The Data-Link Layer: Access Networks and Lans (Abridged Version)
... encapsulate datagram into frame, adding header, trailer channel access if shared medium “MAC” addresses used in frame headers to identify source, dest • different from IP address! ...
... encapsulate datagram into frame, adding header, trailer channel access if shared medium “MAC” addresses used in frame headers to identify source, dest • different from IP address! ...
E1922
... communication session, it initiates a path-discovery process to locate the other node. The source node broadcasts a RREQ packet with its IP address, Broadcast ID (BrID), and the sequence number of the source and destination . While, the BrID and the IP address is used to uniquely identify each reque ...
... communication session, it initiates a path-discovery process to locate the other node. The source node broadcasts a RREQ packet with its IP address, Broadcast ID (BrID), and the sequence number of the source and destination . While, the BrID and the IP address is used to uniquely identify each reque ...
3rd Edition, Chapter 5
... 7 bytes with pattern 10101010 followed by one byte with pattern 10101011 used to synchronize receiver, sender clock rates ...
... 7 bytes with pattern 10101010 followed by one byte with pattern 10101011 used to synchronize receiver, sender clock rates ...
Figure 2.1 Communication requires a message, a transmitter, a
... Systems Interconnect (OSI) model. ...
... Systems Interconnect (OSI) model. ...
TAP 129- 3: Analysing the discharge of a capacitor
... Use automated data capture to study the decay of potential difference across the terminals of a capacitor as it discharges through a resistor. The exact procedure will have to be modified depending on what software is available with your particular data capture and analysis package. If you are handi ...
... Use automated data capture to study the decay of potential difference across the terminals of a capacitor as it discharges through a resistor. The exact procedure will have to be modified depending on what software is available with your particular data capture and analysis package. If you are handi ...
cs6551 computer networks - MET Engineering College
... The first 3 bytes of each row are overhead, with the rest being available for data The first 2 bytes of the frame contain a special bit pattern indicating start of frame. Bit stuffing is not employed here The receiver looks for the special bit pattern once in every 810 bytes. If not so, the frame is ...
... The first 3 bytes of each row are overhead, with the rest being available for data The first 2 bytes of the frame contain a special bit pattern indicating start of frame. Bit stuffing is not employed here The receiver looks for the special bit pattern once in every 810 bytes. If not so, the frame is ...
Touch Screen Technology
... Mutual capacitance or self capacitance. In mutual capacitance, the capacitive circuitry requires two distinct layers of material. One houses driving lines, which carry current, and the other houses sensing lines, which detect the current at nodes. Self capacitance uses one layer of individual e ...
... Mutual capacitance or self capacitance. In mutual capacitance, the capacitive circuitry requires two distinct layers of material. One houses driving lines, which carry current, and the other houses sensing lines, which detect the current at nodes. Self capacitance uses one layer of individual e ...
TAP 129- 3: Analysing the discharge of a capacitor
... Use automated data capture to study the decay of potential difference across the terminals of a capacitor as it discharges through a resistor. The exact procedure will have to be modified depending on what software is available with your particular data capture and analysis package. If you are handi ...
... Use automated data capture to study the decay of potential difference across the terminals of a capacitor as it discharges through a resistor. The exact procedure will have to be modified depending on what software is available with your particular data capture and analysis package. If you are handi ...
Part I: Introduction
... client host requests, receives service from always-on server e.g. Web browser/server; email client/server ...
... client host requests, receives service from always-on server e.g. Web browser/server; email client/server ...
The Data-Link Layer: Access Networks and Lans (Abridged Version)
... encapsulate datagram into frame, adding header, trailer channel access if shared medium “MAC” addresses used in frame headers to identify source, dest • different from IP address! ...
... encapsulate datagram into frame, adding header, trailer channel access if shared medium “MAC” addresses used in frame headers to identify source, dest • different from IP address! ...
Network Layer
... identifier for host, router interface interface: connection between host/router and physical link ...
... identifier for host, router interface interface: connection between host/router and physical link ...
PPT
... • Tests status of link to each neighbor. Sends status info on link availability to neighbors. • Cost can be assigned on reliability & time ...
... • Tests status of link to each neighbor. Sends status info on link availability to neighbors. • Cost can be assigned on reliability & time ...
Slide 1
... • Tests status of link to each neighbor. Sends status info on link availability to neighbors. • Cost can be assigned on reliability & time ...
... • Tests status of link to each neighbor. Sends status info on link availability to neighbors. • Cost can be assigned on reliability & time ...
Slide 1
... – Sometimes referred to as the Packet Length. – Defines the entire packet (fragment) size, including header and data, in bytes. – The minimum length packet is 20 bytes (20-byte header + 0 bytes data) and the maximum is 65,535 bytes. . ...
... – Sometimes referred to as the Packet Length. – Defines the entire packet (fragment) size, including header and data, in bytes. – The minimum length packet is 20 bytes (20-byte header + 0 bytes data) and the maximum is 65,535 bytes. . ...
MQ3624532158
... form a totally improvised network that does not require any pre-established infrastructure. But, how can we make this possible The answer is very simple. Each node acts as a host and a router at the same time. This means that each node participating in a MANET commits itself to forward data packets ...
... form a totally improvised network that does not require any pre-established infrastructure. But, how can we make this possible The answer is very simple. Each node acts as a host and a router at the same time. This means that each node participating in a MANET commits itself to forward data packets ...
Semester 3 Chapter 1 - IIS Windows Server
... Data-Link then encaps. the packet in a frame and addresses it for local ...
... Data-Link then encaps. the packet in a frame and addresses it for local ...
IP Basics
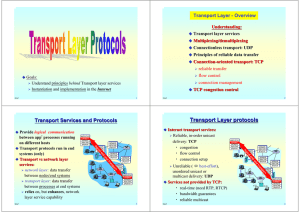
... Generally, TCP/IP (Transmission Control Protocol/Internet Protocol) is described using three to five functional layers. We have chosen the common DoD reference model, which is also known as the Internet reference model. • Process/Application Layer consists of applications and processes that use the ...
... Generally, TCP/IP (Transmission Control Protocol/Internet Protocol) is described using three to five functional layers. We have chosen the common DoD reference model, which is also known as the Internet reference model. • Process/Application Layer consists of applications and processes that use the ...
Chapter 1 Fundamentals
... Low overhead for bursty long-lived or short-lived connectivity End-to-end instead of hop-by-hop Don’t put it in a lower layer if it cannot be completely done there! Hop-by-hop only for performance optimization ...
... Low overhead for bursty long-lived or short-lived connectivity End-to-end instead of hop-by-hop Don’t put it in a lower layer if it cannot be completely done there! Hop-by-hop only for performance optimization ...
Chapter 1 Fundamentals
... Low overhead for bursty long-lived or short-lived connectivity End-to-end instead of hop-by-hop Don’t put it in a lower layer if it cannot be completely done there! Hop-by-hop only for performance optimization ...
... Low overhead for bursty long-lived or short-lived connectivity End-to-end instead of hop-by-hop Don’t put it in a lower layer if it cannot be completely done there! Hop-by-hop only for performance optimization ...
Single Serial Input PLL Frequency Synthesizer
... 10µA (max.). Setting PS pin to High, power saving mode is released so that the IC works normally. In addition, the intermittent operation control circuit is included which helps smooth start up from the power saving mode. In general, the power consumption can be saved by the intermittent operation t ...
... 10µA (max.). Setting PS pin to High, power saving mode is released so that the IC works normally. In addition, the intermittent operation control circuit is included which helps smooth start up from the power saving mode. In general, the power consumption can be saved by the intermittent operation t ...