Application Note: How to Evaluate WirelessHART Network and Device Performance
... fraction of time spent listening versus sleeping is called the join duty cycle. The join duty cycle is one-byte field that can be set from 0 (0.2%) to 255 (almost 100%) - the default is 10% or a setting of 26. Lower settings result in longer search times at lower average current, while higher settin ...
... fraction of time spent listening versus sleeping is called the join duty cycle. The join duty cycle is one-byte field that can be set from 0 (0.2%) to 255 (almost 100%) - the default is 10% or a setting of 26. Lower settings result in longer search times at lower average current, while higher settin ...
Manage Cisco IOS Devices
... Explain How to Disable Unused Cisco Router Network Services and Interfaces Explain how to secure a router with the command-line interface (CLI) auto secure command ...
... Explain How to Disable Unused Cisco Router Network Services and Interfaces Explain how to secure a router with the command-line interface (CLI) auto secure command ...
How to Deploy a NextGen F-Series Vx using Barracuda F
... Hypervisor The OVA package uses a default configuration that may not be suitable for your deployment. If you want to use multiple network interfaces, a different type of network adapter, or a bigger size for the virtual disk, use Barracuda F-Series Install to create the custom configuration files that y ...
... Hypervisor The OVA package uses a default configuration that may not be suitable for your deployment. If you want to use multiple network interfaces, a different type of network adapter, or a bigger size for the virtual disk, use Barracuda F-Series Install to create the custom configuration files that y ...
Multicast Session Announcements on top of SSM
... time of the corresponding multicast forwarding states in the routers. Therefore, when an sdr tool sends out announcements, these announcements create a considerable amount of control traffic in the network. First, the active source information for the announcement originator site is communicated to ...
... time of the corresponding multicast forwarding states in the routers. Therefore, when an sdr tool sends out announcements, these announcements create a considerable amount of control traffic in the network. First, the active source information for the announcement originator site is communicated to ...
Elmustafa Sayed Ali Ahmed and Rashid A. Saeed
... can only communicate among themselves, using multihop wireless transmission and each node has a unique address since there is no external connectivity. However, there are some solutions which extend this architecture providing Internet access for ad-hoc nodes. This means that more than one node or a ...
... can only communicate among themselves, using multihop wireless transmission and each node has a unique address since there is no external connectivity. However, there are some solutions which extend this architecture providing Internet access for ad-hoc nodes. This means that more than one node or a ...
ex4-3-o-can
... status information about Frame Relay connections between the router (DTE) and the Frame Relay switch (DCE). • Every 10 seconds or so, the end device polls the network. • If the network does not respond with the requested information, the user device may consider the connection to be down. • When the ...
... status information about Frame Relay connections between the router (DTE) and the Frame Relay switch (DCE). • Every 10 seconds or so, the end device polls the network. • If the network does not respond with the requested information, the user device may consider the connection to be down. • When the ...
Tapestry: A Resilient Global-scale Overlay for Service Deployment
... or object replicas. DOLR virtualizes resources, since endpoints are named by opaque identifiers encoding nothing about physical location. Properly implemented, this virtualization enables message delivery to mobile or replicated endpoints in the presence of instability in the underlying infrastructu ...
... or object replicas. DOLR virtualizes resources, since endpoints are named by opaque identifiers encoding nothing about physical location. Properly implemented, this virtualization enables message delivery to mobile or replicated endpoints in the presence of instability in the underlying infrastructu ...
Troubleshooting - VPN
... The purchased products, services and features are stipulated by the contract made between Huawei and the customer. All or part of the products, services and features described in this document may not be within the purchase scope or the usage scope. Unless otherwise specified in the contract, all st ...
... The purchased products, services and features are stipulated by the contract made between Huawei and the customer. All or part of the products, services and features described in this document may not be within the purchase scope or the usage scope. Unless otherwise specified in the contract, all st ...
LoRa® ® FAQs
... other industries the definition of gateway and concentrator imply different components. 6.) How well does LoRa® handle Interference? The LoRa modem is capable of co‐channel GMSK rejection of up to 19.5 dB, or stated differently, it can receive signals 19.5dB below an interfering signal or the ...
... other industries the definition of gateway and concentrator imply different components. 6.) How well does LoRa® handle Interference? The LoRa modem is capable of co‐channel GMSK rejection of up to 19.5 dB, or stated differently, it can receive signals 19.5dB below an interfering signal or the ...
slides - Inria
... Router 1d determines from intra-AS routing info that its interface I is on the least cost path to 1a. ...
... Router 1d determines from intra-AS routing info that its interface I is on the least cost path to 1a. ...
Shrack: Description and Performance Evaluation of a Peer-to
... The system stimulates cooperation by learning and sharing new documents within a group of researchers having common interest, which is determined and controlled by peers that seek information. Peers that provide good sources of information can build their reputation and make themselves and their wor ...
... The system stimulates cooperation by learning and sharing new documents within a group of researchers having common interest, which is determined and controlled by peers that seek information. Peers that provide good sources of information can build their reputation and make themselves and their wor ...
Implementing IPv6 in a Production Network
... multicast address is delivered to every interface in a group. The IPv6 difference is that, instead of annoying every single host on the segment with broadcast blather. Only hosts who are members of the multicast group receive the multicast packets. IPv6 multicast is routable, and routers will not fo ...
... multicast address is delivered to every interface in a group. The IPv6 difference is that, instead of annoying every single host on the segment with broadcast blather. Only hosts who are members of the multicast group receive the multicast packets. IPv6 multicast is routable, and routers will not fo ...
Distance Vector Routing Protocols
... Routing Loops Preventing loops with holddown timers – Holddown timers allow a router to not accept any changes to a route for a specified period of time – Point of using holddown timers • Allows routing updates to propagate through network with the most current information ...
... Routing Loops Preventing loops with holddown timers – Holddown timers allow a router to not accept any changes to a route for a specified period of time – Point of using holddown timers • Allows routing updates to propagate through network with the most current information ...
Tema 1: Tecnologías LAN. - GRC
... LS packet dissemination Topology map at each node Route computation using Dijkstra’s algorithm ...
... LS packet dissemination Topology map at each node Route computation using Dijkstra’s algorithm ...
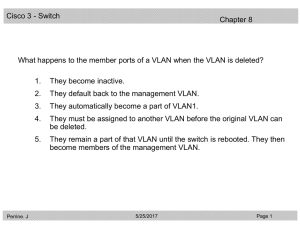
20088-2 CCNA3 3.1-08 Questions VLAN
... A network administrator has configured a switch with three VLANs: VLAN1, VLAN2, and VLAN3. Port 10 is to be assigned to VLAN3. Which of the following commands are needed to assign port 10 to VLAN3? (Choose three.) ...
... A network administrator has configured a switch with three VLANs: VLAN1, VLAN2, and VLAN3. Port 10 is to be assigned to VLAN3. Which of the following commands are needed to assign port 10 to VLAN3? (Choose three.) ...
discus - Cordis
... remote areas getting less effective coverage than more densely populated regions with reduced bandwidth capability and quality of service as a result. Nevertheless, even in populous areas with g ...
... remote areas getting less effective coverage than more densely populated regions with reduced bandwidth capability and quality of service as a result. Nevertheless, even in populous areas with g ...
What is an IP address?
... TCP/IP and UDP/IP Transport are most common over Ethernet ©2008 Opto 22 – All rights reserved. Contents of this document may not be used without the express written permission of Opto 22. ...
... TCP/IP and UDP/IP Transport are most common over Ethernet ©2008 Opto 22 – All rights reserved. Contents of this document may not be used without the express written permission of Opto 22. ...
Notes
... share channel efficiently and fairly at high load inefficient at low load: delay in channel access, 1/N bandwidth allocated even if only 1 active node! Random access MAC protocols efficient at low load: single node can fully utilize channel high load: collision overhead “taking turns” protoc ...
... share channel efficiently and fairly at high load inefficient at low load: delay in channel access, 1/N bandwidth allocated even if only 1 active node! Random access MAC protocols efficient at low load: single node can fully utilize channel high load: collision overhead “taking turns” protoc ...
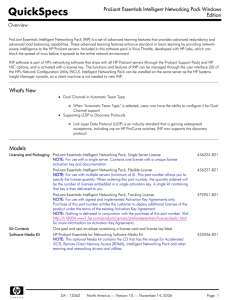
ProLiant Essentials Intelligent Networking Pack Windows Edition
... should not be used by the team based on "tested" connectivity with a network device called an Echo Node. Each teamed port tests connectivity to the Echo Node by transmitting a frame to the Echo Node and monitoring for a response. Active path can determine if teamed ports have become segregated onto ...
... should not be used by the team based on "tested" connectivity with a network device called an Echo Node. Each teamed port tests connectivity to the Echo Node by transmitting a frame to the Echo Node and monitoring for a response. Active path can determine if teamed ports have become segregated onto ...
U.S. Central Command - CENTCOM
... Another benefit related to security is that with the zero clients, no data is stored locally at the end point, (data-at-rest). Provisioning new desktop images is easier. Instead of taking a week per network, CENTCOM can now deploy new VMware View desktops across its entire infrastructure in about ei ...
... Another benefit related to security is that with the zero clients, no data is stored locally at the end point, (data-at-rest). Provisioning new desktop images is easier. Instead of taking a week per network, CENTCOM can now deploy new VMware View desktops across its entire infrastructure in about ei ...
High Availability WLANs Based on Software-Defined
... Recently, the software defined networking (SDN) has attracted a lot of interest. The main characteristics of SDN is to decouple the control and data planes of a network and provide the freedom of programmability to development more efficient network applications [1]. Furthermore, the SDN also result ...
... Recently, the software defined networking (SDN) has attracted a lot of interest. The main characteristics of SDN is to decouple the control and data planes of a network and provide the freedom of programmability to development more efficient network applications [1]. Furthermore, the SDN also result ...
EE579T-Class 4
... Curious Public Key Properties • The encryption function is one-way • The encryption process is fungible – Can encrypt with public key and decrypt with private key, and vice versa ...
... Curious Public Key Properties • The encryption function is one-way • The encryption process is fungible – Can encrypt with public key and decrypt with private key, and vice versa ...