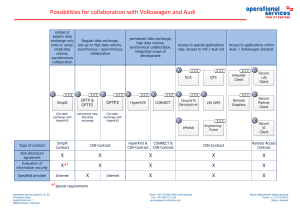
Possibilities for collaboration with Volkswagen
... the contractual relationship with Volkswagen. If users are absent from their workplaces, they have to remove the authorization objects (PKI card or similar) provided to them for performing their activities from the working environment and from the terminal and personally hold them in safe keeping. T ...
... the contractual relationship with Volkswagen. If users are absent from their workplaces, they have to remove the authorization objects (PKI card or similar) provided to them for performing their activities from the working environment and from the terminal and personally hold them in safe keeping. T ...
投影片 1 - NTUT
... based approach,” in Proc. Internet Society INET, Jul. 1998. 6. Sonia Fahmy and Minseok Kwon, “Characterizing Overlay Multicast Networks and Their Costs,” IEEE Transaction on Networking, Vol. 15, no. 2, April 2007 ...
... based approach,” in Proc. Internet Society INET, Jul. 1998. 6. Sonia Fahmy and Minseok Kwon, “Characterizing Overlay Multicast Networks and Their Costs,” IEEE Transaction on Networking, Vol. 15, no. 2, April 2007 ...
9. USABILITY AND USER INTERFACE DESIGN CONSIDERATIONS
... end-users. At first, the basic features need to be tested by a group of test persons in a PC based testbed, simulating the operation of a multimedia Walkman operation. Since we are interested in user behavior in the first place, we need not necessarily implement all the support functions. As a matte ...
... end-users. At first, the basic features need to be tested by a group of test persons in a PC based testbed, simulating the operation of a multimedia Walkman operation. Since we are interested in user behavior in the first place, we need not necessarily implement all the support functions. As a matte ...
Discovering Computers Fundamentals, 2012 Edition Your Interactive Guide
... Network Communications Standards • Bluetooth defines how two Bluetooth devices use shortrange radio waves to transmit data • UWB (ultra-wideband) specifies how two UWB devices use short-range radio waves to communicate at high speeds • IrDA transmits data wirelessly via infrared (IR) light waves • ...
... Network Communications Standards • Bluetooth defines how two Bluetooth devices use shortrange radio waves to transmit data • UWB (ultra-wideband) specifies how two UWB devices use short-range radio waves to communicate at high speeds • IrDA transmits data wirelessly via infrared (IR) light waves • ...
N - Hakan Tolgay
... PSH: push: like the Urgent flag, exists to ensure that the data is given the priority and is processed at the sending or receiving end. RST: reset: is used when a segment arrives that is not intended for the current connection. SYN: sync: is initialy sent when establishing the classical 3-way handsh ...
... PSH: push: like the Urgent flag, exists to ensure that the data is given the priority and is processed at the sending or receiving end. RST: reset: is used when a segment arrives that is not intended for the current connection. SYN: sync: is initialy sent when establishing the classical 3-way handsh ...
Security Assessment Questionnaire
... performed with or without detailed prior knowledge of the environment. When it is performed without prior knowledge additional steps will be taken to enumerate hosts and applications and to assess the ease with which any outsider could exploit publicly available information or social engineering to ...
... performed with or without detailed prior knowledge of the environment. When it is performed without prior knowledge additional steps will be taken to enumerate hosts and applications and to assess the ease with which any outsider could exploit publicly available information or social engineering to ...
Communications Devices
... Communications Devices • A communications device is any type of hardware capable of transmitting data, instructions, and information between a sending device and a receiving device • A dial-up modem converts signals between analog and digital ...
... Communications Devices • A communications device is any type of hardware capable of transmitting data, instructions, and information between a sending device and a receiving device • A dial-up modem converts signals between analog and digital ...
Attack and Surveillance Strategies for Selfish Primary User Emulator
... that the channel is declared to be occupied or to be free, respectively. The attacker is assumed to know nothing about the true status of primary signal during PUE attack. In data frame, if the state “busy” is declared, all CR users should not use the channel; any secondary transmission on that chan ...
... that the channel is declared to be occupied or to be free, respectively. The attacker is assumed to know nothing about the true status of primary signal during PUE attack. In data frame, if the state “busy” is declared, all CR users should not use the channel; any secondary transmission on that chan ...
Ethernet - GITAM University
... Given below is an example situation. Nodes Addresses A 0010 , B 0101 , C 1010 , D 1001 ---- Node C 1010 having higher priority gets to transmit. The problem with this protocol is that the nodes with higher address always wins. Hence this creates a priority which is highly unfair and hence undesirabl ...
... Given below is an example situation. Nodes Addresses A 0010 , B 0101 , C 1010 , D 1001 ---- Node C 1010 having higher priority gets to transmit. The problem with this protocol is that the nodes with higher address always wins. Hence this creates a priority which is highly unfair and hence undesirabl ...
incs775_lect5
... or a block of Class C network addresses can now be connected to the Internet with as little as a single IP address (many home networks are set up this way). – The more common arrangement is having machines that require true bidirectional and unfettered connectivity supplied with a 'real' IP address, ...
... or a block of Class C network addresses can now be connected to the Internet with as little as a single IP address (many home networks are set up this way). – The more common arrangement is having machines that require true bidirectional and unfettered connectivity supplied with a 'real' IP address, ...
CS 3 powerpoint/9781285845500_Ch10
... specifies how two wireless devices communicate over the air with each other • Bluetooth is a network protocol that defines how two Bluetooth devices use short-range radio waves to transmit data • UWB (ultra-wideband) is a network standard that specifies how two UWB devices use short-range radio wave ...
... specifies how two wireless devices communicate over the air with each other • Bluetooth is a network protocol that defines how two Bluetooth devices use short-range radio waves to transmit data • UWB (ultra-wideband) is a network standard that specifies how two UWB devices use short-range radio wave ...
Slide 1
... It breaks network communication into smaller, more manageable parts. It standardizes network components to allow multiple vendor development and support. It allows different types of network hardware and software to communicate with each other. It prevents changes in one layer from affecting ...
... It breaks network communication into smaller, more manageable parts. It standardizes network components to allow multiple vendor development and support. It allows different types of network hardware and software to communicate with each other. It prevents changes in one layer from affecting ...
Types of networks and network topologies File
... lines, cables, and air waves. A WAN often uses transmission facilities provided by common carriers, such as telephone companies. WAN technologies generally function at the lower three layers of the OSI reference model: the physical layer, the data link layer, and the network layer. Campus network A ...
... lines, cables, and air waves. A WAN often uses transmission facilities provided by common carriers, such as telephone companies. WAN technologies generally function at the lower three layers of the OSI reference model: the physical layer, the data link layer, and the network layer. Campus network A ...
2. FSF-1 Sea Fighter - Engineering Informatics Group
... systems that can monitor the structural behavior of ships during their operation at sea. This study seeks to reduce the cost and installation complexity of hull monitoring systems by introducing wireless sensors into their architectural designs. Wireless sensor networks also provide other advantages ...
... systems that can monitor the structural behavior of ships during their operation at sea. This study seeks to reduce the cost and installation complexity of hull monitoring systems by introducing wireless sensors into their architectural designs. Wireless sensor networks also provide other advantages ...
Introduction
... – Tires: Continental recalled Ford SUV tires in 2002 due to wire and vibration problems. – Software: Manufacturer not liable for security flaws. ...
... – Tires: Continental recalled Ford SUV tires in 2002 due to wire and vibration problems. – Software: Manufacturer not liable for security flaws. ...
Remi Ando, Tutomu Murase, Masato Oguchi
... Higher throughput flow can send more, and Lower throughput flow can send less The number of the terminals that becomes fair or unfair changes by buffer size of AP ...
... Higher throughput flow can send more, and Lower throughput flow can send less The number of the terminals that becomes fair or unfair changes by buffer size of AP ...
Computer Networks - E-Resources
... Given below is an example situation. Nodes Addresses A 0010 , B 0101 , C 1010 , D 1001 ---- Node C 1010 having higher priority gets to transmit. ...
... Given below is an example situation. Nodes Addresses A 0010 , B 0101 , C 1010 , D 1001 ---- Node C 1010 having higher priority gets to transmit. ...
Lecture 1
... Come “for free” inside many devices: routers, modems, wireless base stations etc. Alternate: a firewall is a host that mediates access to a network, allowing and disallowing certain type of access based on a configured security policy INFSCI 2935: Introduction to Computer Security ...
... Come “for free” inside many devices: routers, modems, wireless base stations etc. Alternate: a firewall is a host that mediates access to a network, allowing and disallowing certain type of access based on a configured security policy INFSCI 2935: Introduction to Computer Security ...
Module 7 Active Directory and Account Management
... and plan its structure before you implement it • Implement the least number of domains possible • Implement only one domain on most small networks • When an organization is planning to reorganize, use OUs to reflect the organization’s structure • Create only the number of OUs that are absolutely nec ...
... and plan its structure before you implement it • Implement the least number of domains possible • Implement only one domain on most small networks • When an organization is planning to reorganize, use OUs to reflect the organization’s structure • Create only the number of OUs that are absolutely nec ...
Chapter_08
... Describe how wireless phone networks are converging with digital data networks and the impact of that convergence Describe several ways to maximize effectiveness and minimize risks of online communication Describe how online social networks, wikis, and other new tools for creating online communit ...
... Describe how wireless phone networks are converging with digital data networks and the impact of that convergence Describe several ways to maximize effectiveness and minimize risks of online communication Describe how online social networks, wikis, and other new tools for creating online communit ...
Issue - GiaSpace
... Computer with ePHI does not have object level auditing on (11 pts) Issue: Object level auditing helps identify users who have accessed files and other system resources. Object level auditing may impose an unacceptable performance impact and should be considered for use on high risk computers or envi ...
... Computer with ePHI does not have object level auditing on (11 pts) Issue: Object level auditing helps identify users who have accessed files and other system resources. Object level auditing may impose an unacceptable performance impact and should be considered for use on high risk computers or envi ...
Redundant Network Architecture
... Designing the network with resiliency in mind Using technology to identify and eliminate single points of failure Having processes in place to reduce the risk of human error All of these elements are necessary, and all interact with each other ...
... Designing the network with resiliency in mind Using technology to identify and eliminate single points of failure Having processes in place to reduce the risk of human error All of these elements are necessary, and all interact with each other ...
MSI RG54SE Wireless 11g Broadband Router
... Complies with IEEE 802.11b/g standard for 2.4GHz Wireless LAN. Supports 64-bit and 128-bit WEP, WPA, WPA2 encryption/decryption function to protect the wireless data transmission. Supports IEEE 802.1x Authentication. Support Wi-Fi Protected Access Authentication with Radius and Pre-Shared Key mode. ...
... Complies with IEEE 802.11b/g standard for 2.4GHz Wireless LAN. Supports 64-bit and 128-bit WEP, WPA, WPA2 encryption/decryption function to protect the wireless data transmission. Supports IEEE 802.1x Authentication. Support Wi-Fi Protected Access Authentication with Radius and Pre-Shared Key mode. ...
21netsec
... Goal: overwhelm victim machine and deny service to its legitimate clients DoS often exploits networking protocols • Smurf: ICMP echo request to broadcast address with spoofed victim’s address as source • Ping of death: ICMP packets with payloads greater than 64K crash older versions of Windows • S ...
... Goal: overwhelm victim machine and deny service to its legitimate clients DoS often exploits networking protocols • Smurf: ICMP echo request to broadcast address with spoofed victim’s address as source • Ping of death: ICMP packets with payloads greater than 64K crash older versions of Windows • S ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.