Windows Server 2012 R2: Networking
... • VM traffic bypasses virtual switch and performs I/O directly to NIC • Ideal for high I/O workloads that do not require port policies, QoS, or network virtualization enforced at the end host virtual switch ...
... • VM traffic bypasses virtual switch and performs I/O directly to NIC • Ideal for high I/O workloads that do not require port policies, QoS, or network virtualization enforced at the end host virtual switch ...
Information Representation: Summary
... A UPS can cost from as little as €200 to €x,000 depending on amount of time it can keep system running ...
... A UPS can cost from as little as €200 to €x,000 depending on amount of time it can keep system running ...
Introduction to Mobile Computing CNT 5517-5564
... Limitations of the Mobile Computer Short battery lifetime (max ~ 5 hours) Subject to theft and destruction => unreliable Highly unavailable (normally powered-off to conserve battery) Limited capability (display, memory, input devices, and disk space) Lack of de-facto general architecture: ...
... Limitations of the Mobile Computer Short battery lifetime (max ~ 5 hours) Subject to theft and destruction => unreliable Highly unavailable (normally powered-off to conserve battery) Limited capability (display, memory, input devices, and disk space) Lack of de-facto general architecture: ...
Testing Bandwidth around the world
... NETFLOW and open source Flowtools to characterize the network traffic goes through our border ...
... NETFLOW and open source Flowtools to characterize the network traffic goes through our border ...
tia5e_ch12_ppt
... Network Topologies • The physical layout of computers, transmission media, and other components • Types of network topologies – Bus topology – Ring topology – Star topology – Hybrid topology © 2009 Prentice-Hall, Inc. ...
... Network Topologies • The physical layout of computers, transmission media, and other components • Types of network topologies – Bus topology – Ring topology – Star topology – Hybrid topology © 2009 Prentice-Hall, Inc. ...
Chapter 1
... • Have defined information that they act upon and a defined interface to the layers above and below. • Fosters competition because products from different vendors can work together. • Prevents technology or capability changes in one layer from affecting other layers above and below. • Provides a com ...
... • Have defined information that they act upon and a defined interface to the layers above and below. • Fosters competition because products from different vendors can work together. • Prevents technology or capability changes in one layer from affecting other layers above and below. • Provides a com ...
Dynamic Bayesian networks
... Network dynamics and context specificity • What does modeling “dynamics” mean? – The activity of nodes change over time and we want to model how this happens – The network (structure or parameters) changes with time • Structure can change due to changes at the node or ...
... Network dynamics and context specificity • What does modeling “dynamics” mean? – The activity of nodes change over time and we want to model how this happens – The network (structure or parameters) changes with time • Structure can change due to changes at the node or ...
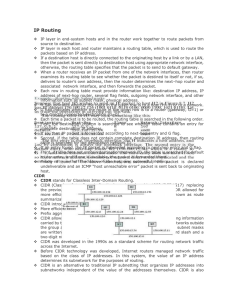
Chapter 17 - Networking Essentials
... Protocols at the Internetwork Layer • Address Resolution Protocol (cont.) – To avoid sending an ARP request every time an IP packet is sent, PCs and other devices store learned IP address/MAC address pairs in an ARP cache, which is a temporary location in RAM – If the destination computer is on ano ...
... Protocols at the Internetwork Layer • Address Resolution Protocol (cont.) – To avoid sending an ARP request every time an IP packet is sent, PCs and other devices store learned IP address/MAC address pairs in an ARP cache, which is a temporary location in RAM – If the destination computer is on ano ...
[slides] Sensor network applications
... Lack of quantitative analysis of passive participation for security reasons ...
... Lack of quantitative analysis of passive participation for security reasons ...
Speed Up Incident Response with Actionable Forensic Analytics
... Forensic Analytics and Incident Response corresponds to the Analyze and Respond phases (bottom-half) of the IT/Security process. Common Challenges Common challenges encountered by organizations implementing this model include: • Organizational Silos: Desktop administration, network, and security op ...
... Forensic Analytics and Incident Response corresponds to the Analyze and Respond phases (bottom-half) of the IT/Security process. Common Challenges Common challenges encountered by organizations implementing this model include: • Organizational Silos: Desktop administration, network, and security op ...
On the Convexity of Latent Social Network Inference
... the network structure learning for estimating the dependency structure of directed graphical models [7] and probabilistic relational models [7]. However, these formulations are often intractable and one has to reside to heuristic solutions. Recently, graphical Lasso methods [25, 21, 6, 19] for stati ...
... the network structure learning for estimating the dependency structure of directed graphical models [7] and probabilistic relational models [7]. However, these formulations are often intractable and one has to reside to heuristic solutions. Recently, graphical Lasso methods [25, 21, 6, 19] for stati ...
1_hProtocolsOSI
... • it defines the actual media and characteristics used to send the 1’s and 0’s over the network. • This includes the actual wiring itself, the connectors used, voltage levels, maximum media distances and so forth. • For example, a packet might start on twisted-pair wiring, move onto a wireless netwo ...
... • it defines the actual media and characteristics used to send the 1’s and 0’s over the network. • This includes the actual wiring itself, the connectors used, voltage levels, maximum media distances and so forth. • For example, a packet might start on twisted-pair wiring, move onto a wireless netwo ...
slides - TNC15
... • The Nature of their early technology led the Phone Companies to Adopt what could be called, a “Beads-on-a-String” architecture. ...
... • The Nature of their early technology led the Phone Companies to Adopt what could be called, a “Beads-on-a-String” architecture. ...
Where Have We Been? - Oakton Community College
... traffic overhead would be like on a network with 254 hosts trying to discover each others MAC addresses? • Subnetting allows us to segment LANs into logical broadcast domains called subnets, thereby improving network performance. ...
... traffic overhead would be like on a network with 254 hosts trying to discover each others MAC addresses? • Subnetting allows us to segment LANs into logical broadcast domains called subnets, thereby improving network performance. ...
Social-Aware Data Dissemination in Opportunistic - UTK-EECS
... Theoretical Analysis Performance Evaluation Summary & Future Work ...
... Theoretical Analysis Performance Evaluation Summary & Future Work ...
The Infrastructure Technologies
... • Messages have header and trailer carry information for delivering and ensuring the integrity of the message • These are used by application and communication protocols • The electronic form of a message is a signal ...
... • Messages have header and trailer carry information for delivering and ensuring the integrity of the message • These are used by application and communication protocols • The electronic form of a message is a signal ...
subscription services brief
... Ethernet, delivering voice, data, and video across any grade of wiring. ...
... Ethernet, delivering voice, data, and video across any grade of wiring. ...
BOOTP Packet Format - Texas Tech University
... Security Protocols, authentication services, encryption services ...
... Security Protocols, authentication services, encryption services ...
Network Fundamentals
... A command line utility usable on either Unix or MS-DOS/Windows which generates and verifies message digests using the MD5 algorithm Security has been compromised as an encryption protocol, however, used mostly to provide some assurance that a transferred file has arrived intact and uncorrupted How t ...
... A command line utility usable on either Unix or MS-DOS/Windows which generates and verifies message digests using the MD5 algorithm Security has been compromised as an encryption protocol, however, used mostly to provide some assurance that a transferred file has arrived intact and uncorrupted How t ...
CAP - MUM - Mikrotik
... centralisation of wireless network management (SSID, Access List, Security,……) and/or data processing (Firewall, QoS, Routing,…) ...
... centralisation of wireless network management (SSID, Access List, Security,……) and/or data processing (Firewall, QoS, Routing,…) ...
20070716-wenji-demar-bowden
... Modify the AMID congestion avoidance scheme of standard TCP to be more aggressive, Keep the same fast retransmit and fast recovery algorithm Solve the under-utilized problem in high speed and long distance networks ...
... Modify the AMID congestion avoidance scheme of standard TCP to be more aggressive, Keep the same fast retransmit and fast recovery algorithm Solve the under-utilized problem in high speed and long distance networks ...
TNC-2001
... • Basic Design Principles for GRNET2 • Implementation Considerations of the 2-layer Architecture for GRNET2 ...
... • Basic Design Principles for GRNET2 • Implementation Considerations of the 2-layer Architecture for GRNET2 ...
Presentation3
... AAL1, a connection-oriented service, is suitable for handling constant bit rate sources (CBR), such as uncompressed audio and videoconferencing ...
... AAL1, a connection-oriented service, is suitable for handling constant bit rate sources (CBR), such as uncompressed audio and videoconferencing ...








![[slides] Sensor network applications](http://s1.studyres.com/store/data/012511086_1-424a16e4574a3171e83c172220490b5b-300x300.png)