Lecture 3
... The above allow us to solve equations involving the same prime modulus. One can also solve equations in which different prime moduli are used, as 7x + 3y ≡ 1 (mod 13) 2x + 5y ≡ 2 (mod 17) but it needs a different technique. One cannot solve the above equations using the reciprocal alone. It needs th ...
... The above allow us to solve equations involving the same prime modulus. One can also solve equations in which different prime moduli are used, as 7x + 3y ≡ 1 (mod 13) 2x + 5y ≡ 2 (mod 17) but it needs a different technique. One cannot solve the above equations using the reciprocal alone. It needs th ...
Clauses Versus Gates in CEGAR-Based 2QBF Solving Valeriy Balabanov, Jie-Hong R. Jiang,
... E.g., in (Mishchenko et al. 2015) FPGA synthesis benchmarks are formulated on And-Inverter graphs (AIGs), which is an efficient way to represent general Boolean networks. It is known that any Boolean circuit can be transformed into an equisatisfiable CNF formula, by the various CNFization procedures ...
... E.g., in (Mishchenko et al. 2015) FPGA synthesis benchmarks are formulated on And-Inverter graphs (AIGs), which is an efficient way to represent general Boolean networks. It is known that any Boolean circuit can be transformed into an equisatisfiable CNF formula, by the various CNFization procedures ...
How to Encrypt with the LPN Problem
... vector x, the sender draws a k-bit random vector a and computes y = C(x) ⊕ a · M ⊕ ν , where ν ← Berm,η is an m-bit noise vector such that each of its bits is (independently) 1 with probability η and 0 with probability 1 − η. The ciphertext is the pair (a, y). Upon reception of this pair, the receiv ...
... vector x, the sender draws a k-bit random vector a and computes y = C(x) ⊕ a · M ⊕ ν , where ν ← Berm,η is an m-bit noise vector such that each of its bits is (independently) 1 with probability η and 0 with probability 1 − η. The ciphertext is the pair (a, y). Upon reception of this pair, the receiv ...
Improving Planning Graph Analysis for Artificial Intelligence Planning
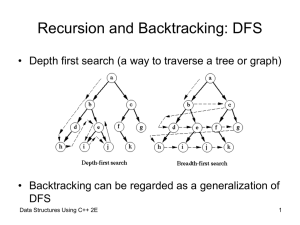
... the last precondition. This procedure will be repeated until all combinations of alternative instantiations under that branch of the tree have been checked, and only then the algorithm will backtrack to the previous decision point and select another value for < product >, which originally caused the ...
... the last precondition. This procedure will be repeated until all combinations of alternative instantiations under that branch of the tree have been checked, and only then the algorithm will backtrack to the previous decision point and select another value for < product >, which originally caused the ...
Recursion Review - Department of Computer Science
... sequence, then F(n) is (gn), where g (1 5 ) / 2 The time complexity is exponential: O(gn) ...
... sequence, then F(n) is (gn), where g (1 5 ) / 2 The time complexity is exponential: O(gn) ...
Computing functions with Turing machines
... • A (total) function f : N → N is (total) computable if we can find a Turing Machine that computes it (given any number n in Unary as input in the tape, after completing the computation the tape contains f(n) in Unary). • A partial function f : N → N is said to be partially computable if there is a ...
... • A (total) function f : N → N is (total) computable if we can find a Turing Machine that computes it (given any number n in Unary as input in the tape, after completing the computation the tape contains f(n) in Unary). • A partial function f : N → N is said to be partially computable if there is a ...
Optimizing the F-Measure in Multi-Label Classification
... theoretical challenges; this includes the possibility to model statistical dependencies between different class labels as well as to define and minimize appropriate loss functions. A large number of MLC loss functions has been proposed in the literature. In experimental studies, many of these losses ...
... theoretical challenges; this includes the possibility to model statistical dependencies between different class labels as well as to define and minimize appropriate loss functions. A large number of MLC loss functions has been proposed in the literature. In experimental studies, many of these losses ...
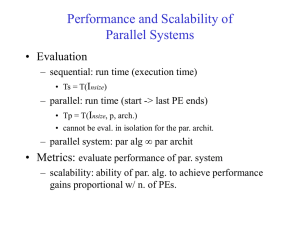
Performance and Scalability of Parallel Systems
... – W--computation steps => Pmax = W – For Pmax -- each PE extends one step of the algorithm – For p
... – W--computation steps => Pmax = W – For Pmax -- each PE extends one step of the algorithm – For p
Achieving Maximum Energy-Efficiency in Multi-Relay
... of increasing the number of RNs in the system and its relation not only to the cell radius, but also to the relays’ positions. The algorithm may be used for characterizing the effects of many other system design choices on the maximum SE and EE. The rest of this paper is organized as follows. In Sec ...
... of increasing the number of RNs in the system and its relation not only to the cell radius, but also to the relays’ positions. The algorithm may be used for characterizing the effects of many other system design choices on the maximum SE and EE. The rest of this paper is organized as follows. In Sec ...
Annals of Pure and Applied Logic Ordinal machines and admissible
... second author recast the proof of the Sacks–Simpson theorem using the computational paradigm instead of constructibility theory. The crucial point involved was how the informally presented recursions in the argument of Sacks and Simpson [11, 12] (and a recursion method presented by Shore [13]) can b ...
... second author recast the proof of the Sacks–Simpson theorem using the computational paradigm instead of constructibility theory. The crucial point involved was how the informally presented recursions in the argument of Sacks and Simpson [11, 12] (and a recursion method presented by Shore [13]) can b ...
Advanced Topics in Theoretical Computer Science
... Logic 1. The set of theorems in propositional logic is decidable 2. The set of theorems in first-order logic is recursively enumerable, but undecidable Idea of proof: • For each signature Σ, the set of valid Σ-formulas is recursively ...
... Logic 1. The set of theorems in propositional logic is decidable 2. The set of theorems in first-order logic is recursively enumerable, but undecidable Idea of proof: • For each signature Σ, the set of valid Σ-formulas is recursively ...
Algorithm
In mathematics and computer science, an algorithm (/ˈælɡərɪðəm/ AL-gə-ri-dhəm) is a self-contained step-by-step set of operations to be performed. Algorithms exist that perform calculation, data processing, and automated reasoning.An algorithm is an effective method that can be expressed within a finite amount of space and time and in a well-defined formal language for calculating a function. Starting from an initial state and initial input (perhaps empty), the instructions describe a computation that, when executed, proceeds through a finite number of well-defined successive states, eventually producing ""output"" and terminating at a final ending state. The transition from one state to the next is not necessarily deterministic; some algorithms, known as randomized algorithms, incorporate random input.The concept of algorithm has existed for centuries, however a partial formalization of what would become the modern algorithm began with attempts to solve the Entscheidungsproblem (the ""decision problem"") posed by David Hilbert in 1928. Subsequent formalizations were framed as attempts to define ""effective calculability"" or ""effective method""; those formalizations included the Gödel–Herbrand–Kleene recursive functions of 1930, 1934 and 1935, Alonzo Church's lambda calculus of 1936, Emil Post's ""Formulation 1"" of 1936, and Alan Turing's Turing machines of 1936–7 and 1939. Giving a formal definition of algorithms, corresponding to the intuitive notion, remains a challenging problem.