document
... independently - different protocols, MTUs Can support notifications that can be used by link and location aware applications IFA’2004 ...
... independently - different protocols, MTUs Can support notifications that can be used by link and location aware applications IFA’2004 ...
Reference Manual for the 108 Mbps Wireless Firewall Router WGT624
... Federal Communications Commission (FCC) Compliance Notice: Radio Frequency Notice This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interfer ...
... Federal Communications Commission (FCC) Compliance Notice: Radio Frequency Notice This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interfer ...
Data_Networking_Slideshow
... Control (MAC) addresses • Define the Spanning Tree Protocol (STP) • Define networking methods, standards and protocols, and their characteristics • Explain the concept of protocol tunneling, and identify elements and benefits of using a Virtual Private Network (VPN) in a convergent network Data Netw ...
... Control (MAC) addresses • Define the Spanning Tree Protocol (STP) • Define networking methods, standards and protocols, and their characteristics • Explain the concept of protocol tunneling, and identify elements and benefits of using a Virtual Private Network (VPN) in a convergent network Data Netw ...
EN 302 636-1 - V1.2.1 - Intelligent Transport Systems (ITS
... Wireless communication is a cornerstone of future Intelligent Transport Systems (ITS). Many ITS applications require the dissemination of information with a rapid and direct communication, which can be achieved by ad hoc networking. GeoNetworking is a network-layer protocol for mobile ad hoc communi ...
... Wireless communication is a cornerstone of future Intelligent Transport Systems (ITS). Many ITS applications require the dissemination of information with a rapid and direct communication, which can be achieved by ad hoc networking. GeoNetworking is a network-layer protocol for mobile ad hoc communi ...
No Slide Title
... – Technologies: passwords, challenge phrase, hard and soft tokens with one-time passwords, and X.509 digital certificates – Products: NT Domains*, NDS*, RADIUS, SDI*, Entrust*, Shiva® CA ...
... – Technologies: passwords, challenge phrase, hard and soft tokens with one-time passwords, and X.509 digital certificates – Products: NT Domains*, NDS*, RADIUS, SDI*, Entrust*, Shiva® CA ...
OfficeConnect ADSL Wireless 11g Firewall Router User Guide
... The OfficeConnect ADSL Wireless 11g Firewall Router is designed to provide a cost-effective means of sharing a single broadband Internet connection amongst several wired and wireless computers. The Router also provides protection in the form of an electronic “firewall” preventing anyone outside of y ...
... The OfficeConnect ADSL Wireless 11g Firewall Router is designed to provide a cost-effective means of sharing a single broadband Internet connection amongst several wired and wireless computers. The Router also provides protection in the form of an electronic “firewall” preventing anyone outside of y ...
SYSTEM ARCHITECTURE OF A WIRELESS BODY AREA SENSOR
... uploads when a link becomes available. This organization allows full mobility of users with secure and near real time health information uploads. A pivotal part of the telemedical system is tier 1 – wireless body area sensor network. It comprises a number of intelligent nodes, each capable of sensin ...
... uploads when a link becomes available. This organization allows full mobility of users with secure and near real time health information uploads. A pivotal part of the telemedical system is tier 1 – wireless body area sensor network. It comprises a number of intelligent nodes, each capable of sensin ...
The Transport Layer: TCP and UDP
... should be sent to port b and the label should be popped (removed). The packet exits as an ordinary IP packet, without MPLS label. An IP packet arrives, at MPLS node B, with source IP address 122.1.2.3 and destination IP address 129.88.38.1. It arrives from outside the MPLS cloud, as an ordinary IP p ...
... should be sent to port b and the label should be popped (removed). The packet exits as an ordinary IP packet, without MPLS label. An IP packet arrives, at MPLS node B, with source IP address 122.1.2.3 and destination IP address 129.88.38.1. It arrives from outside the MPLS cloud, as an ordinary IP p ...
Simulation study of blackhole attack in the mobile Ad hoc networks
... Wireless network is the network of mobile computer nodes or stations that are not physically wired. The main advantage of this is communicating with rest of the world while being mobile. The disadvantages are their limited bandwidth, memory, processing capabilities and open medium. Two basic system ...
... Wireless network is the network of mobile computer nodes or stations that are not physically wired. The main advantage of this is communicating with rest of the world while being mobile. The disadvantages are their limited bandwidth, memory, processing capabilities and open medium. Two basic system ...
Intrusion Defense Firewall
... The Intrusion Defense Firewall is bi-directional; it allows different rules to be applied to data entering or leaving the endpoint. This allows you to deal with both incoming attacks and outbound compliance issues. For example, in an e-health patient record application, a custom rule could block a s ...
... The Intrusion Defense Firewall is bi-directional; it allows different rules to be applied to data entering or leaving the endpoint. This allows you to deal with both incoming attacks and outbound compliance issues. For example, in an e-health patient record application, a custom rule could block a s ...
ZigBee Overview
... addresses left to assign. Decremented by 1 each time an address is assigned. nwkAddressIncrement – The amount by which nwkNextAddress is incremented each time an address is assigned. ...
... addresses left to assign. Decremented by 1 each time an address is assigned. nwkAddressIncrement – The amount by which nwkNextAddress is incremented each time an address is assigned. ...
HotView Pro™ Mesh Management Software
... Any HotPort mesh can internetwork with any other LAN/WAN domain, including the Internet or an enterprise network. A node designated as a Network Gateway Interconnect (NGI) provides the basic connection; multiple NGI nodes add multi-path performance and redundancy. ...
... Any HotPort mesh can internetwork with any other LAN/WAN domain, including the Internet or an enterprise network. A node designated as a Network Gateway Interconnect (NGI) provides the basic connection; multiple NGI nodes add multi-path performance and redundancy. ...
Canon WFT-E1 (A) Wireless File Transmitter Network Support Guide
... The target server address should be should match the address of the PC’s wireless transmitter (dongle) in this case it is 192.168.0.10. The port number should match the port number we opened in the FTP server, in this case Port 21 (which is in fact the industry standard port for FTP transfers). The ...
... The target server address should be should match the address of the PC’s wireless transmitter (dongle) in this case it is 192.168.0.10. The port number should match the port number we opened in the FTP server, in this case Port 21 (which is in fact the industry standard port for FTP transfers). The ...
Download PDF
... Patton Acquires OnSite Systems S10 Next-Generation SONET/SDH Solutions Patton expands its TDM, Ethernet, and Metro-Optical transport solutions through product technology rights agreement to the OnSite S10 product line. GAITHERSBURG, MD: Patton—the leader in carrier-class network access, connectivity ...
... Patton Acquires OnSite Systems S10 Next-Generation SONET/SDH Solutions Patton expands its TDM, Ethernet, and Metro-Optical transport solutions through product technology rights agreement to the OnSite S10 product line. GAITHERSBURG, MD: Patton—the leader in carrier-class network access, connectivity ...
RPL (pronounced ripple) Routing Protocol for Low Power and Lossy
... Cryptographic protection against outsider devices only and not against potential malicious devices in key-sharing group. Granularity of data authenticity via – public-key techniques: unique originator of transmitted information; – symmetric-key techniques: entity in key-sharing group. Signatures use ...
... Cryptographic protection against outsider devices only and not against potential malicious devices in key-sharing group. Granularity of data authenticity via – public-key techniques: unique originator of transmitted information; – symmetric-key techniques: entity in key-sharing group. Signatures use ...
On the Reliability and Additional Overhead of Reliable On
... agent receives both control packets and data packets. The link layer simulates the data link protocols. It also sets the MAC destination address in the MAC header of the packet. This function is implemented for two different issues: finding the next-hop-node’s IP address and converting IP address in ...
... agent receives both control packets and data packets. The link layer simulates the data link protocols. It also sets the MAC destination address in the MAC header of the packet. This function is implemented for two different issues: finding the next-hop-node’s IP address and converting IP address in ...
On TCP Performance Enhancing Proxies in a Wireless Environment
... Consider Fig. 1, where the vertical axis represents the amount of unacknowledged data (called the congestion window or CWND) the TCP sender is permitted to transmit to the receiver, and the horizontal axis is time. The dotted red line represents the optimal bandwidth delay product for the transmissi ...
... Consider Fig. 1, where the vertical axis represents the amount of unacknowledged data (called the congestion window or CWND) the TCP sender is permitted to transmit to the receiver, and the horizontal axis is time. The dotted red line represents the optimal bandwidth delay product for the transmissi ...
Cover Traffic
... • Simply not forward traffic for two corresponding flow identifiers by hi • The initiator will suspect hi+1 not to work and will be trying another mimic of hi • hi can repeat that until hi+1 is an adversary mimic as well, and so on for hi+1 • Attack can be avoided if reconstruction starts at node hi ...
... • Simply not forward traffic for two corresponding flow identifiers by hi • The initiator will suspect hi+1 not to work and will be trying another mimic of hi • hi can repeat that until hi+1 is an adversary mimic as well, and so on for hi+1 • Attack can be avoided if reconstruction starts at node hi ...
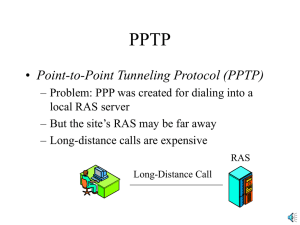
PPTP
... • PPTP Encapsulation – Access concentrator receives the original IP packet, which has the destination IP address of the access concentrator – Adds a new IP header with the IP address of the RAS – Adds an enhanced general routing encapsulation (GRE) header for security Original IP Packet ...
... • PPTP Encapsulation – Access concentrator receives the original IP packet, which has the destination IP address of the access concentrator – Adds a new IP header with the IP address of the RAS – Adds an enhanced general routing encapsulation (GRE) header for security Original IP Packet ...
Note
... as Ethernet, token ring, token bus, FDDI, and ATM LAN, but Ethernet is by far the dominant technology. TCP/IP Protocol Suite ...
... as Ethernet, token ring, token bus, FDDI, and ATM LAN, but Ethernet is by far the dominant technology. TCP/IP Protocol Suite ...
No Slide Title
... Nomadism: “Ability of the user to change his network access point on moving; when changing the network access point, the user's service session is completely stopped and then started again, i.e., there is no session continuity or handover possible. It is assumed that normal usage pattern is that use ...
... Nomadism: “Ability of the user to change his network access point on moving; when changing the network access point, the user's service session is completely stopped and then started again, i.e., there is no session continuity or handover possible. It is assumed that normal usage pattern is that use ...
Linux Networking and Security
... Symmetric cryptosystems can provide confidentiality but they cannot directly provide authentication or nonrepudiation. ...
... Symmetric cryptosystems can provide confidentiality but they cannot directly provide authentication or nonrepudiation. ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.