PDF
... Critical-path driven process • If we can identify common patterns or use cases apriori (or perhaps by analysis of workloads from other similar systems for which data exists)... – Permits us to recognize in advance that particular code paths will arise often and will really determine performance for ...
... Critical-path driven process • If we can identify common patterns or use cases apriori (or perhaps by analysis of workloads from other similar systems for which data exists)... – Permits us to recognize in advance that particular code paths will arise often and will really determine performance for ...
Lesson 11
... Two level addressing (network and host) wastes space Network addresses used even if not connected to Internet Exponential growth of the Internet Single address per host ...
... Two level addressing (network and host) wastes space Network addresses used even if not connected to Internet Exponential growth of the Internet Single address per host ...
topics
... human solution, NOT network solutions A packet switch cannot enforce policy if you want to have a productive and scaleable network ...
... human solution, NOT network solutions A packet switch cannot enforce policy if you want to have a productive and scaleable network ...
Guide to Firewalls and Network Security with Intrusion Detection and
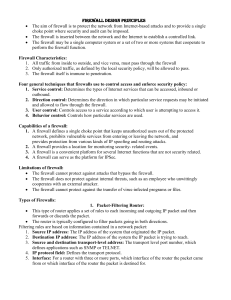
... such as port, IP address, and protocol Review the header, strip it off, and replace it with a new header before sending it to a specific location within the network Fundamental components of firewalls ...
... such as port, IP address, and protocol Review the header, strip it off, and replace it with a new header before sending it to a specific location within the network Fundamental components of firewalls ...
$doc.title
... Seamless mobility and migration Server load balancing Dynamic access control Using multiple wireless access points Energy-efficient networking Adaptive traffic monitoring Denial-of-Service attack detection Network virtualization See http://www.openflow.org/videos/! ...
... Seamless mobility and migration Server load balancing Dynamic access control Using multiple wireless access points Energy-efficient networking Adaptive traffic monitoring Denial-of-Service attack detection Network virtualization See http://www.openflow.org/videos/! ...
Router Architecture
... algorithms to support priorities and guarantees. Support data link layer functionality. ...
... algorithms to support priorities and guarantees. Support data link layer functionality. ...
Sales Meeting - Draware A/S | Tlf. (+45) 45 76 20 21 | Vi
... Packetized voice traffic sent over an IP network Competes with other traffic on the network A new technology that needs real-time, consistent monitoring Sensitive to delay Understanding VoIP Begins with Understanding Delay Normal (not sensitive to delay) example: FTP, HTTP, e-mail, etc. ...
... Packetized voice traffic sent over an IP network Competes with other traffic on the network A new technology that needs real-time, consistent monitoring Sensitive to delay Understanding VoIP Begins with Understanding Delay Normal (not sensitive to delay) example: FTP, HTTP, e-mail, etc. ...
intro-Routing240
... • Connection oriented (state at end points, handshake - TCP) • Connectionless (no state at end points - UDP) ...
... • Connection oriented (state at end points, handshake - TCP) • Connectionless (no state at end points - UDP) ...
Basic Concepts
... but bulk of the design, installation, equipment, and maintenance falls to the Communications Company. Pros: Less expensive, less administration and management Cons: Less control, potential security issues, less performance predictability ...
... but bulk of the design, installation, equipment, and maintenance falls to the Communications Company. Pros: Less expensive, less administration and management Cons: Less control, potential security issues, less performance predictability ...
1-ITN-chap-3g
... Application Protocol - Hypertext Transfer Protocol (HTTP) is a protocol that governs the way a web server and a web client interact. Transport Protocol - Transmission Control Protocol (TCP) is the transport protocol that manages the individual conversations between web servers and web clients. ...
... Application Protocol - Hypertext Transfer Protocol (HTTP) is a protocol that governs the way a web server and a web client interact. Transport Protocol - Transmission Control Protocol (TCP) is the transport protocol that manages the individual conversations between web servers and web clients. ...
Traffic Engineering
... Calculates the routes for traffic demands for edge nodes Service providers then set up MPLS explicit routes between edge routes and match traffic demands over them, creating a full-mesh network Suffers from N-square problem, problems with scalability ...
... Calculates the routes for traffic demands for edge nodes Service providers then set up MPLS explicit routes between edge routes and match traffic demands over them, creating a full-mesh network Suffers from N-square problem, problems with scalability ...
Networking Equipment
... Switch: Because the hub is something of a “drunk,” it can be an inefficient (think about the excess traffic created) and unsecure device. Imagine if you wish to send sensitive credit card information over the network – do you really want every node to receive your electronic signal? To alleviate thi ...
... Switch: Because the hub is something of a “drunk,” it can be an inefficient (think about the excess traffic created) and unsecure device. Imagine if you wish to send sensitive credit card information over the network – do you really want every node to receive your electronic signal? To alleviate thi ...
Flow-based Performance Measurement
... IP Performance Monitoring based on flow/applications is needed in many cases. For mobile operator’s backhaul network, the applications are devided into multiple bearers with proper mobile QoS parameters (e.g. QCI). If the mobile network would manage bearers as QoS and applications, then the performa ...
... IP Performance Monitoring based on flow/applications is needed in many cases. For mobile operator’s backhaul network, the applications are devided into multiple bearers with proper mobile QoS parameters (e.g. QCI). If the mobile network would manage bearers as QoS and applications, then the performa ...
Dasar Jaringan Komputer
... • Relative importance of bandwidth and latency depends on application – For large file transfer, bandwidth is critical – For small messages (HTTP, NFS, etc.), latency is critical – Variance in latency (jitter) can also affect some applications (e.g., audio/video conferencing) ...
... • Relative importance of bandwidth and latency depends on application – For large file transfer, bandwidth is critical – For small messages (HTTP, NFS, etc.), latency is critical – Variance in latency (jitter) can also affect some applications (e.g., audio/video conferencing) ...
ITGS
... – Arranged as a RAID array » Redundant Array of Independent Disks - failover system for hard disks in which multiple hard disks are connected together » the info from one hard disk is mirrored onto another one every time something is saved, so that if a hard disk fails, the computer switches to its ...
... – Arranged as a RAID array » Redundant Array of Independent Disks - failover system for hard disks in which multiple hard disks are connected together » the info from one hard disk is mirrored onto another one every time something is saved, so that if a hard disk fails, the computer switches to its ...
File
... In default discard policy initially, everything is blocked, and services must be added on a caseby-case basis. The default forward policy increases ease of use for end users but provides reduced security. One advantage of a packet-filtering router is its simplicity and transparent to users and a ...
... In default discard policy initially, everything is blocked, and services must be added on a caseby-case basis. The default forward policy increases ease of use for end users but provides reduced security. One advantage of a packet-filtering router is its simplicity and transparent to users and a ...
Communication - Cs.princeton.edu
... –… and the server IP address and port number –Problem: users may log in to another machine E.g., connect from the dorms to another host … and then onward to the blocked server ...
... –… and the server IP address and port number –Problem: users may log in to another machine E.g., connect from the dorms to another host … and then onward to the blocked server ...
Networking Basics and Internet Protocol Stack
... Telco Networks (2 of 2) • Call routing and circuit allocation decided once per call at time of call arrival • End to end path allocation, with dedicated circuit (reserved bandwidth) per active call • All bits travel same path; stay in same order • Call state information crucial in network switches ...
... Telco Networks (2 of 2) • Call routing and circuit allocation decided once per call at time of call arrival • End to end path allocation, with dedicated circuit (reserved bandwidth) per active call • All bits travel same path; stay in same order • Call state information crucial in network switches ...