Border Gateway Protocol (BGP4)
... • NLRI/Prefix – NLRI - network layer reachability information – Reachability information for a IP address & mask ...
... • NLRI/Prefix – NLRI - network layer reachability information – Reachability information for a IP address & mask ...
Definition 3: Detection Quality of Edge Sets
... coverage in WSNs of line-based deployed sensors. He el al. in [12] considered curve-based sensor deployment. They identified the characteristics for optimal curve-based deployment and proposed algorithms to achieve the optimal deployment. Saipulla et al. [13][14] observed that barrier gaps may appea ...
... coverage in WSNs of line-based deployed sensors. He el al. in [12] considered curve-based sensor deployment. They identified the characteristics for optimal curve-based deployment and proposed algorithms to achieve the optimal deployment. Saipulla et al. [13][14] observed that barrier gaps may appea ...
Computer Networks Laboratory
... Experiences more data transmission errors as compared to LAN. WANs (like the Internet) are not owned by any one organization but rather exist under collective distributed ownership and management over long distances. Networks in remote areas have to be connected, Set-up costs are higher. Maintaining ...
... Experiences more data transmission errors as compared to LAN. WANs (like the Internet) are not owned by any one organization but rather exist under collective distributed ownership and management over long distances. Networks in remote areas have to be connected, Set-up costs are higher. Maintaining ...
long talk - Cs.princeton.edu
... – Analyze valid differences between forwarding and signaling paths – Use the AS traceroute tool to detect and characterize anomalies ...
... – Analyze valid differences between forwarding and signaling paths – Use the AS traceroute tool to detect and characterize anomalies ...
Chord: A Scalable Peer-to-peer Lookup Service for Internet Applications Ion Stoica
... the Internet as a hierarchy of geographical, topological, or administrative domains, effectively constructing a static world-wide search tree, much like DNS. Information about an object is stored in a particular leaf domain, and pointer caches provide search short cuts [22]. The Globe system handles ...
... the Internet as a hierarchy of geographical, topological, or administrative domains, effectively constructing a static world-wide search tree, much like DNS. Information about an object is stored in a particular leaf domain, and pointer caches provide search short cuts [22]. The Globe system handles ...
Integrating Cisco Press Resources into the
... System (IS-IS) are link-state routing protocols – Collect routing information from all other routers in the area – Each router calculates all the best paths to all destinations in the network – Because each router calculates best paths, they are less likely to propagate incorrect information learned ...
... System (IS-IS) are link-state routing protocols – Collect routing information from all other routers in the area – Each router calculates all the best paths to all destinations in the network – Because each router calculates best paths, they are less likely to propagate incorrect information learned ...
Chapter 8: Advanced Routing Protocols
... EIGRP Components (continued) • Reliable Transport Protocol (RTP) – Because EIGRP is protocol-independent, it cannot use existing Transport layer protocols to carry its various packet types – Instead, Cisco developed an entirely new layer 4 protocol – RTP can actually provide both reliable and unrel ...
... EIGRP Components (continued) • Reliable Transport Protocol (RTP) – Because EIGRP is protocol-independent, it cannot use existing Transport layer protocols to carry its various packet types – Instead, Cisco developed an entirely new layer 4 protocol – RTP can actually provide both reliable and unrel ...
Green Wave: Latency and Capacity-Efficient Sleep Scheduling for
... such that a satisfiable instance of DESS does not correspond to a satisfiable instance of 3SAT in the reduction. Hence, the NP-hardness of DESS is still an open question. In this paper, we study a slightly harder version of DESS, called delay efficient sleep scheduling by selections problem (DESS-S) ...
... such that a satisfiable instance of DESS does not correspond to a satisfiable instance of 3SAT in the reduction. Hence, the NP-hardness of DESS is still an open question. In this paper, we study a slightly harder version of DESS, called delay efficient sleep scheduling by selections problem (DESS-S) ...
Chord: A Scalable P2P Lookup Service for Internet Applications
... the Internet as a hierarchy of geographical, topological, or administrative domains, effectively constructing a static world-wide search tree, much like DNS. Information about an object is stored in a particular leaf domain, and pointer caches provide search short cuts [22]. The Globe system handles ...
... the Internet as a hierarchy of geographical, topological, or administrative domains, effectively constructing a static world-wide search tree, much like DNS. Information about an object is stored in a particular leaf domain, and pointer caches provide search short cuts [22]. The Globe system handles ...
datagram network
... – Want to process each packet in less time than it takes to receive the next one INFO 203 week 7 ...
... – Want to process each packet in less time than it takes to receive the next one INFO 203 week 7 ...
Chord: A Scalable Peer-to-peer Lookup Service for Internet
... The Chord software takes the form of a library to be linked with the client and server applications that use it. The application interacts with Chord in two main ways. First, Chord provides a lookup(key) algorithm that yields the IP address of the node responsible for the key. Second, the Chord soft ...
... The Chord software takes the form of a library to be linked with the client and server applications that use it. The application interacts with Chord in two main ways. First, Chord provides a lookup(key) algorithm that yields the IP address of the node responsible for the key. Second, the Chord soft ...
ch4_1040106update
... A collision domain refers to a network segment An n-port bridge could separate one collision domain into n collision domains All these collision domains are still under the same broadcast domain unless VLANs are created All nodes can communicate with each other by broadcast at the link layer An n -p ...
... A collision domain refers to a network segment An n-port bridge could separate one collision domain into n collision domains All these collision domains are still under the same broadcast domain unless VLANs are created All nodes can communicate with each other by broadcast at the link layer An n -p ...
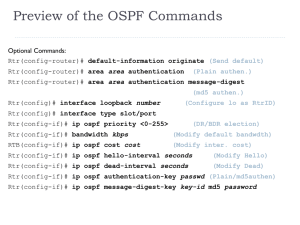
OSPF - Treca
... protocols (IP, IPX, AppleTalk and IPv6) through the use of protocol-dependent modules Reliable Transport Protocol (RTP) – manages communication DUAL – Diffusing Update Algorithm © 2009 Cisco Systems, Inc. All rights reserved. ...
... protocols (IP, IPX, AppleTalk and IPv6) through the use of protocol-dependent modules Reliable Transport Protocol (RTP) – manages communication DUAL – Diffusing Update Algorithm © 2009 Cisco Systems, Inc. All rights reserved. ...
PPT Version
... Info: What the IBTA needs to define • Means for permitting a Host to establish an iSCSI/iSER connection with a peer InfiniBand end-node – Indicating when that end node does not support iSER • So the Host would be able to fall back to iSCSI/TCP over IPoIB ...
... Info: What the IBTA needs to define • Means for permitting a Host to establish an iSCSI/iSER connection with a peer InfiniBand end-node – Indicating when that end node does not support iSER • So the Host would be able to fall back to iSCSI/TCP over IPoIB ...
OSPF
... Provides authentication of routing messages Enables load balancing by allowing traffic to be split evenly across routes with equal cost Type-of-Service routing allows to setup different routes dependent on the TOS field Supports subnetting Supports multicasting Allows hierarchical routing ...
... Provides authentication of routing messages Enables load balancing by allowing traffic to be split evenly across routes with equal cost Type-of-Service routing allows to setup different routes dependent on the TOS field Supports subnetting Supports multicasting Allows hierarchical routing ...
Document
... It establishes a IPv6/IPv6 tunnel with the LMA. All the packets from MN are reverse tunneled to its LMA All the packets from the tunnel are routed to MN. Router Advertisement should be UNICASTed to an MN It will contain MN’s Home Network Prefix (MN-HNP) CNP ...
... It establishes a IPv6/IPv6 tunnel with the LMA. All the packets from MN are reverse tunneled to its LMA All the packets from the tunnel are routed to MN. Router Advertisement should be UNICASTed to an MN It will contain MN’s Home Network Prefix (MN-HNP) CNP ...
From Subnetting to VLSM - YSU Computer Science
... – RFC Number 791 (760) – Class based on value in first octet value – Receiving router ands subnet mask to determine subnet • Class A • Class B • Class C ...
... – RFC Number 791 (760) – Class based on value in first octet value – Receiving router ands subnet mask to determine subnet • Class A • Class B • Class C ...
RIPv2 - College of DuPage
... in creating additional networks without having to add more physical interfaces on the router. A loopback interface can be pinged and the subnet can be advertised in routing updates. Therefore, loopback interfaces are ideal for simulating multiple networks attached to the same router. In our examp ...
... in creating additional networks without having to add more physical interfaces on the router. A loopback interface can be pinged and the subnet can be advertised in routing updates. Therefore, loopback interfaces are ideal for simulating multiple networks attached to the same router. In our examp ...
SNMP - Computer Science and Engineering
... Non-repeaters tells the get-bulk command that the first N objects can be retrieved with a simple get-next operation. Maxrepetitions tells the get-bulk command to attempt up to M getnext operations to retrieve the remaining objects ...
... Non-repeaters tells the get-bulk command that the first N objects can be retrieved with a simple get-next operation. Maxrepetitions tells the get-bulk command to attempt up to M getnext operations to retrieve the remaining objects ...
Routing Theory Part 2
... (Later, we will see another example with real IP addresses.) In their routing updates to the neighboring router(s), distance-vector routing protocols include the following information for each network in their routing table: – Network address – This would normally be an ip network address. – The m ...
... (Later, we will see another example with real IP addresses.) In their routing updates to the neighboring router(s), distance-vector routing protocols include the following information for each network in their routing table: – Network address – This would normally be an ip network address. – The m ...