Microsoft.Realtests.70-642.v2014-01
... Your network contains an Active Directory domain named contoso.com. The domain contains two Active Directory sites named Site1 and Site2. You have a domain-based Distributed File System (DFS) namespace named \\contoso.com\public that has a single namespace server located in Site1. You install anoth ...
... Your network contains an Active Directory domain named contoso.com. The domain contains two Active Directory sites named Site1 and Site2. You have a domain-based Distributed File System (DFS) namespace named \\contoso.com\public that has a single namespace server located in Site1. You install anoth ...
Chapter_11_Final
... Using PXE • The Pre-boot Execution Environment (PXE) is a feature built into many network interface adapters that enables them to connect to a DHCP server over the network and obtain TCP/IP client settings, even when the computer has no operating system. • DHCP can also supply the workstation with ...
... Using PXE • The Pre-boot Execution Environment (PXE) is a feature built into many network interface adapters that enables them to connect to a DHCP server over the network and obtain TCP/IP client settings, even when the computer has no operating system. • DHCP can also supply the workstation with ...
BROCADE NETIRON XMR 4000, 8000 16000, 32000
... routers feature highly scalable inbound and outbound ACLs, which allow operators to implement IPv4, IPv6, and Layer 2 security policies. These policies can be applied permanently or on demand without impacting normal operations. Receive ACLs further harden platform and infrastructure security, allow ...
... routers feature highly scalable inbound and outbound ACLs, which allow operators to implement IPv4, IPv6, and Layer 2 security policies. These policies can be applied permanently or on demand without impacting normal operations. Receive ACLs further harden platform and infrastructure security, allow ...
ARMOR Z1 User`s Guide
... 12.4 LAN IP Screen ..............................................................................................................................102 ...
... 12.4 LAN IP Screen ..............................................................................................................................102 ...
Advanced Routing - Fortinet Document Library
... Troubleshooting IS-IS .......................................................................................... 185 Routing loops................................................................................................. 185 Split horizon and Poison reverse updates ........................... ...
... Troubleshooting IS-IS .......................................................................................... 185 Routing loops................................................................................................. 185 Split horizon and Poison reverse updates ........................... ...
Cisco Catalyst 3550 Series Switches for Metro Access
... Protocol (BGP); Routing Information Protocol (RIP) and RIP v2; Protocol-Independent Multicast (PIM); and hardware-based IGMP snooping for multicast applications. For voice over IP (VoIP), the Cisco Catalyst 3550 Series supports Auxiliary VLAN. Together with the superior QoS and rate-limiting feature ...
... Protocol (BGP); Routing Information Protocol (RIP) and RIP v2; Protocol-Independent Multicast (PIM); and hardware-based IGMP snooping for multicast applications. For voice over IP (VoIP), the Cisco Catalyst 3550 Series supports Auxiliary VLAN. Together with the superior QoS and rate-limiting feature ...
Communications Server for z/OS V1R2 TCP/IP
... This edition applies to Version 1, Release 2 of Communications Server for z/OS. Comments may be addressed to: IBM Corporation, International Technical Support Organization Dept. HZ8 Building 662 P.O. Box 12195 Research Triangle Park, NC 27709-2195 When you send information to IBM, you grant IBM a no ...
... This edition applies to Version 1, Release 2 of Communications Server for z/OS. Comments may be addressed to: IBM Corporation, International Technical Support Organization Dept. HZ8 Building 662 P.O. Box 12195 Research Triangle Park, NC 27709-2195 When you send information to IBM, you grant IBM a no ...
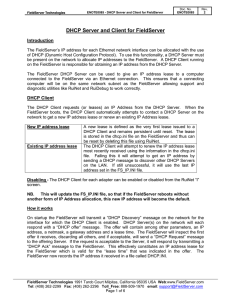
DHCP Server and Client for FieldServer
... The FieldServer DHCP Server is enabled by default on both Ethernet adapters* and will be active after restarting the FieldServer. The DHCP Server has the same IP address as the adapter it is operating on. The FieldServer probes the Ethernet network for other DHCP Servers every 3 minutes and will dis ...
... The FieldServer DHCP Server is enabled by default on both Ethernet adapters* and will be active after restarting the FieldServer. The DHCP Server has the same IP address as the adapter it is operating on. The FieldServer probes the Ethernet network for other DHCP Servers every 3 minutes and will dis ...
On Modern DNS Behavior and Properties
... The connections from each house come together in a switch. We have a packet-level monitor that receives all traffic via a mirroring port on the switch. The CCZ network is atypical in terms of the capacity afforded to users. However, in a companion study [21] we find that the usage patterns are fairl ...
... The connections from each house come together in a switch. We have a packet-level monitor that receives all traffic via a mirroring port on the switch. The CCZ network is atypical in terms of the capacity afforded to users. However, in a companion study [21] we find that the usage patterns are fairl ...
Introduction to Dynamic Routing Protocols
... is important for a network professional to understand the concepts and operations of all the different routing protocols. A network professional must be able to make an informed decision regarding when to use a dynamic routing protocol and which routing protocol is the best choice for a particular e ...
... is important for a network professional to understand the concepts and operations of all the different routing protocols. A network professional must be able to make an informed decision regarding when to use a dynamic routing protocol and which routing protocol is the best choice for a particular e ...
On Modern DNS Behavior and Properties
... The connections from each house come together in a switch. We have a packet-level monitor that receives all traffic via a mirroring port on the switch. The CCZ network is atypical in terms of the capacity afforded to users. However, in a companion study [21] we find that the usage patterns are fairl ...
... The connections from each house come together in a switch. We have a packet-level monitor that receives all traffic via a mirroring port on the switch. The CCZ network is atypical in terms of the capacity afforded to users. However, in a companion study [21] we find that the usage patterns are fairl ...
Layer 2 WAN Technology Design Guide - August 2014
... Service providers implement these Ethernet services by using a variety of methods. MPLS networks support both Ethernet over MPLS (EoMPLS) and Virtual Private LAN Service (VPLS). You can use other network technologies, such as Ethernet switches in various topologies, to provide Ethernet Layer 2 WAN ...
... Service providers implement these Ethernet services by using a variety of methods. MPLS networks support both Ethernet over MPLS (EoMPLS) and Virtual Private LAN Service (VPLS). You can use other network technologies, such as Ethernet switches in various topologies, to provide Ethernet Layer 2 WAN ...
The OAM Jigsaw Puzzle
... software flexibility, while achieving guaranteed high performance. The OAM Virtual Machine (firmware-based) can be seen by the OAM application as hardware, while also having all the flexibility of software. The OAM-VM co-exists transparently with existing application software, with negligible impact ...
... software flexibility, while achieving guaranteed high performance. The OAM Virtual Machine (firmware-based) can be seen by the OAM application as hardware, while also having all the flexibility of software. The OAM-VM co-exists transparently with existing application software, with negligible impact ...
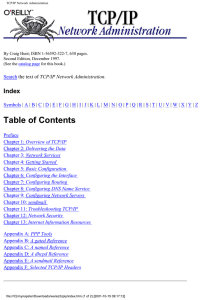
TCP/IP Network Administration - U
... ABORT keyword : A.3. chat Abstract Syntax Notation One (ASN.1) : 11.9. Simple Network Management Protocol access control : 12.5. Access Control levels of : 9.1.2.1. The share command services to place under, listed : 12.5.1. wrapper software for : 12.5. Access Control ACKD command, in POP : 3.4.2. P ...
... ABORT keyword : A.3. chat Abstract Syntax Notation One (ASN.1) : 11.9. Simple Network Management Protocol access control : 12.5. Access Control levels of : 9.1.2.1. The share command services to place under, listed : 12.5.1. wrapper software for : 12.5. Access Control ACKD command, in POP : 3.4.2. P ...
International Technical Support Organization Asynchronous
... When you send information to IBM, you grant IBM a non-exclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. Copyright International Business Machines Corporation 1995. All rights reserved. Note to U.S. Government Users — Do ...
... When you send information to IBM, you grant IBM a non-exclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. Copyright International Business Machines Corporation 1995. All rights reserved. Note to U.S. Government Users — Do ...
Access and Communication Servers Release Notes for Cisco IOS
... Next Hop Resolution Protocol (NHRP)—Access servers and hosts can use NHRP to discover the addresses of other access servers and hosts connected to a nonbroadcast, multiaccess (NBMA) network. NHRP provides an ARP-like solution whereby systems attached to an NBMA network can dynamically learn the addr ...
... Next Hop Resolution Protocol (NHRP)—Access servers and hosts can use NHRP to discover the addresses of other access servers and hosts connected to a nonbroadcast, multiaccess (NBMA) network. NHRP provides an ARP-like solution whereby systems attached to an NBMA network can dynamically learn the addr ...
Microsoft Windows 2000 Network Infrastructure
... The DHCP server can be configured to always assign the same IP address to the same DHCP client ...
... The DHCP server can be configured to always assign the same IP address to the same DHCP client ...
12.4 was released in May of 2005
... Access, and Service Provider Aggregation networks • Provides a comprehensive portfolio of Cisco technologies, including the leading-edge functionality and hardware introduced in Release 12.3T ...
... Access, and Service Provider Aggregation networks • Provides a comprehensive portfolio of Cisco technologies, including the leading-edge functionality and hardware introduced in Release 12.3T ...
Network Working Group G. Bernstein Request for
... over heterogeneous equipment. Otherwise, the process can take days. Developing these tools for each new piece of equipment and each vendor is a significant burden on the service provider. A standardized interface for provisioning, such as GMPLS signaling, could significantly reduce or eliminate this ...
... over heterogeneous equipment. Otherwise, the process can take days. Developing these tools for each new piece of equipment and each vendor is a significant burden on the service provider. A standardized interface for provisioning, such as GMPLS signaling, could significantly reduce or eliminate this ...
MIS 5211.001 Week 5 Site:
... Trace – Use tools like traceroute and/or tracert to map network Port Scanning – Checking for open TCP or UDP ports Fingerprinting – Determine operating system Version Scanning – Finding versions of services and protocols Vulnerability Scanning MIS 5211.001 ...
... Trace – Use tools like traceroute and/or tracert to map network Port Scanning – Checking for open TCP or UDP ports Fingerprinting – Determine operating system Version Scanning – Finding versions of services and protocols Vulnerability Scanning MIS 5211.001 ...
Cisco WRVS4400N Wireless-N Gigabit Security Router
... also use IP based ACL to limit traffic to a specific source, destination and protocol. NAPT allows users to open specific TCP/UDP port numbers to the Internet to provide limited service while minimizing harmful traffic at the same time. The Virtual Private Network (VPN) capability is another securit ...
... also use IP based ACL to limit traffic to a specific source, destination and protocol. NAPT allows users to open specific TCP/UDP port numbers to the Internet to provide limited service while minimizing harmful traffic at the same time. The Virtual Private Network (VPN) capability is another securit ...
D11 - State of Interoperability
... During our work on tools, standards and interoperability we found that there exists a huge amount of tools in that area. We identified more than 350! Many of these have been the result of research within universities and national research organisations. Most of those tools are freely available inclu ...
... During our work on tools, standards and interoperability we found that there exists a huge amount of tools in that area. We identified more than 350! Many of these have been the result of research within universities and national research organisations. Most of those tools are freely available inclu ...
The Design and Implementation of a Next Generation Venugopalan Ramasubramanian
... increases in malicious behavior, explosion in client population, and the need for fast reconfiguration pose difficult problems. The existing DNS architecture is fundamentally unsuitable for addressing these issues. The foremost problem with DNS is that it is susceptible to denial of service (DoS) at ...
... increases in malicious behavior, explosion in client population, and the need for fast reconfiguration pose difficult problems. The existing DNS architecture is fundamentally unsuitable for addressing these issues. The foremost problem with DNS is that it is susceptible to denial of service (DoS) at ...
Supporting Differentiated Service Classes: Queue Scheduling
... different queue scheduling disciplines, each attempting to find the correct balance between complexity, control, and fairness. The queue scheduling disciplines supported by router vendors are implementation-specific, which means that there are no real industry standards. However, a vendor sometimes ...
... different queue scheduling disciplines, each attempting to find the correct balance between complexity, control, and fairness. The queue scheduling disciplines supported by router vendors are implementation-specific, which means that there are no real industry standards. However, a vendor sometimes ...