Internet Architecture and Assumptions
... • Survivability compromise: Heterogenous network -> less information available to end hosts and Internet level recovery mechanisms ...
... • Survivability compromise: Heterogenous network -> less information available to end hosts and Internet level recovery mechanisms ...
Week 2: Routing vs. Switching
... Layering Questions • Do core devices care about layers >3 ? – Generally no, but... – What about performance? – Impact of speed mismatches on tcp vs. udp ...
... Layering Questions • Do core devices care about layers >3 ? – Generally no, but... – What about performance? – Impact of speed mismatches on tcp vs. udp ...
INTRODUCTION - mien phi
... Presentation: formats data for presentation to the user, provides data interfaces, data compression and translation between different data formats Session: responsible for initiating, maintaining and terminating each logical session between sender and ...
... Presentation: formats data for presentation to the user, provides data interfaces, data compression and translation between different data formats Session: responsible for initiating, maintaining and terminating each logical session between sender and ...
Business Data Communications and Networking
... End to end delivery of packets Creates logical paths Path determination (routing) Hides the lower layers making things hardware independent Uses logical hierarchical addresses ...
... End to end delivery of packets Creates logical paths Path determination (routing) Hides the lower layers making things hardware independent Uses logical hierarchical addresses ...
cos440-Intro
... • May move frames from one network architecture to another This may involve addressing issues Physical addresses may vary between architectures Data frame sizes may vary between architectures ...
... • May move frames from one network architecture to another This may involve addressing issues Physical addresses may vary between architectures Data frame sizes may vary between architectures ...
Foundations of Networking Networking CS 3470, Section 1 Sarah Diesburg
... Macro view: How does this packet relate to others? Micro view: What's inside the packet? How's it laid out? ...
... Macro view: How does this packet relate to others? Micro view: What's inside the packet? How's it laid out? ...
Chapter 16
... is underlying hardware bandwidth TW is sliding window throughput TG is stop-and-go throughput W is the window size ...
... is underlying hardware bandwidth TW is sliding window throughput TG is stop-and-go throughput W is the window size ...
Computer Networking
... makes promises about how long it will take to deliver the data from sender to receiver. ...
... makes promises about how long it will take to deliver the data from sender to receiver. ...
The Internet - Matthew T. Jones
... develop a packet switching method called “hot potato” routing. ...
... develop a packet switching method called “hot potato” routing. ...
Routing Protocols & Troubleshooting the Network Semester 2
... information about destination network Send data to default network when you don’t have info in routing table Keeps routing table shorter IP Default-network command addes to all routers in network, example: IP default-network 152.43.0.0 ...
... information about destination network Send data to default network when you don’t have info in routing table Keeps routing table shorter IP Default-network command addes to all routers in network, example: IP default-network 152.43.0.0 ...
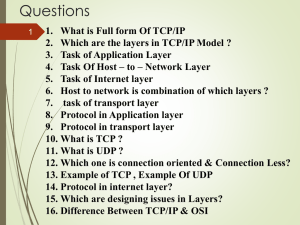
Chapter 4 : TCP/IP and OSI
... from different systems to communicate • Shared conventions for communicating information are called protocols • Includes syntax, semantics, and timing ...
... from different systems to communicate • Shared conventions for communicating information are called protocols • Includes syntax, semantics, and timing ...
pptx
... – packets from many ongoing exchanges can travel on one wire, – which makes it much cheaper to build a network – many computers can share the same wire without interfering. ...
... – packets from many ongoing exchanges can travel on one wire, – which makes it much cheaper to build a network – many computers can share the same wire without interfering. ...
Introduction - Jigar Pandya
... Refers to protocols in which messages are divided into packets before they are sent. Each packet is then transmitted individually and can even follow different routes to its ...
... Refers to protocols in which messages are divided into packets before they are sent. Each packet is then transmitted individually and can even follow different routes to its ...
Chapter 4. - Amoud University
... most important protocol in this layer. It is a connectionless protocol that does not assume reliability from lower layers. IP does not provide reliability, flow control, or error recovery. These functions must be provided at a higher level. IP provides a routing function that attempts to deliver tra ...
... most important protocol in this layer. It is a connectionless protocol that does not assume reliability from lower layers. IP does not provide reliability, flow control, or error recovery. These functions must be provided at a higher level. IP provides a routing function that attempts to deliver tra ...
TCP/IP Protocol Architecture - Department of Electrical Engineering
... confirm file management program at destination is prepared to accept and store file ...
... confirm file management program at destination is prepared to accept and store file ...
Slide 1 - Department of Electrical Engineering & Computer Science
... Actions that are to be taken when a certain event occurs, e.g. sending or receiving messages, expiry of timers The purpose of a protocol is to provide a service to the layer above ...
... Actions that are to be taken when a certain event occurs, e.g. sending or receiving messages, expiry of timers The purpose of a protocol is to provide a service to the layer above ...
LAN BASICS
... • Used by network management utilities to manage network devices • For example, a manageable hub that support SNMP can be managed from a remote location using a SNMP based LAN management software ...
... • Used by network management utilities to manage network devices • For example, a manageable hub that support SNMP can be managed from a remote location using a SNMP based LAN management software ...
A crash course in networking
... • TCP/IP is a suite of international commercial-off-the-shelf protocols – Protocols that require handshaking or a response/replay do not work over long delays and intermittently connected networks – Protocols that require infrastructure may not necessarily be applicable to space unless caching of in ...
... • TCP/IP is a suite of international commercial-off-the-shelf protocols – Protocols that require handshaking or a response/replay do not work over long delays and intermittently connected networks – Protocols that require infrastructure may not necessarily be applicable to space unless caching of in ...
Slide 1
... – IP is a connectionless or datagram internetwork service, providing no end-toend delivery guarantees. IP datagrams may arrive at the destination host damaged, duplicated, out of order, or not at all. The layers above IP are responsible for reliable delivery service when it is required. – The IP pro ...
... – IP is a connectionless or datagram internetwork service, providing no end-toend delivery guarantees. IP datagrams may arrive at the destination host damaged, duplicated, out of order, or not at all. The layers above IP are responsible for reliable delivery service when it is required. – The IP pro ...
TCP/IP Support Protocols
... Diskless workstations have no way to know own IP address IP addresses are set by software configuration (SA) Ethernet port is on card itself.. can’t be changed ...
... Diskless workstations have no way to know own IP address IP addresses are set by software configuration (SA) Ethernet port is on card itself.. can’t be changed ...
Trojan Horse
... 2. Run “Exploit” scripts against open ports 3. Get access to Shell program which is “suid” (has “root” privileges). 4. Download from Hacker Web site special versions of systems files that will let Cracker have free access in the future without his cpu time or disk storage space being noticed by audi ...
... 2. Run “Exploit” scripts against open ports 3. Get access to Shell program which is “suid” (has “root” privileges). 4. Download from Hacker Web site special versions of systems files that will let Cracker have free access in the future without his cpu time or disk storage space being noticed by audi ...
Ref_Models
... • ethernet topology: original topology was bus, as above. Signals broadcast in both directions to all receivers. • can also be configured as tree, but uses same protocol. ...
... • ethernet topology: original topology was bus, as above. Signals broadcast in both directions to all receivers. • can also be configured as tree, but uses same protocol. ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.