ProSafe VPN Firewall 200 FVX538 Reference Manual
... 1. Redistributions of source code must retain the above copyright notice, this list of conditions, and the following disclaimer. 2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions, and the following disclaimer in the documentation and/or other materi ...
... 1. Redistributions of source code must retain the above copyright notice, this list of conditions, and the following disclaimer. 2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions, and the following disclaimer in the documentation and/or other materi ...
Cisco IOS Switching Services Configuration Guide
... AccessPath, AtmDirector, Browse with Me, CCDA, CCDE, CCDP, CCIE, CCNA, CCNP, CCSI, CD-PAC, CiscoLink, the Cisco NetWorks logo, the Cisco Powered Network logo, Cisco Systems Networking Academy, the Cisco Systems Networking Academy logo, Fast Step, Follow Me Browsing, FormShare, FrameShare, GigaStack, ...
... AccessPath, AtmDirector, Browse with Me, CCDA, CCDE, CCDP, CCIE, CCNA, CCNP, CCSI, CD-PAC, CiscoLink, the Cisco NetWorks logo, the Cisco Powered Network logo, Cisco Systems Networking Academy, the Cisco Systems Networking Academy logo, Fast Step, Follow Me Browsing, FormShare, FrameShare, GigaStack, ...
PDF - Complete Book (2.44 MB)
... www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R) Any Internet Protocol (IP) addresses and phone numbers used in this document a ...
... www.cisco.com/go/trademarks. Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R) Any Internet Protocol (IP) addresses and phone numbers used in this document a ...
ProSafe VPN Firewall 50 FVS338 Reference Manual
... 1. Redistributions of source code must retain the above copyright notice, this list of conditions, and the following disclaimer. 2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions, and the following disclaimer in the documentation and/or other materi ...
... 1. Redistributions of source code must retain the above copyright notice, this list of conditions, and the following disclaimer. 2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions, and the following disclaimer in the documentation and/or other materi ...
multinet_admin_guide.. - PointSecure Development Web Server
... exempt from the restrictions specified in this clause. 8. If the version of a covered source file as you received it, when compiled, would normally produce executable code that would print a copyright message followed by a message referring to an ISC web page or other ISC documentation, you may not ...
... exempt from the restrictions specified in this clause. 8. If the version of a covered source file as you received it, when compiled, would normally produce executable code that would print a copyright message followed by a message referring to an ISC web page or other ISC documentation, you may not ...
PDF - Complete Book (655.0 KB)
... command references, including brief descriptions of the contents of the documents. The Cisco IOS command references are comprehensive, meaning that they include commands for both Cisco IOS software and Cisco IOS XE software, for all releases. The configuration guides and command references support m ...
... command references, including brief descriptions of the contents of the documents. The Cisco IOS command references are comprehensive, meaning that they include commands for both Cisco IOS software and Cisco IOS XE software, for all releases. The configuration guides and command references support m ...
ESBC Administrator`s Guide
... INSTALLING THE ESBC10K SERIES TO AN ENTERPRISE NETWORK ................................................................. 19 ...
... INSTALLING THE ESBC10K SERIES TO AN ENTERPRISE NETWORK ................................................................. 19 ...
PDF version
... Console scripting introduction........................................................................................................35 Command........................................................................................................................................35 Grouping level co ...
... Console scripting introduction........................................................................................................35 Command........................................................................................................................................35 Grouping level co ...
TigerSwitch 10/100/1000 Management Guide
... can be accomplished via the enclosed product registration card or online via the SMC web site. Failure to register will not affect the standard limited warranty. The Limited Lifetime warranty covers a product during the Life of that Product, which is defined as the period of time during which the pr ...
... can be accomplished via the enclosed product registration card or online via the SMC web site. Failure to register will not affect the standard limited warranty. The Limited Lifetime warranty covers a product during the Life of that Product, which is defined as the period of time during which the pr ...
ipv6 technology and dns setup
... enough structure. Since an IPv4 network (class A, B or C) can be located anywhere in the world, backbone routers must maintain a record for every active network. This leads to the huge size of routing tables in the "core gateways", and is on the way to exhausting the maximum table capacity of these ...
... enough structure. Since an IPv4 network (class A, B or C) can be located anywhere in the world, backbone routers must maintain a record for every active network. This leads to the huge size of routing tables in the "core gateways", and is on the way to exhausting the maximum table capacity of these ...
Ip Addressing and Subnetting Workbook
... (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each independent of the other. This can only be accomplished by using a custom subnet mask. A cus ...
... (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each independent of the other. This can only be accomplished by using a custom subnet mask. A cus ...
Ip Addressing and Subnetting Workbook
... (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each independent of the other. This can only be accomplished by using a custom subnet mask. A cus ...
... (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each independent of the other. This can only be accomplished by using a custom subnet mask. A cus ...
Presentation Title Size 30PT
... If students have trouble seeing why only one double colon is allowed, give them an example of what would happen if you allowed it. The following two addresses could both be shortened to the third address, so there would be ambiguity ...
... If students have trouble seeing why only one double colon is allowed, give them an example of what would happen if you allowed it. The following two addresses could both be shortened to the third address, so there would be ambiguity ...
Ip Addressing and Subnetting Workbook
... (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each independent of the other. This can only be accomplished by using a custom subnet mask. A cus ...
... (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five smaller subnetworks. Each independent of the other. This can only be accomplished by using a custom subnet mask. A cus ...
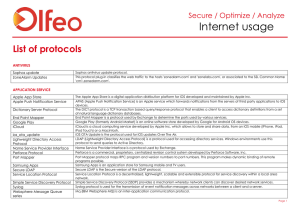
Protocols List
... LDAP (Lightweight Directory Access Protocol) is a protocol used for accessing directory services. Windows environments use this protocol to send queries to Active Directory. Name Service Provider Interface is a protocol used by Exchange. Perforce is a commercial, proprietary, centralized revision co ...
... LDAP (Lightweight Directory Access Protocol) is a protocol used for accessing directory services. Windows environments use this protocol to send queries to Active Directory. Name Service Provider Interface is a protocol used by Exchange. Perforce is a commercial, proprietary, centralized revision co ...
The Second Internet
... This book is published under a Creative Commons License, which can be referenced at http://creativecommons.org/licenses/by-nd/3.0/us/. In short, the terms of this license are as follows: You can share (copy, distribute and/or transmit) machine readable copies of this work. At most there should be mi ...
... This book is published under a Creative Commons License, which can be referenced at http://creativecommons.org/licenses/by-nd/3.0/us/. In short, the terms of this license are as follows: You can share (copy, distribute and/or transmit) machine readable copies of this work. At most there should be mi ...
OSPF
... determining the best route – The best route will have the lowest cost – Cost is based on bandwidth of an interface • Cost is calculated using the formula – 108 / bandwidth – Reference bandwidth • Defaults to 100Mbps • Can be modified using • Auto-cost reference-bandwidth command ...
... determining the best route – The best route will have the lowest cost – Cost is based on bandwidth of an interface • Cost is calculated using the formula – 108 / bandwidth – Reference bandwidth • Defaults to 100Mbps • Can be modified using • Auto-cost reference-bandwidth command ...
Lawrence E. Hughes - The Second Internet
... This book is published under a Creative Commons License, which can be referenced at http://creativecommons.org/licenses/by-nd/3.0/us/ In short, the terms of this license are as follows: You can share (copy, distribute and/or transmit) machine readable copies of this work. At most there should be min ...
... This book is published under a Creative Commons License, which can be referenced at http://creativecommons.org/licenses/by-nd/3.0/us/ In short, the terms of this license are as follows: You can share (copy, distribute and/or transmit) machine readable copies of this work. At most there should be min ...
HERE - Lobometrics High Power Outdoor/Indoor Wireless
... There is an interface list in this submenu level. If you add some interfaces to this list, you allow MAC telnet to that interface. Disabled (disabled=yes) item means that interface is not allowed to accept MAC telnet sessions on that interface. ...
... There is an interface list in this submenu level. If you add some interfaces to this list, you allow MAC telnet to that interface. Disabled (disabled=yes) item means that interface is not allowed to accept MAC telnet sessions on that interface. ...
CISCO CATALYST 3750 SERIES SWITCHES
... The automatic Cisco IOS Software version checking and loading of the global configuration parameters provide the first level of operational time saving. The second level is added during the event of an outage. When you remove a troubled switch from an existing stack of switches, and replace it with ...
... The automatic Cisco IOS Software version checking and loading of the global configuration parameters provide the first level of operational time saving. The second level is added during the event of an outage. When you remove a troubled switch from an existing stack of switches, and replace it with ...
General Information - HauteSpot Networks
... General Information .........................................................................................................................................................125 Logging into the HauteSpot Router ......................................................................................... ...
... General Information .........................................................................................................................................................125 Logging into the HauteSpot Router ......................................................................................... ...
DHCP
... The objective of this presentation is to provide a high-level overview of DHCP in the network infrastructure At the end of this presentation, you will be able to: ...
... The objective of this presentation is to provide a high-level overview of DHCP in the network infrastructure At the end of this presentation, you will be able to: ...
Cisco Industrial Ethernet 3000 Layer 2/Layer 3 Series Switches Data
... ● Cisco Express Setup simplifies initial configuration with a web browser, eliminating the need for more complex terminal emulation programs. ● Cisco Smartports templates provide the option to apply a default global or interface-level macro with a recommended configuration, allowing the user to easi ...
... ● Cisco Express Setup simplifies initial configuration with a web browser, eliminating the need for more complex terminal emulation programs. ● Cisco Smartports templates provide the option to apply a default global or interface-level macro with a recommended configuration, allowing the user to easi ...
Lenovo Network Application Guide for Lenovo Cloud Network
... © Copyright Lenovo 2016 Portions © Copyright IBM Corporation 2014. LIMITED AND RESTRICTED RIGHTS NOTICE: If data or software is delivered pursuant a General Services Administration “GSA” contract, use, reproduction, or disclosure is subject to restrictions set forth in Contract No. GS-35F-05925. Len ...
... © Copyright Lenovo 2016 Portions © Copyright IBM Corporation 2014. LIMITED AND RESTRICTED RIGHTS NOTICE: If data or software is delivered pursuant a General Services Administration “GSA” contract, use, reproduction, or disclosure is subject to restrictions set forth in Contract No. GS-35F-05925. Len ...
SpeedStream™ Router Family
... Efficient Networks provides this publication Òas isÓ without warranty of any kind, either expressed or implied, including, but not limited to, the implied warranties of merchantability or fitness for a particular purpose. All rights reserved. No part of this book may be reproduced in any form or by ...
... Efficient Networks provides this publication Òas isÓ without warranty of any kind, either expressed or implied, including, but not limited to, the implied warranties of merchantability or fitness for a particular purpose. All rights reserved. No part of this book may be reproduced in any form or by ...