Computer Networks & The Internet
... Data transmission modes • There are 3 modes of transmitting data from one point to another: – Simplex: communication is possible only in one direction. The connected devices in such a system are send-only or receive-only. Example, a terminal (send-only) and printer (receive-only). This type of comm ...
... Data transmission modes • There are 3 modes of transmitting data from one point to another: – Simplex: communication is possible only in one direction. The connected devices in such a system are send-only or receive-only. Example, a terminal (send-only) and printer (receive-only). This type of comm ...
Assignment 4
... 9. What is the broadcast address for each subnet? 10. State the IP address for each router interface 2. Consider the given following network information; please state the Class above IP address falls into and calculate the subnet mask for the District based on the total ...
... 9. What is the broadcast address for each subnet? 10. State the IP address for each router interface 2. Consider the given following network information; please state the Class above IP address falls into and calculate the subnet mask for the District based on the total ...
Taxonomy of Computer Security Incidents
... • Operating System, including version, patches, etc. • System Function (e.g., DNS/web server, workstation, etc.) • Antivirus software installed, including version, and latest updates • Location of the system(s) involved in the incident (e.g. Clemson) • Method used to identify the incident (e.g., IDS ...
... • Operating System, including version, patches, etc. • System Function (e.g., DNS/web server, workstation, etc.) • Antivirus software installed, including version, and latest updates • Location of the system(s) involved in the incident (e.g. Clemson) • Method used to identify the incident (e.g., IDS ...
CS 494/594 Computer and Network Security - UTK-EECS
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
CS 494/594 Computer and Network Security - UTK-EECS
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
Network Devices
... the data link layer (layer 2) of the OSI model. • Bridges are similar to repeaters or network hubs, devices that connect network segments at the physical layer • However a bridge works by using bridging where traffic from one network is managed rather than simply rebroadcast to adjacent network segm ...
... the data link layer (layer 2) of the OSI model. • Bridges are similar to repeaters or network hubs, devices that connect network segments at the physical layer • However a bridge works by using bridging where traffic from one network is managed rather than simply rebroadcast to adjacent network segm ...
malay - Shalby Hospitals
... Assisting in the planning and implementation of additions, deletions and major modifications to the supporting location infrastructure Interacting with internal clients at all levels to resolve IT-related issues and provides answers in a timely manner Proposing improvements in the operations a ...
... Assisting in the planning and implementation of additions, deletions and major modifications to the supporting location infrastructure Interacting with internal clients at all levels to resolve IT-related issues and provides answers in a timely manner Proposing improvements in the operations a ...
Information Architecture and Technologies that Support Health Care
... network come together Bridge—connects neworks at the data link layer; networks with the same protocols Router—operates at the network layer; help determine the destination of data ...
... network come together Bridge—connects neworks at the data link layer; networks with the same protocols Router—operates at the network layer; help determine the destination of data ...
Convergence Technology Chapter Objectives
... How routers connect dissimilar networks Explain how to connect LAN or WANs via a modem What components are necessary for access and carrier network connectivity ...
... How routers connect dissimilar networks Explain how to connect LAN or WANs via a modem What components are necessary for access and carrier network connectivity ...
WB_intro
... packet size much more efficient use of facilities several refinements; fast packet switching (ATM) is culmination ...
... packet size much more efficient use of facilities several refinements; fast packet switching (ATM) is culmination ...
Topic 2: Lesson 3 Intro to Firewalls
... firewall sets up rule set, verifies packets with header information what is inside a packet header: ...
... firewall sets up rule set, verifies packets with header information what is inside a packet header: ...
Centre for Defence Communications and Information Networking
... The Centre for Defence Communications and Information Networking (CDCIN) at the University of Adelaide is Australia’s leading university based concentration of defence network analysis capability. CDCIN focusses on the modelling, measurement and management of networked systems, enhancing the robustn ...
... The Centre for Defence Communications and Information Networking (CDCIN) at the University of Adelaide is Australia’s leading university based concentration of defence network analysis capability. CDCIN focusses on the modelling, measurement and management of networked systems, enhancing the robustn ...
CPSC 463 Networks and Distributed Processing
... FTAM ~ FTP File Transfer, Access & Manipulation VTS ~ TELNET Virtual Terminal Service JTM ~ ??? Job Transfer & Manipulation {maybe rsh, RPC?} MHS ~ SMTP Message Handling System (X.400) ...
... FTAM ~ FTP File Transfer, Access & Manipulation VTS ~ TELNET Virtual Terminal Service JTM ~ ??? Job Transfer & Manipulation {maybe rsh, RPC?} MHS ~ SMTP Message Handling System (X.400) ...
NET331_Ch1
... a dedicated link between two devices. Entire capacity of the link is reserved for transmission between those two devices. Example: the connection between the remote control and the ...
... a dedicated link between two devices. Entire capacity of the link is reserved for transmission between those two devices. Example: the connection between the remote control and the ...
Lecture Notes - Computer Science & Engineering
... IP address is a globally unique or private number associated with a host network interface Every system which will send packets directly out across the Internet must have a unique IP address IP addresses are based on where the hosts are connected IP addresses are controlled by a single organ ...
... IP address is a globally unique or private number associated with a host network interface Every system which will send packets directly out across the Internet must have a unique IP address IP addresses are based on where the hosts are connected IP addresses are controlled by a single organ ...
Service Set Identification (SSID)
... objects like files – Synchronization Traffic is used to synchronize data between PDAs and PCs ...
... objects like files – Synchronization Traffic is used to synchronize data between PDAs and PCs ...
Network Security: Intrusion Detection and Protection
... As we employ heavier rules in the IDS we can detect more variances of intrusion attempts but more false positives are probable. If we employ lighter rules, we have less false positives but the system is easier to ...
... As we employ heavier rules in the IDS we can detect more variances of intrusion attempts but more false positives are probable. If we employ lighter rules, we have less false positives but the system is easier to ...
Information Technology and Protection Considerations for E
... unnecessary, and it increases the likelihood someone will try to log in to your home network. Fortunately, most Wi-Fi access points allow the SSID broadcast feature to be disabled by the network administrator. (Network administrator refers to the person setting up the wireless router. In the case of ...
... unnecessary, and it increases the likelihood someone will try to log in to your home network. Fortunately, most Wi-Fi access points allow the SSID broadcast feature to be disabled by the network administrator. (Network administrator refers to the person setting up the wireless router. In the case of ...
IEEE International Conference on Network Protocols
... submission. Papers cannot be previously published nor under review by another conference or journal. Papers containing plagiarized material will be subject to the IEEE plagiarism policy and will be rejected without review. Topics of interest include, but are not limited to: All aspects of network ...
... submission. Papers cannot be previously published nor under review by another conference or journal. Papers containing plagiarized material will be subject to the IEEE plagiarism policy and will be rejected without review. Topics of interest include, but are not limited to: All aspects of network ...
Chapter 13
... – Be authenticated by the server. – Asked for their username and password as if they were on the local network. ...
... – Be authenticated by the server. – Asked for their username and password as if they were on the local network. ...
security
... Hacking - Cracking Passwords • Cracking Passwords – remote access • Dictionary attack is trying to determine a decryption key or pass-phrase by searching a large number of possibilities • Remote access to a user’s account allows files to be copied or corrupted. • Hacking used to be a game – now it ...
... Hacking - Cracking Passwords • Cracking Passwords – remote access • Dictionary attack is trying to determine a decryption key or pass-phrase by searching a large number of possibilities • Remote access to a user’s account allows files to be copied or corrupted. • Hacking used to be a game – now it ...
NAME: NWOSU JENNIFER CHIMENKA COLLEGE: MEDICINE AND
... by computer experts, engineers, scientists, and librarians. There was nothing friendly about it. There were no home or office personal computers in those days, and anyone who used it, whether a computer professional or an engineer or scientist or librarian, had to learn to use a very complex system. ...
... by computer experts, engineers, scientists, and librarians. There was nothing friendly about it. There were no home or office personal computers in those days, and anyone who used it, whether a computer professional or an engineer or scientist or librarian, had to learn to use a very complex system. ...
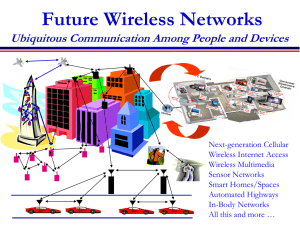
Broadcast Channels
... •Antennas can be used for multiplexing, diversity, or interference cancellation •M-fold possible capacity increase via multiplexing •M2 possible diversity gain •Can cancel M-1 interferers •Errors occur due to fading, interference, and delay • What metric should be optimized? Image “quality” ...
... •Antennas can be used for multiplexing, diversity, or interference cancellation •M-fold possible capacity increase via multiplexing •M2 possible diversity gain •Can cancel M-1 interferers •Errors occur due to fading, interference, and delay • What metric should be optimized? Image “quality” ...