A Rapidly Deployable Radio Network
... The main objective of the RDRN architecture is to use an adaptive point-to-point topology to gain the advantages of ATM for wireless networks. Figure 1 shows a high-level view of the RDRN system which is made up of two types of nodes: Remote Nodes (RNs) to provide wireless ATM access to end-users an ...
... The main objective of the RDRN architecture is to use an adaptive point-to-point topology to gain the advantages of ATM for wireless networks. Figure 1 shows a high-level view of the RDRN system which is made up of two types of nodes: Remote Nodes (RNs) to provide wireless ATM access to end-users an ...
Chapter 24 Wireless Networking
... • Configuring a wireless access point is often done through a Web browser – Enter the WAP’s default IP address (see your documentation or try 192.168.1.1) in your browser – Enter the default administrative password (in your documentation) to log in • The next few slides show some screenshots of the ...
... • Configuring a wireless access point is often done through a Web browser – Enter the WAP’s default IP address (see your documentation or try 192.168.1.1) in your browser – Enter the default administrative password (in your documentation) to log in • The next few slides show some screenshots of the ...
Ch5-Wireless_LANs
... experience from wireless WAN and mobile phones can be used coverage of larger areas possible (radio can penetrate walls, furniture etc.) ...
... experience from wireless WAN and mobile phones can be used coverage of larger areas possible (radio can penetrate walls, furniture etc.) ...
Wi-Fi™ Module Product Training
... Built on the IEEE 802.11 standard Conformance testing performed by the non-profit Wi-Fi Alliance (formed in 1999) ...
... Built on the IEEE 802.11 standard Conformance testing performed by the non-profit Wi-Fi Alliance (formed in 1999) ...
Embedded NGX 6.0 Release Notes
... autonomous system (AS). OSPF chooses the least-cost path as the best path. It is suitable for complex networks with a large number of routers because it provides equal-cost, multi-path routing, where packets to a single destination can be sent via more than one interface simultaneously. In a link-st ...
... autonomous system (AS). OSPF chooses the least-cost path as the best path. It is suitable for complex networks with a large number of routers because it provides equal-cost, multi-path routing, where packets to a single destination can be sent via more than one interface simultaneously. In a link-st ...
LAAC: A Location-Aware Access Control Protocol
... In LAAC, we assume an infrastructure WLAN system based on IEEE 802.11 [1], and an wireless mobile devices (e.g. wireless laptops, PDAs) can communicate with each other through access points. Moreover, we assume that access points can be equipped with directional antennas [8] so as to control the ang ...
... In LAAC, we assume an infrastructure WLAN system based on IEEE 802.11 [1], and an wireless mobile devices (e.g. wireless laptops, PDAs) can communicate with each other through access points. Moreover, we assume that access points can be equipped with directional antennas [8] so as to control the ang ...
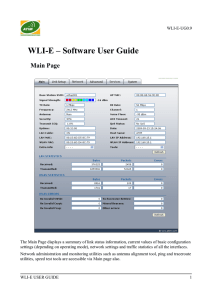
WLI-E – Software User Guide
... 36, 48, 54Mbps (802.11a) are possible. Typically, the higher the signal, the higher the data rate and consequently the higher the data throughput. For the maximum data throughput (54Mbps), a -70dBm or better signal is required typically. Frequency: This is the operating frequency of the 802.11 Servi ...
... 36, 48, 54Mbps (802.11a) are possible. Typically, the higher the signal, the higher the data rate and consequently the higher the data throughput. For the maximum data throughput (54Mbps), a -70dBm or better signal is required typically. Frequency: This is the operating frequency of the 802.11 Servi ...
Wireless Networks for Dummies
... Wireless encryption (WEP) or Wi-Fi Protected Access (WPA), which help protect your wireless network. For most routers, you will provide a passphrase that your router uses to generate several keys. Make sure your passphrase is unique and long (you don't need to memorize it). Your administrative passw ...
... Wireless encryption (WEP) or Wi-Fi Protected Access (WPA), which help protect your wireless network. For most routers, you will provide a passphrase that your router uses to generate several keys. Make sure your passphrase is unique and long (you don't need to memorize it). Your administrative passw ...
App Development for Smart Devices
... Overview • Bluetooth is a specification for the use of low power wireless communications over short distance. • Although Bluetooth standard utilizes the same 2.4 GHz range of Wi-Fi • Compared to Wi-Fi, Bluetooth networking is slower, a bit more limited in range, and supports many fewer devices ...
... Overview • Bluetooth is a specification for the use of low power wireless communications over short distance. • Although Bluetooth standard utilizes the same 2.4 GHz range of Wi-Fi • Compared to Wi-Fi, Bluetooth networking is slower, a bit more limited in range, and supports many fewer devices ...
Week#3
... It consists of mobile hosts, fixed hosts, access stations (BS), core network to support mobility and switching. These slides are based on the slides formatted by Dr Sunilkumar S. manvi and Dr Mahabaleshwar S. Kakkasageri, the authors of the textbook: Wireless and Mobile Networks, concepts and protoc ...
... It consists of mobile hosts, fixed hosts, access stations (BS), core network to support mobility and switching. These slides are based on the slides formatted by Dr Sunilkumar S. manvi and Dr Mahabaleshwar S. Kakkasageri, the authors of the textbook: Wireless and Mobile Networks, concepts and protoc ...
ICND -1 Interconnecting Cisco Networking
... fast routing at higher levels to route between those VLANs. Link aggregation to add bandwidth to overloaded links and to provide some measure of redundancy, although the links won't protect against switch failure because they connect the same pair of switches. ...
... fast routing at higher levels to route between those VLANs. Link aggregation to add bandwidth to overloaded links and to provide some measure of redundancy, although the links won't protect against switch failure because they connect the same pair of switches. ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... An extension of wireless LAN operating in ad hoc mode are multi-hop ad hoc networks. They are typically deployed in large areas. A wireless multi-hop ad-hoc network is a network of nodes (e.g. computers, mobile nodes etc.) connected by wireless communication links. The links are usually implemented ...
... An extension of wireless LAN operating in ad hoc mode are multi-hop ad hoc networks. They are typically deployed in large areas. A wireless multi-hop ad-hoc network is a network of nodes (e.g. computers, mobile nodes etc.) connected by wireless communication links. The links are usually implemented ...
TL-WN350G_350GD User Guide - TP-Link
... The TP-LINK TL-WN350G/TL-WN350GD 54M Wireless PCI Adapter will provide you the flexibility to install your PC in the most convenient location available, without the cost of running network cables. The Adapter's auto-sensing capability allows high packet transfer rate of up to 54Mbps for maximum thro ...
... The TP-LINK TL-WN350G/TL-WN350GD 54M Wireless PCI Adapter will provide you the flexibility to install your PC in the most convenient location available, without the cost of running network cables. The Adapter's auto-sensing capability allows high packet transfer rate of up to 54Mbps for maximum thro ...
IOSR Journal of Electronics and Communication Engineering (IOSRJECE)
... WiMAX (Worldwide Interoperability for Microwave Access) was formed in April 2001, in anticipation of the publication of the original 10-66 GHz IEEE 802.16 specifications. WiMAX is a high throughput packet data transfer technology that supports both delay tolerant, burst-based services like web brows ...
... WiMAX (Worldwide Interoperability for Microwave Access) was formed in April 2001, in anticipation of the publication of the original 10-66 GHz IEEE 802.16 specifications. WiMAX is a high throughput packet data transfer technology that supports both delay tolerant, burst-based services like web brows ...
Before You Begin: Assign Information Classification
... groups that extends the Wi-Fi network outdoors Facilitate fast delivery of services; increase productivity and responsiveness of teachers and students by providing greater access to information Increase collaboration among teachers, students, and parents using devices that better prepare students fo ...
... groups that extends the Wi-Fi network outdoors Facilitate fast delivery of services; increase productivity and responsiveness of teachers and students by providing greater access to information Increase collaboration among teachers, students, and parents using devices that better prepare students fo ...
IEEE 802.11 Wireless LAN Security Performance Using Multiple
... Wireless LANs offer several fundamental benefits including user mobility, rapid installation, flexibility and scalability. However, there are some primary limitations [4]: The speed of wireless networks is constrained by the available bandwidth. Information Theory can be used to deduce the upper lim ...
... Wireless LANs offer several fundamental benefits including user mobility, rapid installation, flexibility and scalability. However, there are some primary limitations [4]: The speed of wireless networks is constrained by the available bandwidth. Information Theory can be used to deduce the upper lim ...
TL-WN722N - Newegg.com
... The adapter is designed to provide a high-speed and unrivaled wireless performance for your notebook and PC. With a faster wireless connection, you can get a better Internet experience, such as downloading, gaming, video streaming and so on. The TL-WN722N’s auto-sensing capability allows high packet ...
... The adapter is designed to provide a high-speed and unrivaled wireless performance for your notebook and PC. With a faster wireless connection, you can get a better Internet experience, such as downloading, gaming, video streaming and so on. The TL-WN722N’s auto-sensing capability allows high packet ...
Windows Server 2008
... • 10BaseT, 100BaseT use two pairs of wires • 1000BaseT (Gig Ethernet) uses all four wire pairs • 10GBaseT runs on Category 6A and in full-duplex only • 40 and 100 Gb standard (802.3ba) recently ratified – uses fiber or 7 meter copper cable Copyright © 2012 Cengage Learning. All rights reserved. ...
... • 10BaseT, 100BaseT use two pairs of wires • 1000BaseT (Gig Ethernet) uses all four wire pairs • 10GBaseT runs on Category 6A and in full-duplex only • 40 and 100 Gb standard (802.3ba) recently ratified – uses fiber or 7 meter copper cable Copyright © 2012 Cengage Learning. All rights reserved. ...
Wireless Sensor Networks: Introduction, Advantages
... An advert hoc network is usually a network that is certainly composed of individual devices communicating jointly directly. The idea of implies spontaneous or impromptu construction because networks often bypass the gate keeping hardware or central access point for example a router. Many random netw ...
... An advert hoc network is usually a network that is certainly composed of individual devices communicating jointly directly. The idea of implies spontaneous or impromptu construction because networks often bypass the gate keeping hardware or central access point for example a router. Many random netw ...
Manual D-Link AirPlus Xtreme G DWL-G810
... A WLAN is a computer network that transmits and receives data with radio signals instead of wires. WLANs are used increasingly in both home and office environments, and public areas such as airports, coffee shops and universities. Innovative ways to utilize WLAN technology are helping people to work ...
... A WLAN is a computer network that transmits and receives data with radio signals instead of wires. WLANs are used increasingly in both home and office environments, and public areas such as airports, coffee shops and universities. Innovative ways to utilize WLAN technology are helping people to work ...
SmartConnect WINC1500 Wireless Network Controller
... THIS DOCUMENT, EVEN IF ATMEL HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Atmel makes no representations or warranties with respect to the accuracy or completeness of the contents of this document and reserves the right to make changes to specifications and products descriptions at any time ...
... THIS DOCUMENT, EVEN IF ATMEL HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Atmel makes no representations or warranties with respect to the accuracy or completeness of the contents of this document and reserves the right to make changes to specifications and products descriptions at any time ...
Wi-Fi
Wi-Fi (or WiFi) is a local area wireless computer networking technology that allows electronic devices to network, mainly using the 2.4 gigahertz (12 cm) UHF and 5 gigahertz (6 cm) SHF ISM radio bands.The Wi-Fi Alliance defines Wi-Fi as any ""wireless local area network"" (WLAN) product based on the Institute of Electrical and Electronics Engineers' (IEEE) 802.11 standards. However, the term ""Wi-Fi"" is used in general English as a synonym for ""WLAN"" since most modern WLANs are based on these standards. ""Wi-Fi"" is a trademark of the Wi-Fi Alliance. The ""Wi-Fi Certified"" trademark can only be used by Wi-Fi products that successfully complete Wi-Fi Alliance interoperability certification testing.Many devices can use Wi-Fi, e.g. personal computers, video-game consoles, smartphones, digital cameras, tablet computers and digital audio players. These can connect to a network resource such as the Internet via a wireless network access point. Such an access point (or hotspot) has a range of about 20 meters (66 feet) indoors and a greater range outdoors. Hotspot coverage can be as small as a single room with walls that block radio waves, or as large as many square kilometres achieved by using multiple overlapping access points. Wi-Fi can be less secure than wired connections, such as Ethernet, precisely because an intruder does not need a physical connection. Web pages that use TLS are secure, but unencrypted internet access can easily be detected by intruders. Because of this, Wi-Fi has adopted various encryption technologies. The early encryption WEP proved easy to break. Higher quality protocols (WPA, WPA2) were added later. An optional feature added in 2007, called Wi-Fi Protected Setup (WPS), had a serious flaw that allowed an attacker to recover the router's password. The Wi-Fi Alliance has since updated its test plan and certification program to ensure all newly certified devices resist attacks.