SMART WIRELESS GATEWAY HART MANUAL
... The Smart Wireless Gateway connects WirelessHART™ self-organizing networks with host systems and data applications. Modbus communications over RS-485 or Ethernet provide universal integration and system interoperability. The optional OPC functionality from the Gateway offers a means to connect to ne ...
... The Smart Wireless Gateway connects WirelessHART™ self-organizing networks with host systems and data applications. Modbus communications over RS-485 or Ethernet provide universal integration and system interoperability. The optional OPC functionality from the Gateway offers a means to connect to ne ...
PRODUCT CATALOG
... networks is frequent moves, adds and changes as well as user-mobility. SMC’s wireless solutions enable you to meet these needs with a series of wireless devices that are fully compliant with IEEE 802.11b wireless networking standards. SMC’s products integrate seamlessly with cabled ethernet networks ...
... networks is frequent moves, adds and changes as well as user-mobility. SMC’s wireless solutions enable you to meet these needs with a series of wireless devices that are fully compliant with IEEE 802.11b wireless networking standards. SMC’s products integrate seamlessly with cabled ethernet networks ...
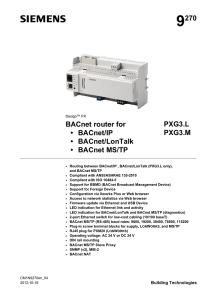
PXG3.L, PXG3.M BACnet Router
... access from a public network to BACnet devices in a private network is possible. Important: the public IP address must be static. For details see standard 135-2010. ...
... access from a public network to BACnet devices in a private network is possible. Important: the public IP address must be static. For details see standard 135-2010. ...
User Manual Broadband Blaster DSL Ethernet/USB 8012U
... Software. Nor may you sub-license any of your rights under this Agreement. You may use the Software for your personal use only, and not for public performance or for the creation of publicly displayed videotapes. 10.Decompiling, Disassembling, or Reverse Engineering You acknowledge that the Software ...
... Software. Nor may you sub-license any of your rights under this Agreement. You may use the Software for your personal use only, and not for public performance or for the creation of publicly displayed videotapes. 10.Decompiling, Disassembling, or Reverse Engineering You acknowledge that the Software ...
Data Sheet
... support Modbus over EIA-232, EIA-485(optionally) and over TCP/IP. The gateway polls the modbus objects at a configurable rate. Values can be read or written by BACnet clients and by the Web Interface using the browser. BACnet clients can requests COV. ...
... support Modbus over EIA-232, EIA-485(optionally) and over TCP/IP. The gateway polls the modbus objects at a configurable rate. Values can be read or written by BACnet clients and by the Web Interface using the browser. BACnet clients can requests COV. ...
TCP for wireless links
... mobile host out of reach of other transceivers (little or no overlap between cells); • Packet losses due to transmission errors in wireless links. ...
... mobile host out of reach of other transceivers (little or no overlap between cells); • Packet losses due to transmission errors in wireless links. ...
wienet - Wieland Electric Inc.
... Wieland's wienet VPN industrial routers ensure increased efficiency and data security. Whether it is about the control of machines, monitoring of production lines or the coordination of all production areas a permanent communication between devices is needed to complete such a complex task. Access t ...
... Wieland's wienet VPN industrial routers ensure increased efficiency and data security. Whether it is about the control of machines, monitoring of production lines or the coordination of all production areas a permanent communication between devices is needed to complete such a complex task. Access t ...
Vodafone Broadband Complete User Guide
... Broadcasting SSID’s displays a list of wireless networks in range allowing the user to select a preferred one. ...
... Broadcasting SSID’s displays a list of wireless networks in range allowing the user to select a preferred one. ...
Update a postal address for your broadband bill
... Broadcasting SSID’s displays a list of wireless networks in range allowing the user to select a preferred one. ...
... Broadcasting SSID’s displays a list of wireless networks in range allowing the user to select a preferred one. ...
No Slide Title - IEEE-SA
... Classification • Each device broadcasts periodically information about its availability for the others by sending id_info PDU • With this PDU the broadcasting device informs that it can be contacted during the next e.g. 1ms – The PDU contains IEEE address and 8-bit device service field – Mini device ...
... Classification • Each device broadcasts periodically information about its availability for the others by sending id_info PDU • With this PDU the broadcasting device informs that it can be contacted during the next e.g. 1ms – The PDU contains IEEE address and 8-bit device service field – Mini device ...
manual de fabricante del cablerouter Technicolor TC7210
... which producers' are responsible. This appliance has been designed and manufactured with high quality materials and components that can be recycled and reused. Electrical and electronic appliances are liable to contain parts that are necessary in order for the system to work properly but which can b ...
... which producers' are responsible. This appliance has been designed and manufactured with high quality materials and components that can be recycled and reused. Electrical and electronic appliances are liable to contain parts that are necessary in order for the system to work properly but which can b ...
CY2009 Interlock Process Bell Labs
... Downlink To perform downlink CoMP there are two options: Data and beam forming coefficients sent to each base station I/Q samples or soft bits sent to each base station After CoMP processing performed at CoMP processor The backhaul network must support the required data distribution to a ...
... Downlink To perform downlink CoMP there are two options: Data and beam forming coefficients sent to each base station I/Q samples or soft bits sent to each base station After CoMP processing performed at CoMP processor The backhaul network must support the required data distribution to a ...
Hongwei Zhang - Computer Science
... cyber-physical-human systems. For instance, our Physical-Ratio-K (PRK) wireless interference model and the PRK-based wireless transmission scheduling protocol PRKS ensure predictable interference control and high channel spatial reuse at the same time, which has been an open problem since early 1970 ...
... cyber-physical-human systems. For instance, our Physical-Ratio-K (PRK) wireless interference model and the PRK-based wireless transmission scheduling protocol PRKS ensure predictable interference control and high channel spatial reuse at the same time, which has been an open problem since early 1970 ...
DLB APC v5.95 User’s Guide Revision 1.0 9 October 2014
... Web Management Structure ............................................................................................................... 9 Appling and Saving Configuration Changes ..................................................................................... 11 ...
... Web Management Structure ............................................................................................................... 9 Appling and Saving Configuration Changes ..................................................................................... 11 ...
Three Challenges in Reliable Data Transport over Heterogeneous
... Suppressing duplicate acknowledgments and TCP-awareness leads to better utilization of link bandwidth and performance ...
... Suppressing duplicate acknowledgments and TCP-awareness leads to better utilization of link bandwidth and performance ...
Spatial Reusability-Aware Routing in Multi-Hop Wireless
... recent years, a large number of routing protocols have been proposed for multi-hop wireless networks. However, a fundamental problem with existing wireless routing protocols is that minimizing the overall number (or time) of transmissions to deliver a single packet from a source node to a destinatio ...
... recent years, a large number of routing protocols have been proposed for multi-hop wireless networks. However, a fundamental problem with existing wireless routing protocols is that minimizing the overall number (or time) of transmissions to deliver a single packet from a source node to a destinatio ...
MM2211 Wireless Broadband Gateway User`s Guide
... This device has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This device generates, uses, and can radiate radi ...
... This device has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation. This device generates, uses, and can radiate radi ...
Aalborg Universitet HomePort ZigBee Adapter
... networks and protocols, including ConLAN’s. It can easily be extended with further adapters to support additional networks. Thus this report considers the addition of a ZigBee Adapter, using a gateway provided by Develco. A. ConLAN ConLAN1 is a small danish company producing keypads and various read ...
... networks and protocols, including ConLAN’s. It can easily be extended with further adapters to support additional networks. Thus this report considers the addition of a ZigBee Adapter, using a gateway provided by Develco. A. ConLAN ConLAN1 is a small danish company producing keypads and various read ...
Machine-to-Machine (M2M) Gateway: Trusted and Connected
... In the year 2020, the world will be more connected, wireless networks will connect more machines than people and Machine-to-Machine (M2M) technology will help us to be more energy and cost-efficient, safer and more secure. This is the era of connected intelligence. The number of mobile connections i ...
... In the year 2020, the world will be more connected, wireless networks will connect more machines than people and Machine-to-Machine (M2M) technology will help us to be more energy and cost-efficient, safer and more secure. This is the era of connected intelligence. The number of mobile connections i ...
Packet-Hiding Methods for Preventing Selective Jamming Attacks
... of time the jammer is active, (e) number of connections established in the network, (f) fraction of time the jammer is active. R p: random jammer with probability p; Con.: constant jammer; Sel.: selective jammer. Note from (2) that reception of ci+1 is sufficient to recover mi if k is known (c1 = IV ...
... of time the jammer is active, (e) number of connections established in the network, (f) fraction of time the jammer is active. R p: random jammer with probability p; Con.: constant jammer; Sel.: selective jammer. Note from (2) that reception of ci+1 is sufficient to recover mi if k is known (c1 = IV ...
The Holku industries
... another in relation to the OSI model Each PC/Host is configured with an IP address; Subnet Mask; and Default Gateway. Using the OSI, from the Physical (1) upwards transmits data. Data Link Layer (2) creates and addresses frames for host-to-host delivery through local LANS Network Layer (3) creates a ...
... another in relation to the OSI model Each PC/Host is configured with an IP address; Subnet Mask; and Default Gateway. Using the OSI, from the Physical (1) upwards transmits data. Data Link Layer (2) creates and addresses frames for host-to-host delivery through local LANS Network Layer (3) creates a ...
R1.What is the difference between a host and an end system?List
... destination without message segmentation. How long does it take to move the message from the source host to the first packet switch? Keeping in mind that each switch uses store-and-forward packet switching, what is the total time to move the message from source host to destination host? ...
... destination without message segmentation. How long does it take to move the message from the source host to the first packet switch? Keeping in mind that each switch uses store-and-forward packet switching, what is the total time to move the message from source host to destination host? ...
Wireless USB

Wireless USB is a short-range, high-bandwidth wireless radio communication protocol created by the Wireless USB Promoter Group. Wireless USB is sometimes abbreviated as ""WUSB"", although the USB Implementers Forum discouraged this practice and instead prefers to call the technology Certified Wireless USB to distinguish it from the competing UWB standard.Wireless USB was based on the (now defunct) WiMedia Alliance's ultra-wideband (UWB) common radio platform, which is capable of sending 480 Mbit/s at distances up to 3 metres (9.8 ft) and 110 Mbit/s at up to 10 metres (33 ft). It was designed to operate in the 3.1 to 10.6 GHz frequency range, although local regulatory policies may restrict the legal operating range for any given country.