between operator: SELECT Orders.cust_id, Orders.cost FROM Orders ...
... • Another refinement is to use the BETWEEN operator. If we want only those orders between 10 and 100 then we could define this as: SELECT Orders.cust_id, Orders.cost FROM Orders WHERE Orders.cost >10 and Orders.cost <100; • Or use the between operator: SELECT Orders.cust_id, Orders.cost FROM Orders ...
b63_midterm-version2..
... determine a word’s category in O(1) time. Hint: you can adjust the data structure in some other way, use a combination of data structures, or both. But don’t increase the memory use by more than a small constant. (That’s an added constant, not a constant factor.) Answer: Use eight hash tables--one f ...
... determine a word’s category in O(1) time. Hint: you can adjust the data structure in some other way, use a combination of data structures, or both. But don’t increase the memory use by more than a small constant. (That’s an added constant, not a constant factor.) Answer: Use eight hash tables--one f ...
Chapter9
... TABLE 9-1 Values of first, last, and mid and the number of comparisons for search item 89 Data Structures Using C++ 2E ...
... TABLE 9-1 Values of first, last, and mid and the number of comparisons for search item 89 Data Structures Using C++ 2E ...
Recursively Partitioned Static IP Router-Tables
... Lampson et al.[4] propose a partitioning scheme for static router-tables. This scheme employs a front-end array, partition, to partition the prefixes in a router table based on their first s, bits. Prefixes that are longer than s bits and whose first s bits correspond to the number i, 0 ≤ i < 2s are ...
... Lampson et al.[4] propose a partitioning scheme for static router-tables. This scheme employs a front-end array, partition, to partition the prefixes in a router table based on their first s, bits. Prefixes that are longer than s bits and whose first s bits correspond to the number i, 0 ≤ i < 2s are ...
Pointers to Functions - CS
... program supplied with this class Run them in DDD (or gdb) set breakpoints step through program force an assert, and see what happens ...
... program supplied with this class Run them in DDD (or gdb) set breakpoints step through program force an assert, and see what happens ...
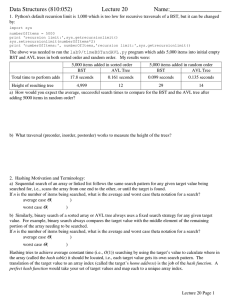
Data Structures (810:052) Lecture 20 Name:_________________
... Try inserting numbers for yourself, and demonstrate how the probe sequences for diverge by inserting these numbers into a table of size 16: 0, 16, 32, 15, 31. Unfortunately, quadratic probing has the disadvantage that typically not all hash table slots will be on the probe sequence. Using p(K, i) = ...
... Try inserting numbers for yourself, and demonstrate how the probe sequences for diverge by inserting these numbers into a table of size 16: 0, 16, 32, 15, 31. Unfortunately, quadratic probing has the disadvantage that typically not all hash table slots will be on the probe sequence. Using p(K, i) = ...
Data Structures So Far
... a test that decides which of several possible recursive calls to make, but it should ultimately choose to make just one of these calls each time we perform this step.) Define each possible recursive call so that it makes progress towards a base case. ...
... a test that decides which of several possible recursive calls to make, but it should ultimately choose to make just one of these calls each time we perform this step.) Define each possible recursive call so that it makes progress towards a base case. ...
Document
... • Identical to passing a one-dimensional array – The called method receives access to the entire array ...
... • Identical to passing a one-dimensional array – The called method receives access to the entire array ...
COS 226 Final Exam Review Fall 2015 Ananda
... – Since 15 and 25 can be represented using 5 bits, we need only 10 bits to represent a total of 15+25 = 40 bits. A compression ratio of 10/40 = 25% Under what circumstances would you use this algorithm? – A great algorithm when sending FAX, lots of white spaces (0’s) leading to long patterns of 0 If ...
... – Since 15 and 25 can be represented using 5 bits, we need only 10 bits to represent a total of 15+25 = 40 bits. A compression ratio of 10/40 = 25% Under what circumstances would you use this algorithm? – A great algorithm when sending FAX, lots of white spaces (0’s) leading to long patterns of 0 If ...
ppt
... One area where we will be able to use the hashtable structure is in storing graphs. Here, we describe a semidynamic directed-graph implementation. This means that the number of vertices is fixed, but edges can be added or deleted at runtime. Let u and v be vertices of a graph. We want the following ...
... One area where we will be able to use the hashtable structure is in storing graphs. Here, we describe a semidynamic directed-graph implementation. This means that the number of vertices is fixed, but edges can be added or deleted at runtime. Let u and v be vertices of a graph. We want the following ...
UNIT-1 Introduction to System Programming
... allows a sequence of source language code to be defined once and then referred to by name each time it is to be referred. Each time this name Occurs in a program, the sequence of codes is substituted at that point. ...
... allows a sequence of source language code to be defined once and then referred to by name each time it is to be referred. Each time this name Occurs in a program, the sequence of codes is substituted at that point. ...
Advanced Design Techniques 2 - Tonga Institute of Higher Education
... • There are newer techniques that are a little more complicated, but allow computer scientists to solve harder problems. We will look at two methods. • "Greedy" programming is a way to optimize a solution where you must make a choice. In this method, you make the best choice at each time and by the ...
... • There are newer techniques that are a little more complicated, but allow computer scientists to solve harder problems. We will look at two methods. • "Greedy" programming is a way to optimize a solution where you must make a choice. In this method, you make the best choice at each time and by the ...
Chapters 3-6 - gozips.uakron.edu
... Font weight – specifies level of bold formatting applied to a text. May be expressed in three ways: o Values (from 100 to 900 in increments of 100). E.g. font-weight: 400 o Keywords (normal, bold). E.g., font-weight: bold o Keywords specifying weight relative to the containing element (bolder, light ...
... Font weight – specifies level of bold formatting applied to a text. May be expressed in three ways: o Values (from 100 to 900 in increments of 100). E.g. font-weight: 400 o Keywords (normal, bold). E.g., font-weight: bold o Keywords specifying weight relative to the containing element (bolder, light ...
Control table

Control tables are tables that control the control flow or play a major part in program control. There are no rigid rules about the structure or content of a control table—its qualifying attribute is its ability to direct control flow in some way through ""execution"" by a processor or interpreter. The design of such tables is sometimes referred to as table-driven design (although this typically refers to generating code automatically from external tables rather than direct run-time tables). In some cases, control tables can be specific implementations of finite-state-machine-based automata-based programming. If there are several hierarchical levels of control table they may behave in a manner equivalent to UML state machinesControl tables often have the equivalent of conditional expressions or function references embedded in them, usually implied by their relative column position in the association list. Control tables reduce the need for programming similar structures or program statements over and over again. The two-dimensional nature of most tables makes them easier to view and update than the one-dimensional nature of program code. In some cases, non-programmers can be assigned to maintain the control tables.