Cradlepoint 4G LTE Parallel Networking
... Limit risk: If an employee device or third-party network is compromised, there is no risk that attackers could pivot to other servers and networks, including those that hold sensitive data. Reduce soft costs: Parallel networks often reduce an enterprise’s soft costs, including the need for complex n ...
... Limit risk: If an employee device or third-party network is compromised, there is no risk that attackers could pivot to other servers and networks, including those that hold sensitive data. Reduce soft costs: Parallel networks often reduce an enterprise’s soft costs, including the need for complex n ...
1.7 The history of Computer Networking and the Internet
... Networks of networks DARPA (Defence ARPA) funded the connection of networks Networks of networks also called inernetting ...
... Networks of networks DARPA (Defence ARPA) funded the connection of networks Networks of networks also called inernetting ...
Chapter 13
... Windows security systems and allows a stranger to witness and record another person’s every mouse click and keystroke on the monitor as it occurs. • For the spy, it looks as if a ghost is moving the mouse and typing in e-mail on ...
... Windows security systems and allows a stranger to witness and record another person’s every mouse click and keystroke on the monitor as it occurs. • For the spy, it looks as if a ghost is moving the mouse and typing in e-mail on ...
CCENT Review
... What is the function of the router in this topology? Determines the path to send the message to get to a destination network. Each port, or interface, on a router connects to a different local network. Every router contains a table of all locally-connected networks and the interfaces that connect t ...
... What is the function of the router in this topology? Determines the path to send the message to get to a destination network. Each port, or interface, on a router connects to a different local network. Every router contains a table of all locally-connected networks and the interfaces that connect t ...
Slides - Duke Computer Science
... An Architecture Question to Study • How should the functionality that controls a network be divided up? • Important: everyone hates net outages • Practical: solutions can be implemented without changing IP or end-hosts • Relevant: trends toward separating decisionmaking from forwarding • Unsolved: ...
... An Architecture Question to Study • How should the functionality that controls a network be divided up? • Important: everyone hates net outages • Practical: solutions can be implemented without changing IP or end-hosts • Relevant: trends toward separating decisionmaking from forwarding • Unsolved: ...
A Preparing And Networking Of Virtual Network - Eagle
... vulnerabilities of desktop Operating System will help in the successful completion of this project. Section 1 Port Scanning: Port scanning is one of the most popular techniques used by hackers to find loop holes in the services they can use to attack. All of the computer machines that are connected ...
... vulnerabilities of desktop Operating System will help in the successful completion of this project. Section 1 Port Scanning: Port scanning is one of the most popular techniques used by hackers to find loop holes in the services they can use to attack. All of the computer machines that are connected ...
Understand Computer Network V
... Protocols at the Network Layer • TCP and UDP communicate with the Network layer, which is sometimes called the Internet layer. • Some of the other supporting protocols include ARP (Address Resolution Protocol), responsible for locating a host on a LAN; RARP (Reverse Address Resolution Protocol), re ...
... Protocols at the Network Layer • TCP and UDP communicate with the Network layer, which is sometimes called the Internet layer. • Some of the other supporting protocols include ARP (Address Resolution Protocol), responsible for locating a host on a LAN; RARP (Reverse Address Resolution Protocol), re ...
cut-through
... A network administrator has a multifloor LAN to monitor and maintain. Through careful monitoring, the administrator has noticed a large amount of broadcast traffic slowing the network. Which device would you use to best solve this problem? • A router, or as they say in Great Britain, a rooter. ...
... A network administrator has a multifloor LAN to monitor and maintain. Through careful monitoring, the administrator has noticed a large amount of broadcast traffic slowing the network. Which device would you use to best solve this problem? • A router, or as they say in Great Britain, a rooter. ...
Computer Networks
... • Extranet is a network or internetwork that is limited in scope to a single organization or entity but which also has limited connections to the networks of one or more other usually, but not necessarily, trusted organizations or entities. – Example: a company's customers may be given access to som ...
... • Extranet is a network or internetwork that is limited in scope to a single organization or entity but which also has limited connections to the networks of one or more other usually, but not necessarily, trusted organizations or entities. – Example: a company's customers may be given access to som ...
Dark Matter and Dark Energy - Hitoshi Murayama Home Page
... • Fiber-optic backbone, machines attached through switches • Switches are smarter network device • Party where everybody talks over cell phone with head set • No “packet collisions,” a “sniffer” cannot steal passwords • Users allowed to install hubs, switches, routers for in-room network ...
... • Fiber-optic backbone, machines attached through switches • Switches are smarter network device • Party where everybody talks over cell phone with head set • No “packet collisions,” a “sniffer” cannot steal passwords • Users allowed to install hubs, switches, routers for in-room network ...
Prof. Chi ZHANG Transport Mechanisms for High
... Packet loss may be caused by random wireless bit errors ACK loss can be judged as packet loss over asymmetric path. Network feedback is received only when congestive drops occur No indication of the level of contention / bandwidth under-utilization Transmission control parameters are static rather t ...
... Packet loss may be caused by random wireless bit errors ACK loss can be judged as packet loss over asymmetric path. Network feedback is received only when congestive drops occur No indication of the level of contention / bandwidth under-utilization Transmission control parameters are static rather t ...
ch._1_-_guided_reading
... 10. ___________________ are people who break into computer systems to _________________ services and ______________________ information such as credit card numbers, ____________________, test data, and even ________________________ security information. They can also __________________ data or creat ...
... 10. ___________________ are people who break into computer systems to _________________ services and ______________________ information such as credit card numbers, ____________________, test data, and even ________________________ security information. They can also __________________ data or creat ...
Unit E - Home - KSU Faculty Member websites
... or a file broken into small, equal size pieces Contains ...
... or a file broken into small, equal size pieces Contains ...
Logical Addressing
... possible. • The NAT protocol achieves this by, in the limiting case, allowing an entire organization to be represented to the Internet by one IP address. • Certain IP address blocks have been set aside as private networks, where anyone can use them. • A NAT system has one device connected to the int ...
... possible. • The NAT protocol achieves this by, in the limiting case, allowing an entire organization to be represented to the Internet by one IP address. • Certain IP address blocks have been set aside as private networks, where anyone can use them. • A NAT system has one device connected to the int ...
Scaling the Network: The Internet Protocol Networking CS 3470, Section 1
... An arbitrary collection of networks interconnected to provide some sort of host-host packet delivery service ...
... An arbitrary collection of networks interconnected to provide some sort of host-host packet delivery service ...
Slides for Chapter 3: Networking and Internetworking
... differ. Encryption is also performed in this layer, if required. At this level reliability and adaptation are performed, such as detection of failures and automatic recovery. This is the lowest level at which messages (rather than packets) are handled. Messages are addressed to communication ports a ...
... differ. Encryption is also performed in this layer, if required. At this level reliability and adaptation are performed, such as detection of failures and automatic recovery. This is the lowest level at which messages (rather than packets) are handled. Messages are addressed to communication ports a ...
Telecommunications and Networking - University of Baltimore Home
... – "a group of interconnected computers, workstations, or computer devices (such as printers and data storage systems).” ...
... – "a group of interconnected computers, workstations, or computer devices (such as printers and data storage systems).” ...
WiFi Security: Keeping Your Information Private and Safe
... SSID is a case sensitive, 32 alphanumeric character unique identifier attached to the header of packets sent over a wireless local-area network (WLAN) that acts as a password when a mobile device tries to connect to the basic service set (BSS) -- a component of the IEEE 802.11 WLAN architecture. (Th ...
... SSID is a case sensitive, 32 alphanumeric character unique identifier attached to the header of packets sent over a wireless local-area network (WLAN) that acts as a password when a mobile device tries to connect to the basic service set (BSS) -- a component of the IEEE 802.11 WLAN architecture. (Th ...
Assignment 3 - Network Components
... A network bridge is a network device that connects multiple network segments or two segments of the same LAN that use the same protocol, such as Ethernet or Token-Ring. Bridges only forward packets between networks that are destined for the other network. Bridges are important in some networks becau ...
... A network bridge is a network device that connects multiple network segments or two segments of the same LAN that use the same protocol, such as Ethernet or Token-Ring. Bridges only forward packets between networks that are destined for the other network. Bridges are important in some networks becau ...
Acceptable Use Policy (AUP)
... Students are expected to use moral and ethical guidelines in making appropriate decisions regarding network use. Use of the district network is not a right, but a privilege, and inappropriate use will result in cancellation of that privilege. School and district administrators will decide what is in ...
... Students are expected to use moral and ethical guidelines in making appropriate decisions regarding network use. Use of the district network is not a right, but a privilege, and inappropriate use will result in cancellation of that privilege. School and district administrators will decide what is in ...
MIS 5211.001 Week 2 Site: 1
... Works to keep localized traffic inside and only passes traffic intended for targets outside the local network Boundary between “Routable” and “NonRoutable” IP addressing ...
... Works to keep localized traffic inside and only passes traffic intended for targets outside the local network Boundary between “Routable” and “NonRoutable” IP addressing ...
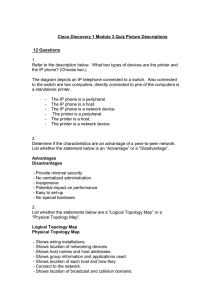
Cisco Discovery 1 Module 03 Quiz Picture Descriptions
... Location and length of cable runs Physical location of all networking devices Location and size of broadcast and collision domains Hardware configuration of end devices such as hosts and services. ...
... Location and length of cable runs Physical location of all networking devices Location and size of broadcast and collision domains Hardware configuration of end devices such as hosts and services. ...
Class_05
... • Provides communications sessions between computers • Establishes sessions by polling destination computer’s port address • TCP tells host computer how much data the destination computer can receive • Establishes a connection ...
... • Provides communications sessions between computers • Establishes sessions by polling destination computer’s port address • TCP tells host computer how much data the destination computer can receive • Establishes a connection ...
Networking
... Unguided Media • Physically not connected using wired connection. use wireless technology to communicate with each other. • Ex: • wi-fi • Infra red ...
... Unguided Media • Physically not connected using wired connection. use wireless technology to communicate with each other. • Ex: • wi-fi • Infra red ...
download
... LAN consists of the following components: – LAN file server is a repository of various software and data files for the network – Nodes are the client machines on the LAN – Wired or wireless communication media that connects the devices ...
... LAN consists of the following components: – LAN file server is a repository of various software and data files for the network – Nodes are the client machines on the LAN – Wired or wireless communication media that connects the devices ...