SpeedStream
... The Software is protected by copyright laws and international copyright treaties. The Software is licensed and not sold to you. Accordingly, while you own the media (CD ROM or floppy disk) on which the Software is recorded, ENI retains ownership of the Software itself. 1. Grant of License. You may i ...
... The Software is protected by copyright laws and international copyright treaties. The Software is licensed and not sold to you. Accordingly, while you own the media (CD ROM or floppy disk) on which the Software is recorded, ENI retains ownership of the Software itself. 1. Grant of License. You may i ...
ppt
... Use virus protection software Keep current on latest service packs Disable unnecessary protocols ...
... Use virus protection software Keep current on latest service packs Disable unnecessary protocols ...
WAN_Unit_7-FRelay
... Almost all North American frame relay implementations use local significant DLCI assignment method The Command/Response (C/R) bit is not used at this time The Forward Explicit Congestion Notification (FECN) bit is a toggle that tells the remote user that network congestion was encountered by t ...
... Almost all North American frame relay implementations use local significant DLCI assignment method The Command/Response (C/R) bit is not used at this time The Forward Explicit Congestion Notification (FECN) bit is a toggle that tells the remote user that network congestion was encountered by t ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... /authenticating itself. It simply configures the address and start communicating with other nodes on the network. Since node does not have to authenticate itself, any malicious node can get access to network. It can cause various kinds of threats which are explained as follows: 3.1. Redirect Attack: ...
... /authenticating itself. It simply configures the address and start communicating with other nodes on the network. Since node does not have to authenticate itself, any malicious node can get access to network. It can cause various kinds of threats which are explained as follows: 3.1. Redirect Attack: ...
Influence of Network Load on the Performance of Opportunistic Scanning
... located within a BSS and are connected to the Internet via their associated AP. Under the ‘best-connected network paradigm’, STAs may continuously choose among alternative links, i.e. another 802.11 AP or secondary technology. Thus, they continuously scan in order to detect alternative technologies ...
... located within a BSS and are connected to the Internet via their associated AP. Under the ‘best-connected network paradigm’, STAs may continuously choose among alternative links, i.e. another 802.11 AP or secondary technology. Thus, they continuously scan in order to detect alternative technologies ...
Basic Service Set
... • The access method differs from the wired Ethernet’s CSMA/CD (Carrier Sensing Media Access and Collision Detection) operation. • 802.11 networks use a collision avoidance approach (CSMA/CA) • Collisions are avoided rather than detected. • This avoidance approach requires each station to listen for ...
... • The access method differs from the wired Ethernet’s CSMA/CD (Carrier Sensing Media Access and Collision Detection) operation. • 802.11 networks use a collision avoidance approach (CSMA/CA) • Collisions are avoided rather than detected. • This avoidance approach requires each station to listen for ...
Network Protocols
... A MN may not use ARP if it is using a FA COA. It needs to use the address of the FA as the destination address. If it is using a collocated COA, then it uses ARP to locate the default router using its COA as source. Note that if the ‘R’ bit is set is uses the FA address as the destination address. F ...
... A MN may not use ARP if it is using a FA COA. It needs to use the address of the FA as the destination address. If it is using a collocated COA, then it uses ARP to locate the default router using its COA as source. Note that if the ‘R’ bit is set is uses the FA address as the destination address. F ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... one receivers. The Internet does not manage the multicast group membership tightly. A multicast message is sent from a source to a group of destination hosts. A source sends a packet to a multicast group specifying as the multicast group address. The packet is automatically duplicated at intermediat ...
... one receivers. The Internet does not manage the multicast group membership tightly. A multicast message is sent from a source to a group of destination hosts. A source sends a packet to a multicast group specifying as the multicast group address. The packet is automatically duplicated at intermediat ...
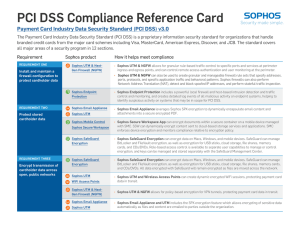
PCI DSS Compliance Reference Card
... The Payment Card Industry Data Security Standard (PCI DSS) is a proprietary information security standard for organizations that handle branded credit cards from the major card schemes including Visa, MasterCard, American Express, Discover, and JCB. The standard covers all major areas of a security ...
... The Payment Card Industry Data Security Standard (PCI DSS) is a proprietary information security standard for organizations that handle branded credit cards from the major card schemes including Visa, MasterCard, American Express, Discover, and JCB. The standard covers all major areas of a security ...
IEEE C802.16ppc-10/0043
... low packet error rate) between the M2M device and the M2M server shall be guaranteed regardless of operating environment (e.g., mobility, channel quality). 6.7 Enhanced Access Priority IEEE 802.16p shall support enhanced access priority which implies that the M2M device is given priority over other ...
... low packet error rate) between the M2M device and the M2M server shall be guaranteed regardless of operating environment (e.g., mobility, channel quality). 6.7 Enhanced Access Priority IEEE 802.16p shall support enhanced access priority which implies that the M2M device is given priority over other ...
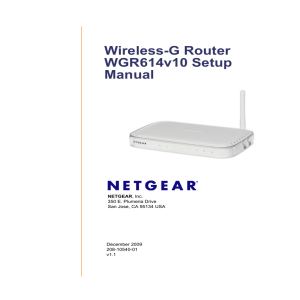
Wireless-G Router WGR614v10 Setup Manual
... Wizard™ Installation Assistant. The Installation Assistant walks you through the steps required to connect your router, modem, and computer(s); configure your wireless settings; and enable wireless security for your network. When you have finished, you will be Internet ready! NETGEAR does not recomm ...
... Wizard™ Installation Assistant. The Installation Assistant walks you through the steps required to connect your router, modem, and computer(s); configure your wireless settings; and enable wireless security for your network. When you have finished, you will be Internet ready! NETGEAR does not recomm ...
Chapter_19_Final
... • Attackers that obtain passwords by illicit means, such as social engineering, and then use remote access technologies to log on to a computer from another location and compromise its data and programming. • Denial of service attacks that use authorized access points to bombard a system with traffi ...
... • Attackers that obtain passwords by illicit means, such as social engineering, and then use remote access technologies to log on to a computer from another location and compromise its data and programming. • Denial of service attacks that use authorized access points to bombard a system with traffi ...
Dia 1
... • The 64-bit prefix is hierarchical – Identifies the network you are on and where it is globally ...
... • The 64-bit prefix is hierarchical – Identifies the network you are on and where it is globally ...
Using Your Gateway WGR
... Now that all the hardware connections have been made, you must configure the access point/router to operate on your network and to connect to the Internet through an ISP. Important ...
... Now that all the hardware connections have been made, you must configure the access point/router to operate on your network and to connect to the Internet through an ISP. Important ...
DNS and ARP
... • used to get datagram from one interface to another physically-connected interface (same network) • 48 bit MAC address (for most LANs) burned into the adapter’s ROM Comnet 2010 ...
... • used to get datagram from one interface to another physically-connected interface (same network) • 48 bit MAC address (for most LANs) burned into the adapter’s ROM Comnet 2010 ...
Campus Fabric Design Guide - CVD - October 2016
... RFC 6830 and other RFCs define LISP as a network architecture and set of protocols that implement a new semantic for IP addressing and forwarding. In traditional IP networks, the IP address is used to identify both an endpoint and its physical location as part of a subnet assignment on a router. In ...
... RFC 6830 and other RFCs define LISP as a network architecture and set of protocols that implement a new semantic for IP addressing and forwarding. In traditional IP networks, the IP address is used to identify both an endpoint and its physical location as part of a subnet assignment on a router. In ...
paper
... multicast problem. Besides video surveillance, several other applications fit this model, such as tactical situation awareness dissemination, periodic sensor measurement distribution, entertainment audio/video steaming, and so forth. Reliable multicast is closely related to the problem at hand. In f ...
... multicast problem. Besides video surveillance, several other applications fit this model, such as tactical situation awareness dissemination, periodic sensor measurement distribution, entertainment audio/video steaming, and so forth. Reliable multicast is closely related to the problem at hand. In f ...
WAN_Unit_8-SMDS
... Access classes are a method of providing bandwidth priorities for times when there is network congestion at the SNI Network congestion occurs when there is an attempt by the network to transfer one or more SMDS data units without an interval of time between the units The access class places a limit ...
... Access classes are a method of providing bandwidth priorities for times when there is network congestion at the SNI Network congestion occurs when there is an attempt by the network to transfer one or more SMDS data units without an interval of time between the units The access class places a limit ...
Chapter 1: A First Look at Windows 2000 Professional
... at upper layers of OSI model Use software to strip all networking information from packet; translate data into new format and return to OSI layers ...
... at upper layers of OSI model Use software to strip all networking information from packet; translate data into new format and return to OSI layers ...
Kismet Menus - SciTech Connect
... or WPA. While these networks are coded as unencrypted, they still may be using a Virtual Private Network (VPN) or some other form of authentication after associating with the network. Yellow networks also indicate that at least some settings have been changed from their factory defaults. The red col ...
... or WPA. While these networks are coded as unencrypted, they still may be using a Virtual Private Network (VPN) or some other form of authentication after associating with the network. Yellow networks also indicate that at least some settings have been changed from their factory defaults. The red col ...
ATM
... – The station then registers with the LES – The BUS address is determined through an LE_ARP with a MAC address of all 1s ...
... – The station then registers with the LES – The BUS address is determined through an LE_ARP with a MAC address of all 1s ...
Denial of Service Attack and Prevention System
... Software, known to us as the Router Control daemon, runs on each of these machines. This software is configured with the location of its neighbors, so that it may know which routers it may communicate with using the Router Control Protocol. The protocol allows for configuration of the traffic blocki ...
... Software, known to us as the Router Control daemon, runs on each of these machines. This software is configured with the location of its neighbors, so that it may know which routers it may communicate with using the Router Control Protocol. The protocol allows for configuration of the traffic blocki ...
Patterson Software Installation Guide
... At least one computer, also known as a workstation or client, that will access the shared resources ...
... At least one computer, also known as a workstation or client, that will access the shared resources ...
Network Support for IP Traceback - David Wetherall
... scheme has many benefits compared to previous work and is in many ways similar to the packet marking approach we have taken. However, there are several disadvantages in the current design that complicate its use. Among these: ICMP traffic is increasingly differentiated and may itself be filtered in ...
... scheme has many benefits compared to previous work and is in many ways similar to the packet marking approach we have taken. However, there are several disadvantages in the current design that complicate its use. Among these: ICMP traffic is increasingly differentiated and may itself be filtered in ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.