Base Table - People.csail.mit.edu
... This manual is for SLIB (version 3b4, May 2013), the portable Scheme library. c 1993, 1994, 1995, 1996, 1997, 1998, 1999, 2000, 2001, 2002, 2003, 2004, 2005, Copyright 2006, 2007, 2008 Free Software Foundation, Inc. Permission is granted to copy, distribute and/or modify this document under the t ...
... This manual is for SLIB (version 3b4, May 2013), the portable Scheme library. c 1993, 1994, 1995, 1996, 1997, 1998, 1999, 2000, 2001, 2002, 2003, 2004, 2005, Copyright 2006, 2007, 2008 Free Software Foundation, Inc. Permission is granted to copy, distribute and/or modify this document under the t ...
Microport System V AT Development System VolII
... These functions provide translation of uppercase to lowercase, lowercase to uppercase, and integer to ASCII. FUNCTION ...
... These functions provide translation of uppercase to lowercase, lowercase to uppercase, and integer to ASCII. FUNCTION ...
Arrays
... Many programs present data to users in a graphical manner. For example, numeric values often are displayed as bars in a bar chart. In such a chart, longer bars represent larger numeric values. One simple way to display numeric data graphically is with a histogram that shows each numeric value as a b ...
... Many programs present data to users in a graphical manner. For example, numeric values often are displayed as bars in a bar chart. In such a chart, longer bars represent larger numeric values. One simple way to display numeric data graphically is with a histogram that shows each numeric value as a b ...
Fast Local Searches and Updates in Bounded Universes
... U stores the bottom portion of the trie as a collection of balanced binary search trees each of size O(log U 0 ), which we will refer to as buckets. In our setting, this ...
... U stores the bottom portion of the trie as a collection of balanced binary search trees each of size O(log U 0 ), which we will refer to as buckets. In our setting, this ...
Fast Local Searches and Updates in Bounded Universes
... U 0 stores the bottom portion of the trie as a collection of balanced binary search trees each of size O(log U 0 ), which we will refer to as buckets. In our setting, this ...
... U 0 stores the bottom portion of the trie as a collection of balanced binary search trees each of size O(log U 0 ), which we will refer to as buckets. In our setting, this ...
Study Material - JNV West Godavari
... were PI and NEWLINE) by the code to which they have been defined (31.4159 and „\n” respectively). The #define directive is not a C++ statement but a directive for the preprocessor; therefore it assumes the entire line as the directive and does not require a semicolon (;) at its end. If we append a s ...
... were PI and NEWLINE) by the code to which they have been defined (31.4159 and „\n” respectively). The #define directive is not a C++ statement but a directive for the preprocessor; therefore it assumes the entire line as the directive and does not require a semicolon (;) at its end. If we append a s ...
an alternative efficient chessboard representation based on 4
... type of a piece on the board. So, there are six bitboards for white pieces; pawn, knight, bishop, rook, queen, king and also six for corresponding black pieces. They annotated the connection between 64-bits in integer and the number of squares on the chessboard, so a 1 bit could be used to indicate ...
... type of a piece on the board. So, there are six bitboards for white pieces; pawn, knight, bishop, rook, queen, king and also six for corresponding black pieces. They annotated the connection between 64-bits in integer and the number of squares on the chessboard, so a 1 bit could be used to indicate ...
C++ for You++ - Skylight Publishing
... Students who take the A- or AB- level AP exam are expected to know how to use the apvector, apmatrix, and apstring classes in programs. Students who take the AB-level exam are also expected to use and re-implement the apstack and apqueue classes. Computer science is an applied discipline, not just a ...
... Students who take the A- or AB- level AP exam are expected to know how to use the apvector, apmatrix, and apstring classes in programs. Students who take the AB-level exam are also expected to use and re-implement the apstack and apqueue classes. Computer science is an applied discipline, not just a ...
Implementing Database Operations Using SIMD
... The goal of vectorizing compilers is to automatically detect opportunities where ordinary code can be transformed into code exploiting SIMD techniques. For example, icc does have vectorizing capabilities [15]. However, [15] describes various reasons why the compiler may fail to apply vectorization, ...
... The goal of vectorizing compilers is to automatically detect opportunities where ordinary code can be transformed into code exploiting SIMD techniques. For example, icc does have vectorizing capabilities [15]. However, [15] describes various reasons why the compiler may fail to apply vectorization, ...
Ders 6. Problemler
... a) The first statement declares an array reference. b) The second statement creates the array. c) g is a reference to an array of integers. d) The value of g[ 3 ] is -1. Ans: d 17. An array must be declared and allocated in the same statement. Ans: False. An array can be declared and allocated in se ...
... a) The first statement declares an array reference. b) The second statement creates the array. c) g is a reference to an array of integers. d) The value of g[ 3 ] is -1. Ans: d 17. An array must be declared and allocated in the same statement. Ans: False. An array can be declared and allocated in se ...
KorthDB6_ch11
... ©Silberschatz, Korth and Sudarshan See www.db-book.com for conditions on re-use ...
... ©Silberschatz, Korth and Sudarshan See www.db-book.com for conditions on re-use ...
Cache conscious column organization in in
... Enterprise Environment We base this work on the assumptions of using a columnar inmemory database for enterprise applications for combined transactional and analytical systems. Recent work analyzed the workload of enterprise customer systems, finding in total more than 80 % of all queries are read a ...
... Enterprise Environment We base this work on the assumptions of using a columnar inmemory database for enterprise applications for combined transactional and analytical systems. Recent work analyzed the workload of enterprise customer systems, finding in total more than 80 % of all queries are read a ...
eel3801
... The const and Pointer Passing The const qualifier tells the compiler that the variable following it is not to be changed by any program statements. Provides a measure of security when passing addresses of variables whose values are not to be modified (for example, arrays). When passing pointers, ...
... The const and Pointer Passing The const qualifier tells the compiler that the variable following it is not to be changed by any program statements. Provides a measure of security when passing addresses of variables whose values are not to be modified (for example, arrays). When passing pointers, ...
Discovering Web Structure with Multiple Experts in a Clustering
... Snippet from Sample Web Page — A name-value list such as the one on this page can be represented as multiple rows in a name-value table or as a single row where the names correspond to the columns of the table. . . . Levels of Effort — We compare the levels of effort required to extract data from th ...
... Snippet from Sample Web Page — A name-value list such as the one on this page can be represented as multiple rows in a name-value table or as a single row where the names correspond to the columns of the table. . . . Levels of Effort — We compare the levels of effort required to extract data from th ...
Chapter 4 Index Structures
... Until this point we have supposed that the search key, upon which the index is based, was also a key of the relation, so there could be at most one recoid with any key value. However, indexes are often used for nonkey attributes, so it is possible that more than one record has a given key value. If ...
... Until this point we have supposed that the search key, upon which the index is based, was also a key of the relation, so there could be at most one recoid with any key value. However, indexes are often used for nonkey attributes, so it is possible that more than one record has a given key value. If ...
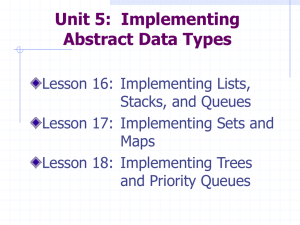
A Practical Introduction to Data Structures and Algorithm Analysis
... A data structure is the physical implementation of an ADT. • Each operation associated with the ADT is implemented by one or more subroutines in the implementation. Data structure usually refers to an organization for data in main memory. File structure: an organization for data on peripheral storag ...
... A data structure is the physical implementation of an ADT. • Each operation associated with the ADT is implemented by one or more subroutines in the implementation. Data structure usually refers to an organization for data in main memory. File structure: an organization for data on peripheral storag ...
Control table

Control tables are tables that control the control flow or play a major part in program control. There are no rigid rules about the structure or content of a control table—its qualifying attribute is its ability to direct control flow in some way through ""execution"" by a processor or interpreter. The design of such tables is sometimes referred to as table-driven design (although this typically refers to generating code automatically from external tables rather than direct run-time tables). In some cases, control tables can be specific implementations of finite-state-machine-based automata-based programming. If there are several hierarchical levels of control table they may behave in a manner equivalent to UML state machinesControl tables often have the equivalent of conditional expressions or function references embedded in them, usually implied by their relative column position in the association list. Control tables reduce the need for programming similar structures or program statements over and over again. The two-dimensional nature of most tables makes them easier to view and update than the one-dimensional nature of program code. In some cases, non-programmers can be assigned to maintain the control tables.