Phillipe Lemonnier`s presentation
... Technologies used for IP transport (OSI level 2) don’t lose bits : they ...
... Technologies used for IP transport (OSI level 2) don’t lose bits : they ...
Multicast_I
... •A unicast address identifies a single IP interface •A broadcast address identifies all IP interfaces on the subnet •A multicast address identifies a set of IP interfaces •A multicast datagram is received only by those interfaces interested in the datagram (applications wishing to participate in the ...
... •A unicast address identifies a single IP interface •A broadcast address identifies all IP interfaces on the subnet •A multicast address identifies a set of IP interfaces •A multicast datagram is received only by those interfaces interested in the datagram (applications wishing to participate in the ...
CN 2015 1-2 - DSpace
... connection to a called party before any communication is possible. It maintain the connection to transfer message The circuit is terminated when the connection is closed. ...
... connection to a called party before any communication is possible. It maintain the connection to transfer message The circuit is terminated when the connection is closed. ...
The Gartner Glossary of Information Technology Acronyms and Terms
... channel, but maximum user throughput will be about half this and the throughput is shared by all users of the same radio channel. Data rates fall off as the distance between the user and the radio access point increases. Frequency bands allowed for 802.11a (also called Wi-Fi5) differ in different pa ...
... channel, but maximum user throughput will be about half this and the throughput is shared by all users of the same radio channel. Data rates fall off as the distance between the user and the radio access point increases. Frequency bands allowed for 802.11a (also called Wi-Fi5) differ in different pa ...
Activating an EVDO Wireless Card in a Cellular
... • Activating a Sierra Wireless EVDO Card in the Verizon Wireless Network, on page 7 • Activating a Sierra Wireless EVDO Card in the Sprint Network, on page 10 • Activating a Novatel Wireless EVDO Card in the Verizon Wireless Network, on page 14 • Activating a Novatel Wireless EVDO Card in the Sprint ...
... • Activating a Sierra Wireless EVDO Card in the Verizon Wireless Network, on page 7 • Activating a Sierra Wireless EVDO Card in the Sprint Network, on page 10 • Activating a Novatel Wireless EVDO Card in the Verizon Wireless Network, on page 14 • Activating a Novatel Wireless EVDO Card in the Sprint ...
HiveR: 2D and 3D Hive Plots of Networks 0.2
... Observations at several different habitats/sites Two sites have been converted to HPD format: ...
... Observations at several different habitats/sites Two sites have been converted to HPD format: ...
(IP) routers
... sustainable network by functioning as a shared backup router. • Current commercial routers was not virtualized but implemented as a proprietary hardware and software. ...
... sustainable network by functioning as a shared backup router. • Current commercial routers was not virtualized but implemented as a proprietary hardware and software. ...
Intelligent Environments
... # The resolution of the Transducer. For instance, 10^-3 means # that the Transducer has resolution to 0.001 unit. sample-rate= integer L # The speed at which samples are obtained per second. For # instance 1000 means that one sample is obtained every millisecond. ...
... # The resolution of the Transducer. For instance, 10^-3 means # that the Transducer has resolution to 0.001 unit. sample-rate= integer L # The speed at which samples are obtained per second. For # instance 1000 means that one sample is obtained every millisecond. ...
Computer Networking : Principles, Protocols and Practice
... [Comer1988], a difficult choice at that time. He later extended his textbook by describing a complete TCP/IP implementation, adding practical considerations to the theoretical descriptions in [Comer1988]. Richard Stevens approached the Internet like an explorer and explained the operation of protoco ...
... [Comer1988], a difficult choice at that time. He later extended his textbook by describing a complete TCP/IP implementation, adding practical considerations to the theoretical descriptions in [Comer1988]. Richard Stevens approached the Internet like an explorer and explained the operation of protoco ...
A Survey of BGP Security Issues and Solutions
... provider closer to the Internet backbone) that bears sole responsibility for providing connectivity to the rest of the Internet. The customer AS may be assigned a private AS number in the range 64512–65535 for communicating via BGP with its provider. The provider’s routers would then advertise the B ...
... provider closer to the Internet backbone) that bears sole responsibility for providing connectivity to the rest of the Internet. The customer AS may be assigned a private AS number in the range 64512–65535 for communicating via BGP with its provider. The provider’s routers would then advertise the B ...
DSL-300T Manual-100 - D-Link
... in question has not been returned to a D-Link office, then a proof of purchase (such as a copy of the dated purchase invoice) must be provided when requesting warranty service. The term "purchase" in this software warranty refers to the purchase transaction and resulting license to use such software ...
... in question has not been returned to a D-Link office, then a proof of purchase (such as a copy of the dated purchase invoice) must be provided when requesting warranty service. The term "purchase" in this software warranty refers to the purchase transaction and resulting license to use such software ...
Acceptable use Policy
... access any other person's computer or computer system, network, software, or data without his or her knowledge and consent; breach the security of another user or system; or attempt to circumvent the user authentication or security of any host, network, or account. This includes, but is not limited ...
... access any other person's computer or computer system, network, software, or data without his or her knowledge and consent; breach the security of another user or system; or attempt to circumvent the user authentication or security of any host, network, or account. This includes, but is not limited ...
Cisco Small Business WAP4410N Wireless-N Access Point with Power Over Ethernet ADMINISTRATION
... The Cisco WAP4410N access point allows for greater range and mobility within your wireless network while also allowing you to connect the wireless network to a wired environment. It also supports the Wi-Fi Protected Setup (WPS) feature to help you simplify the setting up of security on a wireless ne ...
... The Cisco WAP4410N access point allows for greater range and mobility within your wireless network while also allowing you to connect the wireless network to a wired environment. It also supports the Wi-Fi Protected Setup (WPS) feature to help you simplify the setting up of security on a wireless ne ...
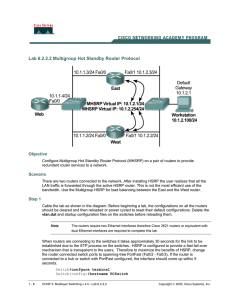
Lab 6.2.2.2 Multigroup Hot Standby Router Protocol
... To utilize both paths from the host network to the server network, configure Multigroup HSRP (MHSRP) between East and West. East and West are both configured with the same two HSRP groups. For group 1, East is the active router and West is the standby router. For group 2, West is the active router a ...
... To utilize both paths from the host network to the server network, configure Multigroup HSRP (MHSRP) between East and West. East and West are both configured with the same two HSRP groups. For group 1, East is the active router and West is the standby router. For group 2, West is the active router a ...
Guidelines for Interdomain Traffic Engineering
... Interdomain traffic engineering is significantly more complicated than intradomain traffic engineering. While IGPs select paths based on link metrics, such as static weights or dynamic load information, BGP advertisements do not explicitly convey any information about the resources available on a pa ...
... Interdomain traffic engineering is significantly more complicated than intradomain traffic engineering. While IGPs select paths based on link metrics, such as static weights or dynamic load information, BGP advertisements do not explicitly convey any information about the resources available on a pa ...
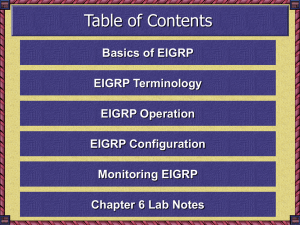
Overview of Scalable Networks
... all the information necessary to calculate a set of distances and vectors to all reachable destinations FD—Feasible Distance; lowest calculated metric to reach a destination as opposed to… RD—Reported Distance or Advertised Distance; distance to the destination reported by the neighbor. ...
... all the information necessary to calculate a set of distances and vectors to all reachable destinations FD—Feasible Distance; lowest calculated metric to reach a destination as opposed to… RD—Reported Distance or Advertised Distance; distance to the destination reported by the neighbor. ...
Performance Characterization and Call Reliability
... VoLTE is superior in a majority of the metrics: it delivers the best audio quality, much better than legacy 3G call; compared to OTT VoIP call, it consumes 83% less data, 75% less energy, and also has around 40% shorter call setup time. The major challenge of VoLTE in the early deployment is the ina ...
... VoLTE is superior in a majority of the metrics: it delivers the best audio quality, much better than legacy 3G call; compared to OTT VoIP call, it consumes 83% less data, 75% less energy, and also has around 40% shorter call setup time. The major challenge of VoLTE in the early deployment is the ina ...
Raven and PinPoint GPRS User Guide
... GPRS is an IP-based service that offers fast, packet-switched access to data networks such as the Internet. It is a mobile service that improves the peak-time capacity of a GSM network. GPRS gives packet-switched access over GSM to external data networks with high peak transfer capacity. The main ob ...
... GPRS is an IP-based service that offers fast, packet-switched access to data networks such as the Internet. It is a mobile service that improves the peak-time capacity of a GSM network. GPRS gives packet-switched access over GSM to external data networks with high peak transfer capacity. The main ob ...
MCT+Design+Options+and+Best+Practices+Guide+for+NetIron+
... • Most IT admin who are familiar with L2 MCT forget to configure l2VPN peers • Cluster will not form without L2VPN peer ...
... • Most IT admin who are familiar with L2 MCT forget to configure l2VPN peers • Cluster will not form without L2VPN peer ...
Power Control for Cognitive Radio Networks
... (receivers) would be colocated. Fig. 1 would also apply to the scenario of the primary users’ and secondary users’ receivers (transmitters) being colocated. An example of this would be if both the secondary and primary users are doing a file upload (download) through a common sink (source). Note tha ...
... (receivers) would be colocated. Fig. 1 would also apply to the scenario of the primary users’ and secondary users’ receivers (transmitters) being colocated. An example of this would be if both the secondary and primary users are doing a file upload (download) through a common sink (source). Note tha ...
Sams Teach Yourself Networking in 24 Hours
... All terms mentioned in this book that are known to be trademarks or service marks have been appropriately capitalized. Sams Publishing cannot attest to the accuracy of this information. Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark. ...
... All terms mentioned in this book that are known to be trademarks or service marks have been appropriately capitalized. Sams Publishing cannot attest to the accuracy of this information. Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark. ...
Communications Market Act
... using cables or other leased lines; 9) public authority network means a communications network built for the needs of public order and security, rescue activities or civil defence, whose subscriber connections can be made available not only to public authorities but also to other user groups essenti ...
... using cables or other leased lines; 9) public authority network means a communications network built for the needs of public order and security, rescue activities or civil defence, whose subscriber connections can be made available not only to public authorities but also to other user groups essenti ...
Ethernet Communication Adapter
... 1.4 Connecting the Network ..................................................................................................................... 6 1.4.1 Network Connector .................................................................................................................. 6 1.4.2 Networ ...
... 1.4 Connecting the Network ..................................................................................................................... 6 1.4.1 Network Connector .................................................................................................................. 6 1.4.2 Networ ...