Intrusion Detection Systems and IPv6∗
... “attack analysis”. Historically in computing Intrusion Detection has always been the alerting to something being amiss, for example “bad logins”. This was a good example of “white-listing” or the alerting on anything which was not known. Unfortunately “white-listing” has the disadvantage of generati ...
... “attack analysis”. Historically in computing Intrusion Detection has always been the alerting to something being amiss, for example “bad logins”. This was a good example of “white-listing” or the alerting on anything which was not known. Unfortunately “white-listing” has the disadvantage of generati ...
Red Hat Database
... accepted mechanism whereby transmissions can be protected from snooping in transit. Red Hat Database connections can also be tunneled over SSH using SSH software, such as the freely available OpenSSH implementation. This is helpful if you already have deployed SSH in your organization, as it does no ...
... accepted mechanism whereby transmissions can be protected from snooping in transit. Red Hat Database connections can also be tunneled over SSH using SSH software, such as the freely available OpenSSH implementation. This is helpful if you already have deployed SSH in your organization, as it does no ...
M-Connect Brochure
... solution for our customers. They are the only company who we use for connectivity because they are the only company that we feel get it right first time. ...
... solution for our customers. They are the only company who we use for connectivity because they are the only company that we feel get it right first time. ...
Secure coprocessors - University of Pittsburgh
... Drop any security associations that depend on TCB list e.g., destroy keys necessary for network access Log event into secure coprocessor node will need to reboot before regaining access ...
... Drop any security associations that depend on TCB list e.g., destroy keys necessary for network access Log event into secure coprocessor node will need to reboot before regaining access ...
HSARPA Cyber Security R&D
... spread of destructive code through networks and applications. These technologies should focus on detecting “zero day attacks”, the first appearance of malicious code for which no known defense has been constructed. 23 September 2004 ...
... spread of destructive code through networks and applications. These technologies should focus on detecting “zero day attacks”, the first appearance of malicious code for which no known defense has been constructed. 23 September 2004 ...
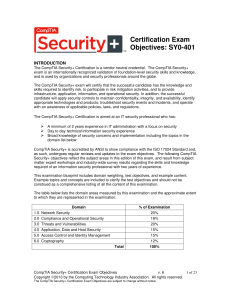
Certification Exam Objectives: SY0-401
... • Risks associated with Cloud Computing and Virtualization • Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
... • Risks associated with Cloud Computing and Virtualization • Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
Ralph`s DHCP #2a
... Relay agent must pick one address to put in ‘giaddr’ If there are multiple subnets on one physical network, which address should relay agent choose? ...
... Relay agent must pick one address to put in ‘giaddr’ If there are multiple subnets on one physical network, which address should relay agent choose? ...
to see the disclosure
... Hostile port blocking: We block known hostile ports to prevent unwanted files, browser hacking and virus attacks. Virus and Spam filtering: We filter email and website traffic for virus activity and Spam using industry standard virus scanning and prevention techniques. Should an email message be fou ...
... Hostile port blocking: We block known hostile ports to prevent unwanted files, browser hacking and virus attacks. Virus and Spam filtering: We filter email and website traffic for virus activity and Spam using industry standard virus scanning and prevention techniques. Should an email message be fou ...
Fujitsu`s Security Technology Based on Practical Knowledge
... measures of security reinforcement. That is, the enhanced detectability through system reinforcement resulted in a torrent of event alerts being issued by the detection system. Soon the situation was one in which there began to be a lack of personnel who were ...
... measures of security reinforcement. That is, the enhanced detectability through system reinforcement resulted in a torrent of event alerts being issued by the detection system. Soon the situation was one in which there began to be a lack of personnel who were ...
Current Internet Threats
... [email protected] [email protected] http://networks.depaul.edu/security/ ...
... [email protected] [email protected] http://networks.depaul.edu/security/ ...
A Hybrid QoS Routing Strategy for Suburban Ad
... may be covered with higher transmission energy Interference may increase as connectivity increases Overall network throughput may decrease ...
... may be covered with higher transmission energy Interference may increase as connectivity increases Overall network throughput may decrease ...
L046027479
... GPS. The positions of the two mobile nodes in Fig. 1 are (x1, y1) and (x2, y2) respectively. Using Fig. 1, the distance d between the two mobile nodes is calculated using (1). The angle θ is defined as shown in Fig. 3 and is calculated using (2). Smart antenna system SAS is a subsystem that contains ...
... GPS. The positions of the two mobile nodes in Fig. 1 are (x1, y1) and (x2, y2) respectively. Using Fig. 1, the distance d between the two mobile nodes is calculated using (1). The angle θ is defined as shown in Fig. 3 and is calculated using (2). Smart antenna system SAS is a subsystem that contains ...
Slide 1
... Number of hosts in the new subnet?? What is the range??? Broadcast address? Network ID of new subnet?? ...
... Number of hosts in the new subnet?? What is the range??? Broadcast address? Network ID of new subnet?? ...
4th Edition: Chapter 1
... Optical links from central office to the home Two competing optical technologies: Passive Optical network (PON) Active Optical Network (PAN) Much higher Internet rates; fiber also carries ...
... Optical links from central office to the home Two competing optical technologies: Passive Optical network (PON) Active Optical Network (PAN) Much higher Internet rates; fiber also carries ...
(LAN) INsecurity 2005 - NotBobTec Enterprises, Incorporeal
... This presentation was produced in the United States Air Force medical environment in the interest of academic freedom and the advancement of national defense-related concepts. The views expressed in this presentation and linked-to material are those of the author(s) of said material and do not refle ...
... This presentation was produced in the United States Air Force medical environment in the interest of academic freedom and the advancement of national defense-related concepts. The views expressed in this presentation and linked-to material are those of the author(s) of said material and do not refle ...
CCIE Security Written Exam Study Guide
... quality and value. Each book is authored with attention to detail, undergoing strenuous development that involves input from a variety of technical experts. For technical support on this book, please visit: www.securityie.com Readers’ feedback is a natural part of this process. If you have any comme ...
... quality and value. Each book is authored with attention to detail, undergoing strenuous development that involves input from a variety of technical experts. For technical support on this book, please visit: www.securityie.com Readers’ feedback is a natural part of this process. If you have any comme ...
Network Infrastructure Security Good Practice Guide
... Agricultural Research (CGIAR). This guide forms part of the CGIAR-wide baseline ICT Security and Acceptable Use good practice set. The target audience for the good practice guides are all centers affiliated with CGIAR, and in particular, the IT teams within each center. The good practice set does no ...
... Agricultural Research (CGIAR). This guide forms part of the CGIAR-wide baseline ICT Security and Acceptable Use good practice set. The target audience for the good practice guides are all centers affiliated with CGIAR, and in particular, the IT teams within each center. The good practice set does no ...
IOSR Journal of Computer Engineering (IOSR-JCE)
... to the wired broadband access such as cable and DSL. It provides a convenient way to build a wireless metropolitan area network (WMN), which offers a broad range of high data rate applications, such as broadband Internet access, Voice over Internet Protocol (VoIP), Internet Protocol Television (IPTV ...
... to the wired broadband access such as cable and DSL. It provides a convenient way to build a wireless metropolitan area network (WMN), which offers a broad range of high data rate applications, such as broadband Internet access, Voice over Internet Protocol (VoIP), Internet Protocol Television (IPTV ...
Suman Bannerjee, U Wisconsin, “Wireless Virtualization of
... • More careful tuning needed for smaller time slices – Need chipset vendor support for very small times ...
... • More careful tuning needed for smaller time slices – Need chipset vendor support for very small times ...
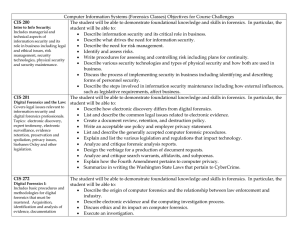
Computer Information Systems (Forensics Classes) Objectives for
... • Describe the function and layout of master boot records, the NTFS Master File Table, and partition tables including how partitions can be hidden and restored. • Identify and describe the Windows registry keys that would be examined relevant to a computer forensics investigation. • Demonstrate the ...
... • Describe the function and layout of master boot records, the NTFS Master File Table, and partition tables including how partitions can be hidden and restored. • Identify and describe the Windows registry keys that would be examined relevant to a computer forensics investigation. • Demonstrate the ...
Three Challenges in Reliable Data Transport over Heterogeneous
... (I.e. over TCP/IP) layer set of services but below the application environment (i.e., below application-level APIs) Def 2: a reusable, expandable set of services and functions that are commonly needed by many applications to function well in a networked environment. ...
... (I.e. over TCP/IP) layer set of services but below the application environment (i.e., below application-level APIs) Def 2: a reusable, expandable set of services and functions that are commonly needed by many applications to function well in a networked environment. ...
Guide to Network Defense and Countermeasures
... • Revenge by disgruntled, current, or former employees might be the primary motivation • Some attackers break into accounts and networks for financial gain • Some attackers may steal proprietary information for their own use or for resale to other parties • E-mail is one of the most important servic ...
... • Revenge by disgruntled, current, or former employees might be the primary motivation • Some attackers break into accounts and networks for financial gain • Some attackers may steal proprietary information for their own use or for resale to other parties • E-mail is one of the most important servic ...
CS4514 Course Objectives
... collection of “autonomous” computers interconnected by a single technology. [LG&W] communications network ::a set of equipment and facilities that provide a service. ...
... collection of “autonomous” computers interconnected by a single technology. [LG&W] communications network ::a set of equipment and facilities that provide a service. ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.