S-72.423 Telecommunication Systems
... UMTS supports wide range of applications that posses different quality of service (QoS) requirements. Applications and services can be divided in different groups, depending on QoS requirements. Four traffic classes can been identified: Conversational class (very delay-sensitive traffic) Streami ...
... UMTS supports wide range of applications that posses different quality of service (QoS) requirements. Applications and services can be divided in different groups, depending on QoS requirements. Four traffic classes can been identified: Conversational class (very delay-sensitive traffic) Streami ...
3G-GPRS GTP Robustness Testing
... • From the test result, the first observation was that buffer overflows are the major vulnerabilities in GTP protocol stack and often found in the information element without specific length indication. Bits Octets ...
... • From the test result, the first observation was that buffer overflows are the major vulnerabilities in GTP protocol stack and often found in the information element without specific length indication. Bits Octets ...
To Proposed a Novel Technique to Remove Effective Collision by
... Abstract— In wireless communication system, group of nodes forms wireless sensor network (WSN). During communication these nodes makes a suitable path for transferring the information. Size of WSN depends on the type and quality of service, the service coverage area, and the scalability of the servi ...
... Abstract— In wireless communication system, group of nodes forms wireless sensor network (WSN). During communication these nodes makes a suitable path for transferring the information. Size of WSN depends on the type and quality of service, the service coverage area, and the scalability of the servi ...
Measurement Based Routing Strategies on Overlay Architectures Tuna G ¨uven
... Higher processing power and lower bandwidth Used to create alternative paths · Source attaches an additional IP header with the address of an overlay node as the destination address · Overlay node strips the extra IP header and forwards the packet to the destination Provides multiple routes for each ...
... Higher processing power and lower bandwidth Used to create alternative paths · Source attaches an additional IP header with the address of an overlay node as the destination address · Overlay node strips the extra IP header and forwards the packet to the destination Provides multiple routes for each ...
Part I: Introduction
... sent to neighbors Neighbors in turn send out new advertisements if their tables changed Link failure info quickly propagates to entire net Poison reverse used to prevent ping-pong loops (infinite distance = 16 hops) Routers can request info about neighbor’s cost Advertisements are sent via UDP using ...
... sent to neighbors Neighbors in turn send out new advertisements if their tables changed Link failure info quickly propagates to entire net Poison reverse used to prevent ping-pong loops (infinite distance = 16 hops) Routers can request info about neighbor’s cost Advertisements are sent via UDP using ...
Digital Business Networks Networking Models: OSI and TCP/IP 2.1
... 4) What do the Open Systems Interconnection (OSI) and the Transmission Control Protocol/Internet Protocol (TCP/IP) models have in common? Answer: First, they are both open architecture models. This means that anyone, anywhere, at any time, can freely design or create technologies based on these mode ...
... 4) What do the Open Systems Interconnection (OSI) and the Transmission Control Protocol/Internet Protocol (TCP/IP) models have in common? Answer: First, they are both open architecture models. This means that anyone, anywhere, at any time, can freely design or create technologies based on these mode ...
mung-class-mar08 - Department of Computer Science
... – Delay-based routing unsuccessful in the early days – Oscillation as routers adapt to out-of-date information – Most Internet transfers are very short-lived Research ...
... – Delay-based routing unsuccessful in the early days – Oscillation as routers adapt to out-of-date information – Most Internet transfers are very short-lived Research ...
The following paper was originally published in the
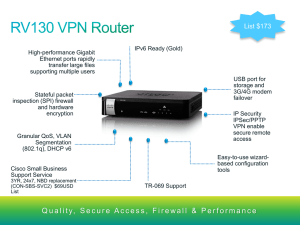
... by specifying the local host’s IP address as one end of the tunnel and the remote host’s IP address (point-to-point address) as the other end. The tunnel transforms all the packets that are given to the tunnel device, stores the original destination address and the original protocol in the body of t ...
... by specifying the local host’s IP address as one end of the tunnel and the remote host’s IP address (point-to-point address) as the other end. The tunnel transforms all the packets that are given to the tunnel device, stores the original destination address and the original protocol in the body of t ...
Slide 1
... • Denial of service attacks are a lower level attack that are used against P2P systems. Lower level attacks focus on the communication aspect (TCP/IP) of P2P systems. Generally, a DoS attack is an attempt to make a computer resource unavailable to those who intend to use it. The most common form of ...
... • Denial of service attacks are a lower level attack that are used against P2P systems. Lower level attacks focus on the communication aspect (TCP/IP) of P2P systems. Generally, a DoS attack is an attempt to make a computer resource unavailable to those who intend to use it. The most common form of ...
Network designers - ECSE - Rensselaer Polytechnic Institute
... 1) make it so simple that there are obviously no deficiencies, and 2) make it so complicated that there are no ...
... 1) make it so simple that there are obviously no deficiencies, and 2) make it so complicated that there are no ...
Lesson4
... In the Napster architecture, P2P file-sharing software connects your PC to a central server that contains a directory of all of the other users (peers) in the network. When you request a file, the software searches the directory for nay other users who have that file and are online at that moment. I ...
... In the Napster architecture, P2P file-sharing software connects your PC to a central server that contains a directory of all of the other users (peers) in the network. When you request a file, the software searches the directory for nay other users who have that file and are online at that moment. I ...
EURESCOM - SALTAMONTES
... destination. MPLS supports LIFO (last in first out) for label stacks. However, now LSRs have to do some more than mapping to
.LSRs must take into
account stack processing.
“Penultimate hop popping”
...
... destination. MPLS supports LIFO (last in first out) for label stacks. However, now LSRs have to do some more than mapping
doc file - Prof. Paul Mc Kevitt
... II. RELATED WORK Packet delay from network congestion has been partially alleviated using routing protocols and application protocols such as real-time transport protocol (RTP) that have been developed to assign a higher priority to time dependant data. However, it is also the case that some servers ...
... II. RELATED WORK Packet delay from network congestion has been partially alleviated using routing protocols and application protocols such as real-time transport protocol (RTP) that have been developed to assign a higher priority to time dependant data. However, it is also the case that some servers ...
Mobile Wireless
... • allows the combination of multiple timeslots • Channels can be multiplexed together to offer a data rate of up to 56 Kbit/s when using all four slots (14.4 Kbs/channel) • because each time slot could carry a conventional conversation, the use of multiple slots restricts the capacity for speech tra ...
... • allows the combination of multiple timeslots • Channels can be multiplexed together to offer a data rate of up to 56 Kbit/s when using all four slots (14.4 Kbs/channel) • because each time slot could carry a conventional conversation, the use of multiple slots restricts the capacity for speech tra ...
Routing
... • Once a TCP connection has been terminated there is some unfinished business: – What if the ACK is lost? • The last FIN will be resent and it must be ACK’d. ...
... • Once a TCP connection has been terminated there is some unfinished business: – What if the ACK is lost? • The last FIN will be resent and it must be ACK’d. ...
1 - Jolata
... communication that pushes CSPs to deploy new revenue-generating capabilities at the edge, rather than the core. Software-Defined-Networking (SDN) and Network Function Virtualization (NFV) are two major innovations that are disrupting the market. SDN and NFV are two major architectural shifts in the ...
... communication that pushes CSPs to deploy new revenue-generating capabilities at the edge, rather than the core. Software-Defined-Networking (SDN) and Network Function Virtualization (NFV) are two major innovations that are disrupting the market. SDN and NFV are two major architectural shifts in the ...
On the Reliability and Additional Overhead of Reliable On
... agent receives both control packets and data packets. The link layer simulates the data link protocols. It also sets the MAC destination address in the MAC header of the packet. This function is implemented for two different issues: finding the next-hop-node’s IP address and converting IP address in ...
... agent receives both control packets and data packets. The link layer simulates the data link protocols. It also sets the MAC destination address in the MAC header of the packet. This function is implemented for two different issues: finding the next-hop-node’s IP address and converting IP address in ...
Gecko: A Contention-Oblivious Design for the
... – Low maintenance : no wires – Low power: no large switches – Low cost: all of the above – Fault tolerant: multiple network paths – High performance: multiple network paths ...
... – Low maintenance : no wires – Low power: no large switches – Low cost: all of the above – Fault tolerant: multiple network paths – High performance: multiple network paths ...
paper
... At the receiver, a buffer is required to store temporarily the packets before they are successfully decoded. Due to the differential delay between the two paths, this is potentially a critical issue. In this paper, for simplicity, we assume that a sufficient buffer is available at the receiver; late ...
... At the receiver, a buffer is required to store temporarily the packets before they are successfully decoded. Due to the differential delay between the two paths, this is potentially a critical issue. In this paper, for simplicity, we assume that a sufficient buffer is available at the receiver; late ...