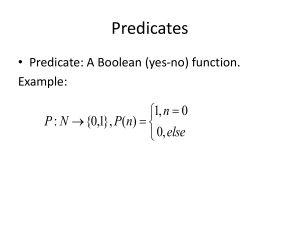
Predicates
... • The fact that a language is decidable means that we can use a Turing Machine to decide membership in the language. Example: L = {anbn , n≥0} is a decidable language because there is a Turing Machine that, given any string in Σ* it decides whether the string belongs in L or not. ...
... • The fact that a language is decidable means that we can use a Turing Machine to decide membership in the language. Example: L = {anbn , n≥0} is a decidable language because there is a Turing Machine that, given any string in Σ* it decides whether the string belongs in L or not. ...
ERRORS and COMPUTER ARITHMETIC Types of Error in
... • Floating Point Number Representation: any real number y can be put in floating point form y = ±.d1d2 . . . dk . . . × b±n for base b, with 0 < d1 < b, 0 ≤ di < b, i > 1. E.g. (.1)10 = +(.1100)2 × 2−3. Conversion from decimal to binary? Integer part: repeatedly divide by 2, saving remainder digits ...
... • Floating Point Number Representation: any real number y can be put in floating point form y = ±.d1d2 . . . dk . . . × b±n for base b, with 0 < d1 < b, 0 ≤ di < b, i > 1. E.g. (.1)10 = +(.1100)2 × 2−3. Conversion from decimal to binary? Integer part: repeatedly divide by 2, saving remainder digits ...
mining on car database employing learning and clustering algorithms
... a model is hence created which predicts the characteristic of a review comment after getting trained. It was found that model successfully predicted correctly about the review comments after getting trained. Also two clustering algorithms: K-Means and Self Organising Maps (SOM) are used and worked u ...
... a model is hence created which predicts the characteristic of a review comment after getting trained. It was found that model successfully predicted correctly about the review comments after getting trained. Also two clustering algorithms: K-Means and Self Organising Maps (SOM) are used and worked u ...
RSA cryptosystem with large key length
... Confidentiality: encipher using public key, decipher using private key; Integrity/authentication: encipher using private key, decipher using public key. ...
... Confidentiality: encipher using public key, decipher using private key; Integrity/authentication: encipher using private key, decipher using public key. ...
L10: k-Means Clustering
... k = O(n )) number of possible distinct cluster centers. But it could be exponential in k and d (the dimension when Euclidean distance used). • However, usually R = 10 is fine. • Smoothed analysis: if data perturbed randomly slightly, then R = O(n35 k 34 d8 ). This is “polynomial,” but still ridiculo ...
... k = O(n )) number of possible distinct cluster centers. But it could be exponential in k and d (the dimension when Euclidean distance used). • However, usually R = 10 is fine. • Smoothed analysis: if data perturbed randomly slightly, then R = O(n35 k 34 d8 ). This is “polynomial,” but still ridiculo ...
PDF
... In particular, we can count the total number of distinct real roots by looking at the limits as a → −∞ and b → +∞. The total number of distinct real roots will depend only on the leading terms of the Sturm sequence polynomials. Note that deg Pn < deg Pn−1 , and so the longest possible Sturm sequence ...
... In particular, we can count the total number of distinct real roots by looking at the limits as a → −∞ and b → +∞. The total number of distinct real roots will depend only on the leading terms of the Sturm sequence polynomials. Note that deg Pn < deg Pn−1 , and so the longest possible Sturm sequence ...
Comparative Computer Results of a New Complementary Pivot
... inequality constraints). The approach is based on the complementary pivoting algorithms that have been developed to solve certain classes of fixed-point problems. The specific approach is to use the equality constraints to solve for some of the variables in terms of the remaining ones, thus enabling ...
... inequality constraints). The approach is based on the complementary pivoting algorithms that have been developed to solve certain classes of fixed-point problems. The specific approach is to use the equality constraints to solve for some of the variables in terms of the remaining ones, thus enabling ...
Programming and Problem Solving with C++, 2/e
... into machine language Main Program -- may call subalgorithms ...
... into machine language Main Program -- may call subalgorithms ...
hw08 - Rose
... For definiteness, I will show you my top-level Python code and its output. You can use my code, adapt it to another language, start from scratch in any language, or simply write very clear pseudocode. You must present your algorithm in a way that makes it easy for the grader to determine whether it ...
... For definiteness, I will show you my top-level Python code and its output. You can use my code, adapt it to another language, start from scratch in any language, or simply write very clear pseudocode. You must present your algorithm in a way that makes it easy for the grader to determine whether it ...
Quiz04-soln - Rose
... Induction step. IN(T) > 0, so T has a root (internal node), and two subtrees TL and TR. Notice that IN(T) + IN(TL) + IN(TR) + 1, and EN(T) = EN(TL) + EN(TR). Induction assumption. The property is true for any EBT with fewer nodes than T. In particular, for TL and TR, which are smaller because they d ...
... Induction step. IN(T) > 0, so T has a root (internal node), and two subtrees TL and TR. Notice that IN(T) + IN(TL) + IN(TR) + 1, and EN(T) = EN(TL) + EN(TR). Induction assumption. The property is true for any EBT with fewer nodes than T. In particular, for TL and TR, which are smaller because they d ...
Algorithm
In mathematics and computer science, an algorithm (/ˈælɡərɪðəm/ AL-gə-ri-dhəm) is a self-contained step-by-step set of operations to be performed. Algorithms exist that perform calculation, data processing, and automated reasoning.An algorithm is an effective method that can be expressed within a finite amount of space and time and in a well-defined formal language for calculating a function. Starting from an initial state and initial input (perhaps empty), the instructions describe a computation that, when executed, proceeds through a finite number of well-defined successive states, eventually producing ""output"" and terminating at a final ending state. The transition from one state to the next is not necessarily deterministic; some algorithms, known as randomized algorithms, incorporate random input.The concept of algorithm has existed for centuries, however a partial formalization of what would become the modern algorithm began with attempts to solve the Entscheidungsproblem (the ""decision problem"") posed by David Hilbert in 1928. Subsequent formalizations were framed as attempts to define ""effective calculability"" or ""effective method""; those formalizations included the Gödel–Herbrand–Kleene recursive functions of 1930, 1934 and 1935, Alonzo Church's lambda calculus of 1936, Emil Post's ""Formulation 1"" of 1936, and Alan Turing's Turing machines of 1936–7 and 1939. Giving a formal definition of algorithms, corresponding to the intuitive notion, remains a challenging problem.