Zebra/Quagga Routing Suite
... Can dynamically change the configuration and you may view routing table from Zebra terminal interface If the network is small, Configuring Zebra is very easy : setup interfaces, Add static routes and/or default routes If the network is rather large or structure change frequently, you may need to set ...
... Can dynamically change the configuration and you may view routing table from Zebra terminal interface If the network is small, Configuring Zebra is very easy : setup interfaces, Add static routes and/or default routes If the network is rather large or structure change frequently, you may need to set ...
Module 6 – Routing and Routed Protocols
... Configuring static routes • Routers do not need to configure static routes for their own directly connected networks. • We need to configure static routes for networks this router needs to reach. • We will need to configure static routes for the other routers as well, as “routing information about a ...
... Configuring static routes • Routers do not need to configure static routes for their own directly connected networks. • We need to configure static routes for networks this router needs to reach. • We will need to configure static routes for the other routers as well, as “routing information about a ...
T7 Network Access Guide
... The following trademarks and service marks are used by Deutsche Boerse Group under license and are property of their respective owners: All MSCI indexes are service marks and the exclusive property of MSCI Barra. ATX®, ATX® five, CECE® and RDX® are registered trademarks of Vienna Stock Exchange AG. ...
... The following trademarks and service marks are used by Deutsche Boerse Group under license and are property of their respective owners: All MSCI indexes are service marks and the exclusive property of MSCI Barra. ATX®, ATX® five, CECE® and RDX® are registered trademarks of Vienna Stock Exchange AG. ...
Basic Features of i-mode - San Jose State University
... • i-mode was developed by DoCoMo ( which means “anywhere” in Japanese) as a subsidiary of NTT (The Japan’s largest telecommunication service provider Nippon Telegraph and Telephone Corp.) in 1992. • i-mode (The “i” stands for information) is a wireless technology and service mark. • The i-mode servi ...
... • i-mode was developed by DoCoMo ( which means “anywhere” in Japanese) as a subsidiary of NTT (The Japan’s largest telecommunication service provider Nippon Telegraph and Telephone Corp.) in 1992. • i-mode (The “i” stands for information) is a wireless technology and service mark. • The i-mode servi ...
23002-a20 - Network architecture
... Public Land Mobile Network (PLMN) ............................................................................................................ 16 Core Network (CN) and Access Network (AN) .............................................................................................. 16 Circuit Switch ...
... Public Land Mobile Network (PLMN) ............................................................................................................ 16 Core Network (CN) and Access Network (AN) .............................................................................................. 16 Circuit Switch ...
IPv6 and the Security of Your Network and Systems
... Your Users May Decide to “Informally” Try It… • Some sites which rely heavily on firewalls and perimeter security may decide to forego or postpone deployment of native IPv6. Having made the decision to do so, folks may emit a big relieved sigh, believing that by “sitting this dance out,” they will h ...
... Your Users May Decide to “Informally” Try It… • Some sites which rely heavily on firewalls and perimeter security may decide to forego or postpone deployment of native IPv6. Having made the decision to do so, folks may emit a big relieved sigh, believing that by “sitting this dance out,” they will h ...
Dante Certification Program, Level 2: Intermediate Dante Concepts
... • When we look at the latency monitor, we can see that some packets are now falling dangerously close to the limit of our latency setting. We have selected a value that is too small for the physical network we are using, and should change settings to avoid problems. • Latency monitoring can also be ...
... • When we look at the latency monitor, we can see that some packets are now falling dangerously close to the limit of our latency setting. We have selected a value that is too small for the physical network we are using, and should change settings to avoid problems. • Latency monitoring can also be ...
ESnet - Indico
... • ESnet provides network and collaboration services to Office of Science laboratories and to sites of other DOE programs in cases where this increases cost ...
... • ESnet provides network and collaboration services to Office of Science laboratories and to sites of other DOE programs in cases where this increases cost ...
Universal Plug and Play Machine Models
... details that are irrelevant for the understanding of the principle protocol behavior. To figure out what is relevant and what can be neglected is often not trivial and sometimes impossible without consulting the application domain experts. In our case these experts are the UPnP developers at Microso ...
... details that are irrelevant for the understanding of the principle protocol behavior. To figure out what is relevant and what can be neglected is often not trivial and sometimes impossible without consulting the application domain experts. In our case these experts are the UPnP developers at Microso ...
EE579S Computer Security
... • A secure system must be secure under all conditions of operation • This, in turn, demands proof that there is no condition under which it could operate that is insecure, i.e. the negative proposition. • But, formal logic teaches us it is impossible to prove a negative ...
... • A secure system must be secure under all conditions of operation • This, in turn, demands proof that there is no condition under which it could operate that is insecure, i.e. the negative proposition. • But, formal logic teaches us it is impossible to prove a negative ...
IP Multicast over Avaya Fabric Connect
... Flexible Network Services Trill and Fabricpath can only do L2 Multicast Snooping ...
... Flexible Network Services Trill and Fabricpath can only do L2 Multicast Snooping ...
slides 3
... – perfSONAR works best when everyone participates, holes in deployment lead to holes in the problem solving phase ...
... – perfSONAR works best when everyone participates, holes in deployment lead to holes in the problem solving phase ...
Chapter 8: Advanced Routing Protocols
... • Protocol Dependent Modules (PDMs) – Allow EIGRP to carry multiple routed protocols within their own native packet formats ...
... • Protocol Dependent Modules (PDMs) – Allow EIGRP to carry multiple routed protocols within their own native packet formats ...
Synchrony IAN-150/IPP Maintenance and Troubleshooting Manual
... For service outside the U.S. and Canada, contact your local sales representative. Information required for service is: Model No._______________________ ...
... For service outside the U.S. and Canada, contact your local sales representative. Information required for service is: Model No._______________________ ...
What Is a Virtual Private Network?
... Communications. Like L2F, PPTP allows the tunneling of remote access client PPP frames between a NAS and a VPN gateway/concentrator. PPTP also allows a tunnel to be set up directly from a remote access client to a VPN gateway/concentrator. PPP encapsulated packets carried over PPTP tunnels are often ...
... Communications. Like L2F, PPTP allows the tunneling of remote access client PPP frames between a NAS and a VPN gateway/concentrator. PPTP also allows a tunnel to be set up directly from a remote access client to a VPN gateway/concentrator. PPP encapsulated packets carried over PPTP tunnels are often ...
BROCADE NETIRON XMR 4000, 8000 16000, 32000
... Series offers a powerful set of security mechanisms that allow operators to enhance both infrastructure security and subscriber security. The NetIron XMR routers feature highly scalable inbound and outbound ACLs, which allow operators to implement IPv4, IPv6, and Layer 2 security policies. These pol ...
... Series offers a powerful set of security mechanisms that allow operators to enhance both infrastructure security and subscriber security. The NetIron XMR routers feature highly scalable inbound and outbound ACLs, which allow operators to implement IPv4, IPv6, and Layer 2 security policies. These pol ...
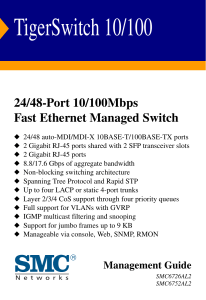
TigerSwitch 10/100 Management Guide
... purchase from SMC or its Authorized Reseller. SMC may, at its own discretion, repair or replace any product not operating as warranted with a similar or functionally equivalent product, during the applicable warranty term. SMC will endeavor to repair or replace any product returned under warranty wi ...
... purchase from SMC or its Authorized Reseller. SMC may, at its own discretion, repair or replace any product not operating as warranted with a similar or functionally equivalent product, during the applicable warranty term. SMC will endeavor to repair or replace any product returned under warranty wi ...
Optical Interconnection Networks
... Optical Interconnection Networks M. S. Thesis Defense Presentation ...
... Optical Interconnection Networks M. S. Thesis Defense Presentation ...
SAILOR 500/250 FleetBroadband Including 19” Rack Version
... Any responsibility or liability for loss or damage in connection with the use of this product and the accompanying documentation is disclaimed by Thrane & Thrane A/S. The information in this manual is provided for information purposes only, is subject to change without notice and may contain errors ...
... Any responsibility or liability for loss or damage in connection with the use of this product and the accompanying documentation is disclaimed by Thrane & Thrane A/S. The information in this manual is provided for information purposes only, is subject to change without notice and may contain errors ...
PDF - This Chapter (262.0 KB)
... Agent Gathering Data from a MIB and Sending Traps to the Manager ...
... Agent Gathering Data from a MIB and Sending Traps to the Manager ...
Cisco TrustSec How-To Guide: Segmenting Clients and Servers in
... The campus-to-data center segmentation includes, but is not limited to, users accessing data center resources either directly from the campus or through a virtual desktop environment. While there are multiple ways to enforce such polices, we will primarily focus on the use of Security Group Access C ...
... The campus-to-data center segmentation includes, but is not limited to, users accessing data center resources either directly from the campus or through a virtual desktop environment. While there are multiple ways to enforce such polices, we will primarily focus on the use of Security Group Access C ...
Netvisor nvOS Configuration Guide
... Any Internet Protocol (IP) addresses used in this document are not intended to be actual addresses. Any examples, command display output, and figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses in illustrative content is unintentional and coincid ...
... Any Internet Protocol (IP) addresses used in this document are not intended to be actual addresses. Any examples, command display output, and figures included in the document are shown for illustrative purposes only. Any use of actual IP addresses in illustrative content is unintentional and coincid ...