Juniper / Cisco Interoperability Cookbook
... Juniper Networks/Cisco Systems Switch Interoperability Cookbook interoperability section uses a Juniper MX80 router as well as the other devices previously mentioned. The Wi-Fi interoperability section also uses a Cisco 5508 controller and Cisco 3602 and Cisco 3702 access points. Appendix B lists s ...
... Juniper Networks/Cisco Systems Switch Interoperability Cookbook interoperability section uses a Juniper MX80 router as well as the other devices previously mentioned. The Wi-Fi interoperability section also uses a Cisco 5508 controller and Cisco 3602 and Cisco 3702 access points. Appendix B lists s ...
PDF - Complete Book (655.0 KB)
... Configuration Guides, Command References, and Supplementary Resources Table 1 lists, in alphabetical order, Cisco IOS and Cisco IOS XE software configuration guides and command references, including brief descriptions of the contents of the documents. The Cisco IOS command references are comprehensi ...
... Configuration Guides, Command References, and Supplementary Resources Table 1 lists, in alphabetical order, Cisco IOS and Cisco IOS XE software configuration guides and command references, including brief descriptions of the contents of the documents. The Cisco IOS command references are comprehensi ...
nvOS Introduction 5 Introduction to nvOS Fabric
... Pluribus Netvisor uses the concept of Fabric-Cluster to describe the interconnectivity of devices into a single logical network. The concept of a virtual network (VNET) describes is a “slice” of resources that apply to a single entity with assigned resources within the fabric. The VNET contains serv ...
... Pluribus Netvisor uses the concept of Fabric-Cluster to describe the interconnectivity of devices into a single logical network. The concept of a virtual network (VNET) describes is a “slice” of resources that apply to a single entity with assigned resources within the fabric. The VNET contains serv ...
Cisco IP SLA`s
... • Service Provider needs visibility in the Customer Edge, in order to commit to SLAs • Enterprise will verify SP SLAs by using access router edge to edge measurements Enterprise may provide restricted Simple Network Management Protocol (SNMP) (RTT, Latency, QoS) visibility into Access router for Ser ...
... • Service Provider needs visibility in the Customer Edge, in order to commit to SLAs • Enterprise will verify SP SLAs by using access router edge to edge measurements Enterprise may provide restricted Simple Network Management Protocol (SNMP) (RTT, Latency, QoS) visibility into Access router for Ser ...
Command Line Interface Guide
... This guide is intended to help you configure and manage the router using the Command Line Interface. The guide assumes that you have read the information about the router and installed the hardware using the Internet Quick Start Guide. The guide is divided into eight parts: Introduction. Describes t ...
... This guide is intended to help you configure and manage the router using the Command Line Interface. The guide assumes that you have read the information about the router and installed the hardware using the Internet Quick Start Guide. The guide is divided into eight parts: Introduction. Describes t ...
Netvisor nvOS Configuration Guide
... Any Internet Protocol (IP) addresses used in this document are not intended to be actual addresses. Any examples, command display output, and figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses in illustrative content is unintentional and coincid ...
... Any Internet Protocol (IP) addresses used in this document are not intended to be actual addresses. Any examples, command display output, and figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses in illustrative content is unintentional and coincid ...
BIG-IP DNS - F5 Networks
... BIG‑IP DNS provides tools that give you a global view of your infrastructure with the means to manage the network and add polices to ensure the highest availability for your businesscritical applications. Features include: • Web-based user interface—Manage global infrastructure from a centralized U ...
... BIG‑IP DNS provides tools that give you a global view of your infrastructure with the means to manage the network and add polices to ensure the highest availability for your businesscritical applications. Features include: • Web-based user interface—Manage global infrastructure from a centralized U ...
BIG-IP DNS
... • Packet filtering—BIG-IP DNS uses packet filtering to limit or deny websites’ access based on source, destination, or port. DNS firewall DNS DDoS, cache poisoning of LDNS, and other unwanted DNS attacks and volume spikes can cause DNS outage and lost productivity. These attacks and traffic spikes ...
... • Packet filtering—BIG-IP DNS uses packet filtering to limit or deny websites’ access based on source, destination, or port. DNS firewall DNS DDoS, cache poisoning of LDNS, and other unwanted DNS attacks and volume spikes can cause DNS outage and lost productivity. These attacks and traffic spikes ...
ESBC Administrator`s Guide
... Understand the network factors which affect quality of service .......................................... 38 ...
... Understand the network factors which affect quality of service .......................................... 38 ...
Garis Panduan Transisi Protokol Internet Versi 6 (IPV6) Sektor Awam
... NDP menggantikan Address Resolution Protocol (ARP), ICMP untuk IPv4 (ICMPv4) Router Discovery dan ICMPv4 Redirect massages. ...
... NDP menggantikan Address Resolution Protocol (ARP), ICMP untuk IPv4 (ICMPv4) Router Discovery dan ICMPv4 Redirect massages. ...
TAC Vista Product Catalog
... Our open, standard technology enables you to integrate heating and cooling, access control, security monitoring, ventilation, fire and smoke control and lighting, across your enterprise. This approach reduces training and maintenance costs, increases energy savings, and adds value by collecting and ...
... Our open, standard technology enables you to integrate heating and cooling, access control, security monitoring, ventilation, fire and smoke control and lighting, across your enterprise. This approach reduces training and maintenance costs, increases energy savings, and adds value by collecting and ...
DataSuite User Guide Supporting Fourtec Data Loggers
... DataSuite includes an additional CFR module which together with the separate DatPass Administrative software achieves compliance with FDA Title 21 CFR Part 11. Among other features, it defines the users that can log into the DataSuite software, their passwords and the digital signatures the users ar ...
... DataSuite includes an additional CFR module which together with the separate DatPass Administrative software achieves compliance with FDA Title 21 CFR Part 11. Among other features, it defines the users that can log into the DataSuite software, their passwords and the digital signatures the users ar ...
IPv6 Migration Plan for BSNL NIB Network
... 1. Introduction The current BSNL NIB Network is not enabled for providing IPv6 services to BSNL customers. Currently customers use Natted Private IPv4 IPs to access Internet services. With the advent of new applications like Voice & Video conferencing, public IPs are required by every user, so that ...
... 1. Introduction The current BSNL NIB Network is not enabled for providing IPv6 services to BSNL customers. Currently customers use Natted Private IPv4 IPs to access Internet services. With the advent of new applications like Voice & Video conferencing, public IPs are required by every user, so that ...
Cisco CCNA Study Guide
... • The Open Systems Interconnection (OSI) model • The Department of Defense (DoD) model Without the framework that network models provide, all network hardware and software would have been proprietary. Organizations would have been locked into a single vendor’s equipment, and global networks like the ...
... • The Open Systems Interconnection (OSI) model • The Department of Defense (DoD) model Without the framework that network models provide, all network hardware and software would have been proprietary. Organizations would have been locked into a single vendor’s equipment, and global networks like the ...
Multicast Rutorial r3
... that want to receive it. Multicast can be implemented at the Ethernet linklayer or at the network layer (layer 3 of the OSI model). Computers join and leave multicast groups by using the IGMP (Internet Group Management Protocol) Each host can register itself as a member of selected multicast groups ...
... that want to receive it. Multicast can be implemented at the Ethernet linklayer or at the network layer (layer 3 of the OSI model). Computers join and leave multicast groups by using the IGMP (Internet Group Management Protocol) Each host can register itself as a member of selected multicast groups ...
Ip Addressing and Subnetting Workbook
... ANDING with the default subnet mask allows your computer to figure out the network portion of the address. ...
... ANDING with the default subnet mask allows your computer to figure out the network portion of the address. ...
Ip Addressing and Subnetting Workbook
... Custom subnet masks When you take a single network such as 192.100.10.0 and divide it into five smaller networks (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five small ...
... Custom subnet masks When you take a single network such as 192.100.10.0 and divide it into five smaller networks (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five small ...
Ip Addressing and Subnetting Workbook
... Custom subnet masks When you take a single network such as 192.100.10.0 and divide it into five smaller networks (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five small ...
... Custom subnet masks When you take a single network such as 192.100.10.0 and divide it into five smaller networks (192.100.10.16, 192.100.10.32, 192.100.10.48, 192.100.10.64, 192.100.10.80) the outside world still sees the network as 192.100.10.0, but the internal computers and routers see five small ...
MPLS and VPN Architectures
... Shortest Path First (OSPF), and Border Gateway Protocol (BGP). Chapter 12, "Advanced MPLS VPN Topologies"— This chapter describes advanced topologies that can be implemented within the MPLS VPN architecture, ranging from overlapping VPN topology through central services topology to emulation of hub- ...
... Shortest Path First (OSPF), and Border Gateway Protocol (BGP). Chapter 12, "Advanced MPLS VPN Topologies"— This chapter describes advanced topologies that can be implemented within the MPLS VPN architecture, ranging from overlapping VPN topology through central services topology to emulation of hub- ...
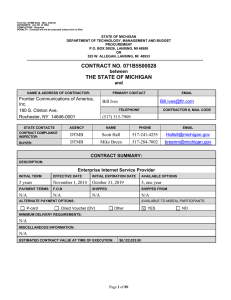
... Contract Administrator and DTMB must approve any tools, in writing, before use on any information technology project for New Work. It is recognized that technology changes rapidly. Either party may, subject to Contract Change Management request, in writing, a change in the standard environment Equip ...
Network Routing Service Fundamentals
... Copyright © 2010 Nortel Networks. All Rights Reserved. While the information in this document is believed to be accurate and reliable, except as otherwise expressly agreed to in writing NORTEL PROVIDES THIS DOCUMENT "AS IS" WITHOUT WARRANTY OR CONDITION OF ANY KIND, EITHER EXPRESS OR IMPLIED. The in ...
... Copyright © 2010 Nortel Networks. All Rights Reserved. While the information in this document is believed to be accurate and reliable, except as otherwise expressly agreed to in writing NORTEL PROVIDES THIS DOCUMENT "AS IS" WITHOUT WARRANTY OR CONDITION OF ANY KIND, EITHER EXPRESS OR IMPLIED. The in ...
PDF
... 4G GPS and NMEA Effective with Cisco IOS Release 15.3(3)M and later releases, the Global Positioning System (GPS) feature is enabled by default on the supported 4G LTE ISRs and Cisco 4G LTE NIMs to provide the geographical location. Both GPS and NMEA features must be configured for GPS coordinates t ...
... 4G GPS and NMEA Effective with Cisco IOS Release 15.3(3)M and later releases, the Global Positioning System (GPS) feature is enabled by default on the supported 4G LTE ISRs and Cisco 4G LTE NIMs to provide the geographical location. Both GPS and NMEA features must be configured for GPS coordinates t ...