Kernel Data Structures
... search of Linux’s page cache for a chunk of a file Each inode has its own rbtree, keyed off of page offsets into file This function thus searches the given inode’s rbtree for a matching offset ...
... search of Linux’s page cache for a chunk of a file Each inode has its own rbtree, keyed off of page offsets into file This function thus searches the given inode’s rbtree for a matching offset ...
Minimum Bounding Boxes
... each edge there are 3 two-dimensional planes in which the minimum bounding boxes can be placed. Each minimum bounding box has n possible rotations, giving us an overall complexity of O(n3) running time to find a minimum volume bounding box in three dimensions. Minimum bounding boxes are often used a ...
... each edge there are 3 two-dimensional planes in which the minimum bounding boxes can be placed. Each minimum bounding box has n possible rotations, giving us an overall complexity of O(n3) running time to find a minimum volume bounding box in three dimensions. Minimum bounding boxes are often used a ...
Fundamental Data Structures
... In computer science, an abstract data type (ADT) is a mathematical model for a certain class of data structures that have similar behavior; or for certain data types of one or more programming languages that have similar semantics. An abstract data type is defined indirectly, only by the operations ...
... In computer science, an abstract data type (ADT) is a mathematical model for a certain class of data structures that have similar behavior; or for certain data types of one or more programming languages that have similar semantics. An abstract data type is defined indirectly, only by the operations ...
ch12
... Before and after deleting “Downtown” The removal of the leaf node containing “Downtown” did not result in its parent having too little pointers. So the cascaded deletions stopped with the deleted leaf node’s parent. Database System Concepts - 5th Edition, Aug 12, 2005. ...
... Before and after deleting “Downtown” The removal of the leaf node containing “Downtown” did not result in its parent having too little pointers. So the cascaded deletions stopped with the deleted leaf node’s parent. Database System Concepts - 5th Edition, Aug 12, 2005. ...
Data Structures and Algorithms for Data
... operations that augment collection libraries in many languages today. Data collection operations like reduction, filtering or mapping can be executed by a single processor or many processors at once. However, there are multiple challenges to overcome when parallelizing collection operations. First, ...
... operations that augment collection libraries in many languages today. Data collection operations like reduction, filtering or mapping can be executed by a single processor or many processors at once. However, there are multiple challenges to overcome when parallelizing collection operations. First, ...
space-efficient data structures for string searching and retrieval
... decomposed into O(p) subproblems, each of them are 3-sided range reporting queries in 2d (which can be solved optimally). This inevitably adds an additive O(p) term in the query time, however it will not change the query time as O(p) time is needed for initial pattern search using suffix tree. Histo ...
... decomposed into O(p) subproblems, each of them are 3-sided range reporting queries in 2d (which can be solved optimally). This inevitably adds an additive O(p) term in the query time, however it will not change the query time as O(p) time is needed for initial pattern search using suffix tree. Histo ...
Chapter 8 DYNAMIC DATA STRUCTURES AND LISTS 8.1 Pointers
... -----------------------------------------Often more than one pointer will point to the same object. For this reason, you must be careful when returning the storage occupied by a record to the heap. If memory is reallocated after it is returned, errors may result. Make sure that you have no need for ...
... -----------------------------------------Often more than one pointer will point to the same object. For this reason, you must be careful when returning the storage occupied by a record to the heap. If memory is reallocated after it is returned, errors may result. Make sure that you have no need for ...
CHAPTER 18 Linked Lists, Stacks, Queues, and Priority
... introduces linked lists. A linked list can be used just like a list. The difference lies in performance. Using linked lists is more efficient for inserting and removing elements from the beginning of the list than using a list. Using a list is more efficient for retrieving an element via an index th ...
... introduces linked lists. A linked list can be used just like a list. The difference lies in performance. Using linked lists is more efficient for inserting and removing elements from the beginning of the list than using a list. Using a list is more efficient for retrieving an element via an index th ...
Fundamental Data Structures - University of North Florida
... In computing, an abstract data type (ADT) is a mathematical model for a certain class of data structures that have similar behavior; or for certain data types of one or more programming languages that have similar semantics. An abstract data type is defined indirectly, only by the operations that ma ...
... In computing, an abstract data type (ADT) is a mathematical model for a certain class of data structures that have similar behavior; or for certain data types of one or more programming languages that have similar semantics. An abstract data type is defined indirectly, only by the operations that ma ...
Chapter 11: Indexing and Hashing
... Search-keys in the subtree to which Pi points are ≤ Ki,, but not necessarily < Ki, To see why, suppose same search key value V is present in two leaf node Li and Li+1. Then in parent node Ki must be equal to V ...
... Search-keys in the subtree to which Pi points are ≤ Ki,, but not necessarily < Ki, To see why, suppose same search key value V is present in two leaf node Li and Li+1. Then in parent node Ki must be equal to V ...
COMP 202 The Linked List Static vs. Dynamic Structures Object
... – Structures that can be built (or re-formed) at run-time (called dynamic structures) ...
... – Structures that can be built (or re-formed) at run-time (called dynamic structures) ...
Improving the efficiency of priority-queue structures
... the same asymptotical bound in the worst-case sense as binomial queues and the comparison complexity of delete is 3 lg n + O(1) given that find -min has the worst-case cost of O(1). Similar to binomial queues the basic components of run-relaxed heaps are binomial trees. Apart from the differences in ...
... the same asymptotical bound in the worst-case sense as binomial queues and the comparison complexity of delete is 3 lg n + O(1) given that find -min has the worst-case cost of O(1). Similar to binomial queues the basic components of run-relaxed heaps are binomial trees. Apart from the differences in ...
Paper
... tree by replacing three edges at a saddle point with a single new edge, based on the height of the edge. [Takahashi et al. 2004b] use the approximate volume of the region represented by the subtree that is discarded. Saddles are processed until only a few remain, then a transfer function is construc ...
... tree by replacing three edges at a saddle point with a single new edge, based on the height of the edge. [Takahashi et al. 2004b] use the approximate volume of the region represented by the subtree that is discarded. Saddles are processed until only a few remain, then a transfer function is construc ...
Worst Case Efficient Data Structures
... arrays of size O(log n). Our bounds match the best known amortized bounds (achieved by respectively binomial queues and Fibonacci heaps). The data structures presented are the first achieving these worst case bounds, in particular supporting Meld in worst case constant time. We show that these time ...
... arrays of size O(log n). Our bounds match the best known amortized bounds (achieved by respectively binomial queues and Fibonacci heaps). The data structures presented are the first achieving these worst case bounds, in particular supporting Meld in worst case constant time. We show that these time ...
Interfaces
... message, the object is using its own internal state (instances variables). Because an object sends messages to itself so frequently, Java provides a shortcut: this and the dot are not really necessary before the method name. Whereas the keyword this is sometimes required, it was not really necessary ...
... message, the object is using its own internal state (instances variables). Because an object sends messages to itself so frequently, Java provides a shortcut: this and the dot are not really necessary before the method name. Whereas the keyword this is sometimes required, it was not really necessary ...
Indexing Structures for Searching in Metric Spaces
... In some applications, the metric space turns out to be of a particular type called vector space, where the elements consist of k coordinates (often termed feature vectors). For example, images are often represented by color and shape histograms [38, 48], typically consisting of 64 or 256 values. A l ...
... In some applications, the metric space turns out to be of a particular type called vector space, where the elements consist of k coordinates (often termed feature vectors). For example, images are often represented by color and shape histograms [38, 48], typically consisting of 64 or 256 values. A l ...
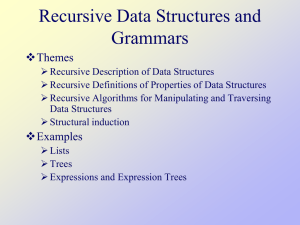
recdata
... Proof of Property 3 Show (append x (append y z)) = (append (append x y) z) Base case. x = nil. (append nil (append y z)) = (append y z) = (append (append nil y) z) Assume property holds for (rest x) (append (append x y) z) (append (cons (first x) (append (rest x) y)) z) [by def] (cons (fir ...
... Proof of Property 3 Show (append x (append y z)) = (append (append x y) z) Base case. x = nil. (append nil (append y z)) = (append y z) = (append (append nil y) z) Assume property holds for (rest x) (append (append x y) z) (append (cons (first x) (append (rest x) y)) z) [by def] (cons (fir ...