RAFI ULLAH KHAN - Agricultural University Peshawar
... Computer network at Local Area as well as Wide Area Designing, Implementing, Testing, And Monitoring Security Configurations for protecting the network developing Maintenance & Management of multi vendor Routers (Cisco 2600 Series, 3800 Series, Juniper, ZTE DSL Routers). Making static routes Dyn ...
... Computer network at Local Area as well as Wide Area Designing, Implementing, Testing, And Monitoring Security Configurations for protecting the network developing Maintenance & Management of multi vendor Routers (Cisco 2600 Series, 3800 Series, Juniper, ZTE DSL Routers). Making static routes Dyn ...
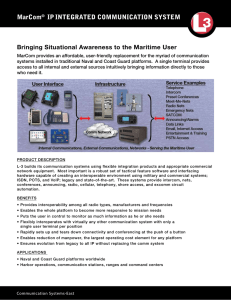
MarCom® IPINTEGRATED COMMUNICATION SYSTEM
... network equipment. Most important is a robust set of tactical feature software and interfacing hardware capable of creating an interoperable environment using military and commercial systems; ISDN, POTS, and VoIP; legacy and state-of-the-art. These systems provide intercom, nets, conferences, announ ...
... network equipment. Most important is a robust set of tactical feature software and interfacing hardware capable of creating an interoperable environment using military and commercial systems; ISDN, POTS, and VoIP; legacy and state-of-the-art. These systems provide intercom, nets, conferences, announ ...
Routing and Switching (CCNA).
... Series - CCNA The Routing and Switching Fundamentals Part 1 and 2 brought to you by Pitman Training is the course for you if you are looking to pass the Cisco CCNA exam and build a career in network management or support in a Cisco environment. This course provides knowledge and skills to make conne ...
... Series - CCNA The Routing and Switching Fundamentals Part 1 and 2 brought to you by Pitman Training is the course for you if you are looking to pass the Cisco CCNA exam and build a career in network management or support in a Cisco environment. This course provides knowledge and skills to make conne ...
Downlaod File - Prince Mohammad Bin Fahd University
... competes with STC the top Internet Service Providers in the region, and enhanced Saudi Arabia, one of the most progressive countries in the field of Internet services. In the recent years, Zain experienced unparalleled development in in its growth in the sum of broadband customers and the volume of ...
... competes with STC the top Internet Service Providers in the region, and enhanced Saudi Arabia, one of the most progressive countries in the field of Internet services. In the recent years, Zain experienced unparalleled development in in its growth in the sum of broadband customers and the volume of ...
T9-routing
... Updates routes only when data is to be transferred Updating routing table gives small overhead to traffic Updating typically done with controlled ’flooding requests’ into the net Possible long delay for packet transmission if entry in routing-table has timed-out ...
... Updates routes only when data is to be transferred Updating routing table gives small overhead to traffic Updating typically done with controlled ’flooding requests’ into the net Possible long delay for packet transmission if entry in routing-table has timed-out ...
Week-2
... services. • Information and applications need to be replicated in each computer on the network. • Administration of application becomes difficult when the size of the network increase. • Integrity of replicated information is questionable. ...
... services. • Information and applications need to be replicated in each computer on the network. • Administration of application becomes difficult when the size of the network increase. • Integrity of replicated information is questionable. ...
3rd Edition: Chapter 4
... We’re making these slides freely available to all (faculty, students, readers). They’re in PowerPoint form so you see the animations; and can add, modify, and delete slides (including this one) and slide content to suit your needs. They obviously represent a lot of work on our part. In return for us ...
... We’re making these slides freely available to all (faculty, students, readers). They’re in PowerPoint form so you see the animations; and can add, modify, and delete slides (including this one) and slide content to suit your needs. They obviously represent a lot of work on our part. In return for us ...
Stand Alone Computers Computer Network Local Area Network
... Each node on the network needs a NIC to connect to a LAN. The NIC allows computers to communicate over a computer network by providing physical access to the network and a unique address for each individual node (Media Access Control - MAC address). Hub A Hub is a device that connects nodes together ...
... Each node on the network needs a NIC to connect to a LAN. The NIC allows computers to communicate over a computer network by providing physical access to the network and a unique address for each individual node (Media Access Control - MAC address). Hub A Hub is a device that connects nodes together ...
Class 24 - Nov. 20
... – intermediate system to connect two LANs that use similar LAN protocols – acts as address filter to transfer packets – operates at layer 2 - network access layer ...
... – intermediate system to connect two LANs that use similar LAN protocols – acts as address filter to transfer packets – operates at layer 2 - network access layer ...
Hypothesis Testing for Network Security
... solving, to check hypotheses against data plane – Translate SAT results to report hypothesis veracity along with diagnostic information ...
... solving, to check hypotheses against data plane – Translate SAT results to report hypothesis veracity along with diagnostic information ...
Mobile Wireless Ad Hoc Network (MANET)
... ascertained that node uses battery power to operate. So it is necessary to optimize the design of energy. Limitations Security: Wireless networks tend to be more vulnerable to security than wired networks. ...
... ascertained that node uses battery power to operate. So it is necessary to optimize the design of energy. Limitations Security: Wireless networks tend to be more vulnerable to security than wired networks. ...
Equipment: IP Networking Tech Gear
... • Private is indirectly connected to the internet if connected at all. – LAN or Local Area Network. Your home or office network • These are not to be confused for the Public and Private Wireless Networks, which are both Private Connections. ...
... • Private is indirectly connected to the internet if connected at all. – LAN or Local Area Network. Your home or office network • These are not to be confused for the Public and Private Wireless Networks, which are both Private Connections. ...
Document
... computer data into analog audio signals for transfer over a telephone line, and then a modem at the destination converts it back into data. ...
... computer data into analog audio signals for transfer over a telephone line, and then a modem at the destination converts it back into data. ...
networking-1234619450976217-2
... utilizing the Internet Protocol for communication between its nodes. Although IP addresses are stored as binary numbers, they are often displayed in more human-readable notations, such as 192.168.100.1 (for IPv4), and 2001:db8:0:1234:0:567:1:1 (for IPv6). IP address was defined as a 32-bit number an ...
... utilizing the Internet Protocol for communication between its nodes. Although IP addresses are stored as binary numbers, they are often displayed in more human-readable notations, such as 192.168.100.1 (for IPv4), and 2001:db8:0:1234:0:567:1:1 (for IPv6). IP address was defined as a 32-bit number an ...
Network Architecture
... Send broadcast messages; do not work well with large networks Effective at separating high-volume areas on a LAN Work best when used to connect LANs that usually do not communicate outside their immediate network ...
... Send broadcast messages; do not work well with large networks Effective at separating high-volume areas on a LAN Work best when used to connect LANs that usually do not communicate outside their immediate network ...
No Slide Title
... IP provides delivery services taking care of addressing ensuring the routers know what to do with your data when it arrives. Every computer on the Internet has a unique address. Information sent across IP networks is broken up into bite-sized pieces, called packets. The information within a pa ...
... IP provides delivery services taking care of addressing ensuring the routers know what to do with your data when it arrives. Every computer on the Internet has a unique address. Information sent across IP networks is broken up into bite-sized pieces, called packets. The information within a pa ...
Network_Hist
... It was the world's first packet switching network, which first went online in 1969. ...
... It was the world's first packet switching network, which first went online in 1969. ...
Chapter 7: Networking
... • Using wireless media is critical when portable computing devices need to be connected to a network. • Data transfer rate (also known as bandwidth) is the maximum speed at which data can be transmitted between two nodes on a network. • Throughput is the actual speed of data transfer that is ...
... • Using wireless media is critical when portable computing devices need to be connected to a network. • Data transfer rate (also known as bandwidth) is the maximum speed at which data can be transmitted between two nodes on a network. • Throughput is the actual speed of data transfer that is ...
Understanding Networking
... • WANs require the crossing of public right of ways (under control and regulations of the interstate commerce and institute of telephone and data communications established by the gov’t and international treaties). • WANs around the world relies on the infrastructure established by the telephone com ...
... • WANs require the crossing of public right of ways (under control and regulations of the interstate commerce and institute of telephone and data communications established by the gov’t and international treaties). • WANs around the world relies on the infrastructure established by the telephone com ...
Aswin Chidambaram
... various kinds of sophisticated cyber-attacks which can have a serious impact on the Critical Infrastructure such as the power grid. Most of the time, the success of the attack is based on the static characteristics of the system, thereby enabling an easier profiling of the target system(s) by the ad ...
... various kinds of sophisticated cyber-attacks which can have a serious impact on the Critical Infrastructure such as the power grid. Most of the time, the success of the attack is based on the static characteristics of the system, thereby enabling an easier profiling of the target system(s) by the ad ...
Networking - Computer Science at RPI
... Data Link Layer - address must be able to select any host on the network. Network Layer - address must be able to provide information to enable routing. Transport Layer - address must identify the ...
... Data Link Layer - address must be able to select any host on the network. Network Layer - address must be able to provide information to enable routing. Transport Layer - address must identify the ...