Module 1: Allocating IP Addressing by using Dynamic Host
... Seconds: number of seconds since the client started to boot Client IP address, Your IP address, server IP address, Gateway IP address, client hardware address, server host name, boot file name: client fills in the information that it has, leaves rest blank ...
... Seconds: number of seconds since the client started to boot Client IP address, Your IP address, server IP address, Gateway IP address, client hardware address, server host name, boot file name: client fills in the information that it has, leaves rest blank ...
GSM 04.11
... This GTS is a TC-SMG approved GSM technical specification version 5, which contains GSM Phase 2+ enhancements/features to the version 4 GSM technical specification. The ETS from which this Phase 2+ GTS has evolved is Phase 2 GSM ETS 300 559 edition 3 (GSM 04.11 version 4.10.0). GTS are produced by T ...
... This GTS is a TC-SMG approved GSM technical specification version 5, which contains GSM Phase 2+ enhancements/features to the version 4 GSM technical specification. The ETS from which this Phase 2+ GTS has evolved is Phase 2 GSM ETS 300 559 edition 3 (GSM 04.11 version 4.10.0). GTS are produced by T ...
TIA-1112
... Interworking between CS Networks Supporting ISUP and the IM CN Subsystem.................................................. 8 7.2.1 Services Performed by Network Entities in the Control Plane ..................................................................... 8 7.2.1.1 Services Performed by the SS7 ...
... Interworking between CS Networks Supporting ISUP and the IM CN Subsystem.................................................. 8 7.2.1 Services Performed by Network Entities in the Control Plane ..................................................................... 8 7.2.1.1 Services Performed by the SS7 ...
TR 0006 - oneM2M
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
... This is a draft oneM2M document and should not be relied upon; the final version, if any, will be made available by oneM2M Partners Type 1. ...
Institutionen f r systemteknik ö
... A Tactical Data Link (TDL) system has been deployed in many military missions as a winning strategy. The performance of a TDL system is governed by the MAC protocol. The MAC protocol that is able to provide more flexibility and high quality of services is more desirable. However, most MAC protocols ...
... A Tactical Data Link (TDL) system has been deployed in many military missions as a winning strategy. The performance of a TDL system is governed by the MAC protocol. The MAC protocol that is able to provide more flexibility and high quality of services is more desirable. However, most MAC protocols ...
Chapter 1 - Introduction
... – To handle ambiguity that arises from overlapping address masks, Internet forwarding uses a longest prefix match • Instead of examining the entries in arbitrary order • forwarding software arranges to examine entries with the longest prefix first ...
... – To handle ambiguity that arises from overlapping address masks, Internet forwarding uses a longest prefix match • Instead of examining the entries in arbitrary order • forwarding software arranges to examine entries with the longest prefix first ...
Chapter 1 - Introduction
... – To handle ambiguity that arises from overlapping address masks, Internet forwarding uses a longest prefix match • Instead of examining the entries in arbitrary order • forwarding software arranges to examine entries with the longest prefix first ...
... – To handle ambiguity that arises from overlapping address masks, Internet forwarding uses a longest prefix match • Instead of examining the entries in arbitrary order • forwarding software arranges to examine entries with the longest prefix first ...
Efficient Way of iSCSI based Remote Storage Service for
... level I/O. File-level I/O service is provided by communication between server and client file systems. In the case of file I/O, because client’s I/O request is passed to device via server file system, data share is possible between other clients through locking mechanism which server file system of ...
... level I/O. File-level I/O service is provided by communication between server and client file systems. In the case of file I/O, because client’s I/O request is passed to device via server file system, data share is possible between other clients through locking mechanism which server file system of ...
TCNM-AD/EX/SP Family Software Configuration Parameter Guide
... This operating mode does not require the connection to an external Presence Sensor. When working in this mode the reader is continuously scanning, while the reading phase is activated each time a barcode enters the reader reading zone. The reader stops reading after an N number of scans without a co ...
... This operating mode does not require the connection to an external Presence Sensor. When working in this mode the reader is continuously scanning, while the reading phase is activated each time a barcode enters the reader reading zone. The reader stops reading after an N number of scans without a co ...
Chapter 8 Lecture Presentation
... IP address: contain the addresses of the www.Bookspar.com | Website for Students | VTU - Notes - Question Papers source and destination hosts. ...
... IP address: contain the addresses of the www.Bookspar.com | Website for Students | VTU - Notes - Question Papers source and destination hosts. ...
third edition
... the book’s focus on core concepts should be appealing to industry professionals who are retraining for network-related assignments, as well as current network practitioners who want to understand the “whys” behind the protocols they work with every day and to see the big picture of networking. It is ...
... the book’s focus on core concepts should be appealing to industry professionals who are retraining for network-related assignments, as well as current network practitioners who want to understand the “whys” behind the protocols they work with every day and to see the big picture of networking. It is ...
TCP/IP Diagnosis Guide - z/VM
... How Numbers Are Used in This Book In this book, numbers over four digits are represented in metric style. A space is used rather than a comma to separate groups of three digits. For example, the number sixteen thousand, one hundred forty-seven is written 16 147. ...
... How Numbers Are Used in This Book In this book, numbers over four digits are represented in metric style. A space is used rather than a comma to separate groups of three digits. For example, the number sixteen thousand, one hundred forty-seven is written 16 147. ...
CallPilot Evolution Strategy Avaya Officelinx
... • All CallPilot systems utilize operating system environments Microsoft has discontinued support for, exposing customers to increased security risk. o Windows NT 4.0 o Windows Server 2003 ...
... • All CallPilot systems utilize operating system environments Microsoft has discontinued support for, exposing customers to increased security risk. o Windows NT 4.0 o Windows Server 2003 ...
Computer Networks and Internets
... Printed in the United States of America. This publication is protected by Copyright and permission should be obtained from the publisher prior to any prohibited reproduction, storage in a retrieval system, or transmission in any form or by any means, electronic, mechanical, photocopying, recording, ...
... Printed in the United States of America. This publication is protected by Copyright and permission should be obtained from the publisher prior to any prohibited reproduction, storage in a retrieval system, or transmission in any form or by any means, electronic, mechanical, photocopying, recording, ...
ppt1
... "Hagelslag is an implementation of GNUtella. The main goals for this implementation are flexibility, stability and performance. The development of Hagelslag was primarily aimed at i386 machines running Linux, as of version 0.8, FreeBSD is supported as well." /7 ...
... "Hagelslag is an implementation of GNUtella. The main goals for this implementation are flexibility, stability and performance. The development of Hagelslag was primarily aimed at i386 machines running Linux, as of version 0.8, FreeBSD is supported as well." /7 ...
Introducing TCP/IP
... – When TCP/IP is configured on the client computer, the Obtain an IP address automatically option button is the only necessary set-up element. Everything is automatic – The next time the workstation attempts to access the network (older versions of Windows must be rebooted first), it broadcasts a DH ...
... – When TCP/IP is configured on the client computer, the Obtain an IP address automatically option button is the only necessary set-up element. Everything is automatic – The next time the workstation attempts to access the network (older versions of Windows must be rebooted first), it broadcasts a DH ...
1. Use Cases
... 1. The SNMP manager sends an SNMP request to the agent. 2. The agent receives an SNMP request and parses it. 3. The agent creates the response message. 4. The agent checks the permissions of the specified object in the message. 5. The agent sets the new value for the object according to the message. ...
... 1. The SNMP manager sends an SNMP request to the agent. 2. The agent receives an SNMP request and parses it. 3. The agent creates the response message. 4. The agent checks the permissions of the specified object in the message. 5. The agent sets the new value for the object according to the message. ...
Computer Networking : Principles, Protocols and Practice Release
... • optical fiber. Optical fibers are frequently used in public and enterprise networks when the distance between the communication devices is larger than one kilometer. There are two main types of optical fibers : multimode and monomode. Multimode is much cheaper than monomode fiber because a LED can ...
... • optical fiber. Optical fibers are frequently used in public and enterprise networks when the distance between the communication devices is larger than one kilometer. There are two main types of optical fibers : multimode and monomode. Multimode is much cheaper than monomode fiber because a LED can ...
(PPT, 327KB)
... specifies the size of the TCP header in 32bit words. The minimum size header is 5 words and the maximum is 15 words thus giving the minimum size of 20 bytes and maximum of 60 bytes, allowing for up to 40 bytes of options in the header. This field gets its name from the fact that it is also the offse ...
... specifies the size of the TCP header in 32bit words. The minimum size header is 5 words and the maximum is 15 words thus giving the minimum size of 20 bytes and maximum of 60 bytes, allowing for up to 40 bytes of options in the header. This field gets its name from the fact that it is also the offse ...
W5100E01-AVR User Manual
... Copyright 2007 WIZnet, Ltd. All Rights Reserved. Technical Support: [email protected] Sales & Distribution: [email protected] General Information: [email protected] For more information, visit our website at http://www.wiznet.co.kr ...
... Copyright 2007 WIZnet, Ltd. All Rights Reserved. Technical Support: [email protected] Sales & Distribution: [email protected] General Information: [email protected] For more information, visit our website at http://www.wiznet.co.kr ...
29414-d10
... This Technical Specification has been produced by the 3rd Generation Partnership Project (3GPP). The contents of the present document are subject to continuing work within the TSG and may change following formal TSG approval. Should the TSG modify the contents of the present document, it will be re- ...
... This Technical Specification has been produced by the 3rd Generation Partnership Project (3GPP). The contents of the present document are subject to continuing work within the TSG and may change following formal TSG approval. Should the TSG modify the contents of the present document, it will be re- ...
Cisco IOS Quality of Service Update
... • Optimize bandwidth utilization for Video, Voice & Data apps • Drives productivity by enhancing servicelevels to missioncritical applications • Helps maintain network availability in the event of DoS/worm attacks ...
... • Optimize bandwidth utilization for Video, Voice & Data apps • Drives productivity by enhancing servicelevels to missioncritical applications • Helps maintain network availability in the event of DoS/worm attacks ...
Wireless Datagram Protocol
... You may use this document or any part of the document for internal or educational purposes only, provided you do not modify, edit or take out of context the information in this document in any manner. You may not use this document in any other manner without the prior written permission of the WAP F ...
... You may use this document or any part of the document for internal or educational purposes only, provided you do not modify, edit or take out of context the information in this document in any manner. You may not use this document in any other manner without the prior written permission of the WAP F ...
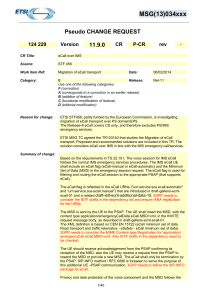
MSG(13)034xxx Pseudo CHANGE REQUEST 124 229 Version 11.9
... filtering and routing the eCall session to the appropriate PSAP (that supports eCall). The eCall flag is reflected in the eCall URNs ("urn:service:sos.ecall.automatic" and "urn:service:sos.ecall.manual") that are introduced in draft-gellens-ecritecall-01 and a related draft-ietf-ecrit-additional-dat ...
... filtering and routing the eCall session to the appropriate PSAP (that supports eCall). The eCall flag is reflected in the eCall URNs ("urn:service:sos.ecall.automatic" and "urn:service:sos.ecall.manual") that are introduced in draft-gellens-ecritecall-01 and a related draft-ietf-ecrit-additional-dat ...
ppt
... “In telecommunications, connectionless describes communication between two network end points in which a message can be sent from one end point to another without prior arrangement. The device at one end of the communication transmits data to the other, without first ensuring that the recipient is a ...
... “In telecommunications, connectionless describes communication between two network end points in which a message can be sent from one end point to another without prior arrangement. The device at one end of the communication transmits data to the other, without first ensuring that the recipient is a ...