Cisco VG200: Cisco IP Telephony Voice Gateway
... NOTE: The VG200 is designed and validated strictly for Cisco AVVID CallManager environments only. It is not intended, tested or supported for applications such as H.323 toll bypass or as a SIP GW. The Cisco VG200 Voice-over-IP (VoIP) Gateway is a next-generation voice-conversion device that provides ...
... NOTE: The VG200 is designed and validated strictly for Cisco AVVID CallManager environments only. It is not intended, tested or supported for applications such as H.323 toll bypass or as a SIP GW. The Cisco VG200 Voice-over-IP (VoIP) Gateway is a next-generation voice-conversion device that provides ...
Auto Dedicated NIC Feature in iDRAC7
... Auto Dedicated NIC Feature in iDRAC7 You can adjust the time allowed to scan and detect a cable connected or disconnected to the dedicated NIC port from 5 to 255 seconds. By default, cable connection is detected within 5 seconds and disconnection is detected within 30 seconds. The time it takes to ...
... Auto Dedicated NIC Feature in iDRAC7 You can adjust the time allowed to scan and detect a cable connected or disconnected to the dedicated NIC port from 5 to 255 seconds. By default, cable connection is detected within 5 seconds and disconnection is detected within 30 seconds. The time it takes to ...
Stateless Addr. Autoconfiguration
... • Use of Anycast address include services where redundancy is desirable, for e.g. - routers, name servers, software mirroring. Information & Communications Networks & Multimedia Communication ...
... • Use of Anycast address include services where redundancy is desirable, for e.g. - routers, name servers, software mirroring. Information & Communications Networks & Multimedia Communication ...
TCP/IP Tutorial and Technical Overview
... When you send information to IBM, you grant IBM a non-exclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. Copyright International Business Machines Corporation 1989, 1998. All rights reserved. Note to U.S. Government User ...
... When you send information to IBM, you grant IBM a non-exclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. Copyright International Business Machines Corporation 1989, 1998. All rights reserved. Note to U.S. Government User ...
23002-a20 - Network architecture
... UMTS™ is a Trade Mark of ETSI registered for the benefit of its members 3GPP™ is a Trade Mark of ETSI registered for the benefit of its Members and of the 3GPP Organizational Partners LTE™ is a Trade Mark of ETSI currently being registered for the benefit of its Members and of the 3GPP Organizationa ...
... UMTS™ is a Trade Mark of ETSI registered for the benefit of its members 3GPP™ is a Trade Mark of ETSI registered for the benefit of its Members and of the 3GPP Organizational Partners LTE™ is a Trade Mark of ETSI currently being registered for the benefit of its Members and of the 3GPP Organizationa ...
Offset Time-Emulated Architecture for Optical Burst Switching - Modelling and Performance Evaluation
... 8.4 Markov chain representing a single-wavelength model of PW mechanism. 8.5 (a) Successful preemption and (b) preemption fail cases; the processing times are neglected for simplicity, T is the duration of the Preemption Window, lLP and lHP are the durations of the LP and HP bursts respectively, t i ...
... 8.4 Markov chain representing a single-wavelength model of PW mechanism. 8.5 (a) Successful preemption and (b) preemption fail cases; the processing times are neglected for simplicity, T is the duration of the Preemption Window, lLP and lHP are the durations of the LP and HP bursts respectively, t i ...
- Webcollage.net
... greater control to block inappropriate and illegal Web sites as well as to control the use of instant messaging and peer-to-peer applications. SonicWALL Application Intelligence, Control and Visualization extends control over nonproductive applications like online trading, instant messaging/chat, pe ...
... greater control to block inappropriate and illegal Web sites as well as to control the use of instant messaging and peer-to-peer applications. SonicWALL Application Intelligence, Control and Visualization extends control over nonproductive applications like online trading, instant messaging/chat, pe ...
Summit WM20 User Guide
... Everywhere, Extreme Networks, Extreme Standby Router Protocol, Extreme Turbodrive, Extreme Velocity, ExtremeWare, ExtremeWorks, ExtremeXOS, the Go Purple Extreme Solution, ScreenPlay, Sentriant, ServiceWatch, Summit, SummitStack, Unified Access Architecture, Unified Access RF Manager, UniStack, UniS ...
... Everywhere, Extreme Networks, Extreme Standby Router Protocol, Extreme Turbodrive, Extreme Velocity, ExtremeWare, ExtremeWorks, ExtremeXOS, the Go Purple Extreme Solution, ScreenPlay, Sentriant, ServiceWatch, Summit, SummitStack, Unified Access Architecture, Unified Access RF Manager, UniStack, UniS ...
Communications Server for z/OS V1R2 TCP/IP
... Take Note! Before using this information and the product it supports, be sure to read the general information in “Notices” on page vii. ...
... Take Note! Before using this information and the product it supports, be sure to read the general information in “Notices” on page vii. ...
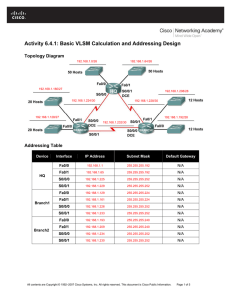
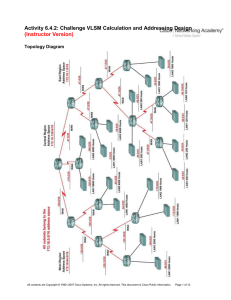
Activity 6.4.1: Basic VLSM Calculation and Addressing Design
... Task 2: Divide the Network into Three Subnetworks. Step 1: Determine the subnet information for each network section. To keep the subnets of each of the major network sections contiguous, begin by creating a main subnet for each of the East, West, and Central network sections. 1. What is the smalles ...
... Task 2: Divide the Network into Three Subnetworks. Step 1: Determine the subnet information for each network section. To keep the subnets of each of the major network sections contiguous, begin by creating a main subnet for each of the East, West, and Central network sections. 1. What is the smalles ...
Thwarting E-mail Spam Laundering - Computer Science
... to be used as spam proxies to pump out e-mail spam. Without serious performance degradation, most nonprofessional Windows users are not aware of the ongoing spamming. Recent research on the network-level behavior of spammers [Ramachandran and Feamster 2006] also confirms that most sinked spam is ori ...
... to be used as spam proxies to pump out e-mail spam. Without serious performance degradation, most nonprofessional Windows users are not aware of the ongoing spamming. Recent research on the network-level behavior of spammers [Ramachandran and Feamster 2006] also confirms that most sinked spam is ori ...
Implementing IPv6 in a Production Network
... exhaustion of IP version 4 (IPv4) addresses and the consequent enablement of more service provider’s infrastructures for IPv6 around the world, but also the imminent availability of IPv6 in consumer devices. This project dealt with the practical implementation of IPv6 on CompanyXYZ production networ ...
... exhaustion of IP version 4 (IPv4) addresses and the consequent enablement of more service provider’s infrastructures for IPv6 around the world, but also the imminent availability of IPv6 in consumer devices. This project dealt with the practical implementation of IPv6 on CompanyXYZ production networ ...
Single Packet IP Traceback in AS-level Partial Deployment Scenario
... traffic. In the same paper, the authors mentioned the idea of IP traceback based on marking packets, either probabilistically or deterministically, with the identification information (e.g., IP addresses) of routers they pass through. Usually, the mark overloads a rarely used field in IP packet head ...
... traffic. In the same paper, the authors mentioned the idea of IP traceback based on marking packets, either probabilistically or deterministically, with the identification information (e.g., IP addresses) of routers they pass through. Usually, the mark overloads a rarely used field in IP packet head ...
slides 3
... the path we know, could miss something – Most network problems occur on the demarcation between networks – Testing around the problem won’t work (we still have to transit this network) ...
... the path we know, could miss something – Most network problems occur on the demarcation between networks – Testing around the problem won’t work (we still have to transit this network) ...
Model FVL328 ProSafe High-Speed VPN Firewall Reference
... This equipment is in the second category (information equipment to be used in a residential area or an adjacent area thereto), and conforms to the standards set by the Voluntary Control Council for Interference by Data Processing Equipment and Electronic Office Machines, aimed at preventing radio in ...
... This equipment is in the second category (information equipment to be used in a residential area or an adjacent area thereto), and conforms to the standards set by the Voluntary Control Council for Interference by Data Processing Equipment and Electronic Office Machines, aimed at preventing radio in ...
Architectures and Algorithms for IPv4/IPv6
... encouragement were the true reason that made me embrace and nourish this endeavour. ...
... encouragement were the true reason that made me embrace and nourish this endeavour. ...
User Manual Wireless Controller
... Wireless LAN AP information ................................................................................ 99 Cluster information ................................................................................................ 101 ...
... Wireless LAN AP information ................................................................................ 99 Cluster information ................................................................................................ 101 ...
IPv6 and Transition Mechanisms
... 6over4 • Deprecated... • "Multicast tunnelling" • Single IPv6 hosts use the IPv4 Multicast Network to connect between them or the native IPv6 network via a 6over4 router (usually a 6to4 router) • The result is IPv6 hosts directly connected, even using IPv6 Link Local addresses (derived fromtheir IPv ...
... 6over4 • Deprecated... • "Multicast tunnelling" • Single IPv6 hosts use the IPv4 Multicast Network to connect between them or the native IPv6 network via a 6over4 router (usually a 6to4 router) • The result is IPv6 hosts directly connected, even using IPv6 Link Local addresses (derived fromtheir IPv ...
LABEL SPACE REDUCTION IN GMPLS AND ALL-OPTICAL LABEL SWAPPING NETWORKS
... be seen in the upper part of Fig. 1. Fig. 1 also shows the forwarding of several lightpaths and demands, which will be described later. Usually, a lightpath forwards more than one demand. This is motivated by: a) the number of wavelengths in a fiber being too small compared to the number of demands ...
... be seen in the upper part of Fig. 1. Fig. 1 also shows the forwarding of several lightpaths and demands, which will be described later. Usually, a lightpath forwards more than one demand. This is motivated by: a) the number of wavelengths in a fiber being too small compared to the number of demands ...
Network Working Group G. Bernstein Request for
... There are currently two different multiplexing technologies in use in optical networks: wavelength-division multiplexing (WDM) and time division multiplexing (TDM). This work focuses on TDM technology. SDH and SONET are two TDM standards widely used by operators to transport and multiplex different ...
... There are currently two different multiplexing technologies in use in optical networks: wavelength-division multiplexing (WDM) and time division multiplexing (TDM). This work focuses on TDM technology. SDH and SONET are two TDM standards widely used by operators to transport and multiplex different ...
ForeRunner
... Copyright © 1995-1998 FORE Systems, Inc. All rights reserved. FORE Systems is a registered trademark, and ForeRunner, ForeRunnerLE, ForeThought, ForeView, PowerHub, and CellPath are trademarks of FORE Systems, Inc. All other brands or product names are trademarks or registered trademarks of their re ...
... Copyright © 1995-1998 FORE Systems, Inc. All rights reserved. FORE Systems is a registered trademark, and ForeRunner, ForeRunnerLE, ForeThought, ForeView, PowerHub, and CellPath are trademarks of FORE Systems, Inc. All other brands or product names are trademarks or registered trademarks of their re ...