Chapter 2: Advanced Data Structures
... do x.keyj+1 = x.keyj for j = 1 to t − 1 x.keyi = y.keyt do z.keyj = y.keyj+t x.n = x.n + 1 if not y.leaf DISK-WRITE(y) then for j = 1 to t DISK-WRITE(z) do z.cj = y.cj+t y.n = t − 1 DISK-WRITE(x) ...
... do x.keyj+1 = x.keyj for j = 1 to t − 1 x.keyi = y.keyt do z.keyj = y.keyj+t x.n = x.n + 1 if not y.leaf DISK-WRITE(y) then for j = 1 to t DISK-WRITE(z) do z.cj = y.cj+t y.n = t − 1 DISK-WRITE(x) ...
Optimal Dynamic Sequence Representations
... 3.1 Structure We assume that the wavelet tree T has node degree ρ = Θ(lgε n). We divide sets B(v) into blocks and store those blocks in a doubly-linked list L(v). Each block Gj (v), except the last one, contains Θ(lg3 n) consecutive elements from B(v); the last block contains O(lg3 n) consecutive e ...
... 3.1 Structure We assume that the wavelet tree T has node degree ρ = Θ(lgε n). We divide sets B(v) into blocks and store those blocks in a doubly-linked list L(v). Each block Gj (v), except the last one, contains Θ(lg3 n) consecutive elements from B(v); the last block contains O(lg3 n) consecutive e ...
Binary Trees
... • An empty tree has height 0, and a tree of height 1 consists of a single node which is both the tree’s root and leaf • The level of a node must be between 1 and the tree’s height • Some examples of trees are shown in Figure 6.1 ...
... • An empty tree has height 0, and a tree of height 1 consists of a single node which is both the tree’s root and leaf • The level of a node must be between 1 and the tree’s height • Some examples of trees are shown in Figure 6.1 ...
Basic Data Structures
... A tree in which each node has out-degree 0, 1, or 2 is called a binary tree. ...
... A tree in which each node has out-degree 0, 1, or 2 is called a binary tree. ...
BINARY TREES AND HEAPS IN JAVA
... The procedure starts by swapping it with the last element on the last level. So, if we have the same max-heap as before, we remove the 11 and replace it with the 4 Now the heap property is violated since 8 is greater than 4. The operation that restores the property is called sift-down. In this case, ...
... The procedure starts by swapping it with the last element on the last level. So, if we have the same max-heap as before, we remove the 11 and replace it with the 4 Now the heap property is violated since 8 is greater than 4. The operation that restores the property is called sift-down. In this case, ...
linked list
... We will now examine linked list operations: • Add an item to the linked list • We have 3 situations to consider: • insert a node at the front • insert a node in the middle • insert a node at the end • Delete an item from the linked list • We have 3 situations to consider: • delete the node at the fr ...
... We will now examine linked list operations: • Add an item to the linked list • We have 3 situations to consider: • insert a node at the front • insert a node in the middle • insert a node at the end • Delete an item from the linked list • We have 3 situations to consider: • delete the node at the fr ...
Document
... • ChildCut of node x is TRUE iff one of the children of node x was cut off after the most recent time x was made the child of its current parent. • Whenever a delete or decrease-key operation deletes a node q that is not a min tree root from its doubly linked list, then the cascading cut step is inv ...
... • ChildCut of node x is TRUE iff one of the children of node x was cut off after the most recent time x was made the child of its current parent. • Whenever a delete or decrease-key operation deletes a node q that is not a min tree root from its doubly linked list, then the cascading cut step is inv ...
XFastMesh: Fast View-dependent Meshing from External Memory
... merge-tree hierarchy is regularly partitioned into binary subtrees as shown in Figure 5. Within each detail block, explicit links between nodes are minimized using an array representation of the complete binary subtree. Tree nodes are numbered and stored in a breath-first ordering such that given th ...
... merge-tree hierarchy is regularly partitioned into binary subtrees as shown in Figure 5. Within each detail block, explicit links between nodes are minimized using an array representation of the complete binary subtree. Tree nodes are numbered and stored in a breath-first ordering such that given th ...
Heaps - COW :: Ceng
... between 2h and 2h+1 – 1 nodes • The height of a complete binary tree is log N. • It can be implemented as an array such that: – For any element in array position i : • the left child is in position 2i, • the right child is in the cell after the left child (2i + 1), and • the parent is in position ...
... between 2h and 2h+1 – 1 nodes • The height of a complete binary tree is log N. • It can be implemented as an array such that: – For any element in array position i : • the left child is in position 2i, • the right child is in the cell after the left child (2i + 1), and • the parent is in position ...
AN OVERVIEW OF HIERARCHICAL SPATIAL DATA STRUCTURES
... The term quadtree is used to describe a class of hierarchical data structures whose common property is that they are based on the principle of recursive decomposition of space. They can be differentiated on the following bases: (1) the type of data that they are used to represent, (2) the principle ...
... The term quadtree is used to describe a class of hierarchical data structures whose common property is that they are based on the principle of recursive decomposition of space. They can be differentiated on the following bases: (1) the type of data that they are used to represent, (2) the principle ...
・ P Q RIORITY
... handled in a separate dictionary [2, 17] such as a hashtable or a balanced tree. If deletions are restricted to elements extracted by MIN, such an auxiliary symbol table is not needed. 1 The heap, a truly elegant data structure discovered by J. W. Williams and R. W. Floyd, handles a sequence of n pr ...
... handled in a separate dictionary [2, 17] such as a hashtable or a balanced tree. If deletions are restricted to elements extracted by MIN, such an auxiliary symbol table is not needed. 1 The heap, a truly elegant data structure discovered by J. W. Williams and R. W. Floyd, handles a sequence of n pr ...
Linked Lists
... – Call isEmpty to determine whether the list is empty – If the list is empty, assign firstNode and lastNode to the new ListNode that was initialized with insertItem • The ListNode constructor call sets data to refer to the insertItem passed as an argument and sets reference nextNode to null – If the ...
... – Call isEmpty to determine whether the list is empty – If the list is empty, assign firstNode and lastNode to the new ListNode that was initialized with insertItem • The ListNode constructor call sets data to refer to the insertItem passed as an argument and sets reference nextNode to null – If the ...
Index Structures for Files Multi-Level Indexes Multi
... Splitting and Promoting The single leaf we have is full, so we split the leaf into two leaves, distributing the keys as evenly as possible between the old leaf node and the new one, using one key to split the keys ...
... Splitting and Promoting The single leaf we have is full, so we split the leaf into two leaves, distributing the keys as evenly as possible between the old leaf node and the new one, using one key to split the keys ...
The ADT Heap
... unordered array, do we have any sub-trees which are heaps? If we look at the leaves of the tree, these are certainly heaps, as they don’t have any children. So if we start from the leaves of the complete binary tree representation of our initial array, we could recursively apply the procedure heapRe ...
... unordered array, do we have any sub-trees which are heaps? If we look at the leaves of the tree, these are certainly heaps, as they don’t have any children. So if we start from the leaves of the complete binary tree representation of our initial array, we could recursively apply the procedure heapRe ...
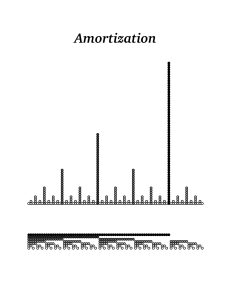
Amortization - Jeff Erickson
... A nice alternative is represent each integer as a pair (P, N ) of bit strings, subject to the invariant P ∧ N = 0 where ∧ represents bit-wise And. In other words, For every index i, at most one of the bits P[i] and N [i] is equal to 1. If we interpret P and N as binary numbers, the actual value of t ...
... A nice alternative is represent each integer as a pair (P, N ) of bit strings, subject to the invariant P ∧ N = 0 where ∧ represents bit-wise And. In other words, For every index i, at most one of the bits P[i] and N [i] is equal to 1. If we interpret P and N as binary numbers, the actual value of t ...
Slides for Linked List
... Recall: Array Representation of Sequences Requires an estimate of the maximum size of the list waste space + always need to track/update “size” insert and delete: have prohibitive overheads when the sequences are sorted (or, if we insist on inserting at a given ...
... Recall: Array Representation of Sequences Requires an estimate of the maximum size of the list waste space + always need to track/update “size” insert and delete: have prohibitive overheads when the sequences are sorted (or, if we insist on inserting at a given ...
Dr-Margush-06-07_LinkedLists
... • Implements List, Cloneable, Serializable • Uses a doubly-linked list backing store • Includes special methods that take advantage of linked list structure ...
... • Implements List, Cloneable, Serializable • Uses a doubly-linked list backing store • Includes special methods that take advantage of linked list structure ...
Data structure - E
... 32.Nodes that have degree zero are called ______ nodes. 33.The method of maintaining a file and index is referred to as ____. 34.In ______ method the identifier X is partitioned into several parts, all but the last being of the same length. These parts are then added together to obtain the hash addr ...
... 32.Nodes that have degree zero are called ______ nodes. 33.The method of maintaining a file and index is referred to as ____. 34.In ______ method the identifier X is partitioned into several parts, all but the last being of the same length. These parts are then added together to obtain the hash addr ...
MemPick: High-Level Data Structure Detection in C/C++
... Observe that not every snapshot of the memory graph is suitable for shape analysis. The problem is that properties characteristic to a data structure are not necessarily maintained at each and every point of the execution. For example, if an application uses a red-black tree, the tree is often not b ...
... Observe that not every snapshot of the memory graph is suitable for shape analysis. The problem is that properties characteristic to a data structure are not necessarily maintained at each and every point of the execution. For example, if an application uses a red-black tree, the tree is often not b ...
2011
... Write a pseudo code to add a node in the linked list at the end of the linked list. Write a pseudo code to add a node at the front of the linked list. Write a pseudo code to add a node at particular position in the linked list. Write a pseudo code to add a node after particular node. Write a pseudo ...
... Write a pseudo code to add a node in the linked list at the end of the linked list. Write a pseudo code to add a node at the front of the linked list. Write a pseudo code to add a node at particular position in the linked list. Write a pseudo code to add a node after particular node. Write a pseudo ...
Searching: Binary Trees and Hash Tables
... – a finite set of elements called nodes or vertices – a finite set of directed arcs which connect the nodes ...
... – a finite set of elements called nodes or vertices – a finite set of directed arcs which connect the nodes ...
Stacks Stack Abstract Data Type Stack (supporting methods) Stack
... List ADT (sequence of elements) first() : return the position of the first element; error occurs if list S is empty last() : return the position of the last element; error occurs if S is empty isFirst() : return a Boolean indicating whether the given position is the first one isLast() : return a Boo ...
... List ADT (sequence of elements) first() : return the position of the first element; error occurs if list S is empty last() : return the position of the last element; error occurs if S is empty isFirst() : return a Boolean indicating whether the given position is the first one isLast() : return a Boo ...
linked list
... We will now examine linked list operations: • Add an item to the linked list • We have 3 situations to consider: • insert a node at the front • insert a node in the middle • insert a node at the end • Delete an item from the linked list • We have 3 situations to consider: • delete the node at the fr ...
... We will now examine linked list operations: • Add an item to the linked list • We have 3 situations to consider: • insert a node at the front • insert a node in the middle • insert a node at the end • Delete an item from the linked list • We have 3 situations to consider: • delete the node at the fr ...
linked list
... We will now examine linked list operations: • Add an item to the linked list • We have 3 situations to consider: • insert a node at the front • insert a node in the middle • insert a node at the end • Delete an item from the linked list • We have 3 situations to consider: • delete the node at the fr ...
... We will now examine linked list operations: • Add an item to the linked list • We have 3 situations to consider: • insert a node at the front • insert a node in the middle • insert a node at the end • Delete an item from the linked list • We have 3 situations to consider: • delete the node at the fr ...
Binary tree
In computer science, a binary tree is a tree data structure in which each node has at most two children, which are referred to as the left child and the right child. A recursive definition using just set theory notions is that a (non-empty) binary tree is a triple (L, S, R), where L and R are binary trees or the empty set and S is a singleton set. Some authors allow the binary tree to be the empty set as well.From a graph theory perspective, binary (and K-ary) trees as defined here are actually arborescences. A binary tree may thus be also called a bifurcating arborescence—a term which actually appears in some very old programming books, before the modern computer science terminology prevailed. It is also possible to interpret a binary tree as an undirected, rather than a directed graph, in which case a binary tree is an ordered, rooted tree. Some authors use rooted binary tree instead of binary tree to emphasize the fact that the tree is rooted, but as defined above, a binary tree is always rooted. A binary tree is a special case of an ordered K-ary tree, where k is 2.In computing, binary trees are seldom used solely for their structure. Much more typical is to define a labeling function on the nodes, which associates some value to each node. Binary trees labelled this way are used to implement binary search trees and binary heaps, and are used for efficient searching and sorting. The designation of non-root nodes as left or right child even when there is only one child present matters in some of these applications, in particular it is significant in binary search trees. In mathematics, what is termed binary tree can vary significantly from author to author. Some use the definition commonly used in computer science, but others define it as every non-leaf having exactly two children and don't necessarily order (as left/right) the children either.