jetstream 4000, 8500, lanstream 2000
... The Perle JETSTREAM 4000, JETSTREAM 8500 and LANSTREAM 2000 products have been found to comply with the limits for a Class A digital device, pursuant to Part 15 of the FCC rules. These limits are designed to provide reasonable protection against harmful interference when the equipment is operated in ...
... The Perle JETSTREAM 4000, JETSTREAM 8500 and LANSTREAM 2000 products have been found to comply with the limits for a Class A digital device, pursuant to Part 15 of the FCC rules. These limits are designed to provide reasonable protection against harmful interference when the equipment is operated in ...
Document
... possible addresses. IPv6 has been slow to arrive IPv4 revitalized by new features, making IPv6 a luxury, and not a desperately needed fix IPv6 requires new software; IT staffs must be retrained IPv6 will most likely coexist with IPv4 for years to come. Some experts believe IPv4 will remain for more ...
... possible addresses. IPv6 has been slow to arrive IPv4 revitalized by new features, making IPv6 a luxury, and not a desperately needed fix IPv6 requires new software; IT staffs must be retrained IPv6 will most likely coexist with IPv4 for years to come. Some experts believe IPv4 will remain for more ...
EH34803812
... Active worms use various scan mechanisms to propagate themselves efficiently. The basic form of active worms can be categorized as having the Pure Random Scan (PRS) nature. In the PRS form, a worm-infected computer continuously scans a set of random Internet IP addresses to find new vulnerable compu ...
... Active worms use various scan mechanisms to propagate themselves efficiently. The basic form of active worms can be categorized as having the Pure Random Scan (PRS) nature. In the PRS form, a worm-infected computer continuously scans a set of random Internet IP addresses to find new vulnerable compu ...
DutyCon: A dynamic duty-cycle control approach to end
... Periodic sleeping is a widely adopted approach to saving energy for WSNs. The existing periodic sleeping approaches can be categorized into two classes: static sleep scheduling and dynamic sleep scheduling. In the static sleeping approach category, S-MAC [Ye et al. 2002] proposes a synchronous perio ...
... Periodic sleeping is a widely adopted approach to saving energy for WSNs. The existing periodic sleeping approaches can be categorized into two classes: static sleep scheduling and dynamic sleep scheduling. In the static sleeping approach category, S-MAC [Ye et al. 2002] proposes a synchronous perio ...
Cisco MDS 9148S 16G Multilayer Fabric Switch Data Sheet
... The Cisco MDS 9148S offers built-in storage network management and SAN plug-and-play capabilities. All features are available through a command-line interface (CLI) or Cisco Prime DCNM for SAN Essentials Edition, a centralized management tool. Cisco DCNM task-based wizards simplify management of sin ...
... The Cisco MDS 9148S offers built-in storage network management and SAN plug-and-play capabilities. All features are available through a command-line interface (CLI) or Cisco Prime DCNM for SAN Essentials Edition, a centralized management tool. Cisco DCNM task-based wizards simplify management of sin ...
슬라이드 제목 없음
... In Slide 47 we want to send data from a node with network address A and physical address 10, located on one LAN, to a node with a network address P and physical address 95, located on another LAN. Because the two devices are located on different networks, we cannot use link addresses only; the link ...
... In Slide 47 we want to send data from a node with network address A and physical address 10, located on one LAN, to a node with a network address P and physical address 95, located on another LAN. Because the two devices are located on different networks, we cannot use link addresses only; the link ...
Slides
... Multicast is a technique for one-tomany communication over an IPv6 infrastructure in a network. It is often employed for streaming media and Internet television applications. ...
... Multicast is a technique for one-tomany communication over an IPv6 infrastructure in a network. It is often employed for streaming media and Internet television applications. ...
VLAN Trunking
... • A management VLAN is any VLAN you configure to access the management capabilities of a switch. – VLAN 1 would serve as the management VLAN if you did not proactively define a unique VLAN to serve as the management VLAN. – You assign the management VLAN an IP address and ...
... • A management VLAN is any VLAN you configure to access the management capabilities of a switch. – VLAN 1 would serve as the management VLAN if you did not proactively define a unique VLAN to serve as the management VLAN. – You assign the management VLAN an IP address and ...
NPort 6000 Series User`s Manual
... MOXA provides this document “as is,” without warranty of any kind, either expressed or implied, including, but not limited to, its particular purpose. MOXA reserves the right to make improvements and/or changes to this manual, or to the products and/or the programs described in this manual, at any t ...
... MOXA provides this document “as is,” without warranty of any kind, either expressed or implied, including, but not limited to, its particular purpose. MOXA reserves the right to make improvements and/or changes to this manual, or to the products and/or the programs described in this manual, at any t ...
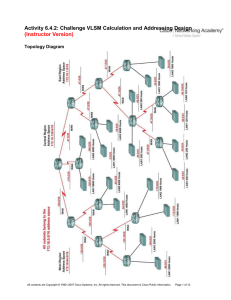
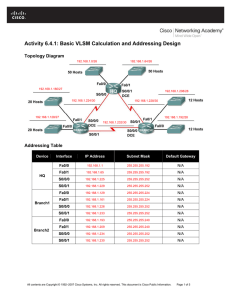
2e_06_6_4_2_vlsm_instr
... All contents are Copyright © 1992–2007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. ...
... All contents are Copyright © 1992–2007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. ...
Configuring VoIP for SonicOS Enhanced
... SonicWALL ViewPoint is a Web-based graphical reporting tool that provides detailed and comprehensive reports of your security and network activities based on syslog data streams received from the firewall. Reports can be generated about virtually any aspect of firewall activity, including individual ...
... SonicWALL ViewPoint is a Web-based graphical reporting tool that provides detailed and comprehensive reports of your security and network activities based on syslog data streams received from the firewall. Reports can be generated about virtually any aspect of firewall activity, including individual ...
TESI DOCTORAL Àlex Vallejo Blanxart
... It is true, a thesis is a very long and lonely journey, but not all the way. It would have been impossible to carry out this thesis without the collaboration of many people. Some of them just helped a bit at some crucial points, some have been around transversally, some we have never met in real lif ...
... It is true, a thesis is a very long and lonely journey, but not all the way. It would have been impossible to carry out this thesis without the collaboration of many people. Some of them just helped a bit at some crucial points, some have been around transversally, some we have never met in real lif ...
re-feedback - Bob Briscoe
... Bob Briscoe et al (BT, UCL & Eurécom ), “Policing Congestion Response in an Internetwork using Re-feedback,” in Proc ACM SIGCOMM'05, CCR 35(4) (Sep 2005) Bob Briscoe (BT & UCL), Arnaud Jacquet and Alessandro Salvatori (BT), “Re-ECN: Adding Accountability for Causing Congestion to TCP/IP,” IETF Inter ...
... Bob Briscoe et al (BT, UCL & Eurécom ), “Policing Congestion Response in an Internetwork using Re-feedback,” in Proc ACM SIGCOMM'05, CCR 35(4) (Sep 2005) Bob Briscoe (BT & UCL), Arnaud Jacquet and Alessandro Salvatori (BT), “Re-ECN: Adding Accountability for Causing Congestion to TCP/IP,” IETF Inter ...
Multicast Basic Concept
... • In practice, the TTL acts a “hop limit” rather than an estimate of delays. • Two uses: – It guarantees that datagrams cannot travel around an internet forever. – Source might want to intentionally limit the journey of the packet. ...
... • In practice, the TTL acts a “hop limit” rather than an estimate of delays. • Two uses: – It guarantees that datagrams cannot travel around an internet forever. – Source might want to intentionally limit the journey of the packet. ...
MCT+Design+Options+and+Best+Practices+Guide+for+NetIron+
... • Number of clients, ports and VLANs must conform scalability formula • Exceeding the supported scalability may cause cluster in unstable forwarding • More clients can be added later without interrupting the traffic from existing clients with scalability enhancement © 2012 Brocade Communications Sys ...
... • Number of clients, ports and VLANs must conform scalability formula • Exceeding the supported scalability may cause cluster in unstable forwarding • More clients can be added later without interrupting the traffic from existing clients with scalability enhancement © 2012 Brocade Communications Sys ...
PDF - Complete Book (2.38 MB)
... gateway for the device. You can also use this command to transfer a Cisco software image to a device when the device is in boot mode. In boot mode, IP routing is not enabled on the device. Unlike the ip default-gateway command, the ip default-network command can be used when IP routing is enabled on ...
... gateway for the device. You can also use this command to transfer a Cisco software image to a device when the device is in boot mode. In boot mode, IP routing is not enabled on the device. Unlike the ip default-gateway command, the ip default-network command can be used when IP routing is enabled on ...
Configuring VoIP for SonicOS Standard
... SonicWALL ViewPoint is a Web-based graphical reporting tool that provides detailed and comprehensive reports of your security and network activities based on syslog data streams received from the firewall. Reports can be generated about virtually any aspect of firewall activity, including individual ...
... SonicWALL ViewPoint is a Web-based graphical reporting tool that provides detailed and comprehensive reports of your security and network activities based on syslog data streams received from the firewall. Reports can be generated about virtually any aspect of firewall activity, including individual ...
Activity 6.4.1: Basic VLSM Calculation and Addressing Design
... 4. What is the maximum number of host IP addresses that are needed for a single subnet? _______ 5. What is the least number of host IP addresses that are needed for a single subnet? _______ 6. How many IP addresses are needed for the East portion of the network? Be sure to include the WAN links betw ...
... 4. What is the maximum number of host IP addresses that are needed for a single subnet? _______ 5. What is the least number of host IP addresses that are needed for a single subnet? _______ 6. How many IP addresses are needed for the East portion of the network? Be sure to include the WAN links betw ...
MPLS QoS - Lyle School of Engineering
... • If LSR1 does not already have a LDP session for the exchange of label spaces LSR1:a and LSR2:b, it attempts to open a TCP connection with LSR2 • LSR1 determines the transport addresses at its end (A1) and LSR2’s end (A2) of the TCP connection • If A1>A2, LSR1 plays the active role; otherwise it is ...
... • If LSR1 does not already have a LDP session for the exchange of label spaces LSR1:a and LSR2:b, it attempts to open a TCP connection with LSR2 • LSR1 determines the transport addresses at its end (A1) and LSR2’s end (A2) of the TCP connection • If A1>A2, LSR1 plays the active role; otherwise it is ...
EE689 Lecture 12
... • Allows sender-specific reports when multiple senders are in a multicast group • Can exclude certain senders and allow certain senders - allows better bandwidth management in multi-sender multicasts. ...
... • Allows sender-specific reports when multiple senders are in a multicast group • Can exclude certain senders and allow certain senders - allows better bandwidth management in multi-sender multicasts. ...
Serial Server Installation Guide
... Connect the MSS to the Ethernet. The MSS1 can be connected to a 10BASE-T Ethernet network. The MSS100 can be connected to a 10BASE-T or 100BASE-T Ethernet network. Connect the appropriate twisted-pair Ethernet cable to the RJ45 connector on the back of the MSS. The MSS100 will autosense whether the ...
... Connect the MSS to the Ethernet. The MSS1 can be connected to a 10BASE-T Ethernet network. The MSS100 can be connected to a 10BASE-T or 100BASE-T Ethernet network. Connect the appropriate twisted-pair Ethernet cable to the RJ45 connector on the back of the MSS. The MSS100 will autosense whether the ...
CoreBuilder 3500 Implementation Guide
... If you are a United States government agency, then this documentation and the software described herein are provided to you subject to the following: All technical data and computer software are commercial in nature and developed solely at private expense. Software is delivered as “Commercial Comput ...
... If you are a United States government agency, then this documentation and the software described herein are provided to you subject to the following: All technical data and computer software are commercial in nature and developed solely at private expense. Software is delivered as “Commercial Comput ...
Wireless-G VPN Router with RangeBooster USER GUIDE BUSINESS SERIES
... to your broadband DSL or Cable modem. For the LAN interface, there is a built-in 4-port, full-duplex 10/100 Ethernet switch that can connect up to four devices. The wireless AP supports 802.11b/g and incorporates Linksys RangeBooster technology, which utilizes a MIMO antennae configuration to provid ...
... to your broadband DSL or Cable modem. For the LAN interface, there is a built-in 4-port, full-duplex 10/100 Ethernet switch that can connect up to four devices. The wireless AP supports 802.11b/g and incorporates Linksys RangeBooster technology, which utilizes a MIMO antennae configuration to provid ...
Computer Networking : Principles, Protocols and Practice
... information about a given topic is sometimes only a few clicks away. Websites such as wikipedia provide lots of information on various topics and students often consult them. Unfortunately, the organisation of the information on these websites is not well suited to allow students to learn from them. ...
... information about a given topic is sometimes only a few clicks away. Websites such as wikipedia provide lots of information on various topics and students often consult them. Unfortunately, the organisation of the information on these websites is not well suited to allow students to learn from them. ...