presentation
... Problem: The VISIT dataset with 901128 records with keys of TRIALNO and VISIT. There is a “lookup” dataset which contains visit descriptions. This is VISDESC, again with keys TRIALNO and VISIT and consists of 1049 records. The goal is to merge these two files together to pick up the visit label VISI ...
... Problem: The VISIT dataset with 901128 records with keys of TRIALNO and VISIT. There is a “lookup” dataset which contains visit descriptions. This is VISDESC, again with keys TRIALNO and VISIT and consists of 1049 records. The goal is to merge these two files together to pick up the visit label VISI ...
ppt
... pass an array into a function can change its value (will explain this later) int split(int a[], int low, int high); // return the position of the pivot after the split void quicksort(int a[], int ...
... pass an array into a function can change its value (will explain this later) int split(int a[], int low, int high); // return the position of the pivot after the split void quicksort(int a[], int ...
exam solutions
... algorithm and then doing busy-work to consume the remaining time will not receive credit. Hint: Use standard data structures and sorting techniques. a. Print the duplicates in time O(n2). Is the time bound for your algorithm expected or worstcase? Use nested for-loops to compare all pairs of numbers ...
... algorithm and then doing busy-work to consume the remaining time will not receive credit. Hint: Use standard data structures and sorting techniques. a. Print the duplicates in time O(n2). Is the time bound for your algorithm expected or worstcase? Use nested for-loops to compare all pairs of numbers ...
Finding a Square Root Using an Algorithm
... The use of this method, similar to long division, diminished with the advent of calculators. This pencil-and-paper method works well if you cannot use a calculator, especially if your number is large and you need your answer to several decimal places. The guess-and-check method then becomes time-con ...
... The use of this method, similar to long division, diminished with the advent of calculators. This pencil-and-paper method works well if you cannot use a calculator, especially if your number is large and you need your answer to several decimal places. The guess-and-check method then becomes time-con ...
File
... When searching for the number 62, give the value of the middle, upper and lower variables after the second pass. ...
... When searching for the number 62, give the value of the middle, upper and lower variables after the second pass. ...
Lecture 11: Algorithms - United International College
... • Bubble sort is one of the simplest sorting algorithms, but not one of the most efficient. The smaller elements “bubble” to the top ,the larger elements “sink” to the bottom. • The Bubble sort algorithm: Procedure bubblesort(a1,…,an :real numbers with n>=2) for i:=1 to n-1 for j=1 to n-I if aj > aj ...
... • Bubble sort is one of the simplest sorting algorithms, but not one of the most efficient. The smaller elements “bubble” to the top ,the larger elements “sink” to the bottom. • The Bubble sort algorithm: Procedure bubblesort(a1,…,an :real numbers with n>=2) for i:=1 to n-1 for j=1 to n-I if aj > aj ...
T(n)
... This merge procedure does a constant amount of work per recursive call (provided the required array space is allocated in advance), for a total running time of O(k + m). ...
... This merge procedure does a constant amount of work per recursive call (provided the required array space is allocated in advance), for a total running time of O(k + m). ...
P2 - CEMC
... 2178, 2277, 2376, 2475. So, for the multiples from 11 × 99 to 20 × 99, the patterns are: • the ones digit decreases by 1 with each multiple, going from 9 to 0; • the tens digit remains 8; • the hundreds digit increases by 1, going from 0 to 9; • the thousands digit remains 1 in each multiple. 2. Fro ...
... 2178, 2277, 2376, 2475. So, for the multiples from 11 × 99 to 20 × 99, the patterns are: • the ones digit decreases by 1 with each multiple, going from 9 to 0; • the tens digit remains 8; • the hundreds digit increases by 1, going from 0 to 9; • the thousands digit remains 1 in each multiple. 2. Fro ...
Analysis of Algorithms Background Asymptotic Analysis Worst
... Just as Big O notation provides an asymptotic upper bound on a function, notation provides an asymptotic lower bound Notation can be useful when we have lower bound on time complexity of an algorithm For a given function g(n), we denote by (g(n)) the set of functions (g(n)) = { f(n): there e ...
... Just as Big O notation provides an asymptotic upper bound on a function, notation provides an asymptotic lower bound Notation can be useful when we have lower bound on time complexity of an algorithm For a given function g(n), we denote by (g(n)) the set of functions (g(n)) = { f(n): there e ...
CIS 265/506 Midterm Review
... 4. String class: in java.lang package; creating a String using new operator and String constructor, and “shortcut” way for creating a String without using new operator. 5. Comparing Strings: == vs. equals method; other String methods: charAt, compareTo, indexOf, concat, toUpper, toLower, substring ( ...
... 4. String class: in java.lang package; creating a String using new operator and String constructor, and “shortcut” way for creating a String without using new operator. 5. Comparing Strings: == vs. equals method; other String methods: charAt, compareTo, indexOf, concat, toUpper, toLower, substring ( ...
Course Plan
... *. Suppose Davis is to be inserted into the array. How many names must be moved to new locations? *. Suppose Gupta is to be deleted from the array. How many names must be moved to new locations? ...
... *. Suppose Davis is to be inserted into the array. How many names must be moved to new locations? *. Suppose Gupta is to be deleted from the array. How many names must be moved to new locations? ...
Data Structures Name:___________________________ iterator our
... If I further solve the problems of size 50 by splitting each of them into two problems of size 25, then what would be the approximate amount of work? ...
... If I further solve the problems of size 50 by splitting each of them into two problems of size 25, then what would be the approximate amount of work? ...
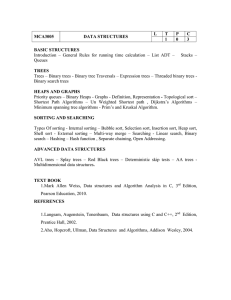
DATA STRUCTURES - University of Cape Town
... Given two integers A and B, output all 5x5 squares of single digits such that: Each row, each column and the two diagonals can be read as a five digit prime number. The rows are read from left to right. The columns are read from top to bottom. Both diagonals are read from left to right. The prime nu ...
... Given two integers A and B, output all 5x5 squares of single digits such that: Each row, each column and the two diagonals can be read as a five digit prime number. The rows are read from left to right. The columns are read from top to bottom. Both diagonals are read from left to right. The prime nu ...
15-451 Homework 1 Jan 20, 2008
... (b) Mergesort. (Take an array of n elements, mergesort the first half and the second half, then merge the two halves into one sorted array. The base case is one element, which must always be sorted.) (c) Consider the following algorithm: Given an n × n matrix, the algorithm squares the matrix using ...
... (b) Mergesort. (Take an array of n elements, mergesort the first half and the second half, then merge the two halves into one sorted array. The base case is one element, which must always be sorted.) (c) Consider the following algorithm: Given an n × n matrix, the algorithm squares the matrix using ...
No Slide Title
... Generally there are two types of devices from which numbers are read - analogue and digital Digital devices are simple to determine the least significant figure. It is the last digit (to the right) that is read out. For analogue devices determine the value that each mark on the device signifies. On ...
... Generally there are two types of devices from which numbers are read - analogue and digital Digital devices are simple to determine the least significant figure. It is the last digit (to the right) that is read out. For analogue devices determine the value that each mark on the device signifies. On ...
Chris Petrie`s solution
... Since A is a multiple of 10 the product of A(A+2) must also be a multiple of 10 and the sum of (A+2) must also be even: that is the tens digit must always be even. In this case B2 is 1, so the addition of B2 to A(A+2) only affects the last digit. Thus it is not possible to have a perfect square endi ...
... Since A is a multiple of 10 the product of A(A+2) must also be a multiple of 10 and the sum of (A+2) must also be even: that is the tens digit must always be even. In this case B2 is 1, so the addition of B2 to A(A+2) only affects the last digit. Thus it is not possible to have a perfect square endi ...
OLD_s1a_alg_analysis..
... • sorting problem the number of items to be sorted • multiply two matrices together the total number of elements in the two matrices And sometimes the input order as well (e.g., sorting algorithms). ...
... • sorting problem the number of items to be sorted • multiply two matrices together the total number of elements in the two matrices And sometimes the input order as well (e.g., sorting algorithms). ...
Decrease-and
... Proof: Given an array A, consider Ar, which is the array in reverse order. Now consider a pair (x, y) with x < y. This pair is an inversion in exactly one of A, Ar. The total number of such pairs is given by N (N - 1)/2, and (on average) half of these will be inversions in A. Thus A has N (N - 1) / ...
... Proof: Given an array A, consider Ar, which is the array in reverse order. Now consider a pair (x, y) with x < y. This pair is an inversion in exactly one of A, Ar. The total number of such pairs is given by N (N - 1)/2, and (on average) half of these will be inversions in A. Thus A has N (N - 1) / ...
Different Data Structures
... Each internal node x also contains x.n+1 pointers x.c1, x.c2, … x.cx.n+1 to its children. Leaf nodes have no children, and so their ci attributes are undefined. The keys x.keyi separate the ranges of keys stored in each subtree: if ki is any key stored in the subtree with root x.ci, then k1 <= x.key ...
... Each internal node x also contains x.n+1 pointers x.c1, x.c2, … x.cx.n+1 to its children. Leaf nodes have no children, and so their ci attributes are undefined. The keys x.keyi separate the ranges of keys stored in each subtree: if ki is any key stored in the subtree with root x.ci, then k1 <= x.key ...
CS 332: Algorithms
... Review: Counting Sort ● Counting sort: ■ Assumption: input is in the range 1..k ■ Basic idea: ○ Count number of elements k each element i ○ Use that number to place i in position k of sorted array ■ No comparisons! Runs in time O(n + k) ■ Stable sort ■ Does not sort in place: ○ O(n) array to hold ...
... Review: Counting Sort ● Counting sort: ■ Assumption: input is in the range 1..k ■ Basic idea: ○ Count number of elements k each element i ○ Use that number to place i in position k of sorted array ■ No comparisons! Runs in time O(n + k) ■ Stable sort ■ Does not sort in place: ○ O(n) array to hold ...