(M1) why are protocols important
... Network management tools also rely on them They work unseen at a low level and need no authoring or attention by users There are literally dozens of protocols all designed to perform specific tasks from the principle WAN essential ones such as TCP/IP, POP3, FTP to the less well know ones ...
... Network management tools also rely on them They work unseen at a low level and need no authoring or attention by users There are literally dozens of protocols all designed to perform specific tasks from the principle WAN essential ones such as TCP/IP, POP3, FTP to the less well know ones ...
PPT - Pages
... • Stop and wait flow control results in poor throughput for long-delay paths: packet size/ roundtrip-time. • Solution: receiver provides sender with a window that it can fill with packets. – The window is backed up by buffer space on receiver – Receiver acknowledges the a packet every time a packet ...
... • Stop and wait flow control results in poor throughput for long-delay paths: packet size/ roundtrip-time. • Solution: receiver provides sender with a window that it can fill with packets. – The window is backed up by buffer space on receiver – Receiver acknowledges the a packet every time a packet ...
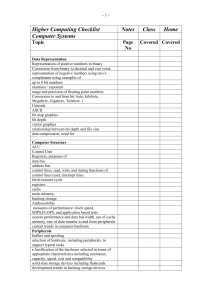
Course Arrangements: Higher Computing 6
... measures of performance: clock speed, MIPS,FLOPS, and application based tests system performance and data bus width, use of cache memory, rate of data transfer to and from peripherals current trends in computer hardware Peripherals buffers and spooling selection of hardware, including peripherals, t ...
... measures of performance: clock speed, MIPS,FLOPS, and application based tests system performance and data bus width, use of cache memory, rate of data transfer to and from peripherals current trends in computer hardware Peripherals buffers and spooling selection of hardware, including peripherals, t ...
WAN Technologies
... Established path (all packets use the same path) Used for connection-oriented services such as streaming video ...
... Established path (all packets use the same path) Used for connection-oriented services such as streaming video ...
Part I: Introduction
... each end-end data stream divided into packets user A, B packets share network resources each packet uses full link bandwidth ...
... each end-end data stream divided into packets user A, B packets share network resources each packet uses full link bandwidth ...
INTRODUCTION - University of Southern California
... Finite Mobile Robots :random Transmission range ‘r’ ...
... Finite Mobile Robots :random Transmission range ‘r’ ...
Solutions to Finals
... 000 Î No Remainder means no error was detected b. What can you tell about possible errors in the data received? Solution: No error was detected in the data received using the CRC algorithm CRC with no remainder guarantees that there were no single bit errors, also no odd number of errors (as x+1 is ...
... 000 Î No Remainder means no error was detected b. What can you tell about possible errors in the data received? Solution: No error was detected in the data received using the CRC algorithm CRC with no remainder guarantees that there were no single bit errors, also no odd number of errors (as x+1 is ...
05 LAES presentation
... Call-identifying information "dialing" or signaling which identifies the destination, direction, origin or termination of each communication generated or received by a subscriber by means of any equipment, facility, or service of a TSP Call content actual voice or, for data, the payload ...
... Call-identifying information "dialing" or signaling which identifies the destination, direction, origin or termination of each communication generated or received by a subscriber by means of any equipment, facility, or service of a TSP Call content actual voice or, for data, the payload ...
Computer Networks - Career Center Construction Technology
... • In addition to these types, the following characteristics are also used to categorize different types of networks: • topology : The geometric arrangement of a computer system. Common topologies include a bus, star, and ring. See the Network topology diagrams in the Quick Reference section of Web ...
... • In addition to these types, the following characteristics are also used to categorize different types of networks: • topology : The geometric arrangement of a computer system. Common topologies include a bus, star, and ring. See the Network topology diagrams in the Quick Reference section of Web ...
ppt
... • Recall that 100Mbps Ethernet restricts cable lengths to 100m. Suppose we want to connect two hosts which are 1000m apart. Can we use 10 100m cables with 9 hubs in series to accomplish this? – No. Since all ports are on same collision domain, max network diameter (1km) is too large to meet the TRAN ...
... • Recall that 100Mbps Ethernet restricts cable lengths to 100m. Suppose we want to connect two hosts which are 1000m apart. Can we use 10 100m cables with 9 hubs in series to accomplish this? – No. Since all ports are on same collision domain, max network diameter (1km) is too large to meet the TRAN ...
Test your knowledge
... 13. Why do manufacturers of network hardware and software follow established standards? They establish these standards because it will avoid problems associated with incompatibility between hardware and software components, organisations such as the Institution of Electrical and Electronics Engineer ...
... 13. Why do manufacturers of network hardware and software follow established standards? They establish these standards because it will avoid problems associated with incompatibility between hardware and software components, organisations such as the Institution of Electrical and Electronics Engineer ...
Protocols - Teach ICT
... • LAN protocols refer to network operating systems. Access protocols determine how an attached device communicates with the network transmission medium (often cabling). ...
... • LAN protocols refer to network operating systems. Access protocols determine how an attached device communicates with the network transmission medium (often cabling). ...
COE 308: Computer Architecture (T032) Dr. Marwan Abu
... OK with telephony, as people keep talking till end of call Not the case with many computer data situations (bursty) Advantage: Reliable, predictable performance – Once connection is established, devices appear as if connected directly through a dedicated link Disadvantage: Inefficient utilization wi ...
... OK with telephony, as people keep talking till end of call Not the case with many computer data situations (bursty) Advantage: Reliable, predictable performance – Once connection is established, devices appear as if connected directly through a dedicated link Disadvantage: Inefficient utilization wi ...
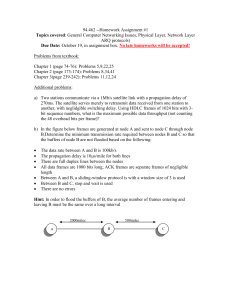
NetworkingReview
... 17. Suppose a 128-Kbps point-to-point link is set up between Earth and a rover on Mars. The distance from Earth to Mars (when they are closest together) is approximately 55 Gm, and data travels over the link at the speed of light 3 × 108 m/s. a. Calculate the minimum RTT for the link. b. Calculate ...
... 17. Suppose a 128-Kbps point-to-point link is set up between Earth and a rover on Mars. The distance from Earth to Mars (when they are closest together) is approximately 55 Gm, and data travels over the link at the speed of light 3 × 108 m/s. a. Calculate the minimum RTT for the link. b. Calculate ...
Public Key Protected Data Plane and Demo
... understand HIP Data. Need to modify the code to send R1 when it is not HIP Data enabled. Need to do measurements and comparisions Requirement for Ack and Seq functionalities need to be discussed further and their impact on TCP Seq/Ack. ...
... understand HIP Data. Need to modify the code to send R1 when it is not HIP Data enabled. Need to do measurements and comparisions Requirement for Ack and Seq functionalities need to be discussed further and their impact on TCP Seq/Ack. ...
Physical and Datalink Layer and LANS: Part I
... transmission (although asynchronous transmission is more common) ...
... transmission (although asynchronous transmission is more common) ...
1. Communication Network
... • Collection of computers that are both autonomous and interconnected • Differs from distributed computer system – in distributed system, presence of multiple processors is made transparent to user whereas in network knowledge of the multiple processors is fundamental to user ...
... • Collection of computers that are both autonomous and interconnected • Differs from distributed computer system – in distributed system, presence of multiple processors is made transparent to user whereas in network knowledge of the multiple processors is fundamental to user ...
Lect5
... • NRZI (signal is toggled only when a logic 1 is to be transmitted) • 4B/5B encoding translated 4 bits of data into a 5-bit symbol • for the 16 possible permutations there are 32 symbols • carefully choose symbols to guarantee that at least one signal transition within any 3 bit period. ...
... • NRZI (signal is toggled only when a logic 1 is to be transmitted) • 4B/5B encoding translated 4 bits of data into a 5-bit symbol • for the 16 possible permutations there are 32 symbols • carefully choose symbols to guarantee that at least one signal transition within any 3 bit period. ...
Document
... 270ms. The satellite serves merely to retransmit data received from one station to another, with neglidgible switching delay. Using HDLC frames of 1024 bits with 3bit sequence numbers, what is the maximum possible data throughput (not counting the 48 overhead bits per frame)? b) In the figure below ...
... 270ms. The satellite serves merely to retransmit data received from one station to another, with neglidgible switching delay. Using HDLC frames of 1024 bits with 3bit sequence numbers, what is the maximum possible data throughput (not counting the 48 overhead bits per frame)? b) In the figure below ...
Networking Your Office
... The Internet is a system of worldwide linked networks that facilitate data communication services such as remote login, file transfer, electronic mail, the World Wide Web, and newsgroups. With the large demand for connectivity, the Internet has become a communications highway for millions of users. ...
... The Internet is a system of worldwide linked networks that facilitate data communication services such as remote login, file transfer, electronic mail, the World Wide Web, and newsgroups. With the large demand for connectivity, the Internet has become a communications highway for millions of users. ...
What is Communication - Comsats Institute of Information Technology
... Data communications are the exchange of data between two devices via some form of transmission medium such as a wire cable. The word data refers to information presented in whatever form is agreed upon by the parties creating and using the data. ...
... Data communications are the exchange of data between two devices via some form of transmission medium such as a wire cable. The word data refers to information presented in whatever form is agreed upon by the parties creating and using the data. ...