tutorial 1 - Portal UniMAP
... 5. What is the business case for voice and data network convergence? Since PDNs were overwhelmingly used for data transmission alone, the average business customer needed two distinct networks: the telephone system for voice, and PDN for computer connections. Using and maintaining two separate netwo ...
... 5. What is the business case for voice and data network convergence? Since PDNs were overwhelmingly used for data transmission alone, the average business customer needed two distinct networks: the telephone system for voice, and PDN for computer connections. Using and maintaining two separate netwo ...
chapter1
... • Connecting all nodes directly to each other using point-to-point links is unmanageable and very expensive for large number of nodes covering a large geographic area • A switched network solves all preceding problems ...
... • Connecting all nodes directly to each other using point-to-point links is unmanageable and very expensive for large number of nodes covering a large geographic area • A switched network solves all preceding problems ...
PowerPoint XP
... If one machine goes down, use another A user is able to store data in multiple locations ...
... If one machine goes down, use another A user is able to store data in multiple locations ...
phys-layer-interface..
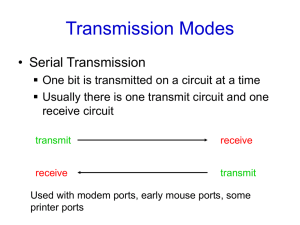
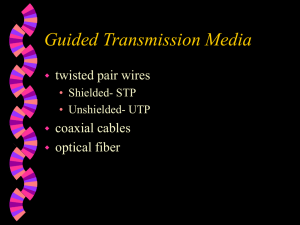
... • How do we organize the bits for transmission? • How do we keep bits synchronized? • If we transmit bytes, what distinguishes the start of each byte? • How is the data rate determined? • We must define the rules, the standards, in order for different equipment to properly ...
... • How do we organize the bits for transmission? • How do we keep bits synchronized? • If we transmit bytes, what distinguishes the start of each byte? • How is the data rate determined? • We must define the rules, the standards, in order for different equipment to properly ...
The Network Layer
... – first set up a connection between two nodes – label it (called a virtual circuit identifier (VCI)) – all packets carry label ...
... – first set up a connection between two nodes – label it (called a virtual circuit identifier (VCI)) – all packets carry label ...
No Slide Title
... Dial-up – This method is used for modem to modem data communication over the Public Switched Telephone Network (PSTN). Both the source and destination must have compatible modems ...
... Dial-up – This method is used for modem to modem data communication over the Public Switched Telephone Network (PSTN). Both the source and destination must have compatible modems ...
The Network Layer
... A basic idea is to allocate the remaining class C networks (more than 2 million, and later A and B) in variable sized blocks of 254 addresses, a site needing 8000 addresses then gets 32 contiguous class C networks. The world was divided up into 4 zones to easy hierarchical routing. A site outside Eu ...
... A basic idea is to allocate the remaining class C networks (more than 2 million, and later A and B) in variable sized blocks of 254 addresses, a site needing 8000 addresses then gets 32 contiguous class C networks. The world was divided up into 4 zones to easy hierarchical routing. A site outside Eu ...
Networking | computer Network | TCP/IP
... Application-Oriented Networking • All kinds of new application-specific routing and transport layers ...
... Application-Oriented Networking • All kinds of new application-specific routing and transport layers ...
1.1 Chapter 1 Introduction Data Communication Objectives
... Medium:- Physical path by which a message travels Protocol:- Set of rule governing data communication. ...
... Medium:- Physical path by which a message travels Protocol:- Set of rule governing data communication. ...
Class Notes #1
... exchange information with each other in a meaningful way. – Computer networks may link computers that are all of the same type (homogeneous networks), or they may link computers of several different types (heterogeneous networks) – Size of the network: same room, same floor, same building, same camp ...
... exchange information with each other in a meaningful way. – Computer networks may link computers that are all of the same type (homogeneous networks), or they may link computers of several different types (heterogeneous networks) – Size of the network: same room, same floor, same building, same camp ...
William Stallings Data and Computer Communications
... • Protocol specification • Operates between the same layer on two systems • May involve different operating system • Protocol specification must be precise • Format of data units • Semantics of all fields • allowable sequence of PCUs ...
... • Protocol specification • Operates between the same layer on two systems • May involve different operating system • Protocol specification must be precise • Format of data units • Semantics of all fields • allowable sequence of PCUs ...
The Transport Layer
... • Is optional in UDP • If checksum is non-zero, and receiver computes another value: – Silently drop the packet, no error message detected ...
... • Is optional in UDP • If checksum is non-zero, and receiver computes another value: – Silently drop the packet, no error message detected ...
Internet slides
... • IP addresses are assigned to hosts by their internet service providers • Not physical addresses: IP address does not identify a single node, can swap machines and reuse the same IP address • Not entirely virtual: the IP address determines how packets get to you, and changes when you change your ...
... • IP addresses are assigned to hosts by their internet service providers • Not physical addresses: IP address does not identify a single node, can swap machines and reuse the same IP address • Not entirely virtual: the IP address determines how packets get to you, and changes when you change your ...
ILAFID+ (Live Fiber Monitoring)
... -32dBm, Insertion Loss: 1.5 dB (splitting ratio not included) ...
... -32dBm, Insertion Loss: 1.5 dB (splitting ratio not included) ...
Poster - The University of Manchester
... into PCs at JIVE. The achieved throughputs and packet loss are shown in Architecture of the VLBI-UDP Program the plots to the right. The absence of packet loss clearly shows the superior performance of the UKLight lightpath when compared with the packet switched production network. UDP Data ...
... into PCs at JIVE. The achieved throughputs and packet loss are shown in Architecture of the VLBI-UDP Program the plots to the right. The absence of packet loss clearly shows the superior performance of the UKLight lightpath when compared with the packet switched production network. UDP Data ...
Module 10 presentation
... • IP determines the most efficient route for data based on the routing protocol • The terms unreliable and best-effort do not imply that the system is unreliable and does not work well, but that IP does not verify that the data reached its destination. This function is handled by the upper layer pro ...
... • IP determines the most efficient route for data based on the routing protocol • The terms unreliable and best-effort do not imply that the system is unreliable and does not work well, but that IP does not verify that the data reached its destination. This function is handled by the upper layer pro ...
9. telecommunications
... – Transmission Control Protocol (TCP) • Controls the assembly of a message into smaller packets before transmission, and reassembles them once received ...
... – Transmission Control Protocol (TCP) • Controls the assembly of a message into smaller packets before transmission, and reassembles them once received ...
IP Encapsulator
... dedicated to processing high speed incoming traffic, and a Fast Ethernet interface that is dedicated to management and control. Decoupling the data and management interfaces provides additional flexibility and security for the network architecture, while maximizing performance. High Speed Processing ...
... dedicated to processing high speed incoming traffic, and a Fast Ethernet interface that is dedicated to management and control. Decoupling the data and management interfaces provides additional flexibility and security for the network architecture, while maximizing performance. High Speed Processing ...