MPLS Based Web Switching
... Emergence of high-speed 802.11a WLANs (108Mbps) WLANs can operate a varying rates (1,2,..,11, ..,22, ..,54, 108) Reception range decreases with rate Given the above, we can think of a cellular-like architecture for multi-hop wireless networks Start with a large cell; as nodes increase split into ( ...
... Emergence of high-speed 802.11a WLANs (108Mbps) WLANs can operate a varying rates (1,2,..,11, ..,22, ..,54, 108) Reception range decreases with rate Given the above, we can think of a cellular-like architecture for multi-hop wireless networks Start with a large cell; as nodes increase split into ( ...
wp2 transmission technology study - CzechLight
... Procure „ISP-like“ equipment Procure network operation and maintenance The first goal is service for researchers (research in networking is secondary) Main Advantages: Relatively simple design and operation (we use large and matured building elements and services, with guarantee) Transparency for do ...
... Procure „ISP-like“ equipment Procure network operation and maintenance The first goal is service for researchers (research in networking is secondary) Main Advantages: Relatively simple design and operation (we use large and matured building elements and services, with guarantee) Transparency for do ...
Basics of Voice and Video over IP performance
... Basics of Voice and Video over IP performance measurement Voice and Video Traffic are inherently different from Data Traffic They use Signaling protocols such as H.323, SIP, … Media (Voice and Video payload) is delivered over IP using RTP packets irrespective of which codec or end-point technology ...
... Basics of Voice and Video over IP performance measurement Voice and Video Traffic are inherently different from Data Traffic They use Signaling protocols such as H.323, SIP, … Media (Voice and Video payload) is delivered over IP using RTP packets irrespective of which codec or end-point technology ...
Part I: Introduction
... 1. Require all telnet users to telnet through gateway. 2. For authorized users, gateway sets up telnet connection to dest host. Gateway relays data between 2 connections 3. Router filter blocks all telnet connections not originating from gateway. 8: Network Management ...
... 1. Require all telnet users to telnet through gateway. 2. For authorized users, gateway sets up telnet connection to dest host. Gateway relays data between 2 connections 3. Router filter blocks all telnet connections not originating from gateway. 8: Network Management ...
Problem 3
... General purpose NMS, such as HP OpenView, can monitor several vendors' components and do an overall fault monitoring. In addition, intelligence is built into the system to localize the fault. ...
... General purpose NMS, such as HP OpenView, can monitor several vendors' components and do an overall fault monitoring. In addition, intelligence is built into the system to localize the fault. ...
Brocade Mainframe BC/DR Solution solution brief
... © 2015 Brocade Communications Systems, Inc. All Rights Reserved. 04/15 GA-SB-1943-00 ADX, Brocade, Brocade Assurance, the B-wing symbol, DCX, Fabric OS, HyperEdge, ICX, MLX, MyBrocade, OpenScript, The Effortless Network, VCS, VDX, Vplane, and Vyatta are registered trademarks, and Fabric Vision and v ...
... © 2015 Brocade Communications Systems, Inc. All Rights Reserved. 04/15 GA-SB-1943-00 ADX, Brocade, Brocade Assurance, the B-wing symbol, DCX, Fabric OS, HyperEdge, ICX, MLX, MyBrocade, OpenScript, The Effortless Network, VCS, VDX, Vplane, and Vyatta are registered trademarks, and Fabric Vision and v ...
Chapter 02 - Communicating Over The Network
... protocol with low overhead. It provides only the functions that are necessary to deliver a packet from a source to a destination over an interconnected system of networks. The protocol was not designed to track and manage the flow of packets. ...
... protocol with low overhead. It provides only the functions that are necessary to deliver a packet from a source to a destination over an interconnected system of networks. The protocol was not designed to track and manage the flow of packets. ...
Lecture Notes - Computer Science & Engineering
... IP address is a globally unique or private number associated with a host network interface Every system which will send packets directly out across the Internet must have a unique IP address IP addresses are based on where the hosts are connected IP addresses are controlled by a single organ ...
... IP address is a globally unique or private number associated with a host network interface Every system which will send packets directly out across the Internet must have a unique IP address IP addresses are based on where the hosts are connected IP addresses are controlled by a single organ ...
Network Design Proposal
... Network security plan ensures that data access is limited to authorized users. The sophistication of cyber attackers and hackers can only be challenged by a similar level of sophistication in network security. Network security system with monitoring capabilities gives IT organizations a powerful wea ...
... Network security plan ensures that data access is limited to authorized users. The sophistication of cyber attackers and hackers can only be challenged by a similar level of sophistication in network security. Network security system with monitoring capabilities gives IT organizations a powerful wea ...
Database Client/Server Apps - NYU Stern School of Business
... How are errors handled How much information in a message How is message routed from sender to receiver ...
... How are errors handled How much information in a message How is message routed from sender to receiver ...
slides - network systems lab @ sfu
... – Produce redundant traffic on physical link: multiple overlay edges use the same physical link – Increase latency: communication involves other end systems ...
... – Produce redundant traffic on physical link: multiple overlay edges use the same physical link – Increase latency: communication involves other end systems ...
Network
... clients and enable computers to share processing power Network Operating System (NOS) Is software that controls the network enabling computers to communicate by enabling network services Information Systems Today ...
... clients and enable computers to share processing power Network Operating System (NOS) Is software that controls the network enabling computers to communicate by enabling network services Information Systems Today ...
Envirostore: A Cooperative Storage System for Disconnected
... Scenarios 1: Single Disconnected sensor network Scenario 2 :Partitioned sensor network with data mules ...
... Scenarios 1: Single Disconnected sensor network Scenario 2 :Partitioned sensor network with data mules ...
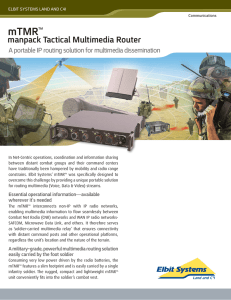
mTMRTM - Elbit Systems
... terminals at the command center. mTMR incorporates a VoIP gateway with standard SIP (RFC 3261) protocol for interoperability with common VoIP terminals and SIP phones. mTMRTM enables voice tunneling between tactical radios, LAN/WAN interfaces and a local hand-set. mTMR’s DSP provides voice activity ...
... terminals at the command center. mTMR incorporates a VoIP gateway with standard SIP (RFC 3261) protocol for interoperability with common VoIP terminals and SIP phones. mTMRTM enables voice tunneling between tactical radios, LAN/WAN interfaces and a local hand-set. mTMR’s DSP provides voice activity ...
A Probabilistic Misbehavior Detection Scheme towards
... Malicious and selfish behaviors represent a serious threat against routing in Delay/Disruption Tolerant Networks (DTNs). Due to the unique network characteristics, designing a misbehavior detection scheme in DTN is regarded as a great challenge. In this paper, we propose iTrust, a probabilistic misb ...
... Malicious and selfish behaviors represent a serious threat against routing in Delay/Disruption Tolerant Networks (DTNs). Due to the unique network characteristics, designing a misbehavior detection scheme in DTN is regarded as a great challenge. In this paper, we propose iTrust, a probabilistic misb ...
Devices & Internet - The Computer Engineers` Blog
... Types of Networking Domains What Are the Features of Switches? ...
... Types of Networking Domains What Are the Features of Switches? ...
Collaboration Bus - UNC Computer Science
... Automatic applianceremote control binding A single remote control for ...
... Automatic applianceremote control binding A single remote control for ...
NetworkConcepts
... The given network scenario describes the computer network of a small trading company. It has a sales department and an inventory section. The company is managed by a manager who has a personal assistant. All the parties mentioned above need to use computers to support their duties in the company. Co ...
... The given network scenario describes the computer network of a small trading company. It has a sales department and an inventory section. The company is managed by a manager who has a personal assistant. All the parties mentioned above need to use computers to support their duties in the company. Co ...
A+ Guide to Managing and Maintaining Your PC, 7e
... • If link breaks, nodes can still communicate ...
... • If link breaks, nodes can still communicate ...
Lecture 1 Introduction
... Networks Switched Communication Network Circuit-Switched Communication Network ...
... Networks Switched Communication Network Circuit-Switched Communication Network ...