Chapter 5
... PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
... PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
SAMSUNG Multifunction Printer Security
... working together to achieve a goal. It is this ability to share information over great distances at the speed of light that has created the technological world we live in today. Unfortunately the creation of so many ways to access information has also resulted in so many more ways for unauthorized a ...
... working together to achieve a goal. It is this ability to share information over great distances at the speed of light that has created the technological world we live in today. Unfortunately the creation of so many ways to access information has also resulted in so many more ways for unauthorized a ...
Chapter 5 outline
... PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
... PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
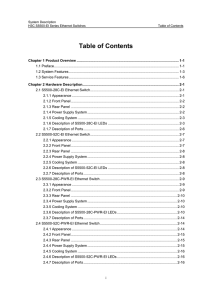
Table of Contents - HP Enterprise Group
... 3.6 STP/RSTP/MSTP ............................................................................................................ 3-36 3.6.1 STP/RSTP ............................................................................................................. 3-36 3.6.2 MSTP ........................... ...
... 3.6 STP/RSTP/MSTP ............................................................................................................ 3-36 3.6.1 STP/RSTP ............................................................................................................. 3-36 3.6.2 MSTP ........................... ...
GISFI_CSeON_201309395
... The U.S. Trade and Development Agency (USTDA) provided a grant to the Ministry of Home Affairs (MHA), Government of India to partially fund a feasibility study to establish an Integrated Emergency Communications System (IECS) and supporting infrastructure in Hyderabad, Andhra Pradesh, India [68]. Th ...
... The U.S. Trade and Development Agency (USTDA) provided a grant to the Ministry of Home Affairs (MHA), Government of India to partially fund a feasibility study to establish an Integrated Emergency Communications System (IECS) and supporting infrastructure in Hyderabad, Andhra Pradesh, India [68]. Th ...
Chapter 1 - Anvari.Net
... 27. In general, what type of cabling can sustain the most bending without impairing transmission? Answer: D. UTP 28. What is the maximum amount of insulation you should strip from copper wires before inserting them into connectors? Answer: C. 1 inch 29. What is the maximum amount you should untwist ...
... 27. In general, what type of cabling can sustain the most bending without impairing transmission? Answer: D. UTP 28. What is the maximum amount of insulation you should strip from copper wires before inserting them into connectors? Answer: C. 1 inch 29. What is the maximum amount you should untwist ...
Chapter 5 outline
... PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
... PPP for dial-up access point-to-point link between Ethernet switch and host broadcast (shared wire or medium) traditional Ethernet upstream HFC 802.11 wireless LAN ...
Routing - La Salle University
... • All destination addresses with the same first part will be forwarded (routed) to the same packet switch. – That’s not exactly true. A given network destination (as opposed to node destination) may be listed on the table a few times. – This allows the router to “re-route” packets if previous packet ...
... • All destination addresses with the same first part will be forwarded (routed) to the same packet switch. – That’s not exactly true. A given network destination (as opposed to node destination) may be listed on the table a few times. – This allows the router to “re-route” packets if previous packet ...
ppt1
... "Phex is entirely based on William W. Wong´s Furi. As Furi has not been updated for over one year I decided to continue it´s development. But in case Wong is currently working on a new version of Furi i decided to rename my branch of the client to Phex. FURI is a Gnutella protocol-compatible Java pr ...
... "Phex is entirely based on William W. Wong´s Furi. As Furi has not been updated for over one year I decided to continue it´s development. But in case Wong is currently working on a new version of Furi i decided to rename my branch of the client to Phex. FURI is a Gnutella protocol-compatible Java pr ...
Business Ready Branch Solutions for Enterprise and Small
... AccessPath, AtmDirector, Browse with Me, CCIP, CCSI, CD-PAC, CiscoLink, the Cisco Powered Network logo, Cisco Systems Networking Academy, the Cisco Systems Networking Academy logo, Cisco Unity, Fast Step, Follow Me Browsing, FormShare, FrameShare, IGX, Internet Quotient, IP/VC, iQ Breakthrough, iQ E ...
... AccessPath, AtmDirector, Browse with Me, CCIP, CCSI, CD-PAC, CiscoLink, the Cisco Powered Network logo, Cisco Systems Networking Academy, the Cisco Systems Networking Academy logo, Cisco Unity, Fast Step, Follow Me Browsing, FormShare, FrameShare, IGX, Internet Quotient, IP/VC, iQ Breakthrough, iQ E ...
Network Security White Paper
... organizations, such as CERT Coordination Center (CERT/CC: http:// www.cert.org/ ). Whenever we find security vulnerabilities in the products, we provide appropriate countermeasures. For more information, see the information posted in our online Knowledge Base at: http://www.ricoh-usa.com/support/kno ...
... organizations, such as CERT Coordination Center (CERT/CC: http:// www.cert.org/ ). Whenever we find security vulnerabilities in the products, we provide appropriate countermeasures. For more information, see the information posted in our online Knowledge Base at: http://www.ricoh-usa.com/support/kno ...
Low Level Design - Juniper Networks
... the individual campus LAN, the Virtual Chassis size can vary in total number of members. The configurations required to support this design are detailed in later sections of this document. Figure 1 shows a four-member EX3300 Virtual Chassis. ...
... the individual campus LAN, the Virtual Chassis size can vary in total number of members. The configurations required to support this design are detailed in later sections of this document. Figure 1 shows a four-member EX3300 Virtual Chassis. ...
draft-li-idr-cc-bgp-arch-00
... This document introduces an architecture of using BGP for central control. Some use cases under this new framework are also discussed. For specific use cases, making necessary extensions in BGP are required. ...
... This document introduces an architecture of using BGP for central control. Some use cases under this new framework are also discussed. For specific use cases, making necessary extensions in BGP are required. ...
The Network Layer - London South Bank University
... Routing Information Protocol (RIP) a) RIP is based on distance vector routing, which uses the BellmanFord algorithm for calculating the routing table. b) RIP treats all network equals; the cost of passing thru a network is the same: one hop count per network. c) Each router/node maintains a vector ...
... Routing Information Protocol (RIP) a) RIP is based on distance vector routing, which uses the BellmanFord algorithm for calculating the routing table. b) RIP treats all network equals; the cost of passing thru a network is the same: one hop count per network. c) Each router/node maintains a vector ...
Configuring VoIP for SonicOS Standard
... The Session Initiation Protocol (SIP) standard was developed by the Internet Engineering Task Force (IETF). RFC 2543 was released in March 1999. RFC 3261 was released in June 2002. SIP is a signaling protocol for initiating, managing and terminating sessions. SIP supports ‘presence’ and mobility and ...
... The Session Initiation Protocol (SIP) standard was developed by the Internet Engineering Task Force (IETF). RFC 2543 was released in March 1999. RFC 3261 was released in June 2002. SIP is a signaling protocol for initiating, managing and terminating sessions. SIP supports ‘presence’ and mobility and ...
IntroductionToUnix_S14 - Silicon Valley University
... 1982, prototype Internet using TCP/IP became operational and in 1983, all U.S. military sites connected to ARPANET was on the Internet. 1991, first Web Browser, Mosaic, was developed by National Center for Supercomputer Application (NCSA). 1995, World Wide Web browsing surpassed FTP as the maj ...
... 1982, prototype Internet using TCP/IP became operational and in 1983, all U.S. military sites connected to ARPANET was on the Internet. 1991, first Web Browser, Mosaic, was developed by National Center for Supercomputer Application (NCSA). 1995, World Wide Web browsing surpassed FTP as the maj ...
EAP701 / EAP717 v1.11 Enterprise Access Point
... 4IPNET, INC. does not assume any liability arising out the application or use of any products, or software described herein. Neither does it convey any license under its parent rights not the parent rights of others. 4IPNET further reserves the right to make changes in any products described herein ...
... 4IPNET, INC. does not assume any liability arising out the application or use of any products, or software described herein. Neither does it convey any license under its parent rights not the parent rights of others. 4IPNET further reserves the right to make changes in any products described herein ...
Securing Wireless Systems
... numbers, passwords, or other information. Securing wireless communication is an important aspect of any security professional’s duties. ...
... numbers, passwords, or other information. Securing wireless communication is an important aspect of any security professional’s duties. ...
Link-State Routing Protocols
... Link-State Routing Process – step 2 Sending Hello Packets to Neighbors Link state routing protocols use a hello protocol Purpose of a hello protocol: To discover neighbors (that use the same link state routing protocol) on its link ...
... Link-State Routing Process – step 2 Sending Hello Packets to Neighbors Link state routing protocols use a hello protocol Purpose of a hello protocol: To discover neighbors (that use the same link state routing protocol) on its link ...
EdgeMarc 5300 Network Services Gateway
... The EdgeMarc Series 5300 network services gateway provides the demarcation point for realtime, interactive IP services. The EdgeMarc 5300 is used in large office deployments and is RoHS (Restriction of certain Hazardous Substances - a directive in electrical and electronic equipment) and WEEE compli ...
... The EdgeMarc Series 5300 network services gateway provides the demarcation point for realtime, interactive IP services. The EdgeMarc 5300 is used in large office deployments and is RoHS (Restriction of certain Hazardous Substances - a directive in electrical and electronic equipment) and WEEE compli ...
7: TCP - unimi.it
... bytes data results in a UDP datagram with X bytes of data – not so with TCP In TCP, the stream of bytes coming from an application is broken at arbitrary points by TCP into the “best” size chunks to send Sender may write 10 bytes then 15 then 30 but this is not in general visible to the receiver ...
... bytes data results in a UDP datagram with X bytes of data – not so with TCP In TCP, the stream of bytes coming from an application is broken at arbitrary points by TCP into the “best” size chunks to send Sender may write 10 bytes then 15 then 30 but this is not in general visible to the receiver ...