PHysical laYer protocol
... • Bridges increase the latency (delay) in a network by 10-30%. • A bridge is considered a store-andforward device because it must receive the entire frame and compute the cyclic redundancy check (CRC) before forwarding can take place. • The time it takes to perform these tasks can slow network trans ...
... • Bridges increase the latency (delay) in a network by 10-30%. • A bridge is considered a store-andforward device because it must receive the entire frame and compute the cyclic redundancy check (CRC) before forwarding can take place. • The time it takes to perform these tasks can slow network trans ...
Routing Protocols
... • Dedicate part of a routers resources for protocol operation, including CPU time and network link bandwidth Times when static routing is more appropriate Presentation_ID ...
... • Dedicate part of a routers resources for protocol operation, including CPU time and network link bandwidth Times when static routing is more appropriate Presentation_ID ...
Performance Evaluation and Comparison of Facsimile Transmission
... one dimensional image compression of black and white images. The evolution of IP networks has led to the transmission of facsimile through the IP network. There are two methods for facsimile transmission using IP networks. This has been given by the International Telecommunication Union (ITU) recomm ...
... one dimensional image compression of black and white images. The evolution of IP networks has led to the transmission of facsimile through the IP network. There are two methods for facsimile transmission using IP networks. This has been given by the International Telecommunication Union (ITU) recomm ...
Business Roles and Architecture to realize MUSE
... Usage of unallocated resource is done only after requesting all relevant Border Nodes and getting confirmation, to fore come that multiple usage. If there is no confirmation from all relevant Border Nodes, then there will be a time-out and call request will be denied. MUSE Summer School July 2006 — ...
... Usage of unallocated resource is done only after requesting all relevant Border Nodes and getting confirmation, to fore come that multiple usage. If there is no confirmation from all relevant Border Nodes, then there will be a time-out and call request will be denied. MUSE Summer School July 2006 — ...
Engineering Wireless-based Software Systems and Applications
... To meet the increasing demand on various reliable wireless-based software application systems, engineers and students need to know how to engineer quality wireless-based application systems using a cost-effective approach. Since the first book on mobile computing was published in 1996, many books ha ...
... To meet the increasing demand on various reliable wireless-based software application systems, engineers and students need to know how to engineer quality wireless-based application systems using a cost-effective approach. Since the first book on mobile computing was published in 1996, many books ha ...
Peer
... •Using this protocol, peers can advertise their own resources, and discover the resources from other peers ...
... •Using this protocol, peers can advertise their own resources, and discover the resources from other peers ...
Network Analysis Module
... This figure shows Cisco Prime NAM’s role as a mediation layer tool—collecting and analyzing network data from a variety of sources and displaying the results on an integrated management and reporting console, for instance, NAM web GUI, and also providing data to Cisco Prime Infrastructure via repres ...
... This figure shows Cisco Prime NAM’s role as a mediation layer tool—collecting and analyzing network data from a variety of sources and displaying the results on an integrated management and reporting console, for instance, NAM web GUI, and also providing data to Cisco Prime Infrastructure via repres ...
TESI DOCTORAL Àlex Vallejo Blanxart
... It is true, a thesis is a very long and lonely journey, but not all the way. It would have been impossible to carry out this thesis without the collaboration of many people. Some of them just helped a bit at some crucial points, some have been around transversally, some we have never met in real lif ...
... It is true, a thesis is a very long and lonely journey, but not all the way. It would have been impossible to carry out this thesis without the collaboration of many people. Some of them just helped a bit at some crucial points, some have been around transversally, some we have never met in real lif ...
Description
... and meets the requirements for broadband communication. This section describes important radio access features and functions of LTE. For details about E-UTRAN NodeB (eNodeB) features related to eLTE2.1, see the feature list and feature description of the corresponding eRAN version. ...
... and meets the requirements for broadband communication. This section describes important radio access features and functions of LTE. For details about E-UTRAN NodeB (eNodeB) features related to eLTE2.1, see the feature list and feature description of the corresponding eRAN version. ...
Cisco CCNA Study Guide
... In a basic peer-to-peer architecture, all hosts on the network can both request and provide data and services. For example, two Windows XP workstations configured to share files would be considered a peer-to-peer network. Peer-to-peer networks are very simple to configure, yet this architecture pres ...
... In a basic peer-to-peer architecture, all hosts on the network can both request and provide data and services. For example, two Windows XP workstations configured to share files would be considered a peer-to-peer network. Peer-to-peer networks are very simple to configure, yet this architecture pres ...
PDF
... information regarding platform support for this feature, access Cisco Feature Navigator. Cisco Feature Navigator dynamically updates the list of supported platforms as new platform support is added for the feature. Cisco Feature Navigator is a web-based tool that enables you to quickly determine whi ...
... information regarding platform support for this feature, access Cisco Feature Navigator. Cisco Feature Navigator dynamically updates the list of supported platforms as new platform support is added for the feature. Cisco Feature Navigator is a web-based tool that enables you to quickly determine whi ...
S9700 Series Terabit Routing Switches
... aggregation. Based on cutting-edge hardware and Huawei Versatile Routing Platform (VRP) software, the S5700 provides a large switching capacity and high-density GE ports to accommodate 10 Gbit/s upstream transmissions. The S5700 can be used in various enterprise network scenarios. For example, it ca ...
... aggregation. Based on cutting-edge hardware and Huawei Versatile Routing Platform (VRP) software, the S5700 provides a large switching capacity and high-density GE ports to accommodate 10 Gbit/s upstream transmissions. The S5700 can be used in various enterprise network scenarios. For example, it ca ...
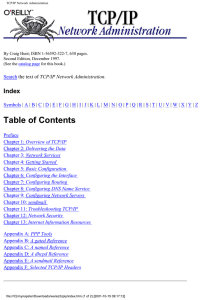
TCP/IP Network Administration - U
... Abstract Syntax Notation One (ASN.1) : 11.9. Simple Network Management Protocol access control : 12.5. Access Control levels of : 9.1.2.1. The share command services to place under, listed : 12.5.1. wrapper software for : 12.5. Access Control ACKD command, in POP : 3.4.2. Post Office Protocol Acknow ...
... Abstract Syntax Notation One (ASN.1) : 11.9. Simple Network Management Protocol access control : 12.5. Access Control levels of : 9.1.2.1. The share command services to place under, listed : 12.5.1. wrapper software for : 12.5. Access Control ACKD command, in POP : 3.4.2. Post Office Protocol Acknow ...
SmartMesh IP Application Notes
... 14.1.2 Unicast Handshake with the Motes on the Receive List ________________________________________ 78 14.1.3 Calculating the otapMIC ________________________________________________________________ 80 14.1.4 Fragment the .otap2 File into Network Packets ____________________________________________ ...
... 14.1.2 Unicast Handshake with the Motes on the Receive List ________________________________________ 78 14.1.3 Calculating the otapMIC ________________________________________________________________ 80 14.1.4 Fragment the .otap2 File into Network Packets ____________________________________________ ...
Apuntes seguridad Redes Avanzadas 0708
... to the gateway. Gateways are deployed within networks that lack multicast support or lack connectivity to a multicast-enabled network containing multicast sources of interest. The gateway functionality may be directly implemented in the host requesting the multicast service or within an application ...
... to the gateway. Gateways are deployed within networks that lack multicast support or lack connectivity to a multicast-enabled network containing multicast sources of interest. The gateway functionality may be directly implemented in the host requesting the multicast service or within an application ...
Introduction to Storage Area Networks
... 1.5.1 Storage area network connectivity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14 1.5.2 Storage area network storage. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14 1.5.3 Storage area network servers . . . . . . . . . . . . . . . . . ...
... 1.5.1 Storage area network connectivity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14 1.5.2 Storage area network storage. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14 1.5.3 Storage area network servers . . . . . . . . . . . . . . . . . ...
Slide 1
... • Need to find the situations and improve the protocols Examples: • Broadcast storm: one broadcast triggers another • Synchronization: a building of computers all contact the DHCP server together after a power failure • Tiny packets: some situations can cause TCP to send many small packets instead o ...
... • Need to find the situations and improve the protocols Examples: • Broadcast storm: one broadcast triggers another • Synchronization: a building of computers all contact the DHCP server together after a power failure • Tiny packets: some situations can cause TCP to send many small packets instead o ...