LINQ and LINQ-to-SQL
... Create a DAO class with static methods which provide functionality for inserting, modifying and deleting customers. Write a testing class. ...
... Create a DAO class with static methods which provide functionality for inserting, modifying and deleting customers. Write a testing class. ...
Resource Bricolage for Parallel Database Systems
... disk, CPU, memory, and network resources, they will take varying amounts of time to process the same amount of data. Unfortunately, the execution time of a query in a parallel database system is determined by its slowest machine. At worst, a slow machine can substantially degrade the performance of ...
... disk, CPU, memory, and network resources, they will take varying amounts of time to process the same amount of data. Unfortunately, the execution time of a query in a parallel database system is determined by its slowest machine. At worst, a slow machine can substantially degrade the performance of ...
What is a Database Management System?
... DBMS independent. Supporting many programming languages. Microsoft implements the first ODBC driver manager over Windows Platforms. • A good way to implement client-server database under MS. Windows environment. Database Management COP4540, SCS, FIU ...
... DBMS independent. Supporting many programming languages. Microsoft implements the first ODBC driver manager over Windows Platforms. • A good way to implement client-server database under MS. Windows environment. Database Management COP4540, SCS, FIU ...
DARWin-ME Database Information
... following functions: 1. Archiving reference or design projects. Any valid DARWin-ME project may be stored in its entirety to the database 2. Creating material libraries. Individual material or other analysis objects (traffic, climate, etc.) can be stored and retrieved by users. DARWin-ME enterprise ...
... following functions: 1. Archiving reference or design projects. Any valid DARWin-ME project may be stored in its entirety to the database 2. Creating material libraries. Individual material or other analysis objects (traffic, climate, etc.) can be stored and retrieved by users. DARWin-ME enterprise ...
Course Review
... also nominates where it is. Super Key : This is normally a key with too many attributes in it. Some of the columns could be removed and a key would still exist. A good example is a key which contains ‘old value/new value’ such as ‘old telephone number/new telephone number’ when numbers are upgrades ...
... also nominates where it is. Super Key : This is normally a key with too many attributes in it. Some of the columns could be removed and a key would still exist. A good example is a key which contains ‘old value/new value’ such as ‘old telephone number/new telephone number’ when numbers are upgrades ...
SQL Injection in Web Application: A Review Sangeeta1 1MTech
... SQLIAs are introduced only via user input that is submitted as part of a Web form. Once attackers have identified an input source [3, 4] that can be used to exploit an SQLIA vulnerability, there are many different types of attack techniques that they can leverage. Depending on the type and extent of ...
... SQLIAs are introduced only via user input that is submitted as part of a Web form. Once attackers have identified an input source [3, 4] that can be used to exploit an SQLIA vulnerability, there are many different types of attack techniques that they can leverage. Depending on the type and extent of ...
Select * from - anuradhasrinivas
... The SQL standard defines embeddings of SQL in a variety of programming languages such as C, Java, and Cobol. A language to which SQL queries are embedded is referred to as a host language, and the SQL structures permitted in the host language comprise embedded SQL. The basic form of these languages ...
... The SQL standard defines embeddings of SQL in a variety of programming languages such as C, Java, and Cobol. A language to which SQL queries are embedded is referred to as a host language, and the SQL structures permitted in the host language comprise embedded SQL. The basic form of these languages ...
Musician
... Once you create a database SQL commands or Script files are loaded into a New Script interface and executed to create the tables for the ERD’s. As you work through the exercises examine the SQL code provided which has been written in notepad. Also note the SQL code for … the allocation of primary ...
... Once you create a database SQL commands or Script files are loaded into a New Script interface and executed to create the tables for the ERD’s. As you work through the exercises examine the SQL code provided which has been written in notepad. Also note the SQL code for … the allocation of primary ...
Getting Started with Elastic DB Database Tools with Azure SQL
... Growing and shrinking capacity on demand is one of the key cloud computing promises. Delivering on this promise has historically been tedious and complex for the database tier of cloud applications. Over the last few years, the industry has converged on well-established design patterns commonly know ...
... Growing and shrinking capacity on demand is one of the key cloud computing promises. Delivering on this promise has historically been tedious and complex for the database tier of cloud applications. Over the last few years, the industry has converged on well-established design patterns commonly know ...
Policy-Based Management of SQL Servers and Databases
... Many organizations require high availability solutions that protect the entire SQL Server instance, and not the individual databases. To meet this requirement, SQL Server 2008 can participate in a Microsoft Cluster Service Cluster group. A failover cluster appears to clients as a single instance of ...
... Many organizations require high availability solutions that protect the entire SQL Server instance, and not the individual databases. To meet this requirement, SQL Server 2008 can participate in a Microsoft Cluster Service Cluster group. A failover cluster appears to clients as a single instance of ...
Installation Reference Card
... ODBC compliant and Y2K compliant, relational database management system (RDBM) installed on its own computer. The database is required for logging transaction and CPM Server information. CPM supports Microsoft SQL Server and Oracle database applications. ...
... ODBC compliant and Y2K compliant, relational database management system (RDBM) installed on its own computer. The database is required for logging transaction and CPM Server information. CPM supports Microsoft SQL Server and Oracle database applications. ...
Database Schema Diagrams
... following schema diagrams useful when designing custom SQL queries and reports. If you need assistance or advice writing an SQL query please contact support. By default PaperCut stores its data in an internal database format that is not accessible for external reporting. To access the database for r ...
... following schema diagrams useful when designing custom SQL queries and reports. If you need assistance or advice writing an SQL query please contact support. By default PaperCut stores its data in an internal database format that is not accessible for external reporting. To access the database for r ...
Installation Reference Card
... ODBC compliant and Y2K compliant, relational database management system (RDBM) installed on its own computer. The database is required for logging transaction and CPM Server information. CPM supports Microsoft SQL Server and Oracle database applications. Note CyberSource recommends that SQL Server u ...
... ODBC compliant and Y2K compliant, relational database management system (RDBM) installed on its own computer. The database is required for logging transaction and CPM Server information. CPM supports Microsoft SQL Server and Oracle database applications. Note CyberSource recommends that SQL Server u ...
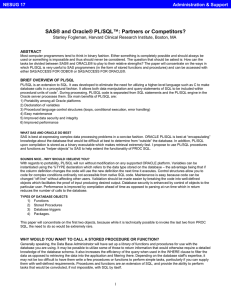
SAS and ORACLE PL/SQL: Partners or Competitors'
... database you are using. It may be possible to utilize some of those to return information that would otherwise require a detailed knowledge of the database schema. It also increases the efficiency of the query when used in the WHERE clause to filter the data as opposed to retrieving the data into th ...
... database you are using. It may be possible to utilize some of those to return information that would otherwise require a detailed knowledge of the database schema. It also increases the efficiency of the query when used in the WHERE clause to filter the data as opposed to retrieving the data into th ...
eCommerce&Security - DCU School of Computing
... • Embedding SQL from any real database system into any conventional programming language + Host languages such as PL/1, COBOL, Pascal , C use the same style + Java solution looks a bit different + Dual-mode principle: every SQL statement can be used interactively as well as in an application program ...
... • Embedding SQL from any real database system into any conventional programming language + Host languages such as PL/1, COBOL, Pascal , C use the same style + Java solution looks a bit different + Dual-mode principle: every SQL statement can be used interactively as well as in an application program ...
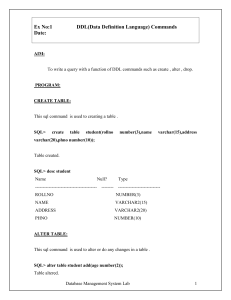
Simple version control
... All newly added not-null columns should have default to prevent errors when adding to table with data. If no default value is possible – add column as nullable, fill it with appropriate data and then alter to not null. ...
... All newly added not-null columns should have default to prevent errors when adding to table with data. If no default value is possible – add column as nullable, fill it with appropriate data and then alter to not null. ...
Course Topics - Webject Systems Inc
... Invoke a function Remove a function Differentiate between a procedure and a function ...
... Invoke a function Remove a function Differentiate between a procedure and a function ...
LINQ and LINQ-to-SQL
... Create a DAO class with static methods which provide functionality for inserting, modifying and deleting customers. Write a testing class. ...
... Create a DAO class with static methods which provide functionality for inserting, modifying and deleting customers. Write a testing class. ...
2. Introduction-to-MS-SQL-Server
... Attach the database Northwind (use the files Northwind.mdf and Northwind.ldf) to SQL Server and connect to it. ...
... Attach the database Northwind (use the files Northwind.mdf and Northwind.ldf) to SQL Server and connect to it. ...
Introduction to SQL Server and MySQL
... Attach the database Northwind (use the files Northwind.mdf and Northwind.ldf) to SQL Server and connect to it. ...
... Attach the database Northwind (use the files Northwind.mdf and Northwind.ldf) to SQL Server and connect to it. ...
Tuning I/O Subsystem: A Key Component in RDBMS Performance
... take advantage of RAID technology to provide a measure of fault tolerance. OS striping is very good; however, It does consume system resources that hardware striping does not. 4.5 Hardware Striping Hardware striping has a similar effect to OS striping. Hardware fault tolerance is obtained by replaci ...
... take advantage of RAID technology to provide a measure of fault tolerance. OS striping is very good; however, It does consume system resources that hardware striping does not. 4.5 Hardware Striping Hardware striping has a similar effect to OS striping. Hardware fault tolerance is obtained by replaci ...
MS SQL Database Security Policy
... Analysis Services account (svcMSSqlAnSrvc), if they exist, should be normal domain users with no domain admin rights; Remove Built-in\Administrators Login from System Administrator role; Do not grant permissions to the public role; Create custom database roles if required, for finer control over per ...
... Analysis Services account (svcMSSqlAnSrvc), if they exist, should be normal domain users with no domain admin rights; Remove Built-in\Administrators Login from System Administrator role; Do not grant permissions to the public role; Create custom database roles if required, for finer control over per ...
MS SQL/SSIS/SSRS Developer
... Used Performance Monitor/Profiler to solve dead locks/long running queries. Experienced in Performance Tuning, Query Optimization and running Database checked the physical and logical consistency of a database using DBCC Utilities. Well-versed with database Installation,configuration, maintenance, m ...
... Used Performance Monitor/Profiler to solve dead locks/long running queries. Experienced in Performance Tuning, Query Optimization and running Database checked the physical and logical consistency of a database using DBCC Utilities. Well-versed with database Installation,configuration, maintenance, m ...
White paper: Intel® Core™ Duo processor
... To learn more about the new, mobile-optimized Intel Core Duo processor, visit www.intel.com/products/processor. † System performance, battery life, and functionality will vary depending on your specific operating system, hardware and software configurations. References to enhanced performance as measu ...
... To learn more about the new, mobile-optimized Intel Core Duo processor, visit www.intel.com/products/processor. † System performance, battery life, and functionality will vary depending on your specific operating system, hardware and software configurations. References to enhanced performance as measu ...
Tandem Computers

Tandem Computers, Inc. was the dominant manufacturer of fault-tolerant computer systems for ATM networks, banks, stock exchanges, telephone switching centers, and other similar commercial transaction processing applications requiring maximum uptime and zero data loss. The company was founded in 1974 and remained independent until 1997. It is now a server division within Hewlett Packard.Tandem's NonStop systems use a number of independent identical processors and redundant storage devices and controllers to provide automatic high-speed ""failover"" in the case of a hardware or software failure. To contain the scope of failures and of corrupted data, these multi-computer systems have no shared central components, not even main memory. Conventional multi-computer systems all use shared memories and work directly on shared data objects. Instead, NonStop processors cooperate by exchanging messages across a reliable fabric, and software takes periodic snapshots for possible rollback of program memory state.Besides handling failures well, this ""shared-nothing"" messaging system design also scales extremely well to the largest commercial workloads. Each doubling of the total number of processors would double system throughput, up to the maximum configuration of 4000 processors. In contrast, the performance of conventional multiprocessor systems is limited by the speed of some shared memory, bus, or switch. Adding more than 4–8 processors that way gives no further system speedup. NonStop systems have more often been bought to meet scaling requirements than for extreme fault tolerance. They compete well against IBM's largest mainframes, despite being built from simpler minicomputer technology.