Networking - Faculty of Computer Science and Information Technology
... – Arrival/departure screens at airport ...
... – Arrival/departure screens at airport ...
Serial Communications
... The Parity is computed first on the transmitting end, and included as the Parity bit in the frame. The Parity is then recomputed on the receiving end, and the result is compared to the Parity bit value. If the Parity calculation on the receiving end does not match, the receiver knows data corruption ...
... The Parity is computed first on the transmitting end, and included as the Parity bit in the frame. The Parity is then recomputed on the receiving end, and the result is compared to the Parity bit value. If the Parity calculation on the receiving end does not match, the receiver knows data corruption ...
topics
... lower margins less money to expand the network limited available network for more IP-based activities ...
... lower margins less money to expand the network limited available network for more IP-based activities ...
CM0130-1 Hardware and Software Systems
... equalizer and baseline wander compensation for amplitude attenuation and phase shift due to transmission line parasitics. 4B/5B encoding procedure: Each 4-bit data nibble (representing half of a data byte) is mapped into a 5-bit binary code-group that is transmitted bit-serial over the link. ...
... equalizer and baseline wander compensation for amplitude attenuation and phase shift due to transmission line parasitics. 4B/5B encoding procedure: Each 4-bit data nibble (representing half of a data byte) is mapped into a 5-bit binary code-group that is transmitted bit-serial over the link. ...
Introduction to Networks
... Inter-Process Communication • Turn host-to-host connectivity into process-to-process ...
... Inter-Process Communication • Turn host-to-host connectivity into process-to-process ...
TeamTrak uses cheap commodity equipment and software, so it is
... compass + camera) and accelerometer on the foot. Software: Collects sensor data, shares data with neighbors via multi-hop ad-hoc network over WiFi. TeamTrak allows us to explore concepts relevant to current and proposed mobile computing systems: – Cellular phones reporting sensor data. – Mobile cart ...
... compass + camera) and accelerometer on the foot. Software: Collects sensor data, shares data with neighbors via multi-hop ad-hoc network over WiFi. TeamTrak allows us to explore concepts relevant to current and proposed mobile computing systems: – Cellular phones reporting sensor data. – Mobile cart ...
Chapter 1 - UniMAP Portal
... established for duration of conversation • comprising a sequence of physical links • with a dedicated logical channel • eg. telephone network ...
... established for duration of conversation • comprising a sequence of physical links • with a dedicated logical channel • eg. telephone network ...
CHAP10 - Lyle School of Engineering
... • Can’t Replace Large TPS Programs (e.g.: Payroll; Accounting; Production / Operations; Marketing) • Too Slow for High-Speed Data Transfer • Not yet as Functional as Groupware • Require Tight Security Control and Careful Management Planning ...
... • Can’t Replace Large TPS Programs (e.g.: Payroll; Accounting; Production / Operations; Marketing) • Too Slow for High-Speed Data Transfer • Not yet as Functional as Groupware • Require Tight Security Control and Careful Management Planning ...
slides - network systems lab @ sfu
... Sender: transmits T(x), which consists of d+1 data bits AND r redundant bits such that G(x)|T(x), ...
... Sender: transmits T(x), which consists of d+1 data bits AND r redundant bits such that G(x)|T(x), ...
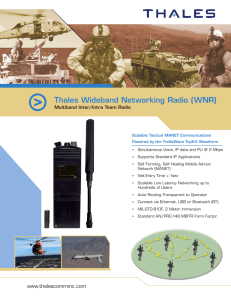
Thales Wideband Networking Radio (WNR)
... communications unit. It is designed to provide robust voice and data communication in the most challenging RF environments. This unique tactical Mobile Ad-Hoc Networking (MANET) product enables rapid deployment of high throughput networks across the harshest conditions. The Thales WNR PHY and MAC la ...
... communications unit. It is designed to provide robust voice and data communication in the most challenging RF environments. This unique tactical Mobile Ad-Hoc Networking (MANET) product enables rapid deployment of high throughput networks across the harshest conditions. The Thales WNR PHY and MAC la ...
Computer Networking
... datagram networks and virtual circuit networks route according to host dest addr or to vc number datagram net : Internet vc network : X.25, frame relay and ATM ...
... datagram networks and virtual circuit networks route according to host dest addr or to vc number datagram net : Internet vc network : X.25, frame relay and ATM ...
William Stallings Data and Computer Communications
... Point to point communication not usually practical Devices are too far apart Large set of devices would need impractical number of connections ...
... Point to point communication not usually practical Devices are too far apart Large set of devices would need impractical number of connections ...
EE579S Computer Security
... node they pass through • Jitter: variation in packet delay • Data overhead in every packet for routing ...
... node they pass through • Jitter: variation in packet delay • Data overhead in every packet for routing ...
Network and Telecommunications
... in Business TELECOMMUNICATIONS – the transmission of data between devices in different locations ...
... in Business TELECOMMUNICATIONS – the transmission of data between devices in different locations ...
Chapter 12 - Key Terms
... Integrity control: mechanisms and procedures that are built into an application system to safeguard information contained within it. Internal output: a printed report or document produced for use inside an organization. Privileged user: a user who has special security access privileges to a system. ...
... Integrity control: mechanisms and procedures that are built into an application system to safeguard information contained within it. Internal output: a printed report or document produced for use inside an organization. Privileged user: a user who has special security access privileges to a system. ...
Language Support for Concurrency
... send bits on a link: transmitter/receiver [clock, modulation,…] send packet on each hop [framing, error detection,…] send packet end to end [addressing, routing] pace transmissions [detect congestion] retransmit erroneous or missing packets [acks, timeout] find destination address from name [DNS] ...
... send bits on a link: transmitter/receiver [clock, modulation,…] send packet on each hop [framing, error detection,…] send packet end to end [addressing, routing] pace transmissions [detect congestion] retransmit erroneous or missing packets [acks, timeout] find destination address from name [DNS] ...
William Stallings Data and Computer Communications
... Corporate internet operating within the organization Uses Internet (TCP/IP and http)technology to deliver documents and resources ...
... Corporate internet operating within the organization Uses Internet (TCP/IP and http)technology to deliver documents and resources ...
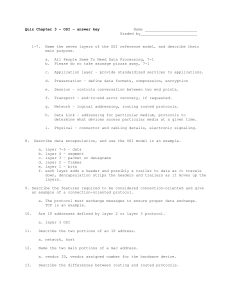
b227_Quiz2
... 56. What is the main purpose of the secondary ring in FDDI protocol? a) If the primary ring fails, the secondary takes over. b) If the primary ring fails, the primary makes a wrap connection with the secondary to heal the ring. c) The secondary alternates with the primary in transmission of data. d) ...
... 56. What is the main purpose of the secondary ring in FDDI protocol? a) If the primary ring fails, the secondary takes over. b) If the primary ring fails, the primary makes a wrap connection with the secondary to heal the ring. c) The secondary alternates with the primary in transmission of data. d) ...
lecture
... First protocol for sending IP datagrams over dial-up links (from 1988) Encapsulation, not much else ...
... First protocol for sending IP datagrams over dial-up links (from 1988) Encapsulation, not much else ...
PowerPoint File - Regis University: Academic Web Server for Faculty
... Bridges • Connects separate networks ▫ One Ethernet network to another one ▫ “Bridges” two network segments together ▫ Makes it appear as if the two segments were a ...
... Bridges • Connects separate networks ▫ One Ethernet network to another one ▫ “Bridges” two network segments together ▫ Makes it appear as if the two segments were a ...
Computer Networks
... convert it to a packet formatted for another protocol before forwarding it. They operate in all seven layers of the OSI model. 26. What is ICMP? ICMP is Internet Control Message Protocol, a network layer protocol of the TCP/IP suite used by hosts and gateways to send notification of datagram problem ...
... convert it to a packet formatted for another protocol before forwarding it. They operate in all seven layers of the OSI model. 26. What is ICMP? ICMP is Internet Control Message Protocol, a network layer protocol of the TCP/IP suite used by hosts and gateways to send notification of datagram problem ...