Open Multi-Core Router
... BFD provides light-load, short-time detection. It can be used to provide real-time detection of any media and any protocol layer. The detection time and the overhead scope are wide. According to BFD, fault detection can be performed on any type of channels between two systems, including the direct p ...
... BFD provides light-load, short-time detection. It can be used to provide real-time detection of any media and any protocol layer. The detection time and the overhead scope are wide. According to BFD, fault detection can be performed on any type of channels between two systems, including the direct p ...
Slides
... Wireless host communicates with a base station base station = access point (AP) Basic Service Set (BSS) (a.k.a. “cell”) contains: ...
... Wireless host communicates with a base station base station = access point (AP) Basic Service Set (BSS) (a.k.a. “cell”) contains: ...
Switched Broadcast 2003
... and screen) are needed when network access and remote control applications have failed. ...
... and screen) are needed when network access and remote control applications have failed. ...
McAfee Security Management Center
... same server or on separate servers, McAfee SMC is designed to manage large geographically distributed networks. McAfee SMC’s flexibility and scalability enable you to scale up current components and add new components to the system without sacrificing ease of use. The larger the environment, the gre ...
... same server or on separate servers, McAfee SMC is designed to manage large geographically distributed networks. McAfee SMC’s flexibility and scalability enable you to scale up current components and add new components to the system without sacrificing ease of use. The larger the environment, the gre ...
Remote Access VPN IPsec
... lines that can only be used by one company. The main purpose of a VPN is to give the company the same capabilities as private leased lines at much lower cost by using the shared public infrastructure. Phone companies have provided private shared resources for voice messages for over a decade. A virt ...
... lines that can only be used by one company. The main purpose of a VPN is to give the company the same capabilities as private leased lines at much lower cost by using the shared public infrastructure. Phone companies have provided private shared resources for voice messages for over a decade. A virt ...
IOSR Journal of Electronics and Communication Engineering (IOSR-JECE)
... In general, we do not want this to happen since some data paths may be extended. Distributed Routing Algorithm opts to avoid that by sustaining the existing links. Thus, if a child receives a message that the parent P is moving, the child then notices its neighbors (grandchildren of node P) and trav ...
... In general, we do not want this to happen since some data paths may be extended. Distributed Routing Algorithm opts to avoid that by sustaining the existing links. Thus, if a child receives a message that the parent P is moving, the child then notices its neighbors (grandchildren of node P) and trav ...
GSC-12 - ITU-T security standardization
... LIVE at: http://www.itu.int/cybersecurity Provides an easy-to-use information resource on national, regional and international cybersecurity-related activities and initiatives worldwide. ...
... LIVE at: http://www.itu.int/cybersecurity Provides an easy-to-use information resource on national, regional and international cybersecurity-related activities and initiatives worldwide. ...
Chapter 15. Recent advances
... bandwidth, and a transparent support for user mobility. On today’s internet, 90% of the traffic uses TCP, while 80% of the networking is done over the IP network. ...
... bandwidth, and a transparent support for user mobility. On today’s internet, 90% of the traffic uses TCP, while 80% of the networking is done over the IP network. ...
FS-ETH-SC09
... Before you use,please be sure to read this manual carefully, you will know its powerful and perfect function and simple use. The main function of the product is the date communication between the Mitsubishi FX series PLC( ( FX0N/FX1N/FX2N/FX3U/FX3G……) through the programming interfaces or FXxx-422-B ...
... Before you use,please be sure to read this manual carefully, you will know its powerful and perfect function and simple use. The main function of the product is the date communication between the Mitsubishi FX series PLC( ( FX0N/FX1N/FX2N/FX3U/FX3G……) through the programming interfaces or FXxx-422-B ...
LectureClientServerM..
... Appears as though each layer communicates with its peer at the same layer. ...
... Appears as though each layer communicates with its peer at the same layer. ...
1 - Education Queensland
... DETE3G network When the device is delivered it is pre-loaded with a ‘data only’ 3G SIM card. The device serial number and SIM card number is linked to the allocated student. Phone calls cannot be made using the SIM card. If the SIM cards are swapped between devices or inserted into mobile phones, it ...
... DETE3G network When the device is delivered it is pre-loaded with a ‘data only’ 3G SIM card. The device serial number and SIM card number is linked to the allocated student. Phone calls cannot be made using the SIM card. If the SIM cards are swapped between devices or inserted into mobile phones, it ...
A Protocol for a Wireless ... Xiaolan Qian
... Mobile hosts forward all outgoing packets to an access point and receives all incoming packets from the AP. The dependency on the AP emphasizes the importance to maintain adequate communication channels between the AP and the mobile at all times. How robust the channel is depends on the physical lay ...
... Mobile hosts forward all outgoing packets to an access point and receives all incoming packets from the AP. The dependency on the AP emphasizes the importance to maintain adequate communication channels between the AP and the mobile at all times. How robust the channel is depends on the physical lay ...
Chapter 02 - Communicating Over The Network
... services. Users use an application called a Mail User Agent (MUA), or e-mail client to allow messages to be sent and places received messages into the client's mailbox. In order to receive e-mail messages from an email server, the e-mail client can use POP. Sending e-mail from either a client or a s ...
... services. Users use an application called a Mail User Agent (MUA), or e-mail client to allow messages to be sent and places received messages into the client's mailbox. In order to receive e-mail messages from an email server, the e-mail client can use POP. Sending e-mail from either a client or a s ...
notes - Academic Csuohio
... Examine incoming frame’s MAC address, selectively forward frame to one-or-more outgoing links when frame is to be forwarded on segment, uses CSMA/CD to access segment Hosts are unaware of presence of switches ...
... Examine incoming frame’s MAC address, selectively forward frame to one-or-more outgoing links when frame is to be forwarded on segment, uses CSMA/CD to access segment Hosts are unaware of presence of switches ...
Overview Presentation
... Upon completion of this course, students will be able to: • Describe security threats facing modern network infrastructures • Secure network device access • Implement AAA on network devices • Mitigate threats to networks using ACLs • Implement secure network management and reporting • Mitigate comm ...
... Upon completion of this course, students will be able to: • Describe security threats facing modern network infrastructures • Secure network device access • Implement AAA on network devices • Mitigate threats to networks using ACLs • Implement secure network management and reporting • Mitigate comm ...
A Review on Intrusion Detection System to Protect Cloud Data
... potentially eradicate attacks on a system. An Intrusion detection system pertains to the methods used to identify an attack on a computer or computer network. In cloud computing environment the applications are user-centric and the customers should be confident about their applications stored in the ...
... potentially eradicate attacks on a system. An Intrusion detection system pertains to the methods used to identify an attack on a computer or computer network. In cloud computing environment the applications are user-centric and the customers should be confident about their applications stored in the ...
ECx Ethernet Control Guide
... Compatibility Information The following are required to use ECx: • A VENUE system that has already been installed and configured, running D-Show software 1.1 or higher • A Digidesign-qualified router or wireless access point (WAP) device • A client computer running Digidesign-qualified Windows or Ma ...
... Compatibility Information The following are required to use ECx: • A VENUE system that has already been installed and configured, running D-Show software 1.1 or higher • A Digidesign-qualified router or wireless access point (WAP) device • A client computer running Digidesign-qualified Windows or Ma ...
Wireless Topologies
... • Several companies have introduced proprietary Inter-Access Point Protocols (IAPP) to support roaming. • IAPP accomplishes roaming within a subnet. However, it does not address how the wireless system tracks users moving from one subnet to another when the same session must be maintained, as in the ...
... • Several companies have introduced proprietary Inter-Access Point Protocols (IAPP) to support roaming. • IAPP accomplishes roaming within a subnet. However, it does not address how the wireless system tracks users moving from one subnet to another when the same session must be maintained, as in the ...
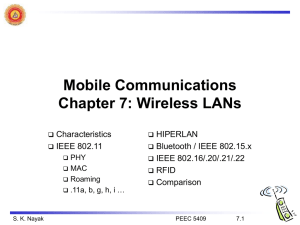
C07-Wireless_LANs_f
... typically very low bandwidth compared to wired networks (1-10 Mbit/s) due to shared medium many proprietary solutions, especially for higher bit-rates, standards take their time (e.g. IEEE 802.11) products have to follow many national restrictions if working wireless, it takes a vary long time t ...
... typically very low bandwidth compared to wired networks (1-10 Mbit/s) due to shared medium many proprietary solutions, especially for higher bit-rates, standards take their time (e.g. IEEE 802.11) products have to follow many national restrictions if working wireless, it takes a vary long time t ...
VPN
... connection and tracks what you do while you're logged in. Firewall - maintaining that the information on the private network is secure ...
... connection and tracks what you do while you're logged in. Firewall - maintaining that the information on the private network is secure ...
945U-E Ethernet Modem
... ELPRO products are designed to be used in industrial environments by experienced industrial engineering personnel with adequate knowledge of safety design considerations. ELPRO radio products are used on unprotected license-free radio bands with radio noise and interference. The products are designe ...
... ELPRO products are designed to be used in industrial environments by experienced industrial engineering personnel with adequate knowledge of safety design considerations. ELPRO radio products are used on unprotected license-free radio bands with radio noise and interference. The products are designe ...
Emulating Mobile Ad-hoc Networks of Hand
... even if they do not provide the features which we need for our intends. NS2 [3] on its own enables to emulate only wired networks. Anyway, Magdeburg University has developed a NS2’s patch to perform wireless emulation [6]. This patched NS2 version can emulate an arbitrary IEEE 802.11 network by conn ...
... even if they do not provide the features which we need for our intends. NS2 [3] on its own enables to emulate only wired networks. Anyway, Magdeburg University has developed a NS2’s patch to perform wireless emulation [6]. This patched NS2 version can emulate an arbitrary IEEE 802.11 network by conn ...
Network Building Blocks
... which essentially establishes a private link between one telephone and another for the duration of a call. The computer network uses a technology called packet switching (数据包转换) in which a message was divided into several packets that can be routed independently to their destination to avoid out-o ...
... which essentially establishes a private link between one telephone and another for the duration of a call. The computer network uses a technology called packet switching (数据包转换) in which a message was divided into several packets that can be routed independently to their destination to avoid out-o ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.