Analysis of the RSA Encryption Algorithm
... totient function and prime factorization, and the modulo function. In general, there is a public key function defined as (n, e) and a private key function defined as (n, d). The algorithm statement is given c = m^e % n, where c is the ciphertext and m is the integer representation of the original me ...
... totient function and prime factorization, and the modulo function. In general, there is a public key function defined as (n, e) and a private key function defined as (n, d). The algorithm statement is given c = m^e % n, where c is the ciphertext and m is the integer representation of the original me ...
7th grade Pre-Algebra Chapter 4 Factors, Fractions, and Exponents
... fraction where the numerator is less than the denominator. An improper fraction is a fraction where the numerator is more than the denominator. W n/d = (W·d +n)/d When a division problem results in a remainder of 0, the quotient is a terminating decimal. If one or more of the digits repeat without e ...
... fraction where the numerator is less than the denominator. An improper fraction is a fraction where the numerator is more than the denominator. W n/d = (W·d +n)/d When a division problem results in a remainder of 0, the quotient is a terminating decimal. If one or more of the digits repeat without e ...
Document
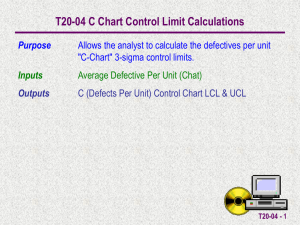
... Also, note that since the formula is an approximation the LCL can be negative. In these cases the LCL is set to 0. T20-04 - 2 ...
... Also, note that since the formula is an approximation the LCL can be negative. In these cases the LCL is set to 0. T20-04 - 2 ...
Full text
... Previously, most work on /c-reverse multiples has focused on either finding all those less than a given m [1], or characterizing, for a given n, those with n-digits. This latter problem seems to be quite difficult and has been completely solved only for the 2- and 3-digit cases (see [1] and [3]). Ad ...
... Previously, most work on /c-reverse multiples has focused on either finding all those less than a given m [1], or characterizing, for a given n, those with n-digits. This latter problem seems to be quite difficult and has been completely solved only for the 2- and 3-digit cases (see [1] and [3]). Ad ...
Divisibility Math Tricks to Learn the Facts
... More and more in my teaching career, I see that we often are able to enhance student learning in mathematics with tricks. There are many tricks to teach children divisibility in mathematics. Some tricks that I used to use in my classroom are listed here. If you know of some that I may have missed, d ...
... More and more in my teaching career, I see that we often are able to enhance student learning in mathematics with tricks. There are many tricks to teach children divisibility in mathematics. Some tricks that I used to use in my classroom are listed here. If you know of some that I may have missed, d ...
TEST - Cobb Learning
... The given point is on the terminal side of an angle in standard position. Determine the exact values of the six trigonometric functions of the angle. ...
... The given point is on the terminal side of an angle in standard position. Determine the exact values of the six trigonometric functions of the angle. ...
Homework 1
... (b) How many possibilities are there if every kid buys exactly two balloons of different colors? (c) How many possibilities are there if every kid buys one balloon and exactly 4 kids have bought a red balloon? (d) How many different combinations of balloons can be left in the shop if every kid buys ...
... (b) How many possibilities are there if every kid buys exactly two balloons of different colors? (c) How many possibilities are there if every kid buys one balloon and exactly 4 kids have bought a red balloon? (d) How many different combinations of balloons can be left in the shop if every kid buys ...
lec_3_DataRepresentation_2
... The first 32 characters of ASCII table are used for control Control character codes = 00 to 1F (hex) Examples of Control Characters Character 0 is the NULL character used to terminate a string Character 9 is the Horizontal Tab (HT) character Character 0A (hex) = 10 (decimal) is the Lin ...
... The first 32 characters of ASCII table are used for control Control character codes = 00 to 1F (hex) Examples of Control Characters Character 0 is the NULL character used to terminate a string Character 9 is the Horizontal Tab (HT) character Character 0A (hex) = 10 (decimal) is the Lin ...
significant figures
... Leading zeros are NOT significant. 0.001050 has 4 significant figures. • 1.050 x 10-3 • Zeros at the end of a number without a written decimal point are ambiguous and should be avoided by using scientific notation. If 150 has 2 significant figures, then 1.5 x 102, but if 150 has 3 significant fi ...
... Leading zeros are NOT significant. 0.001050 has 4 significant figures. • 1.050 x 10-3 • Zeros at the end of a number without a written decimal point are ambiguous and should be avoided by using scientific notation. If 150 has 2 significant figures, then 1.5 x 102, but if 150 has 3 significant fi ...
Class X Delhi Math Set-30/1 Section – A [Outside Delhi... Section-A 1. The common difference of AP 1/2q, (1-2q)/2q, (1-4q)/2q...........is (A) -1
... 10. Find the number of all three digit natural number which are divisible by 9? Solution: All the three-digit natural numbers that are divisible by 9will be of the form 9n. Therefore, 100 7n 999 1119 7n 111 Since, n is an integer, therefore, there will be 111 – 11 = 100 three-digit natural n ...
... 10. Find the number of all three digit natural number which are divisible by 9? Solution: All the three-digit natural numbers that are divisible by 9will be of the form 9n. Therefore, 100 7n 999 1119 7n 111 Since, n is an integer, therefore, there will be 111 – 11 = 100 three-digit natural n ...
Intermediate Pythagoras / Trigonometry Questions GRADE C/B 1. A
... Intermediate Pythagoras / Trigonometry Questions ...
... Intermediate Pythagoras / Trigonometry Questions ...
Approximations of π
Approximations for the mathematical constant pi (π) in the history of mathematics reached an accuracy within 0.04% of the true value before the beginning of the Common Era (Archimedes). In Chinese mathematics, this was improved to approximations correct to what corresponds to about seven decimal digits by the 5th century.Further progress was made only from the 15th century (Jamshīd al-Kāshī), and early modern mathematicians reached an accuracy of 35 digits by the 18th century (Ludolph van Ceulen), and 126 digits by the 19th century (Jurij Vega), surpassing the accuracy required for any conceivable application outside of pure mathematics.The record of manual approximation of π is held by William Shanks, who calculated 527 digits correctly in the years preceding 1873. Since the mid 20th century, approximation of π has been the task of electronic digital computers; the current record (as of May 2015) is at 13.3 trillion digits, calculated in October 2014.