Kuliah Komunikasi Data
... Project 802, to set standards to enable intercommunication among equipment from a variety of manufacturers. Project 802 is a way of specifying functions of the physical layer and the data link layer of major LAN protocols. ...
... Project 802, to set standards to enable intercommunication among equipment from a variety of manufacturers. Project 802 is a way of specifying functions of the physical layer and the data link layer of major LAN protocols. ...
23-wrapup
... • Traffic data rate, pattern (bursty or constant bit rate), target (multipoint or single destination, mobile or fixed) • Delay and loss sensitivity • Other application-support services • Overlays, Active Networks, Data-oriented, … ...
... • Traffic data rate, pattern (bursty or constant bit rate), target (multipoint or single destination, mobile or fixed) • Delay and loss sensitivity • Other application-support services • Overlays, Active Networks, Data-oriented, … ...
PPT
... The Internet is the physical connection of millions of networks. The Web uses the Internet for its existence The Web consists of hypertext embedded on Web pages that are hosted on Web sites Web browsers display a Web document and enable users to link to other Web pages Web servers respond to the req ...
... The Internet is the physical connection of millions of networks. The Web uses the Internet for its existence The Web consists of hypertext embedded on Web pages that are hosted on Web sites Web browsers display a Web document and enable users to link to other Web pages Web servers respond to the req ...
Network - Missouri State University
... Voice over IP (VoIP) • Voice over IP (VoIP) - uses _______ technology to transmit voice calls over long-distance telephone lines ...
... Voice over IP (VoIP) • Voice over IP (VoIP) - uses _______ technology to transmit voice calls over long-distance telephone lines ...
Session5-Group4-Networking
... query/response protocol that is widely used for querying databases in order to determine the registrant or assignee of Internet resources, such as a domain name, an IP address block, or an autonomous system number. ...
... query/response protocol that is widely used for querying databases in order to determine the registrant or assignee of Internet resources, such as a domain name, an IP address block, or an autonomous system number. ...
Test 3 Emerge Terms
... Really Simple Syndication (RSS): web technology used to automatically deliver frequently updated web content. Router: a network device that manages network traffic by evaluating messages and routing them over the fastest path to their destination. The majority of these hardware devices are manufactu ...
... Really Simple Syndication (RSS): web technology used to automatically deliver frequently updated web content. Router: a network device that manages network traffic by evaluating messages and routing them over the fastest path to their destination. The majority of these hardware devices are manufactu ...
Kuliah Komunikasi Data
... Project 802, to set standards to enable intercommunication among equipment from a variety of manufacturers. Project 802 is a way of specifying functions of the physical layer and the data link layer of major LAN protocols. ...
... Project 802, to set standards to enable intercommunication among equipment from a variety of manufacturers. Project 802 is a way of specifying functions of the physical layer and the data link layer of major LAN protocols. ...
Abstract: Performance Analysis of RPL over AMI (Advanced
... operated by IP internet. With this, the researchers have come up with M2M communication paradigm to standardize the communication of IP operated machines with end hosts connected via traditional internet infrastructure and 3G/4G access network broadening their reach to distant networks. The traffic ...
... operated by IP internet. With this, the researchers have come up with M2M communication paradigm to standardize the communication of IP operated machines with end hosts connected via traditional internet infrastructure and 3G/4G access network broadening their reach to distant networks. The traffic ...
STATE UNIVERSITY OF NEW YORK COLLEGE OF TECHNOLOGY CANTON, NEW YORK
... H. CATALOG DESCRIPTION: This course will cover topics include: Network topologies and connectivity devices, TCP/IP protocol suite and internet protocol addressing, networks and sub-networks, network-layer protocols, internet control message protocol, transport layer protocol, internet protocol ver ...
... H. CATALOG DESCRIPTION: This course will cover topics include: Network topologies and connectivity devices, TCP/IP protocol suite and internet protocol addressing, networks and sub-networks, network-layer protocols, internet control message protocol, transport layer protocol, internet protocol ver ...
Chapter 4 PowerPoint
... computers at businesses as well as at your home. In the 1980’s, Ethernet LANs used coax cable in a bus configuration, but now they use twisted pair wire in a star configuration. Each network adapter has a hard-coded MAC address. To see this address on the Ethernet adapter on a PC, open a command pro ...
... computers at businesses as well as at your home. In the 1980’s, Ethernet LANs used coax cable in a bus configuration, but now they use twisted pair wire in a star configuration. Each network adapter has a hard-coded MAC address. To see this address on the Ethernet adapter on a PC, open a command pro ...
Presentation 10
... Second Step: Internet[work] • A collection of interconnected networks • Host: network endpoints (computer, PDA, light switch, …) • Router: node that connects networks • Internet vs. internet ...
... Second Step: Internet[work] • A collection of interconnected networks • Host: network endpoints (computer, PDA, light switch, …) • Router: node that connects networks • Internet vs. internet ...
Network Fundamentals
... Successful transmission of data depends on: The quality of the signal being transmitted Characteristics of the transmission medium Data rate – bits per second in data communications Bandwidth – bandwidth or signal is constrained by the transmitter and the nature of the transmission in cycles per sec ...
... Successful transmission of data depends on: The quality of the signal being transmitted Characteristics of the transmission medium Data rate – bits per second in data communications Bandwidth – bandwidth or signal is constrained by the transmitter and the nature of the transmission in cycles per sec ...
Career Highlights - University of the Pacific
... products. Instituted electronic bonding and product training, which reduced switch over time to three to seven days. Diagnosed equipment failure point and recommended adding a fan to aide in cooling equipment, which eliminated power supply failures. Designed and executed internet backbone arch ...
... products. Instituted electronic bonding and product training, which reduced switch over time to three to seven days. Diagnosed equipment failure point and recommended adding a fan to aide in cooling equipment, which eliminated power supply failures. Designed and executed internet backbone arch ...
ppt3
... at each layer interacts only with adjacent layers (fig. 16.2) Each frame is nested in next one, from lower layer of stack (fig. 16.4) Each layer at destination receives frame sent from corresponding layer at origin (fig. 16.5) ...
... at each layer interacts only with adjacent layers (fig. 16.2) Each frame is nested in next one, from lower layer of stack (fig. 16.4) Each layer at destination receives frame sent from corresponding layer at origin (fig. 16.5) ...
Why Internetworking? - California State University, Long Beach
... "One of the most utterly scintillating notions presented in the text is that there is no such thing as an internet. Universal service exists by deftly combining software and hardware into a virtual network system, where the communication system is an abstraction." Dr. Jennifer Seitzer University of ...
... "One of the most utterly scintillating notions presented in the text is that there is no such thing as an internet. Universal service exists by deftly combining software and hardware into a virtual network system, where the communication system is an abstraction." Dr. Jennifer Seitzer University of ...
ModuleONEandTWO
... Numbers of Networking Base 2 is called binary and uses only 0’s and 1’s to represent a number. Base 10 is the decimal system we use on the regular basis. (0,1,2,3,4,5…) Base 16 is the hexadecimal system uses the first ten numbers, (0-9), and the first six letters of the alphabet, (A-F). There ar ...
... Numbers of Networking Base 2 is called binary and uses only 0’s and 1’s to represent a number. Base 10 is the decimal system we use on the regular basis. (0,1,2,3,4,5…) Base 16 is the hexadecimal system uses the first ten numbers, (0-9), and the first six letters of the alphabet, (A-F). There ar ...
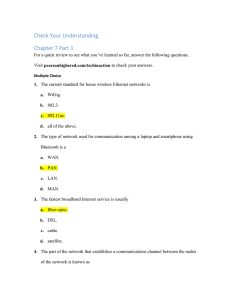
Check Your Understanding Chapter 7 Part 1 For a quick review to
... 1. The current standard for home wireless Ethernet networks is a. WiGig. b. 802.3. c. 802.11ac. d. all of the above. 2. The type of network used for communication among a laptop and smartphone using Bluetooth is a a. WAN. b. PAN. c. LAN. d. MAN. 3. The fastest broadband Internet service is usually a ...
... 1. The current standard for home wireless Ethernet networks is a. WiGig. b. 802.3. c. 802.11ac. d. all of the above. 2. The type of network used for communication among a laptop and smartphone using Bluetooth is a a. WAN. b. PAN. c. LAN. d. MAN. 3. The fastest broadband Internet service is usually a ...
Troubleshooting your PC - Hill City SD 51-2
... A network links computers for communicating and sharing information and resources. A network must provide ...
... A network links computers for communicating and sharing information and resources. A network must provide ...







![Computer Networks [Opens in New Window]](http://s1.studyres.com/store/data/001432217_1-c782ef807e718d5ed80f4e9484b1006a-300x300.png)